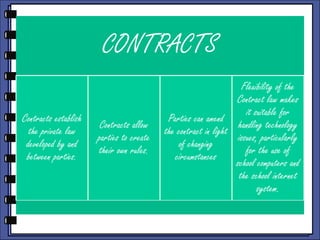
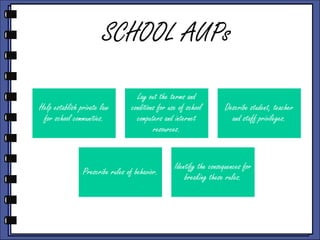
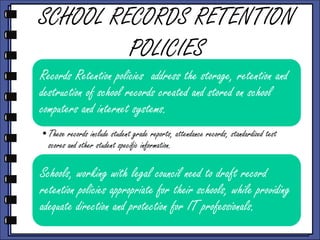
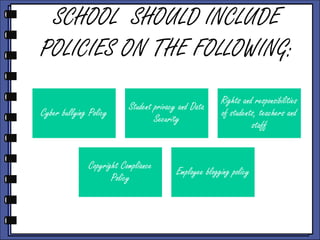
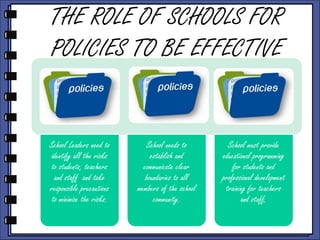
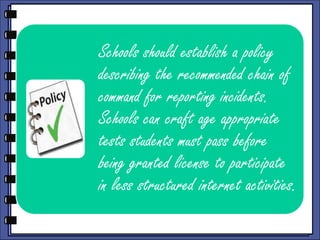
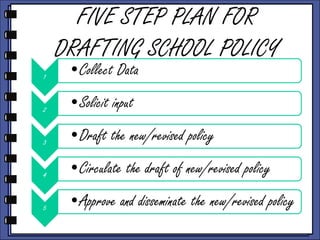
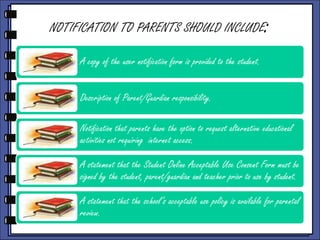
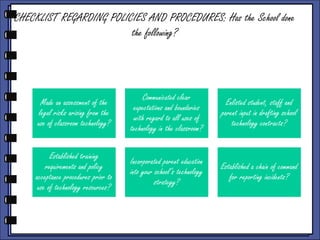
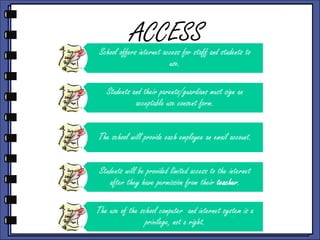
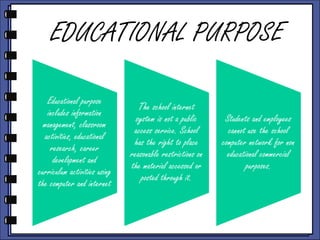
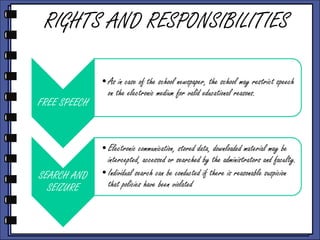
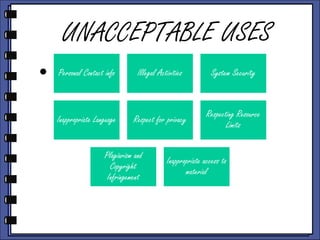
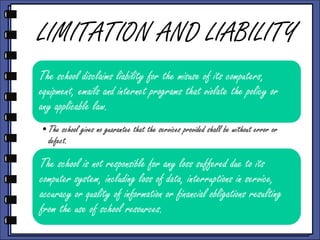
The document discusses school policies, procedures, and contracts regarding technology use. It emphasizes that well-crafted policies lay out expectations, define rights and responsibilities, and describe consequences for violations. Acceptable use policies, bullying policies, and other agreements between the school and community form binding contracts. The document provides guidance on creating, updating, and disseminating policies to effectively govern appropriate technology use by students and staff.