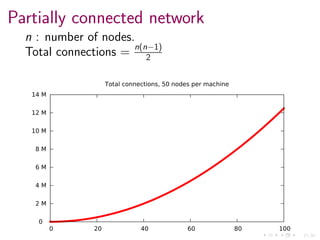
The document discusses the management of large, distributed systems using Erlang, drawing parallels with military strategies, particularly the Battle of Stalingrad. It focuses on the need for effective communication, adaptability amidst changing conditions, and a shared objective among nodes in the system. The spapi-router library is introduced as a solution to facilitate peer-to-peer communication within this distributed environment, optimizing network topology for better performance.

































![22/34
For example
pagebuilder@host3.fqdn
kernel stdlib
pagebuilder
spapi_router
kernel
stdlib
header
kernel
stdlib
mainsection
kernel
stdlib
mainsection
header@host1.fqdn
mainsec2@host2.fqdn
mainsec1@host1.fqdn
test2@host2.fqdn
kernel
stdlib
mainsection
Configuration of
pagebuilder@host3.fqdn:
{spapi_router, [
{host_names, [
"host1.fqdn",
"host2.fqdn",
]},
{workers, [
{"^header[0-9]*", [header]},
{"^mainsec[0-9]*", [mainsection]},
]}
]}](https://image.slidesharecdn.com/slides-140709120348-phpapp02/85/Large-Partially-connected-Erlang-Clusters-48-320.jpg)

![24/34
How it works
{spapi_router, [
{host_names, [
"host1.fqdn",
"host2.fqdn",
]},
{workers, [
{"^header[0-9]*", [header]},
{"^mainsec[0-9]*", [mainsection]},
]}
]}](https://image.slidesharecdn.com/slides-140709120348-phpapp02/85/Large-Partially-connected-Erlang-Clusters-50-320.jpg)
![24/34
How it works
{spapi_router, [
{host_names, [
"host1.fqdn",
"host2.fqdn",
]},
{workers, [
{"^header[0-9]*", [header]},
{"^mainsec[0-9]*", [mainsection]},
]}
]}
1. Connects to
host names](https://image.slidesharecdn.com/slides-140709120348-phpapp02/85/Large-Partially-connected-Erlang-Clusters-51-320.jpg)
![24/34
How it works
{spapi_router, [
{host_names, [
"host1.fqdn",
"host2.fqdn",
]},
{workers, [
{"^header[0-9]*", [header]},
{"^mainsec[0-9]*", [mainsection]},
]}
]}
1. Connects to
host names
2. Asks EPMD for
running nodes](https://image.slidesharecdn.com/slides-140709120348-phpapp02/85/Large-Partially-connected-Erlang-Clusters-52-320.jpg)
![24/34
How it works
{spapi_router, [
{host_names, [
"host1.fqdn",
"host2.fqdn",
]},
{workers, [
{"^header[0-9]*", [header]},
{"^mainsec[0-9]*", [mainsection]},
]}
]}
1. Connects to
host names
2. Asks EPMD for
running nodes
3. Connects to nodes
matching regexp](https://image.slidesharecdn.com/slides-140709120348-phpapp02/85/Large-Partially-connected-Erlang-Clusters-53-320.jpg)
![24/34
How it works
{spapi_router, [
{host_names, [
"host1.fqdn",
"host2.fqdn",
]},
{workers, [
{"^header[0-9]*", [header]},
{"^mainsec[0-9]*", [mainsection]},
]}
]}
1. Connects to
host names
2. Asks EPMD for
running nodes
3. Connects to nodes
matching regexp
4. Checks for
applications in
nodes](https://image.slidesharecdn.com/slides-140709120348-phpapp02/85/Large-Partially-connected-Erlang-Clusters-54-320.jpg)
![24/34
How it works
{spapi_router, [
{host_names, [
"host1.fqdn",
"host2.fqdn",
]},
{workers, [
{"^header[0-9]*", [header]},
{"^mainsec[0-9]*", [mainsection]},
]}
]}
1. Connects to
host names
2. Asks EPMD for
running nodes
3. Connects to nodes
matching regexp
4. Checks for
applications in
nodes
5. Connects to
relevant nodes](https://image.slidesharecdn.com/slides-140709120348-phpapp02/85/Large-Partially-connected-Erlang-Clusters-55-320.jpg)




![28/34
Calling others
spr_router:call(piqi_rpc, erlang, node, []).](https://image.slidesharecdn.com/slides-140709120348-phpapp02/85/Large-Partially-connected-Erlang-Clusters-60-320.jpg)
![28/34
Calling others
spr_router:call(piqi_rpc, erlang, node, []).
spr_router:call_all(piqi_rpc, erlang, node, []).](https://image.slidesharecdn.com/slides-140709120348-phpapp02/85/Large-Partially-connected-Erlang-Clusters-61-320.jpg)
![28/34
Calling others
spr_router:call(piqi_rpc, erlang, node, []).
spr_router:call_all(piqi_rpc, erlang, node, []).
Extras:
call/5
call all/5
list workers/0
list workers/1
list hosts/0](https://image.slidesharecdn.com/slides-140709120348-phpapp02/85/Large-Partially-connected-Erlang-Clusters-62-320.jpg)

![30/34
How to change nodes?
Puppet plus
RelUp
... or anything really:
spr app:config change([], [], []).](https://image.slidesharecdn.com/slides-140709120348-phpapp02/85/Large-Partially-connected-Erlang-Clusters-64-320.jpg)