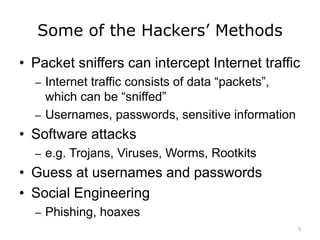
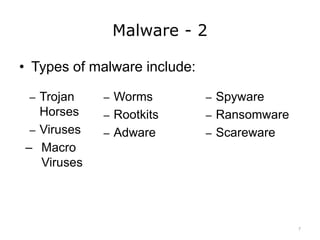
This lecture discusses common methods of cyberattack and types of malware. Some methods of attack explored include packet sniffing to intercept internet traffic, software attacks like trojans and viruses, and social engineering through phishing and hoaxes. Common types of malware described are trojans, viruses, worms, rootkits, adware, spyware, and ransomware. Social engineering methods used by cybercriminals like phishing are also explained.
![Security and Privacy
References – Lecture b
References
Macro language - computer definition. (n.d.). Retrieved July 10, 2016, from
http://www.yourdictionary.com/macro-language
Malware. (n.d.). In Wikipedia. Retrieved July 10, 2016, from
https://en.wikipedia.org/wiki/Malware
Images
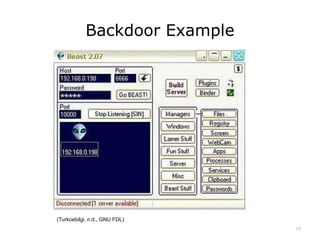
Slide 17: Screenshot of Beast 2.07 malware. (n.d.). Turkcebilgi. Retrieved from
https://www.turkcebilgi.com/kötücül_yazılım_(malware) [Turkish]. This file is licensed
through the GNU Free Documentation License.
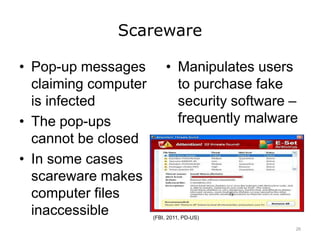
Slide 26: Scareware image. (2011, June 22). In ‘Scareware’ Distributors Targeted.
Federal Bureau of Investigation. Retrieved April 18, 2016, from
https://www.fbi.gov/news/stories/scareware-distributors-targeted.
32](https://image.slidesharecdn.com/comp4unit7blectureslides-201103145532/85/Security-Privacy-Lecture-B-32-320.jpg)