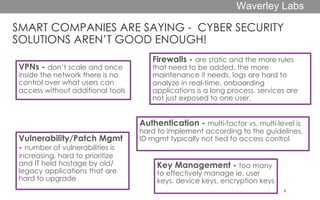
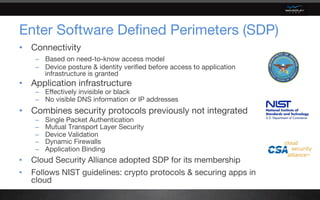
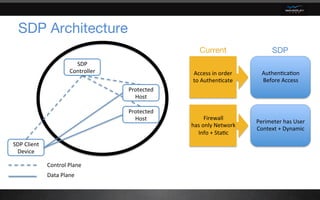
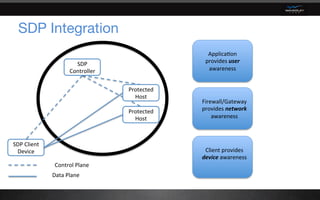
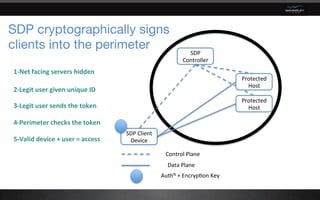
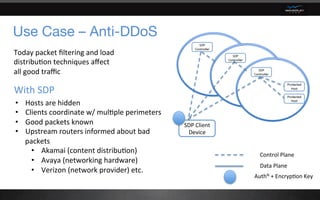
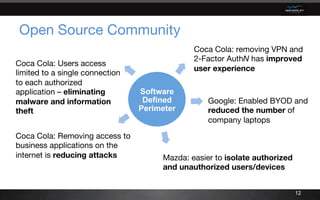
The document discusses Software Defined Perimeter (SDP) as a new approach to cybersecurity that reduces the attack surface. SDP implements a zero trust, need-to-know access model where device posture and identity are verified before access to application infrastructure is granted. It combines previously separate security protocols like single packet authentication and dynamic firewalls. This makes application infrastructure invisible to threats while cryptographically signing legitimate users and devices into a secure perimeter. The document provides examples of how SDP has benefits like simplified security, reduced costs, lower risk proportionate to effort, and improved user experience for companies.