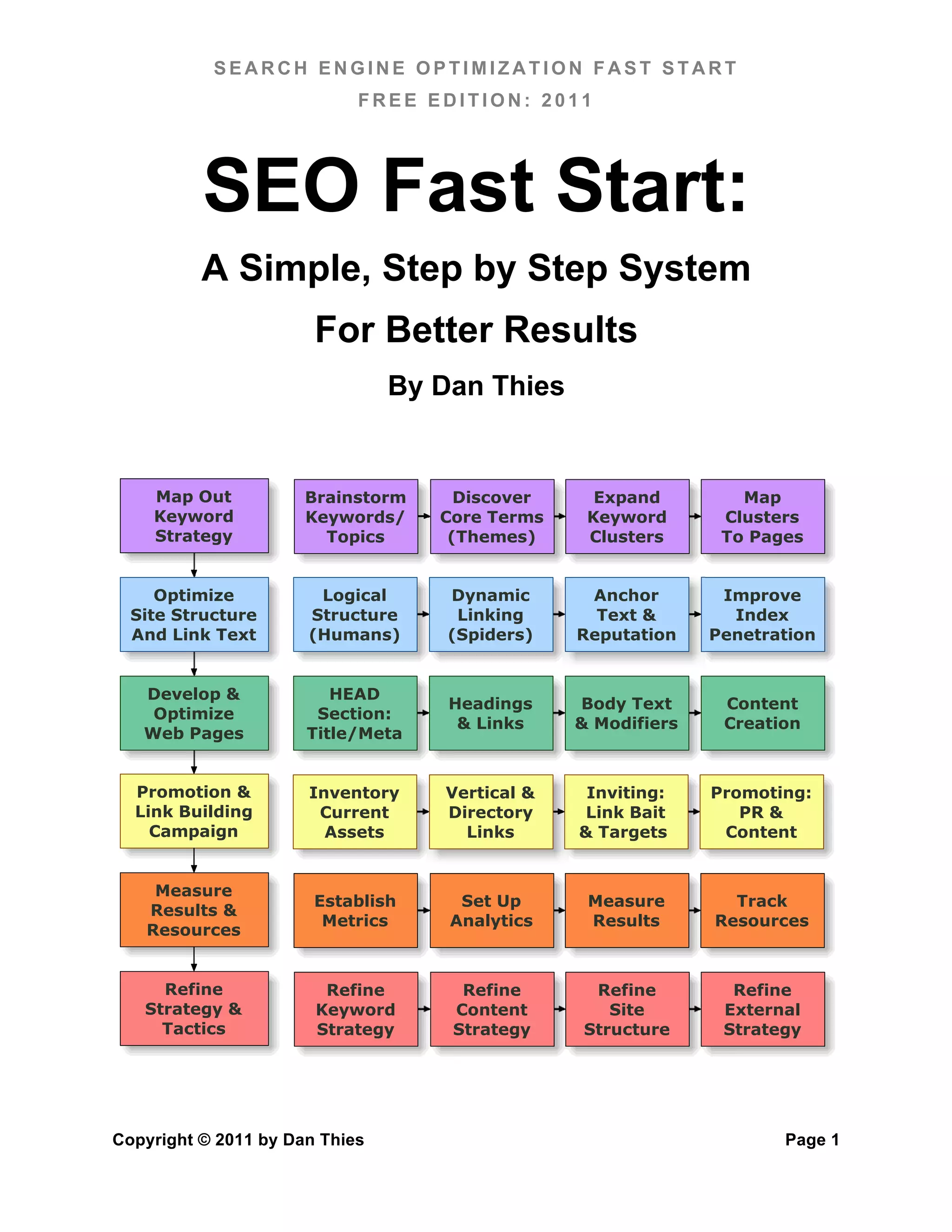
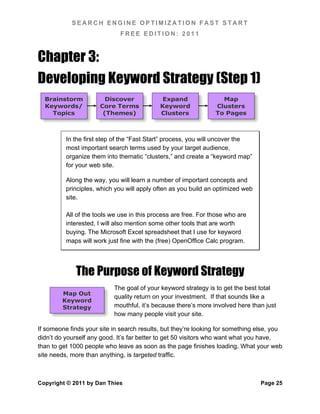
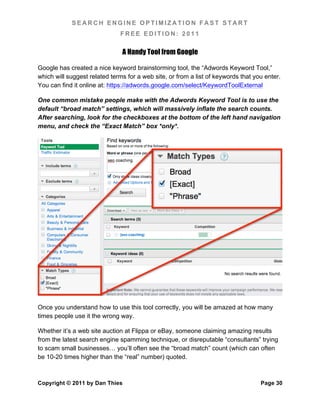
This document provides an overview and table of contents for the book "Search Engine Optimization Fast Start" by Dan Thies. It discusses how search engine optimization has changed over the past decade but the core "fast start" system remains useful. The book is separated into two sections, with the free edition covering the fundamentals of SEO and the "pro section" including more advanced techniques. The book guides readers through a six step framework for SEO including developing keyword strategies, optimizing site structure and content, link building, measuring results, and refining strategies. It aims to simplify SEO without secrets or gimmicks.