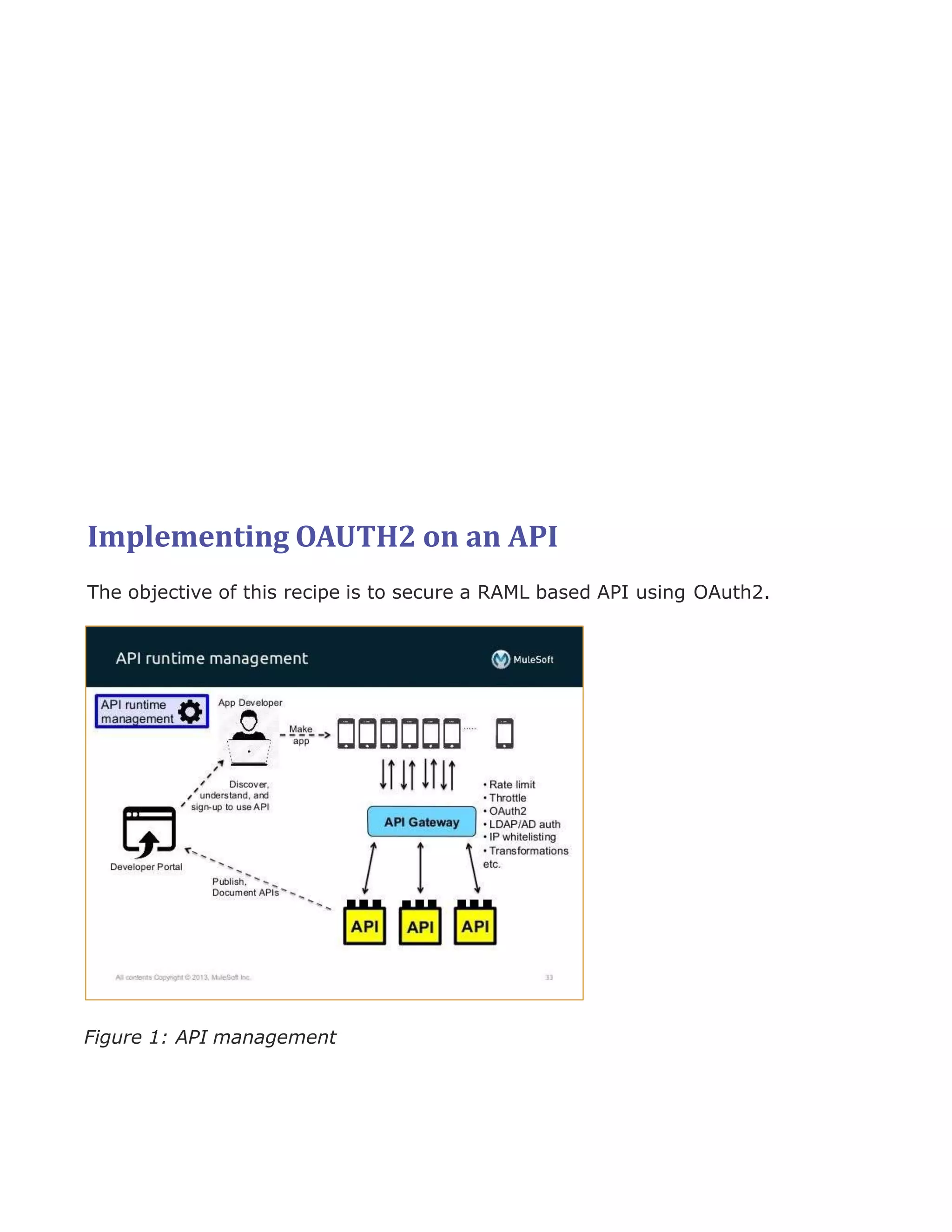
The document describes how to implement OAuth2 authentication on an API using Anypoint Platform. It involves:
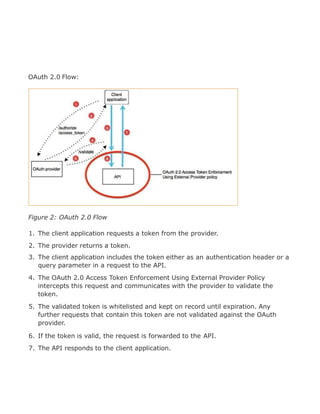
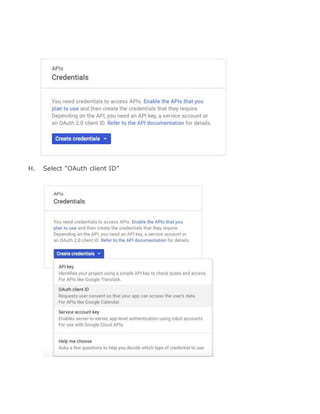
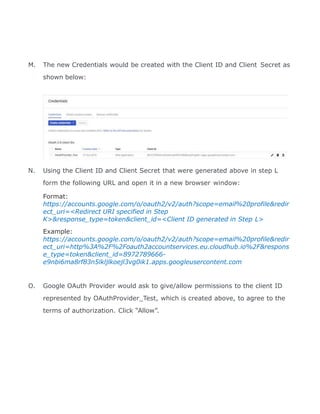
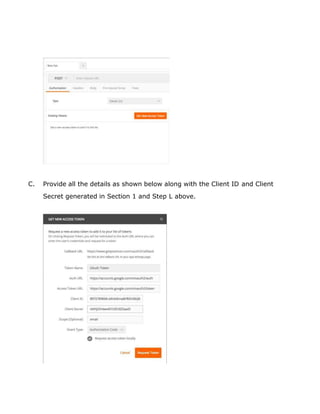
1. Enabling an OAuth2 provider (Google in this case) by registering a client ID and secret.
2. Applying an OAuth2 policy to the API specification to require valid access tokens.
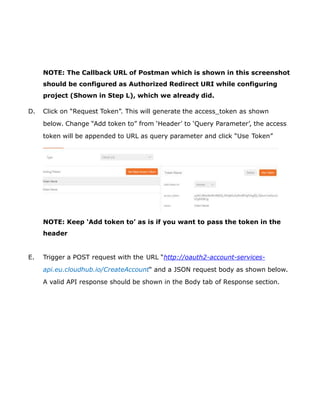
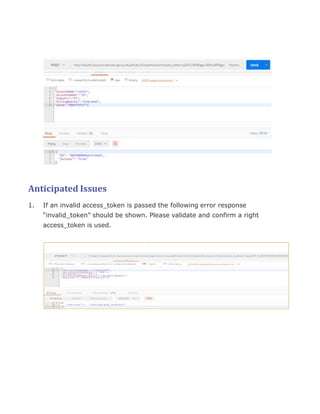
3. Testing the secured API by obtaining an access token from the provider and including it in requests.