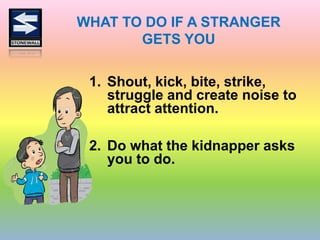
The document is a security awareness program designed for children, emphasizing the importance of recognizing and protecting themselves from potential dangers in their environment. It outlines various safety tips, such as not talking to strangers, protecting personal information, and seeking help from trusted adults. The program encourages parental involvement in teaching children emergency procedures and safety measures.