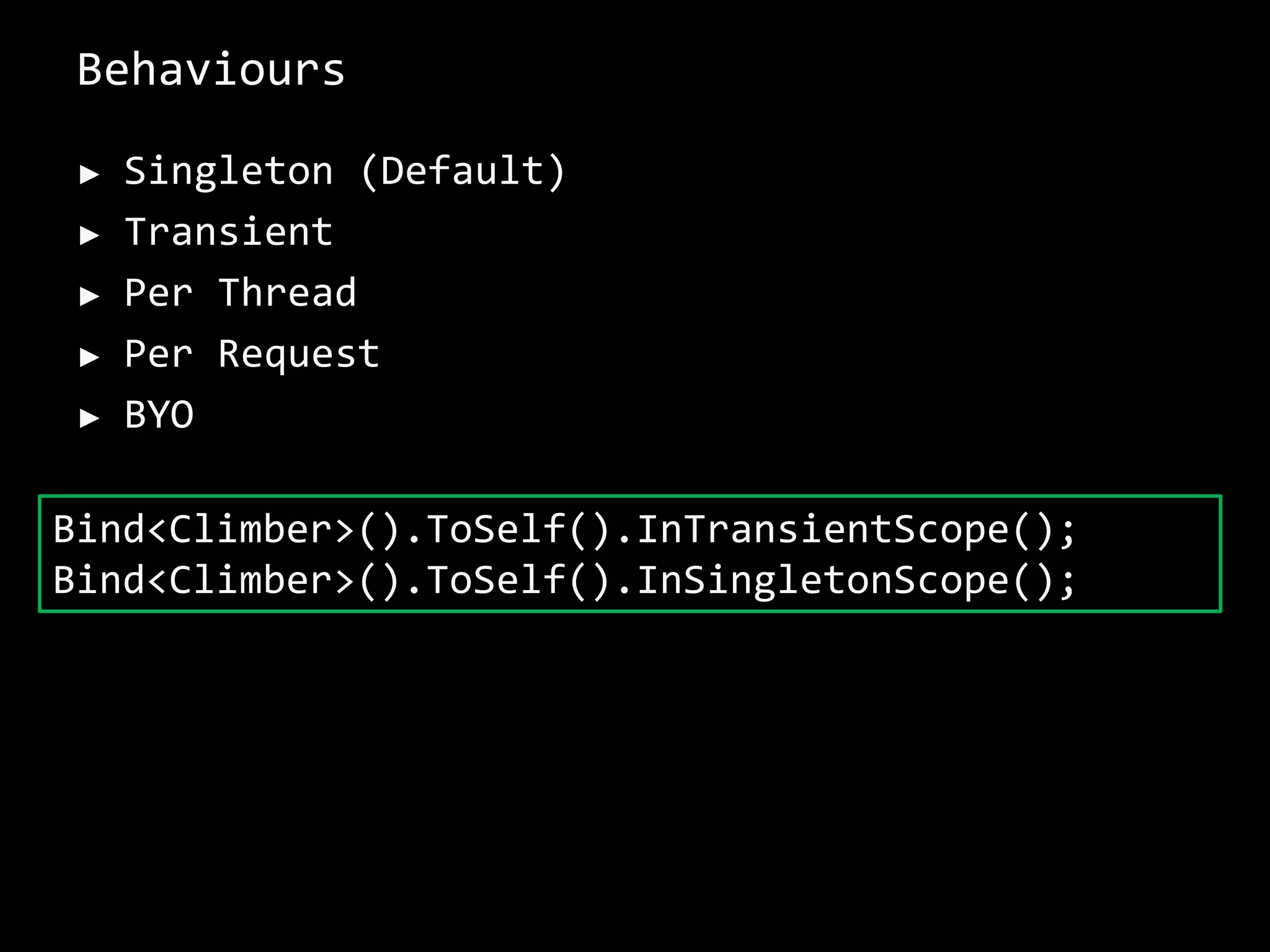
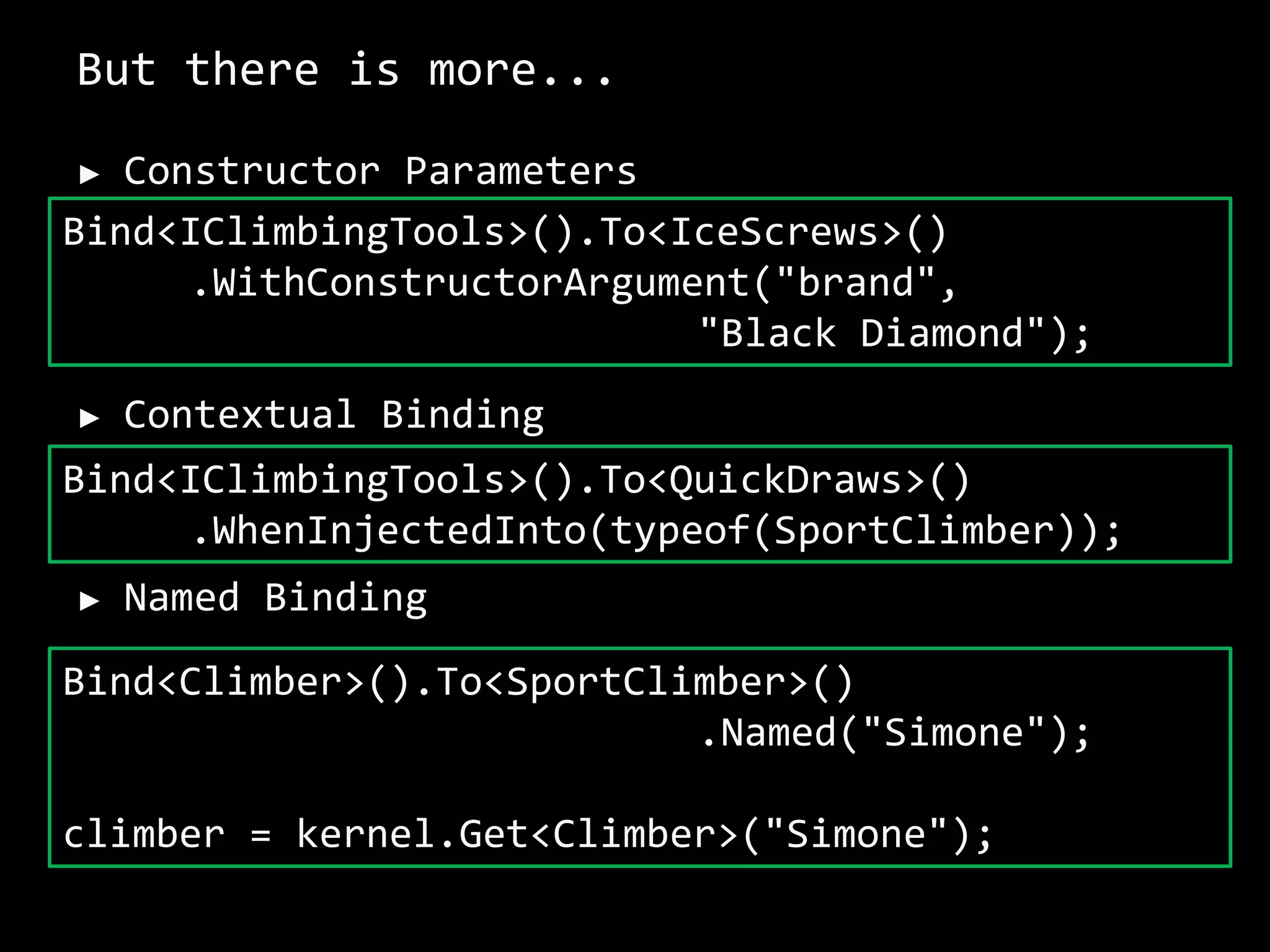
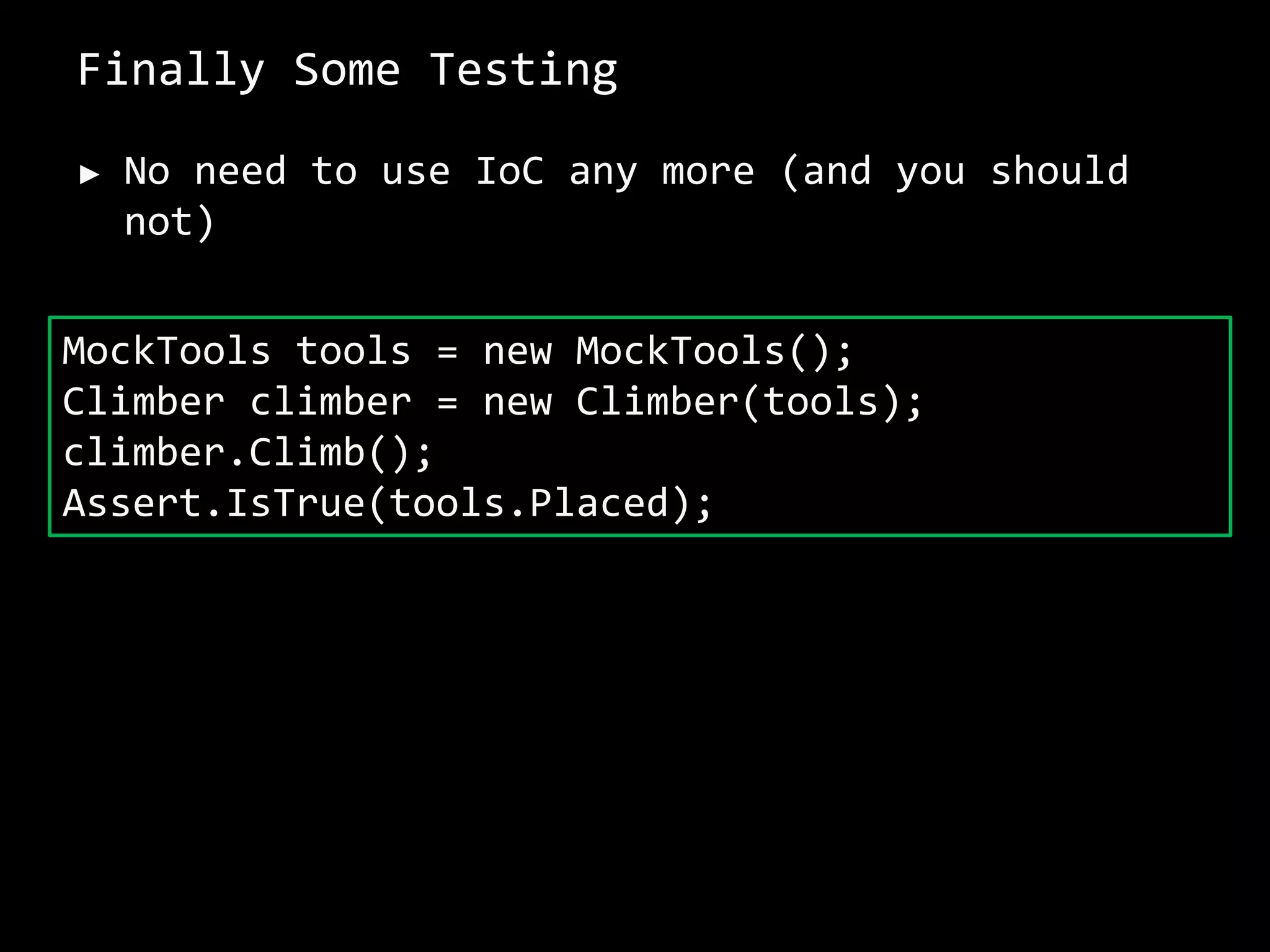
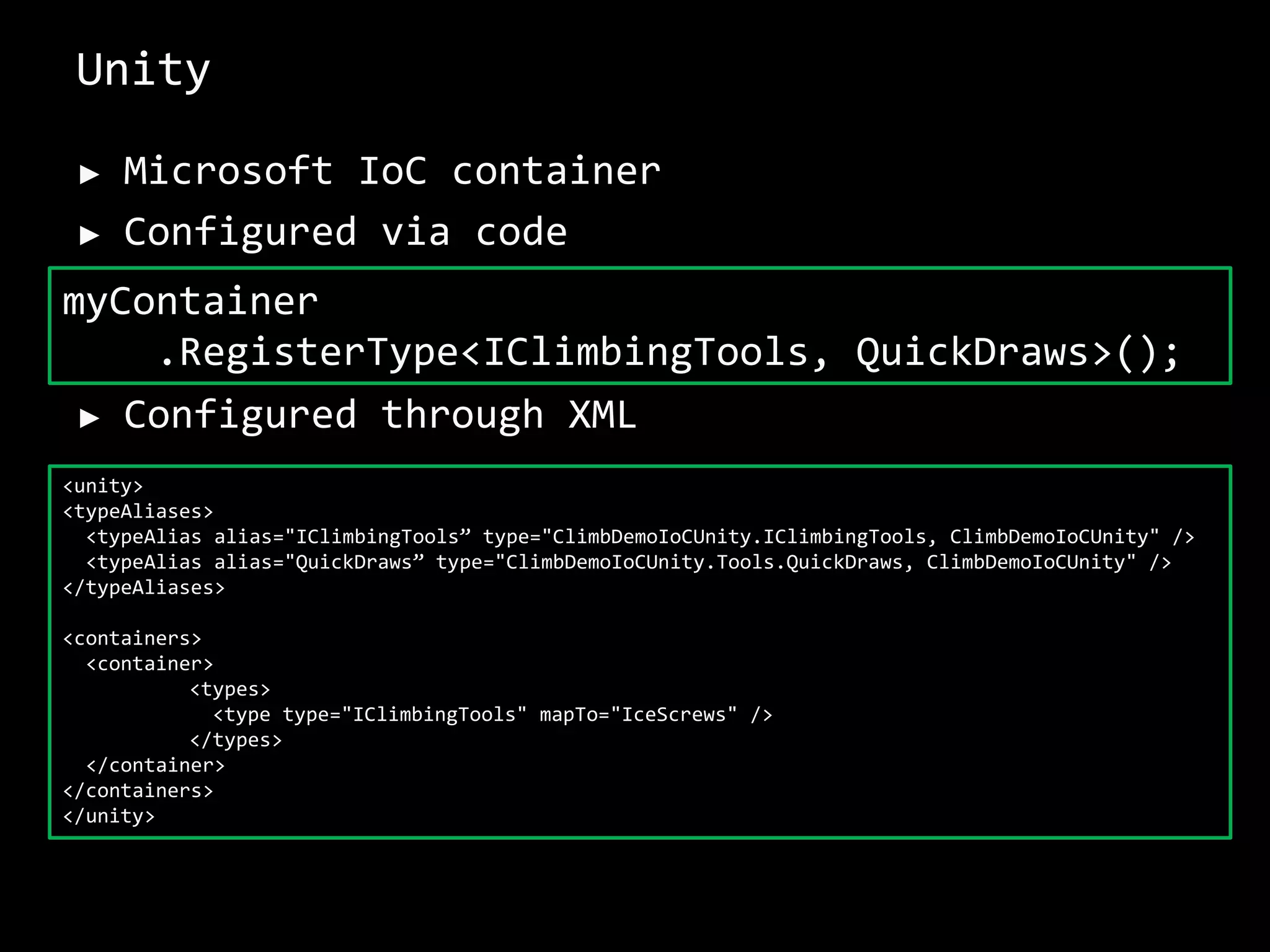
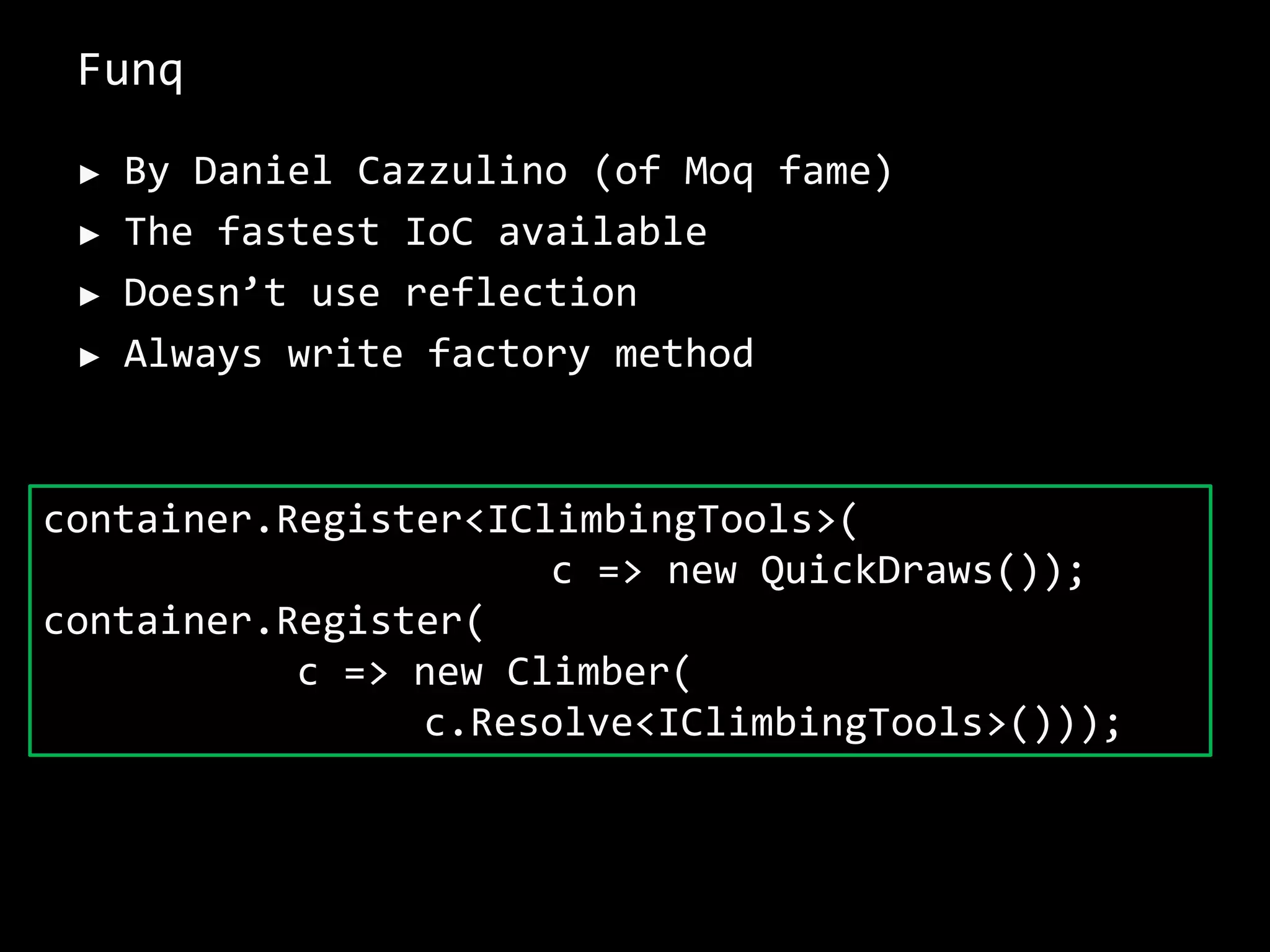
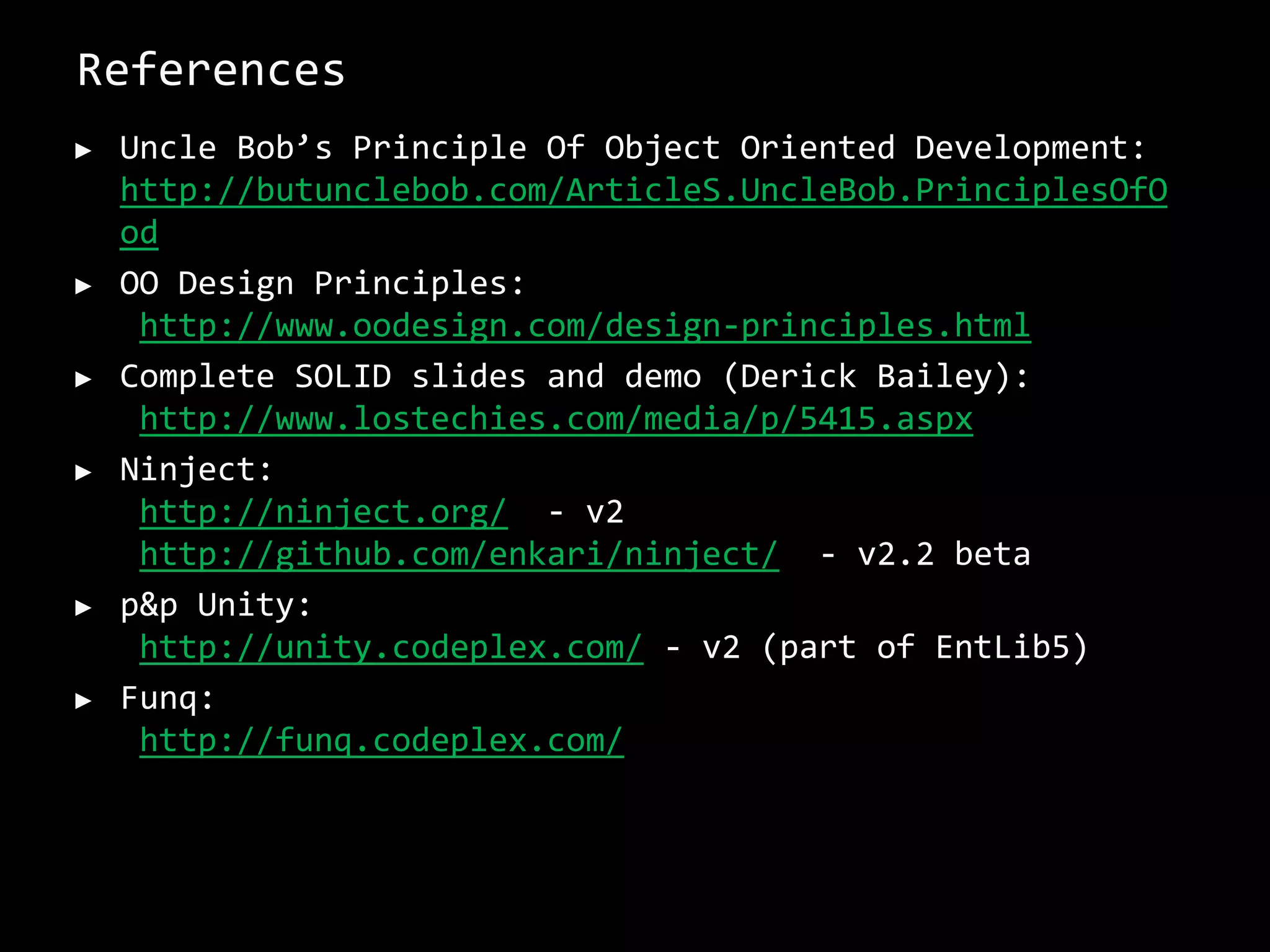
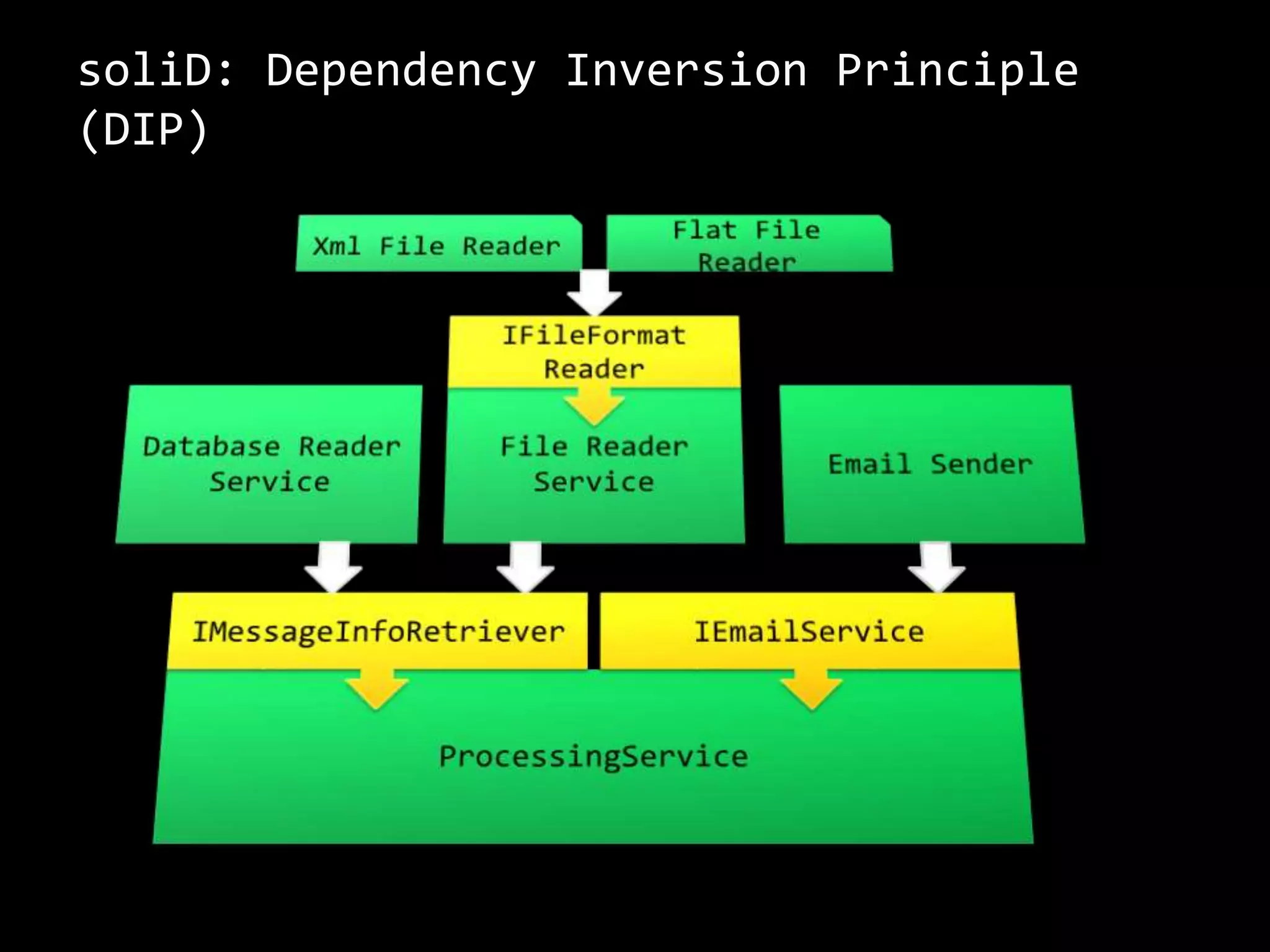
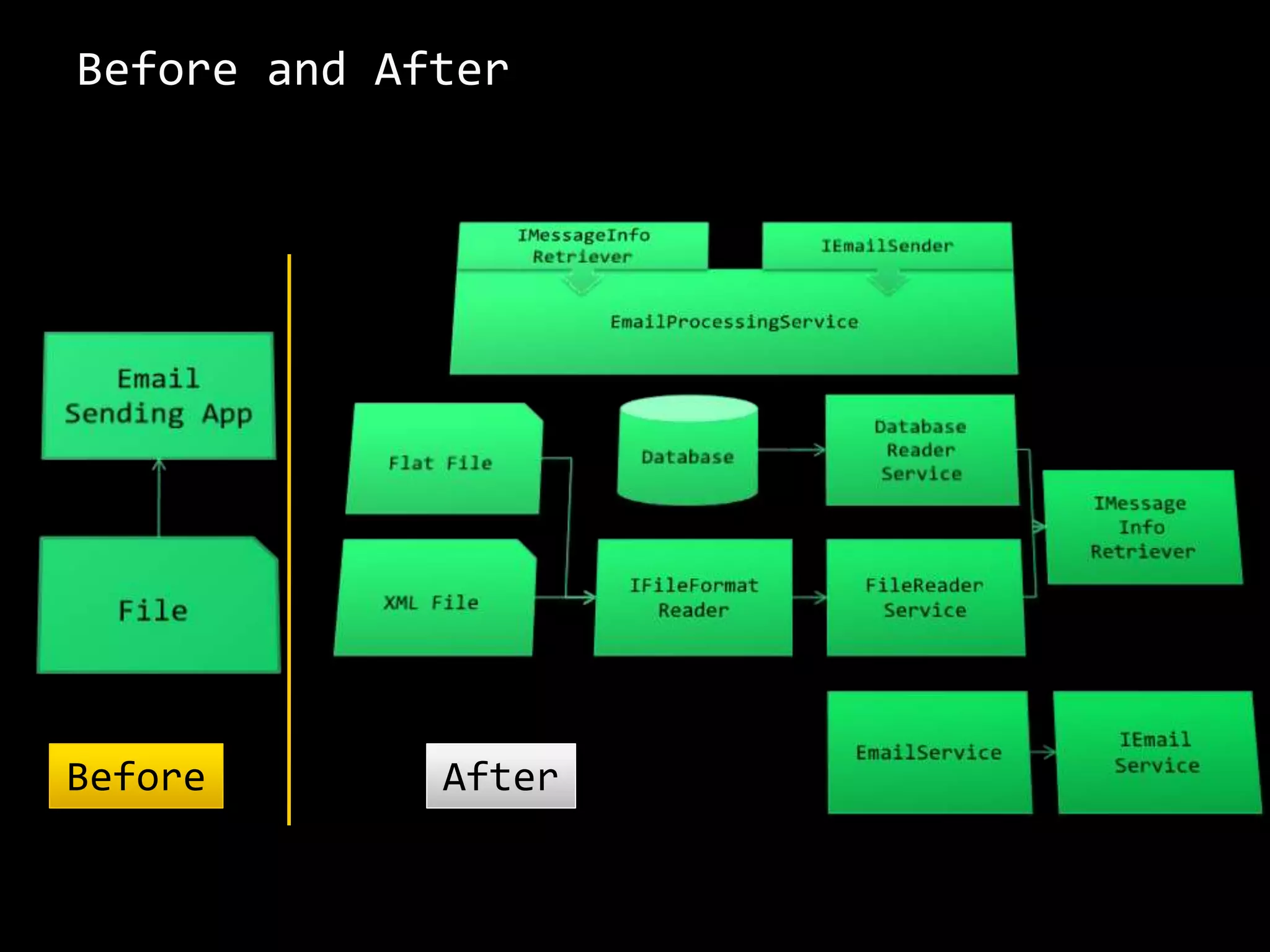
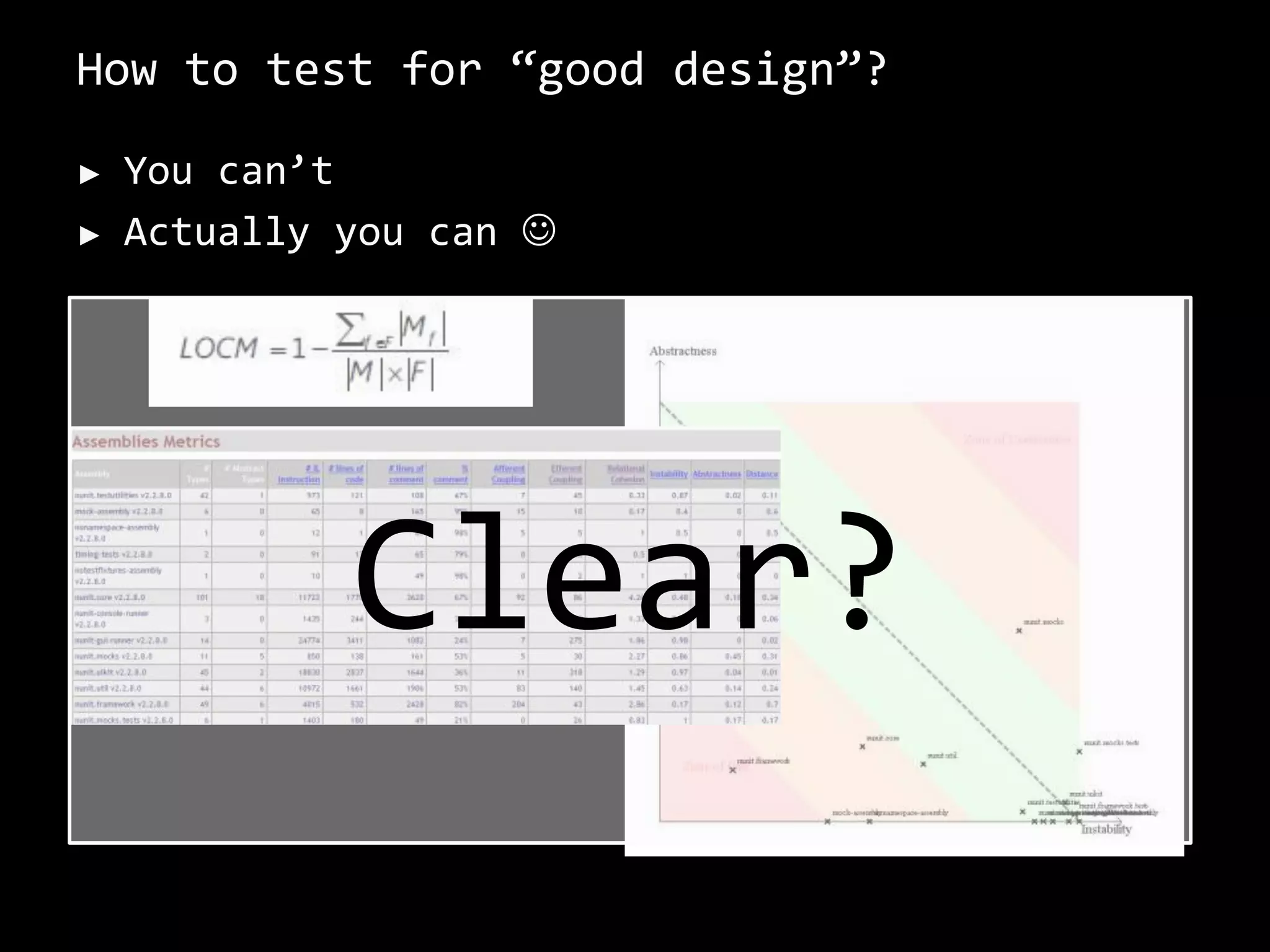
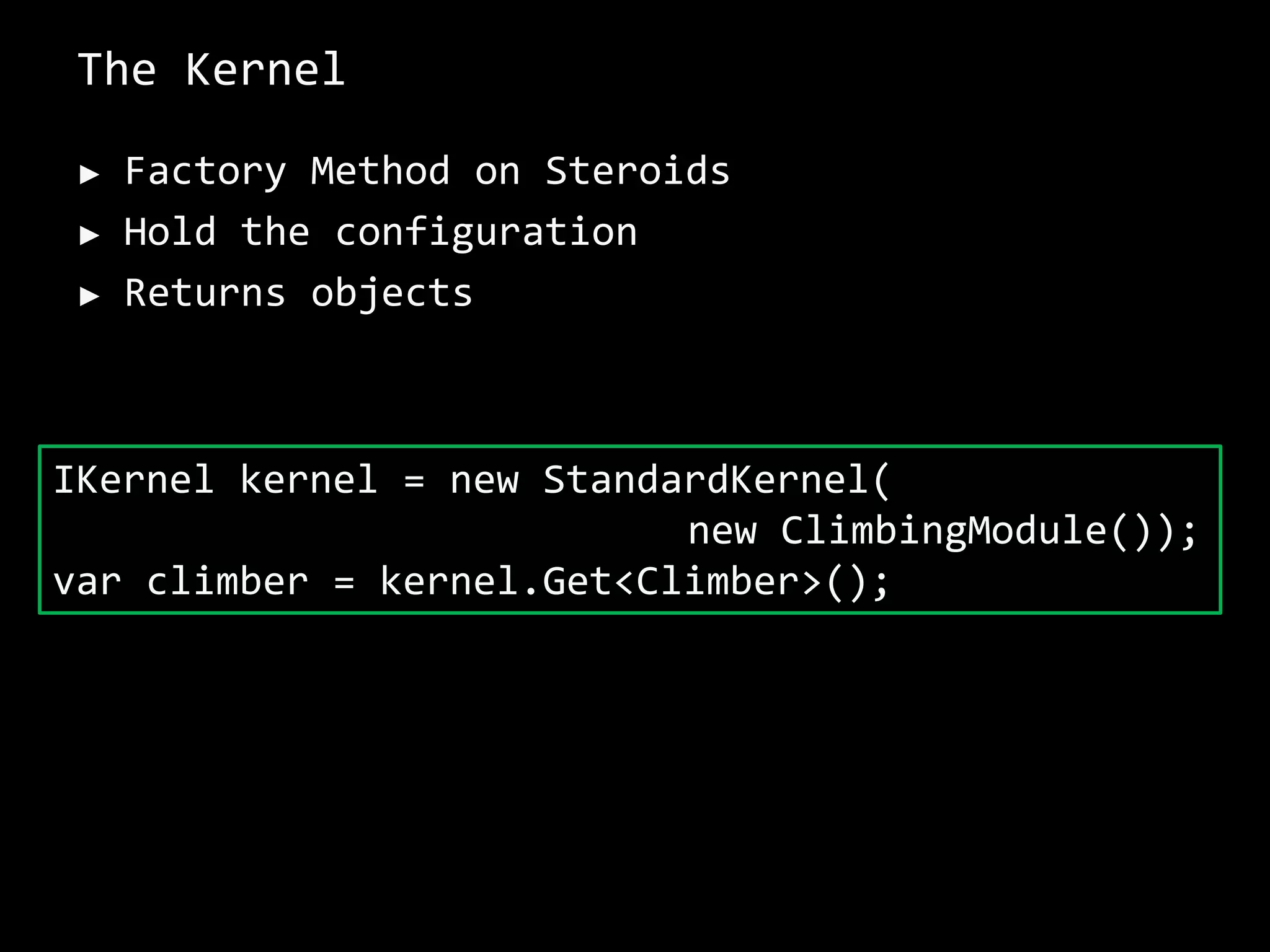
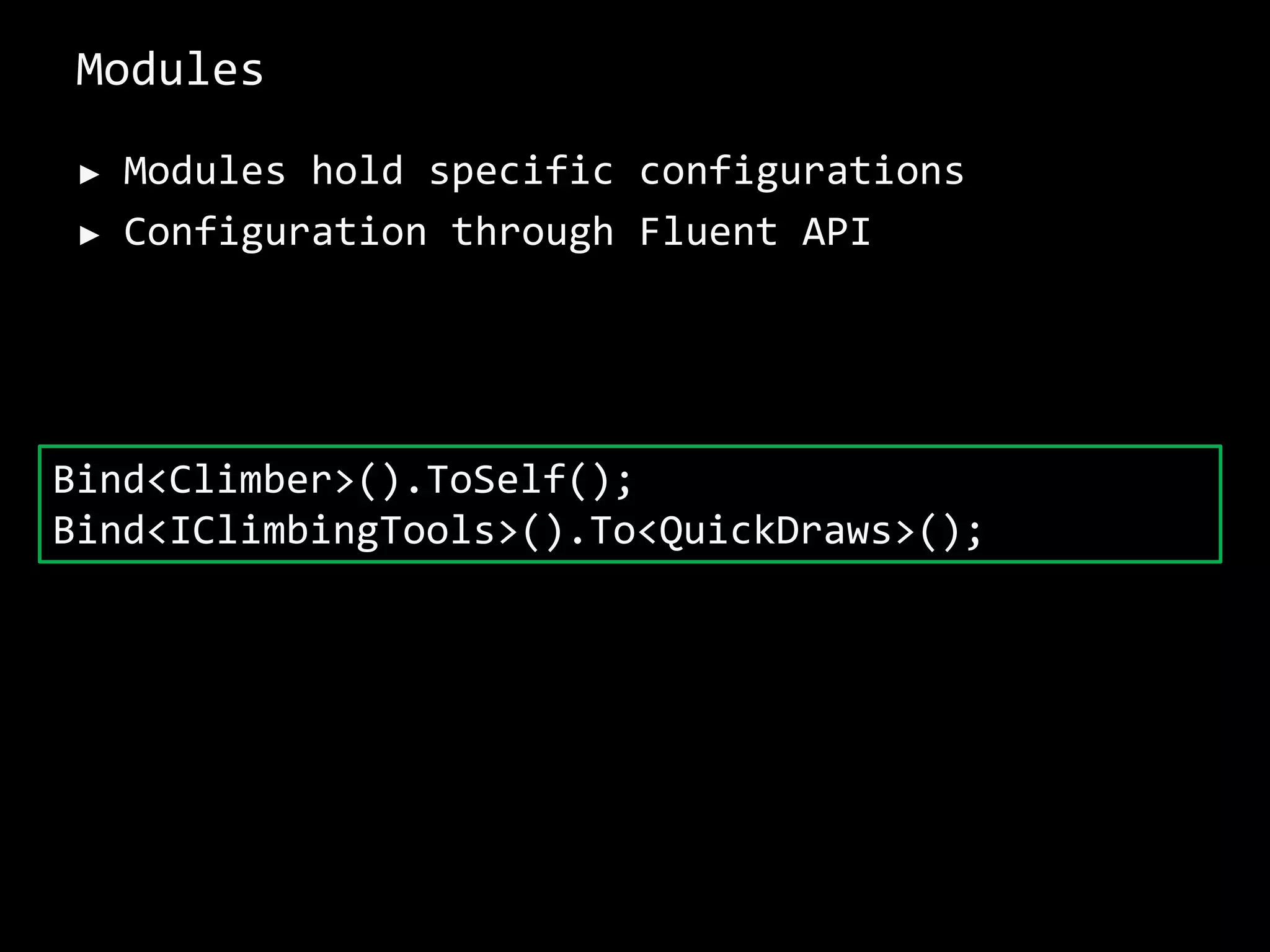
Simone Chiaretta gives a presentation on design for testability as a way to achieve good coding. He discusses principles of good design like high cohesion and low coupling. He then covers testability requirements and concepts like testing individual features in isolation. Chiaretta advocates for dependency injection and inversion of control as ways to achieve design for testability and thus good design. He demonstrates these concepts using examples in Ninject and Unity dependency injection frameworks.


![Attributes
► Are used to help discriminate injection
patterns
[Inject]
public IClimbingTools tools {get; set;}
[Inject]
public void GetReady(IClimbingTools tools)](https://image.slidesharecdn.com/bern-designfortestability-di-ioc-230326095707-40f841d9/75/SOLID-Code-52-2048.jpg)