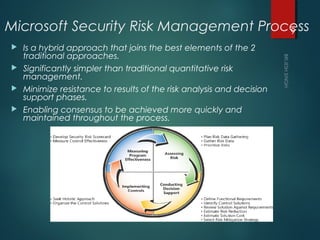
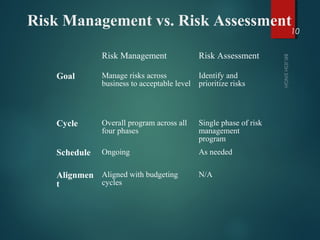
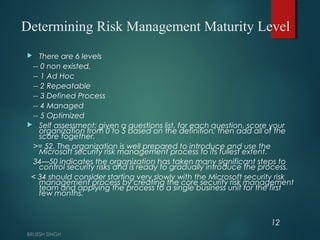
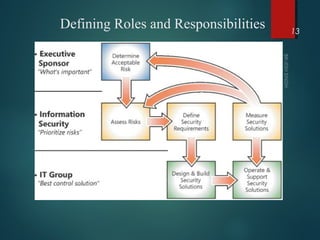
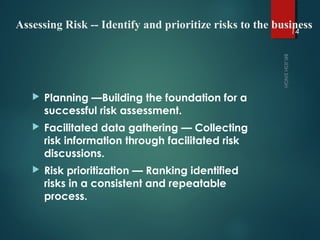
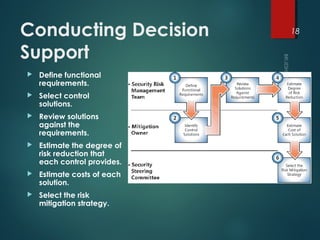
This document provides an overview of security risk management. It discusses reactive versus proactive approaches, and quantitative versus qualitative risk prioritization. The key steps of the security risk management process include assessing risks, conducting decision support, implementing controls, and measuring effectiveness. When assessing risks, organizations should plan the assessment, gather data through facilitated discussions, and prioritize risks. Both quantitative and qualitative approaches have benefits and drawbacks.