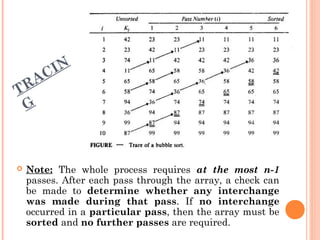
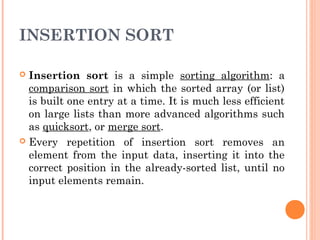
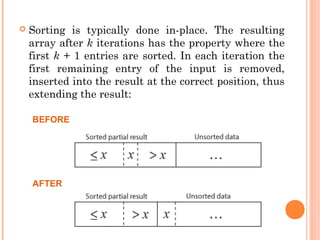
The document describes various searching and sorting techniques including linear search, binary search, selection sort, bubble sort, and insertion sort. Each algorithm is outlined with its respective procedure for searching or sorting an array, detailing the steps involved and illustrating examples. It emphasizes the efficiency and requirements of each method in handling unordered data.
![ALGORITHM:
SEQSEARCH (K, N, X) – Given an unordered array K of N
elements, this algorithm searches the array for a particular
element having value X. The given algorithm returns the index
(position) of the required element if the search is successful,
and returns 0 otherwise.
1. [Initialize search]
I 1
2. [Search the array]
Repeat while K[I] ≠ X
I I + 1
3. [Is the search successful?]
if I > N
then Write (‘UNSUCCESSFUL SEARCH’)
Return (0)
else Write (‘SUCCESSFUL SEARCH’)
Return (I)](https://image.slidesharecdn.com/searchingsorting-131010131451-phpapp02/85/Data-Structures-Searching-sorting-3-320.jpg)
![BINARYSEARCH (K, N, X) – Given an array K of size N arranged in
ascending order, this algorithm searches the array for a given
element whose value is given by X. The variables LOW, MIDDLE and
HIGH denote the lower, middle and upper limits of the search
interval, respectively.
1. [Initialize]
LOW 1
HIGH N
2. [Perform search]
Repeat thru step 4 while LOW <= HIGH
3. [Obtain index of midpoint of interval]
MIDDLE (LOW + HIGH) / 2
4. [Compare]
If X < K [MIDDLE]
then HIGH MIDDLE – 1
else if X > K[MIDDLE]
then LOW MIDDLE + 1
else Write (‘SUCCESSFUL SEARCH’)
Return (MIDDLE)
5. [Unsuccessful Search]
Write (‘UNSUCCESSFUL SEARCH’)
Return (0)](https://image.slidesharecdn.com/searchingsorting-131010131451-phpapp02/85/Data-Structures-Searching-sorting-5-320.jpg)
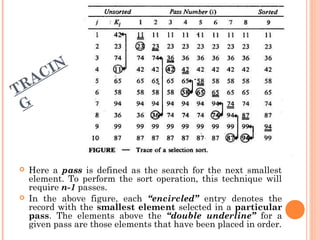
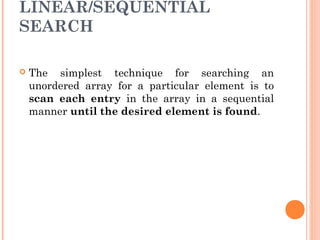
![SELECTIONSORT (K, N) – Given an array K of size N, this procedure
rearranges the elements of array in ascending order. The variable
PASS represents the pass index and the position of the first element in
the array which is to be examined during a particular pass. The
variable MIN_INDEX shows the position of the smallest element
encountered till now in a particular pass. The variable I is used to
index elements from PASS to N in a given pass.
1. [Create a loop for n-1 passes]
Repeat thru step 4 for PASS = 1, 2, …, N - 1
2. [Initialize MIN_INDEX to first element of each pass]
MIN_INDEX PASS
3. [Make a pass and obtain element with smallest value]
Repeat for I = PASS + 1, PASS + 2, …, N
If K[I[ < K[MIN_INDEX]
Then MIN_INDEX I
4. [Exchange smallest element with first element of each pass]
If MIN_INDEX ≠ PASS
Then K[PASS] ↔ K[MIN_INDEX] (Interchange)
5. [Finished]
Return](https://image.slidesharecdn.com/searchingsorting-131010131451-phpapp02/85/Data-Structures-Searching-sorting-9-320.jpg)
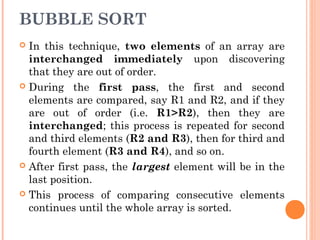
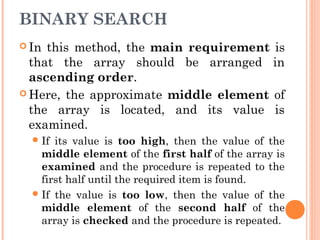
![BUBBLESORT (K, N) – Given an array K of size N, this procedure rearranges the
elements of array in ascending order. PASS and LAST variables are used for the
pass counter and position of the last unsorted element, respectively. The variable I
is used to index the elements of array. The variable EXCHS is used to count the
number of interchanges made on any pass.
1. [Initialize]
LAST N
2. [Create a loop for the passes]
Repeat thru step 5 for PASS = 1, 2, …, N - 1
3. [Initialize counter for no of interchanges for this pass]
EXCHS 0
4. [Perform pair-wise comparisons on unsorted consecutive elements]
Repeat for I = 1, 2, … LAST-1
If K[I[ > K[I+1]
Then K[I] ↔ K[I+1] (Interchange elements)
EXCHS EXCHS + 1
5. [Check if any interchange was made on this pass]
If EXCHS = 0
Then Return (Array Sorted; Return early)
Else
LAST LAST – 1 (Reduce size of unsorted list)
6. [Finished]
Return](https://image.slidesharecdn.com/searchingsorting-131010131451-phpapp02/85/Data-Structures-Searching-sorting-12-320.jpg)
![InsSort(A[1…N]) –
For i = 2 to N
{
temp = A[i]
j = i-1
while(j>0 and temp<A[j])
{
A[j+1] = A[j]
j = j-1
}
A[j+1] = temp
}
ALGORITHM:](https://image.slidesharecdn.com/searchingsorting-131010131451-phpapp02/85/Data-Structures-Searching-sorting-16-320.jpg)