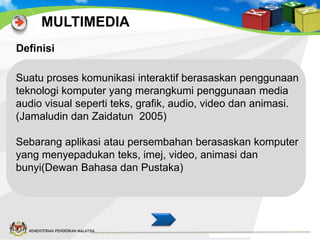
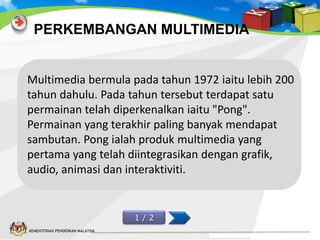
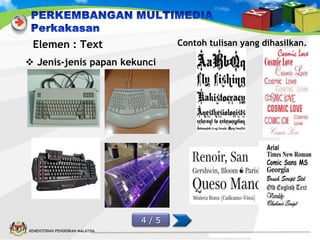
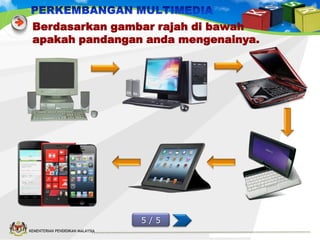
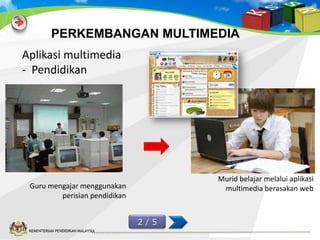
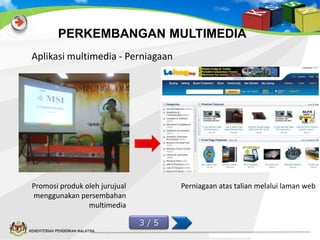
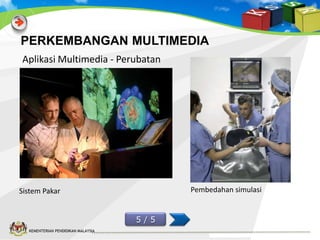
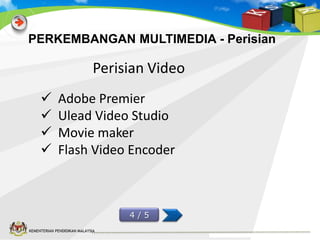
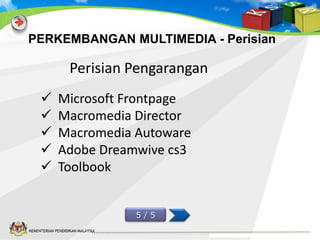
Dokumen ini memberikan definisi dan perkembangan multimedia, yang dimulai pada tahun 1972 dengan permainan 'Pong' sebagai produk multimedia pertama. Multimedia kini meliputi aplikasi dalam pendidikan, perniagaan, komunikasi, dan perubatan, dengan penggunaan teknologi audio, video, dan animasi. Terdapat juga penjelasan mengenai jenis perangkat keras dan perangkat lunak yang digunakan dalam produksi multimedia.