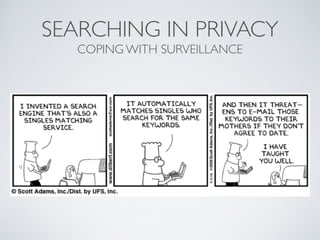
Searching in Privacy
•
0 likes•408 views
H
hnxThis document discusses privacy-enhanced search techniques. It begins by motivating the need for searching encrypted or remote data without revealing sensitive information to untrusted providers. It then outlines several approaches for private information retrieval and searching directly on encrypted data, including techniques using bloom filters and searchable symmetric encryption. Key properties and examples of each technique are provided.
Report
Share
Report
Share
Download to read offline
Recommended
CRYPTOGRAPHY AND NETWORK SECURITY

Discrete Logarithms – Computing discrete logs – Diffie-Hellman key exchange – ElGamal Public key cryptosystems – Hash functions – Secure Hash – Birthday attacks - MD5 – Digital signatures – RSA – ElGamal – DSA.
Sped mental ratardation

The ppt. presention includes a brief and concise definition of mental retardation, kinds of assessment, interventions, and practical advises on how to treat MRs.
Foscarini caboche

The Foscarini Design Workshop
offers lighting that evokes a flood of emotion through its purposeful designs. The company has a full stable of impressive, renowned, and progressively thinking designers, as well as collections to mirror those reputations. Collections like Big Bang and Caboche are as intricate as they are eye-catching, and can prove to be quite versatile as an element of design. Foscarini's other notable collections are Gregg and Havana, which both offer functional lighting with a focus on simplicity and modern design. Also, the Tress and Twiggy collections present an even more modern take on lighting design, while again offering simplicity in research based design.
Recommended
CRYPTOGRAPHY AND NETWORK SECURITY

Discrete Logarithms – Computing discrete logs – Diffie-Hellman key exchange – ElGamal Public key cryptosystems – Hash functions – Secure Hash – Birthday attacks - MD5 – Digital signatures – RSA – ElGamal – DSA.
Sped mental ratardation

The ppt. presention includes a brief and concise definition of mental retardation, kinds of assessment, interventions, and practical advises on how to treat MRs.
Foscarini caboche

The Foscarini Design Workshop
offers lighting that evokes a flood of emotion through its purposeful designs. The company has a full stable of impressive, renowned, and progressively thinking designers, as well as collections to mirror those reputations. Collections like Big Bang and Caboche are as intricate as they are eye-catching, and can prove to be quite versatile as an element of design. Foscarini's other notable collections are Gregg and Havana, which both offer functional lighting with a focus on simplicity and modern design. Also, the Tress and Twiggy collections present an even more modern take on lighting design, while again offering simplicity in research based design.
Moooi heracleum by bertjan pot

Started by acclaimed designers Marcel Wanders and Casper Vissers, Moooi has quickly developed a keen ability to produce some of the industrys most inspiring and truly innovative lighting products. Such products include Moooi lighting systems, like Heracleum, which was designed by Bertjan Pot, and collections like Raimond and Random Light.
Maintaining a healthy relationship with designers like Front, Freshwest, and Maarten Baas, has allowed Moooi to offer a number of additional design collections, like Non Random, and Dandelion, which are both cerebral and innovative in their own right. The brand also often works with other designers like Studio Job, and Ron Gilad.
While Mooois designs may focus heavily on lighting fixtures and suspension systems, like chandeliers and pendants, there are also several Moooi Lamps that give design lovers even more style to place on their surfaces.
Microsoft Dynamics NAV - as ERP Solution for Manufacturing Process

- Purchase Order Management.
- Sales Order Management.
- Production Orders.
- Supply Planning Capabilities in
Microsoft Dynamics NAV 2015.
- Sales/ Purchase Budgets.
- Demand Forecasting- Production Forecast.
- Supply Planning in Dynamics NAV.
- Requisition Management.
- Order Promising.
- Item Availability by Period.
- Item Availability by BOM Level.
- Production Bill of Materials.
- Calendars.
- Capacity Planning.
- Standard Cost Worksheet.
- Reporting Tool.
Lactancia materna

Resalta la importancia de la lactancia materna en nuestra sociedad promoviendo la salud e impulsando a las madres a dar el pecho a sus hijos
Permasalahan Lingkungan Hidup Lokal, Nasional dan Global 

permasalahan lingkungan yang dikaji secara lokal, nasional, dan global
Rapid Upper Limb Assessment (RULA) - Human Factors 

Rapid Upper Limb Assessment (RULA)- Human Factors
ERP : Arabized Microsoft dynamics NAV إدارة موارد المؤسسات

ERP : Arabized Microsoft dynamics NAV إدارة موارد المؤسسات
Isra@que-solutions.com
Teaching with questioning and answering method

Outline:
Categories of Questions
Uses of Questions
Types of Questions According to Purpose
Types of Questions According to Level
Characteristics of Good Questions
Questioning Skills and Conduct of Good Questioning
Handling Student’s Response & Handling Student’s Questions
Sequence of Questions
Digital Security 101

Fundamentals of digital security. Some info I made throughout the years as a refresher for digital security. Basic primer for beginners. If you are an expert, comments and feedbacks welcome.
Cassandra Summit 2014: Fuzzy Entity Matching at Scale

Presenter: Ken Krugler, President of Scale Unlimited
Early Warning has information on hundreds of millions of people and companies. When a person wants to open a new bank account, they need to be able to accurately find similar entities in this large dataset, to provide a risk assessment. Using the combination of Cassandra & Solr via DSE, they can quickly find and evaluate all reasonable candidates.
Osint, shoelaces, bubblegum

How To Use OSInt With Limited Time And Budget To Better Understand How Attackers See Your Organization
Detecting Malicious SSL Certificates Using Bro

We have developed a set of techniques to detect malicious SSL certificates using data collected by Bro. Our analysis framework consists of Bro for collecting the data and a variety of tools such as Splunk and AWS ML for data analysis. We show how we used Bro for collecting the attributes we needed for SSL certificates from both good and bad sources. Bro is a very effective and simple tool for analyzing and extracting data from network traffic.
Next, the extracted data was loaded into Splunk and we ran a series of Machine Learning algorithms to identify those attributes that correlated with malicious activity. The algorithms we used also allowed for categorization of certificates used in the delivery and control of malware. Our analysis showed that there were a number of patterns that emerged that allowed for classification of high-jacked devices, self-signed certificates, etc. We will present the results of our analysis which show which attributes are the most relevant for detecting malicious SSL certificates and as well the performance of the ML algorithms. Finally, we show how well the training has worked in detecting new malicious sources. All of the source code will be made available on github.
CNIT 126 13: Data Encoding

Slides for a college course at City College San Francisco. Based on "Practical Malware Analysis: The Hands-On Guide to Dissecting Malicious Software", by Michael Sikorski and Andrew Honig; ISBN-10: 1593272901.
Instructor: Sam Bowne
Class website: https://samsclass.info/126/126_S17.shtml
Test driving Azure Search and DocumentDB

This presentation describes what Azure Search and Azure DocumentDB is, where it fits, and how to use it.
Introduction to Neo4j and .Net

Complex hierarchical relationships between entities can only be mapped with difficulty in a relational database and demanding queries are usually quite slow.
Graph databases are optimized for exactly these kinds of relationships and can provide high-performance results even with huge amounts of data. Moreover, not only the entities that are stored in the database, have attributes, but also their relationships. Queries can look at entities as well as their relationships.
Get to know the basics of graph databases, using Neo4j as an example, and see how it is used C# projects.
More Related Content
Viewers also liked
Moooi heracleum by bertjan pot

Started by acclaimed designers Marcel Wanders and Casper Vissers, Moooi has quickly developed a keen ability to produce some of the industrys most inspiring and truly innovative lighting products. Such products include Moooi lighting systems, like Heracleum, which was designed by Bertjan Pot, and collections like Raimond and Random Light.
Maintaining a healthy relationship with designers like Front, Freshwest, and Maarten Baas, has allowed Moooi to offer a number of additional design collections, like Non Random, and Dandelion, which are both cerebral and innovative in their own right. The brand also often works with other designers like Studio Job, and Ron Gilad.
While Mooois designs may focus heavily on lighting fixtures and suspension systems, like chandeliers and pendants, there are also several Moooi Lamps that give design lovers even more style to place on their surfaces.
Microsoft Dynamics NAV - as ERP Solution for Manufacturing Process

- Purchase Order Management.
- Sales Order Management.
- Production Orders.
- Supply Planning Capabilities in
Microsoft Dynamics NAV 2015.
- Sales/ Purchase Budgets.
- Demand Forecasting- Production Forecast.
- Supply Planning in Dynamics NAV.
- Requisition Management.
- Order Promising.
- Item Availability by Period.
- Item Availability by BOM Level.
- Production Bill of Materials.
- Calendars.
- Capacity Planning.
- Standard Cost Worksheet.
- Reporting Tool.
Lactancia materna

Resalta la importancia de la lactancia materna en nuestra sociedad promoviendo la salud e impulsando a las madres a dar el pecho a sus hijos
Permasalahan Lingkungan Hidup Lokal, Nasional dan Global 

permasalahan lingkungan yang dikaji secara lokal, nasional, dan global
Rapid Upper Limb Assessment (RULA) - Human Factors 

Rapid Upper Limb Assessment (RULA)- Human Factors
ERP : Arabized Microsoft dynamics NAV إدارة موارد المؤسسات

ERP : Arabized Microsoft dynamics NAV إدارة موارد المؤسسات
Isra@que-solutions.com
Teaching with questioning and answering method

Outline:
Categories of Questions
Uses of Questions
Types of Questions According to Purpose
Types of Questions According to Level
Characteristics of Good Questions
Questioning Skills and Conduct of Good Questioning
Handling Student’s Response & Handling Student’s Questions
Sequence of Questions
Viewers also liked (11)
Microsoft Dynamics NAV - as ERP Solution for Manufacturing Process

Microsoft Dynamics NAV - as ERP Solution for Manufacturing Process
Permasalahan Lingkungan Hidup Lokal, Nasional dan Global 

Permasalahan Lingkungan Hidup Lokal, Nasional dan Global
Rapid Upper Limb Assessment (RULA) - Human Factors 

Rapid Upper Limb Assessment (RULA) - Human Factors
ERP : Arabized Microsoft dynamics NAV إدارة موارد المؤسسات

ERP : Arabized Microsoft dynamics NAV إدارة موارد المؤسسات
Similar to Searching in Privacy
Digital Security 101

Fundamentals of digital security. Some info I made throughout the years as a refresher for digital security. Basic primer for beginners. If you are an expert, comments and feedbacks welcome.
Cassandra Summit 2014: Fuzzy Entity Matching at Scale

Presenter: Ken Krugler, President of Scale Unlimited
Early Warning has information on hundreds of millions of people and companies. When a person wants to open a new bank account, they need to be able to accurately find similar entities in this large dataset, to provide a risk assessment. Using the combination of Cassandra & Solr via DSE, they can quickly find and evaluate all reasonable candidates.
Osint, shoelaces, bubblegum

How To Use OSInt With Limited Time And Budget To Better Understand How Attackers See Your Organization
Detecting Malicious SSL Certificates Using Bro

We have developed a set of techniques to detect malicious SSL certificates using data collected by Bro. Our analysis framework consists of Bro for collecting the data and a variety of tools such as Splunk and AWS ML for data analysis. We show how we used Bro for collecting the attributes we needed for SSL certificates from both good and bad sources. Bro is a very effective and simple tool for analyzing and extracting data from network traffic.
Next, the extracted data was loaded into Splunk and we ran a series of Machine Learning algorithms to identify those attributes that correlated with malicious activity. The algorithms we used also allowed for categorization of certificates used in the delivery and control of malware. Our analysis showed that there were a number of patterns that emerged that allowed for classification of high-jacked devices, self-signed certificates, etc. We will present the results of our analysis which show which attributes are the most relevant for detecting malicious SSL certificates and as well the performance of the ML algorithms. Finally, we show how well the training has worked in detecting new malicious sources. All of the source code will be made available on github.
CNIT 126 13: Data Encoding

Slides for a college course at City College San Francisco. Based on "Practical Malware Analysis: The Hands-On Guide to Dissecting Malicious Software", by Michael Sikorski and Andrew Honig; ISBN-10: 1593272901.
Instructor: Sam Bowne
Class website: https://samsclass.info/126/126_S17.shtml
Test driving Azure Search and DocumentDB

This presentation describes what Azure Search and Azure DocumentDB is, where it fits, and how to use it.
Introduction to Neo4j and .Net

Complex hierarchical relationships between entities can only be mapped with difficulty in a relational database and demanding queries are usually quite slow.
Graph databases are optimized for exactly these kinds of relationships and can provide high-performance results even with huge amounts of data. Moreover, not only the entities that are stored in the database, have attributes, but also their relationships. Queries can look at entities as well as their relationships.
Get to know the basics of graph databases, using Neo4j as an example, and see how it is used C# projects.
WLIA - 2015 Fall Regional, Oshkosh WI

Talk given at the 2015 Fall Regional in Oshkosh WI.
"An Approach to Address Parsing and Data Standardization"
Abstract:
Maintaining fully parsed address elements in your database can be one of the most beneficial steps toward
achieving quality and consistency in addressing. Parsed address elements also serve a preparatory step in
modeling an address toward NG9-1-1 supporting formats such as the FGDC address standard. In this talk,
we’ll take a look at the approach we’ve used for parsing site addresses for the V1 Statewide Parcel Map, the
role regular expressions played in this approach, and will unveil a suite of (free) ArcPy tools that can help you
parse addresses, standardize field values, and achieve other tasks.
Presenters:
Codie See
David Vogel
Practical Malware Analysis Ch13

Slides for CNIT 126 at City College San Francisco
Website: https://samsclass.info/126/126_S16.shtml
Relational Database Design Bootcamp

Nearly every application uses some sort of data storage. Proper data structure can lead to increased performance, reduced application complexity, and ensure data integrity. Foreign keys, indexes, and correct data types truly are your best friends when you respect them and use them for the correct purposes. Structuring data to be normalized and with the correct data types can lead to significant performance increases. Learn how to structure your tables to achieve normalization, performance, and integrity, by building a database from the ground up during this tutorial.
Privacy Protectin Models and Defamation caused by k-anonymity

Introduction of Privacy Protection Mathematical Models
are the topics of this slide. The Models explained are 1) Private Information Retrieval
, 2) IR with Homomorphic Encryption, 3)
k-anonymity, 4)
l-diversity, and finally 5)
Defamation caused by k-Anonymity
Intro to Cypher

This developer-focused webinar will explain how to use the Cypher graph query language. Cypher, a query language designed specifically for graphs, allows for expressing complex graph patterns using simple ASCII art-like notation and offers a simple but expressive approach for working with graph data.
During this webinar you'll learn:
-Basic Cypher syntax
-How to construct graph patterns using Cypher
-Querying existing data
-Data import with Cypher
-Using aggregations such as statistical functions
-Extending the power of Cypher using procedures and functions
Workshop - Best of Both Worlds_ Combine KG and Vector search for enhanced R...

These are the slides delivered in a workshop at Data Innovation Summit Stockholm April 2024, by Kristof Neys and Jonas El Reweny.
Similar to Searching in Privacy (20)
Cassandra Summit 2014: Fuzzy Entity Matching at Scale

Cassandra Summit 2014: Fuzzy Entity Matching at Scale
Privacy Protectin Models and Defamation caused by k-anonymity

Privacy Protectin Models and Defamation caused by k-anonymity
SqlDay 2018 - Brief introduction into SQL Server Execution Plans

SqlDay 2018 - Brief introduction into SQL Server Execution Plans
Workshop - Best of Both Worlds_ Combine KG and Vector search for enhanced R...

Workshop - Best of Both Worlds_ Combine KG and Vector search for enhanced R...
Recently uploaded
AI for Every Business: Unlocking Your Product's Universal Potential by VP of ...

AI for Every Business: Unlocking Your Product's Universal Potential by VP of Product, Slack
LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...

Do you want to learn how to model and simulate an electrical network from scratch in under an hour?
Then welcome to this PowSyBl workshop, hosted by Rte, the French Transmission System Operator (TSO)!
During the webinar, you will discover the PowSyBl ecosystem as well as handle and study an electrical network through an interactive Python notebook.
PowSyBl is an open source project hosted by LF Energy, which offers a comprehensive set of features for electrical grid modelling and simulation. Among other advanced features, PowSyBl provides:
- A fully editable and extendable library for grid component modelling;
- Visualization tools to display your network;
- Grid simulation tools, such as power flows, security analyses (with or without remedial actions) and sensitivity analyses;
The framework is mostly written in Java, with a Python binding so that Python developers can access PowSyBl functionalities as well.
What you will learn during the webinar:
- For beginners: discover PowSyBl's functionalities through a quick general presentation and the notebook, without needing any expert coding skills;
- For advanced developers: master the skills to efficiently apply PowSyBl functionalities to your real-world scenarios.
Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI): pav...

Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI)
Knowledge engineering: from people to machines and back

Keynote at the 21st European Semantic Web Conference
To Graph or Not to Graph Knowledge Graph Architectures and LLMs

Reflecting on new architectures for knowledge based systems in light of generative ai
UiPath Test Automation using UiPath Test Suite series, part 4

Welcome to UiPath Test Automation using UiPath Test Suite series part 4. In this session, we will cover Test Manager overview along with SAP heatmap.
The UiPath Test Manager overview with SAP heatmap webinar offers a concise yet comprehensive exploration of the role of a Test Manager within SAP environments, coupled with the utilization of heatmaps for effective testing strategies.
Participants will gain insights into the responsibilities, challenges, and best practices associated with test management in SAP projects. Additionally, the webinar delves into the significance of heatmaps as a visual aid for identifying testing priorities, areas of risk, and resource allocation within SAP landscapes. Through this session, attendees can expect to enhance their understanding of test management principles while learning practical approaches to optimize testing processes in SAP environments using heatmap visualization techniques
What will you get from this session?
1. Insights into SAP testing best practices
2. Heatmap utilization for testing
3. Optimization of testing processes
4. Demo
Topics covered:
Execution from the test manager
Orchestrator execution result
Defect reporting
SAP heatmap example with demo
Speaker:
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

The IoT and OT threat landscape report has been prepared by the Threat Research Team at Sectrio using data from Sectrio, cyber threat intelligence farming facilities spread across over 85 cities around the world. In addition, Sectrio also runs AI-based advanced threat and payload engagement facilities that serve as sinks to attract and engage sophisticated threat actors, and newer malware including new variants and latent threats that are at an earlier stage of development.
The latest edition of the OT/ICS and IoT security Threat Landscape Report 2024 also covers:
State of global ICS asset and network exposure
Sectoral targets and attacks as well as the cost of ransom
Global APT activity, AI usage, actor and tactic profiles, and implications
Rise in volumes of AI-powered cyberattacks
Major cyber events in 2024
Malware and malicious payload trends
Cyberattack types and targets
Vulnerability exploit attempts on CVEs
Attacks on counties – USA
Expansion of bot farms – how, where, and why
In-depth analysis of the cyber threat landscape across North America, South America, Europe, APAC, and the Middle East
Why are attacks on smart factories rising?
Cyber risk predictions
Axis of attacks – Europe
Systemic attacks in the Middle East
Download the full report from here:
https://sectrio.com/resources/ot-threat-landscape-reports/sectrio-releases-ot-ics-and-iot-security-threat-landscape-report-2024/
Leading Change strategies and insights for effective change management pdf 1.pdf

Leading Change strategies and insights for effective change management pdf 1.pdf
Securing your Kubernetes cluster_ a step-by-step guide to success !

Today, after several years of existence, an extremely active community and an ultra-dynamic ecosystem, Kubernetes has established itself as the de facto standard in container orchestration. Thanks to a wide range of managed services, it has never been so easy to set up a ready-to-use Kubernetes cluster.
However, this ease of use means that the subject of security in Kubernetes is often left for later, or even neglected. This exposes companies to significant risks.
In this talk, I'll show you step-by-step how to secure your Kubernetes cluster for greater peace of mind and reliability.
Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024

As AI technology is pushing into IT I was wondering myself, as an “infrastructure container kubernetes guy”, how get this fancy AI technology get managed from an infrastructure operational view? Is it possible to apply our lovely cloud native principals as well? What benefit’s both technologies could bring to each other?
Let me take this questions and provide you a short journey through existing deployment models and use cases for AI software. On practical examples, we discuss what cloud/on-premise strategy we may need for applying it to our own infrastructure to get it to work from an enterprise perspective. I want to give an overview about infrastructure requirements and technologies, what could be beneficial or limiting your AI use cases in an enterprise environment. An interactive Demo will give you some insides, what approaches I got already working for real.
Essentials of Automations: Optimizing FME Workflows with Parameters

Are you looking to streamline your workflows and boost your projects’ efficiency? Do you find yourself searching for ways to add flexibility and control over your FME workflows? If so, you’re in the right place.
Join us for an insightful dive into the world of FME parameters, a critical element in optimizing workflow efficiency. This webinar marks the beginning of our three-part “Essentials of Automation” series. This first webinar is designed to equip you with the knowledge and skills to utilize parameters effectively: enhancing the flexibility, maintainability, and user control of your FME projects.
Here’s what you’ll gain:
- Essentials of FME Parameters: Understand the pivotal role of parameters, including Reader/Writer, Transformer, User, and FME Flow categories. Discover how they are the key to unlocking automation and optimization within your workflows.
- Practical Applications in FME Form: Delve into key user parameter types including choice, connections, and file URLs. Allow users to control how a workflow runs, making your workflows more reusable. Learn to import values and deliver the best user experience for your workflows while enhancing accuracy.
- Optimization Strategies in FME Flow: Explore the creation and strategic deployment of parameters in FME Flow, including the use of deployment and geometry parameters, to maximize workflow efficiency.
- Pro Tips for Success: Gain insights on parameterizing connections and leveraging new features like Conditional Visibility for clarity and simplicity.
We’ll wrap up with a glimpse into future webinars, followed by a Q&A session to address your specific questions surrounding this topic.
Don’t miss this opportunity to elevate your FME expertise and drive your projects to new heights of efficiency.
Epistemic Interaction - tuning interfaces to provide information for AI support

Paper presented at SYNERGY workshop at AVI 2024, Genoa, Italy. 3rd June 2024
https://alandix.com/academic/papers/synergy2024-epistemic/
As machine learning integrates deeper into human-computer interactions, the concept of epistemic interaction emerges, aiming to refine these interactions to enhance system adaptability. This approach encourages minor, intentional adjustments in user behaviour to enrich the data available for system learning. This paper introduces epistemic interaction within the context of human-system communication, illustrating how deliberate interaction design can improve system understanding and adaptation. Through concrete examples, we demonstrate the potential of epistemic interaction to significantly advance human-computer interaction by leveraging intuitive human communication strategies to inform system design and functionality, offering a novel pathway for enriching user-system engagements.
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

Effective Application Security in Software Delivery lifecycle using Deployment Firewall and DBOM
The modern software delivery process (or the CI/CD process) includes many tools, distributed teams, open-source code, and cloud platforms. Constant focus on speed to release software to market, along with the traditional slow and manual security checks has caused gaps in continuous security as an important piece in the software supply chain. Today organizations feel more susceptible to external and internal cyber threats due to the vast attack surface in their applications supply chain and the lack of end-to-end governance and risk management.
The software team must secure its software delivery process to avoid vulnerability and security breaches. This needs to be achieved with existing tool chains and without extensive rework of the delivery processes. This talk will present strategies and techniques for providing visibility into the true risk of the existing vulnerabilities, preventing the introduction of security issues in the software, resolving vulnerabilities in production environments quickly, and capturing the deployment bill of materials (DBOM).
Speakers:
Bob Boule
Robert Boule is a technology enthusiast with PASSION for technology and making things work along with a knack for helping others understand how things work. He comes with around 20 years of solution engineering experience in application security, software continuous delivery, and SaaS platforms. He is known for his dynamic presentations in CI/CD and application security integrated in software delivery lifecycle.
Gopinath Rebala
Gopinath Rebala is the CTO of OpsMx, where he has overall responsibility for the machine learning and data processing architectures for Secure Software Delivery. Gopi also has a strong connection with our customers, leading design and architecture for strategic implementations. Gopi is a frequent speaker and well-known leader in continuous delivery and integrating security into software delivery.
Transcript: Selling digital books in 2024: Insights from industry leaders - T...

The publishing industry has been selling digital audiobooks and ebooks for over a decade and has found its groove. What’s changed? What has stayed the same? Where do we go from here? Join a group of leading sales peers from across the industry for a conversation about the lessons learned since the popularization of digital books, best practices, digital book supply chain management, and more.
Link to video recording: https://bnctechforum.ca/sessions/selling-digital-books-in-2024-insights-from-industry-leaders/
Presented by BookNet Canada on May 28, 2024, with support from the Department of Canadian Heritage.
Generating a custom Ruby SDK for your web service or Rails API using Smithy

Have you ever wanted a Ruby client API to communicate with your web service? Smithy is a protocol-agnostic language for defining services and SDKs. Smithy Ruby is an implementation of Smithy that generates a Ruby SDK using a Smithy model. In this talk, we will explore Smithy and Smithy Ruby to learn how to generate custom feature-rich SDKs that can communicate with any web service, such as a Rails JSON API.
From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP...

From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP of Product, Amplitude
Connector Corner: Automate dynamic content and events by pushing a button

Here is something new! In our next Connector Corner webinar, we will demonstrate how you can use a single workflow to:
Create a campaign using Mailchimp with merge tags/fields
Send an interactive Slack channel message (using buttons)
Have the message received by managers and peers along with a test email for review
But there’s more:
In a second workflow supporting the same use case, you’ll see:
Your campaign sent to target colleagues for approval
If the “Approve” button is clicked, a Jira/Zendesk ticket is created for the marketing design team
But—if the “Reject” button is pushed, colleagues will be alerted via Slack message
Join us to learn more about this new, human-in-the-loop capability, brought to you by Integration Service connectors.
And...
Speakers:
Akshay Agnihotri, Product Manager
Charlie Greenberg, Host
UiPath Test Automation using UiPath Test Suite series, part 3

Welcome to UiPath Test Automation using UiPath Test Suite series part 3. In this session, we will cover desktop automation along with UI automation.
Topics covered:
UI automation Introduction,
UI automation Sample
Desktop automation flow
Pradeep Chinnala, Senior Consultant Automation Developer @WonderBotz and UiPath MVP
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...

From Siloed Products to Connected Ecosystem: Building a Sustainable and Scalable Platform by VP of Product, The New York Times
Accelerate your Kubernetes clusters with Varnish Caching

A presentation about the usage and availability of Varnish on Kubernetes. This talk explores the capabilities of Varnish caching and shows how to use the Varnish Helm chart to deploy it to Kubernetes.
This presentation was delivered at K8SUG Singapore. See https://feryn.eu/presentations/accelerate-your-kubernetes-clusters-with-varnish-caching-k8sug-singapore-28-2024 for more details.
Recently uploaded (20)
AI for Every Business: Unlocking Your Product's Universal Potential by VP of ...

AI for Every Business: Unlocking Your Product's Universal Potential by VP of ...
LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...

LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...
Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI): pav...

Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI): pav...
Knowledge engineering: from people to machines and back

Knowledge engineering: from people to machines and back
To Graph or Not to Graph Knowledge Graph Architectures and LLMs

To Graph or Not to Graph Knowledge Graph Architectures and LLMs
UiPath Test Automation using UiPath Test Suite series, part 4

UiPath Test Automation using UiPath Test Suite series, part 4
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

State of ICS and IoT Cyber Threat Landscape Report 2024 preview
Leading Change strategies and insights for effective change management pdf 1.pdf

Leading Change strategies and insights for effective change management pdf 1.pdf
Securing your Kubernetes cluster_ a step-by-step guide to success !

Securing your Kubernetes cluster_ a step-by-step guide to success !
Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024

Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024
Essentials of Automations: Optimizing FME Workflows with Parameters

Essentials of Automations: Optimizing FME Workflows with Parameters
Epistemic Interaction - tuning interfaces to provide information for AI support

Epistemic Interaction - tuning interfaces to provide information for AI support
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...
Transcript: Selling digital books in 2024: Insights from industry leaders - T...

Transcript: Selling digital books in 2024: Insights from industry leaders - T...
Generating a custom Ruby SDK for your web service or Rails API using Smithy

Generating a custom Ruby SDK for your web service or Rails API using Smithy
From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP...

From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP...
Connector Corner: Automate dynamic content and events by pushing a button

Connector Corner: Automate dynamic content and events by pushing a button
UiPath Test Automation using UiPath Test Suite series, part 3

UiPath Test Automation using UiPath Test Suite series, part 3
From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...

From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...
Accelerate your Kubernetes clusters with Varnish Caching

Accelerate your Kubernetes clusters with Varnish Caching
Searching in Privacy
- 1. SEARCHING IN PRIVACY COPING WITH SURVEILLANCE
- 2. OVERVIEW • Motivation • Types of privacy-enhanced search • Search by Example
- 3. MOTIVATION • Use remote / untrusted storage for any data • Protect your data
- 4. REMOTE / UNTRUSTED STORAGE • What if you don’t trust the storage provider ? • Encrypt • What if you want to use a search provider but don’t trust them ? • What if you want to search your encrypted data ?
- 5. WHAT IFYOU WANTTO SEARCH YOUR ENCRYPTED DATA ? Naïve approach: Server sends you everything
- 6. WHAT IFYOU WANTTO SEARCH YOUR ENCRYPTED DATA ? Can we do better ?
- 7. TYPES OF PRIVACY-ENHANCED SEARCH • Private Information Retrieval (PIR) • Search on encrypted data
- 8. PRIVATE INFORMATION RETRIEVAL (PIR) • Server should not learn what you are looking for • Server may or may not have access to searchable data
- 9. SEARCH ON ENCRYPTED DATA • Server should not learn anything about your data • Especially not learn anything when you are searching
- 10. ADDRESS BOOK MATCHING Naïve approach • Normalize, then send to server
- 11. ADDRESS BOOK MATCHING Naïve approach • Normalize, then send to server JUST DON’T.
- 12. ADDRESS BOOK MATCHING Better approach • Hash your data. Like WhatsApp, or Gravatar. • Still guessable (e-mail addresses) • Gravatar tracking • Still pre-computable (phone numbers) • Steal the database or match what you like
- 13. ADDRESS BOOK MATCHING Hash (social) connections • My phone number m, friend's number f • Hash: h(min(m, f), max(m, f)) • Both ends must have the other contact in the address book to match • Anybody can confirm your connections
- 14. ADDRESS BOOK MATCHING Hash (phone # | e-mail) || (first | last name) • Common names (e.g. John) still easily retrievable • Users have to enter their own name (besides phone no.) for others to find them • Contacts must contain first name & last name
- 15. ADDRESS BOOK MATCHING BLOOM FILTERS Setup • Compute m-bit vector from k independent hash functions with range [1…m] of all entries to match • Hashes need not be cryptographically secure, just independent
- 16. ADDRESS BOOK MATCHING BLOOM FILTERS 1 1 1 h1(p) = i1 h2(p) = i2 h3(p) = i3 h4(p) = i4 1 …………… position i3 m bits
- 17. ADDRESS BOOK MATCHING BLOOM FILTERS Properties: • Never any false negatives • n insertions • Probability of bit = 0: (1 - 1/m)kn • False positive rate: (1 - e-kn/m)k
- 18. KEYWORD SEARCH SEARCHABLE SYMMETRIC KEY ENCRYPTION Properties: • Probabilistic search • False positives with probability 1/2 m per word, i.e. L/2 m for a document with L words • n insertions • Probability of bit being zero: (1 - 1/m) kn • False positive rate: (1 - e -kn/m ) k
- 19. SSKE BASIC SCHEME Setup • Break document into L words W1...WL, either with • n bits (padded; leaks word count) or • with length information (leaks word & document lengths) • PRG (stream cipher with key k' that only client knows) • S1...SL with (n - m) bits each • Keyed PRF Fki(x) maps (n - m) bits to m bits W1 W2 Wi WL… …
- 20. SSKE BASIC SCHEME Setup • Ti := Si || Fki(Si) • Ciphertext Ci := Wi ⊕ Ti • Send encrypted document to server Si Fki(Si) Wi ⊕ Ci C1 C2 Ci CL… …
- 21. SSKE BASIC SCHEME Search for keyword wj • Tell server • wj • ki for all locations i (with Wi) to search
- 22. SSKE BASIC SCHEME Search for keyword wj • Server computes Ci ⊕ wj • If Ci ⊕ wj = s || Fki(s), yield s for all locations i • Client can decrypt s and check for false positives
- 23. SSKE BASIC SCHEME Problems • Linear search effort, inefficient for real-world documents with different word lengths • Client reveals ki of searched subset and wj
- 24. SSKE BASIC SCHEME Improvement • Use PRG G to generate ki := GK(Wi), K secret key • Does not depend on i but only on K and Wi • Reveal wj and GK(wj) for lookup • Still reveals keyword wj
- 25. SSKE BASIC SCHEME Second improvement: Setup • Encrypt all words in document xi := Esk(Wi) • Split each word xi into Li with (n - m) and Ri with m bits • Now generate ki := GK(Li) • Ci := xi ⊕ Ti
- 26. SSKE BASIC SCHEME Search • Tell server • xj • kj := GK(Lj)
- 27. QUESTIONS ?
- 28. REFERENCES • https://whispersystems.org/blog/contact-discovery/ • http://www.cs.berkeley.edu/~dawnsong/papers/ se.pdf • http://www.csd.uoc.gr/~hy590-82/lecture9-se.ppt • https://crypto.stanford.edu/~eujin/papers/ secureindex/2003nov-encsearch.pdf
- 29. IMAGE SOURCES • http://www.cominvent.com/wp-content/uploads/2008/02/ dilbert-searchengine.gif • http://i3.asn.im/Overloaded-truck-_tshp.jpg • http://www.hairofthedogdave.com/wp/wp-content/ uploads/2008/11/yes-we-can.jpg • http://www.8-bitcentral.com/blog/2013/allMyHeart.html • https://oeilsj.files.wordpress.com/2011/02/nike_swoosh.gif