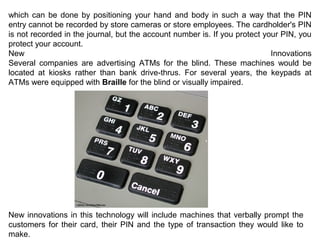
An ATM, or automated teller machine, allows bank customers to access their accounts and perform transactions like withdrawing cash or checking balances without interacting with a human teller. The document provides a history of the first ATM, how ATMs work by connecting to bank networks, common security features of ATMs, and tips for safe ATM usage. Modern ATMs use encryption and other technologies to securely process transactions and protect customers' financial information.