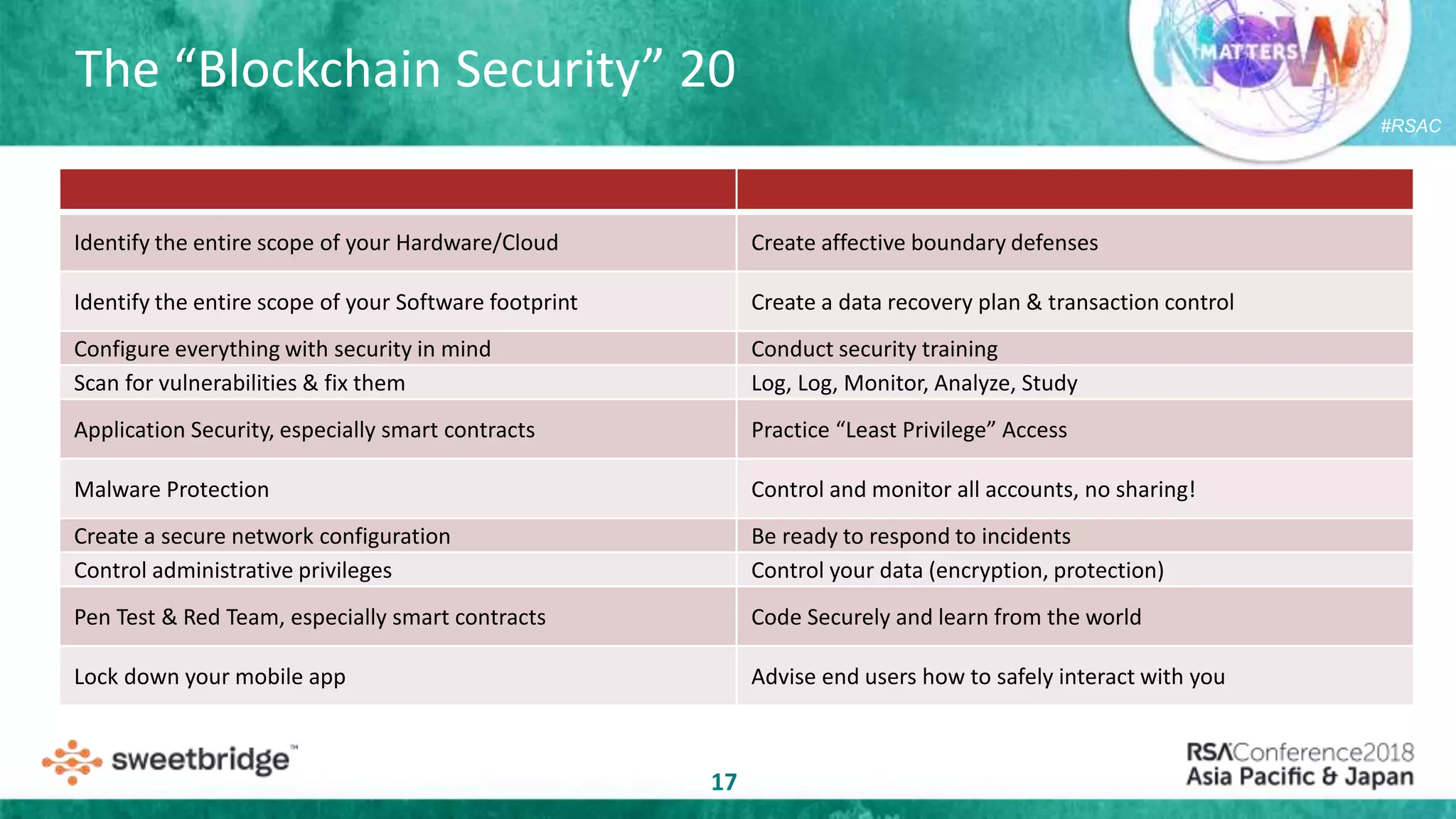
Scott Carlson discusses the uniqueness of blockchain security compared to traditional systems, emphasizing the elimination of third-party trust and the potential for anonymity. He outlines various motivations for using cryptocurrencies and the importance of robust security measures in blockchain projects due to associated risks. Carlson also suggests proactive strategies for ensuring blockchain security, including rigorous training, vulnerability scanning, and incident response preparations.

![#RSAC
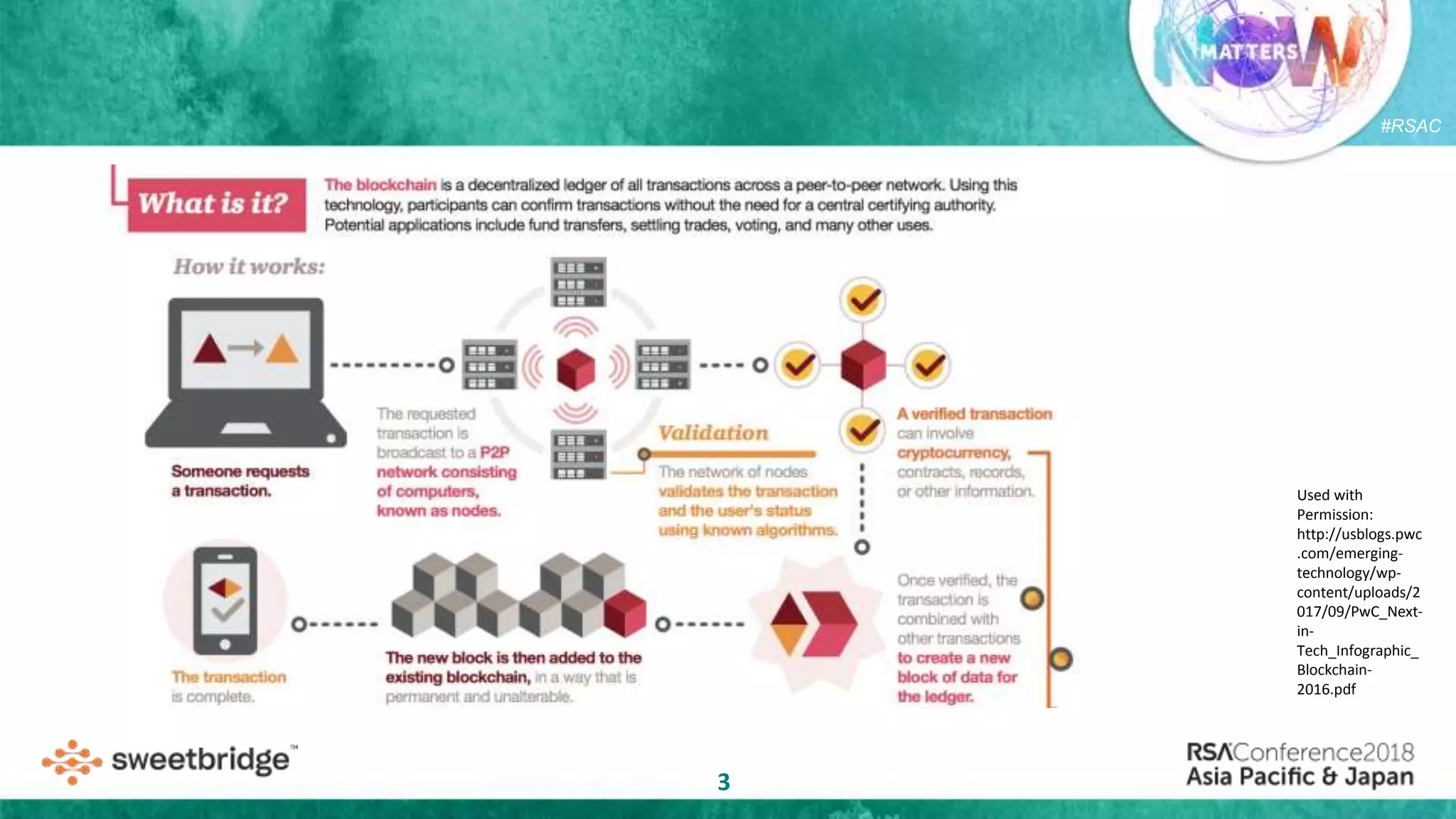
Blockchain [ Ethereum, NEO, Cardano ]
Smart Contracts / Keys / API Logic
End User Facing ”Interface”
Blockchain
”layers”
Blockchain projects almost always have a
public/private chain, contracts/logic, and
applications facing API/Users](https://image.slidesharecdn.com/carlsonblockchainrsaapj2018-181213001248/75/RSA-APJ-BLOCKCHAIN-SECURITY-IS-IT-REALLY-DIFFERENT-THAN-ANYTHING-ELSE-12-2048.jpg)