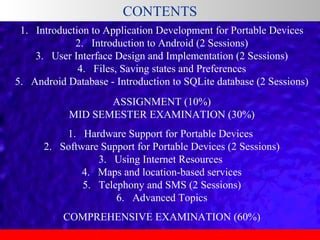
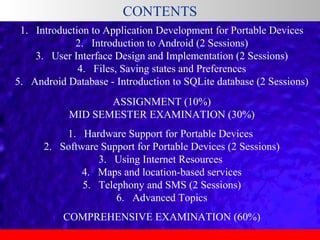
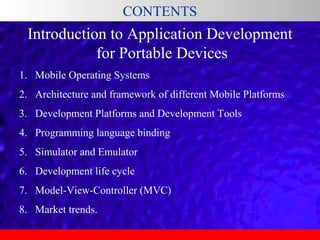
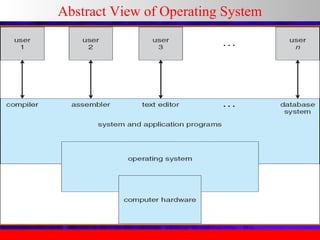
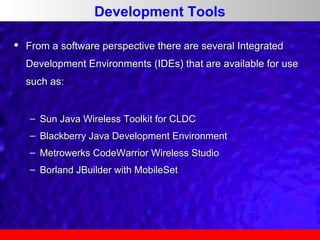
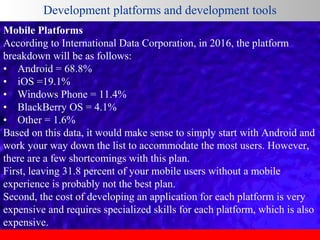
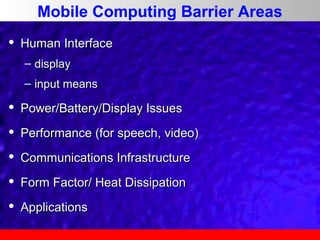
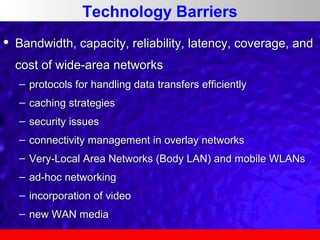
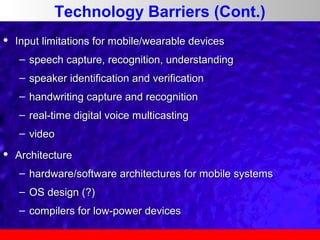
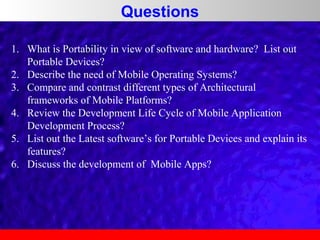
This document outlines a course on software development for portable devices. It covers topics like introduction to mobile operating systems, application development frameworks, programming languages, emulators and simulators, and the development lifecycle. It discusses challenges like device heterogeneity, security, and networks. Solutions involve optimizing for varying screen sizes, memory constraints, processing power, and input methods. It also addresses network issues like transmission errors, latency, and bandwidth usage through techniques like error correction, caching messages, and minimizing data transfer.