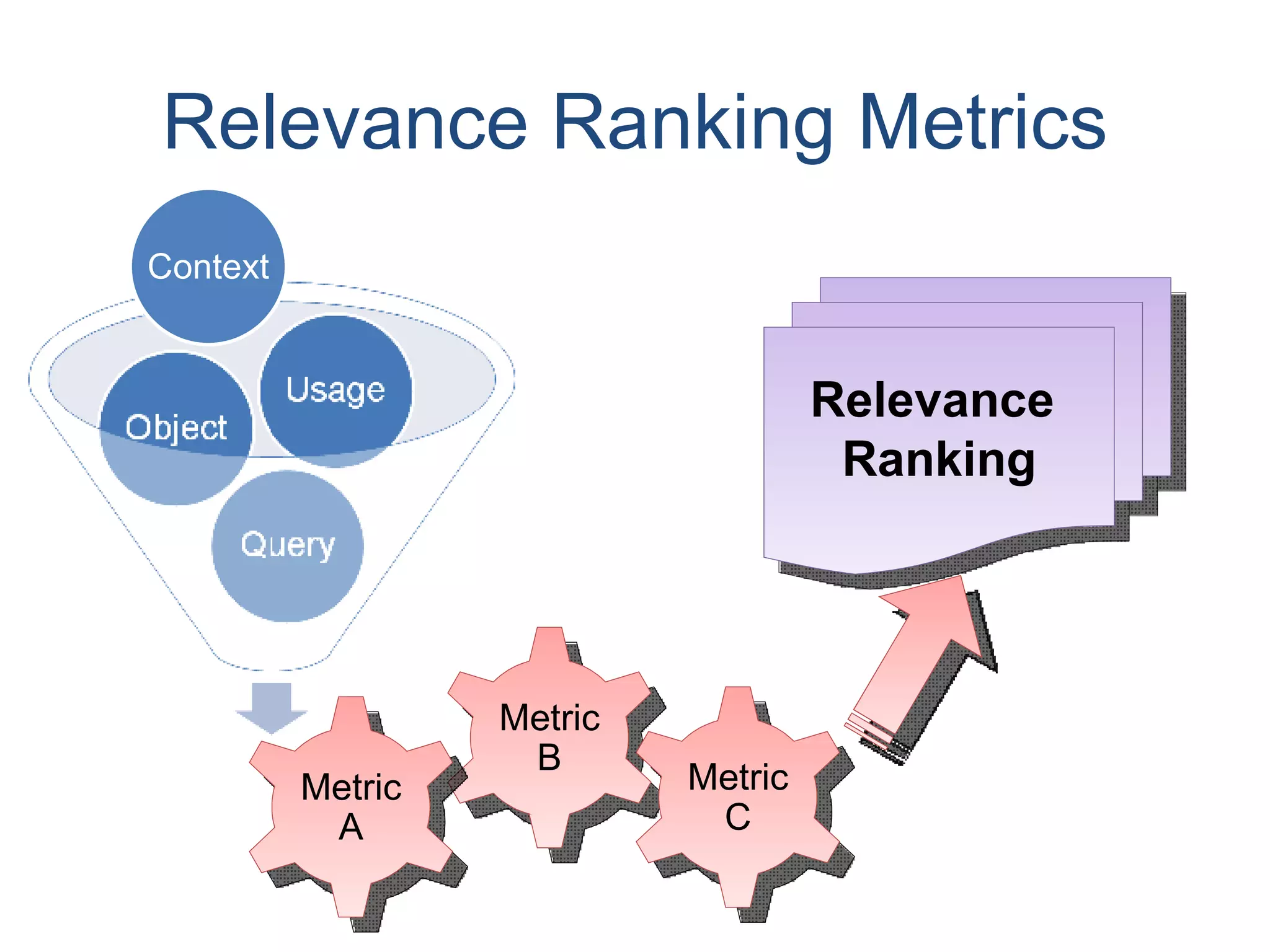
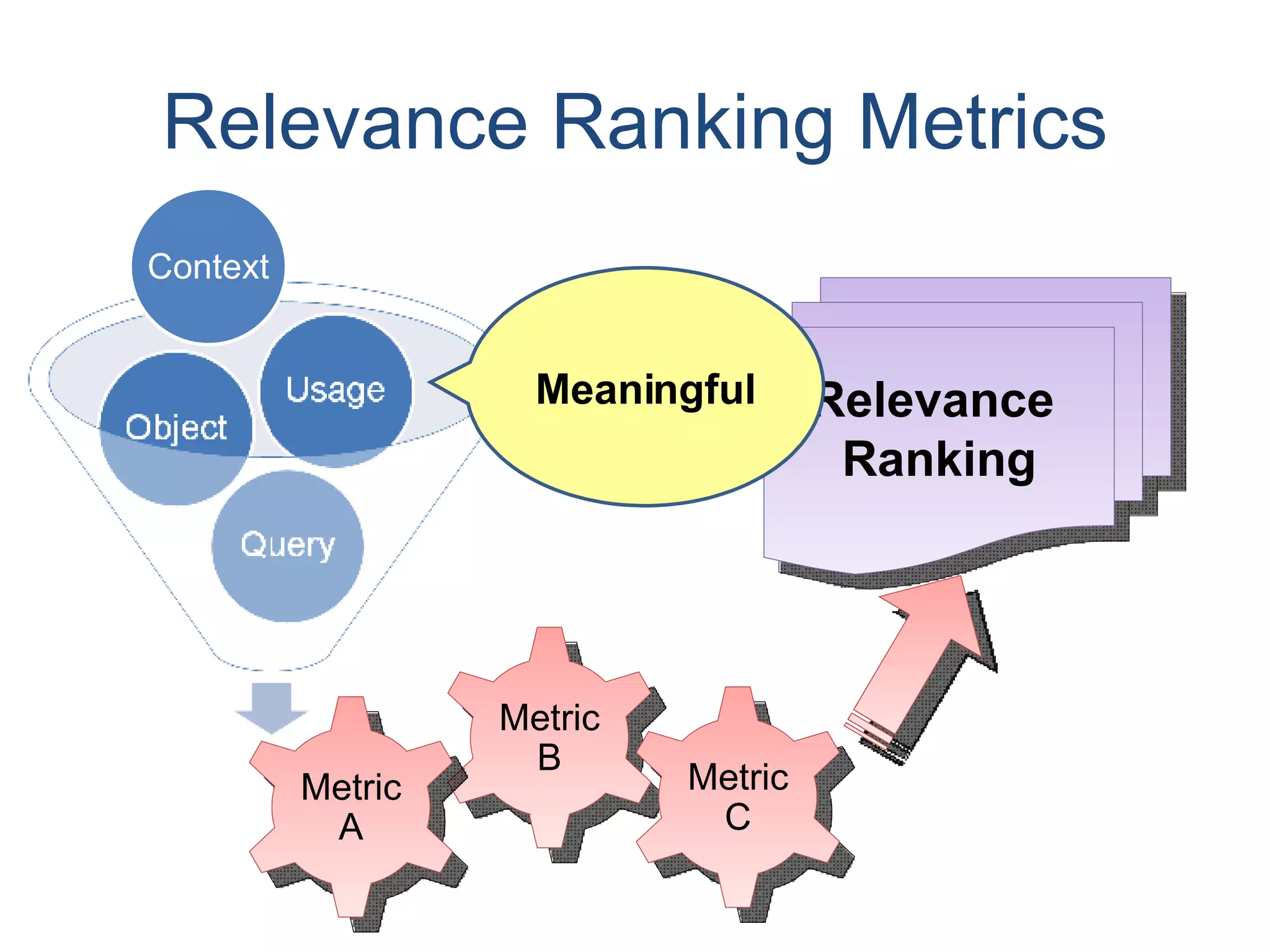
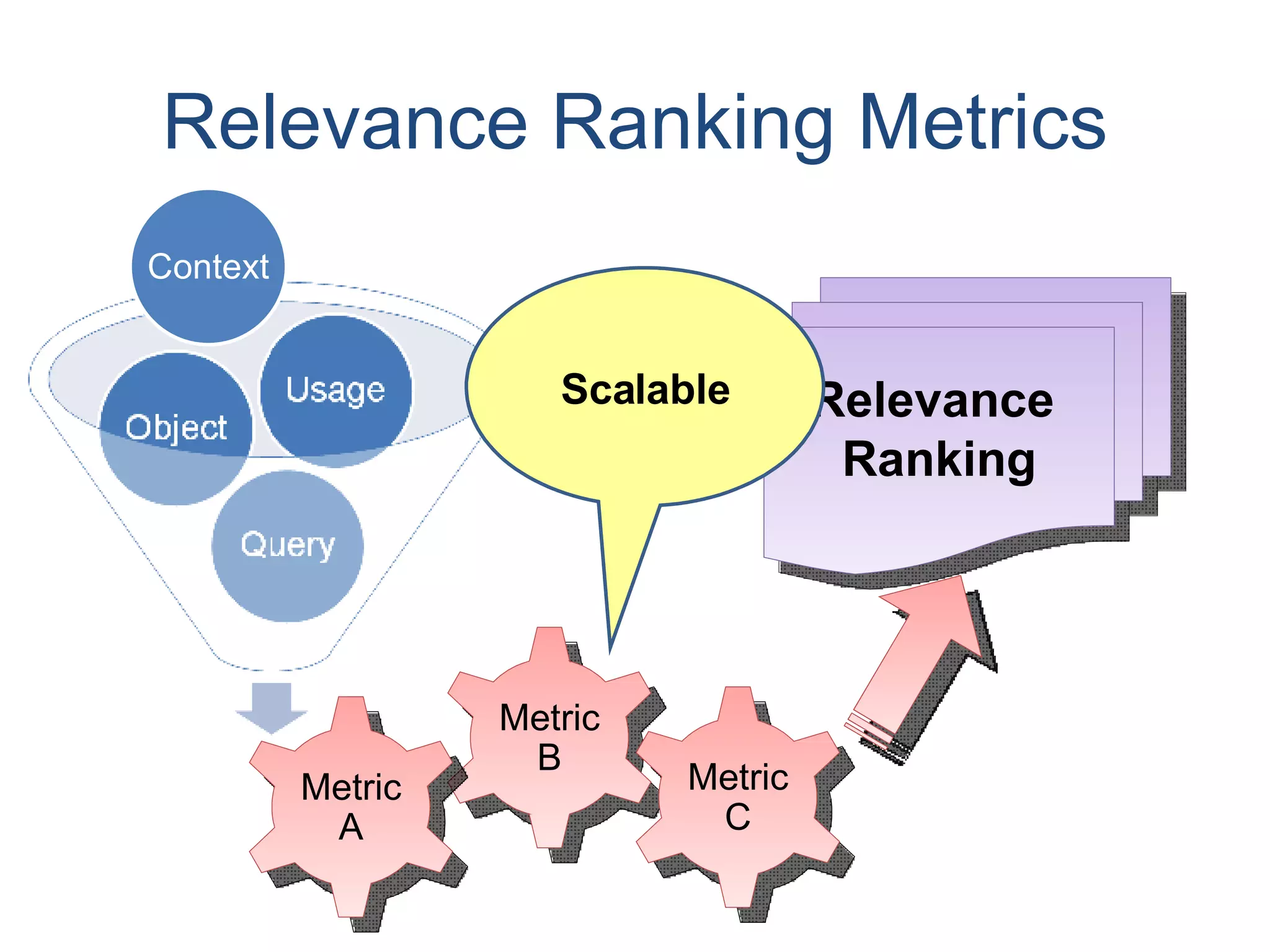
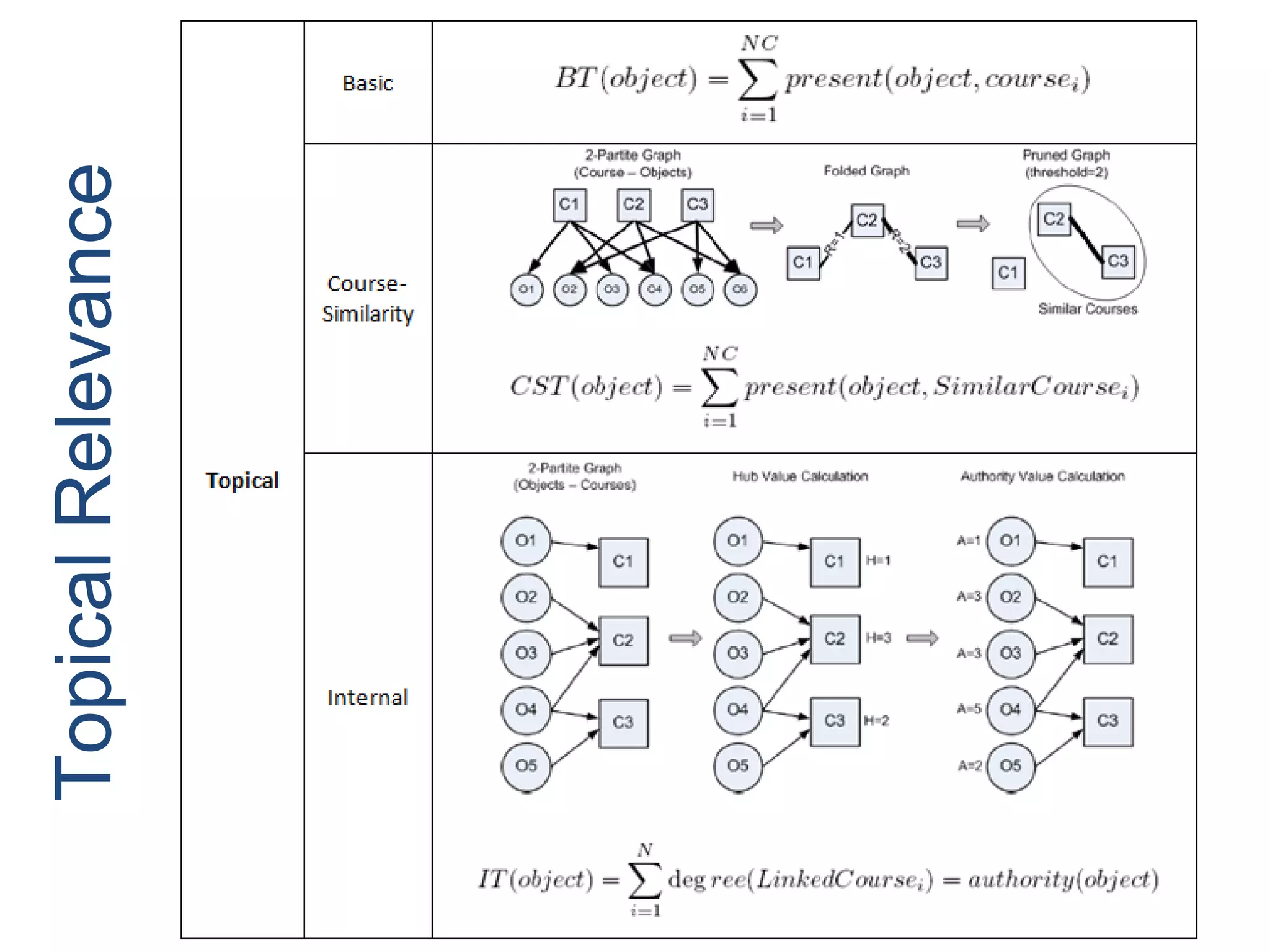
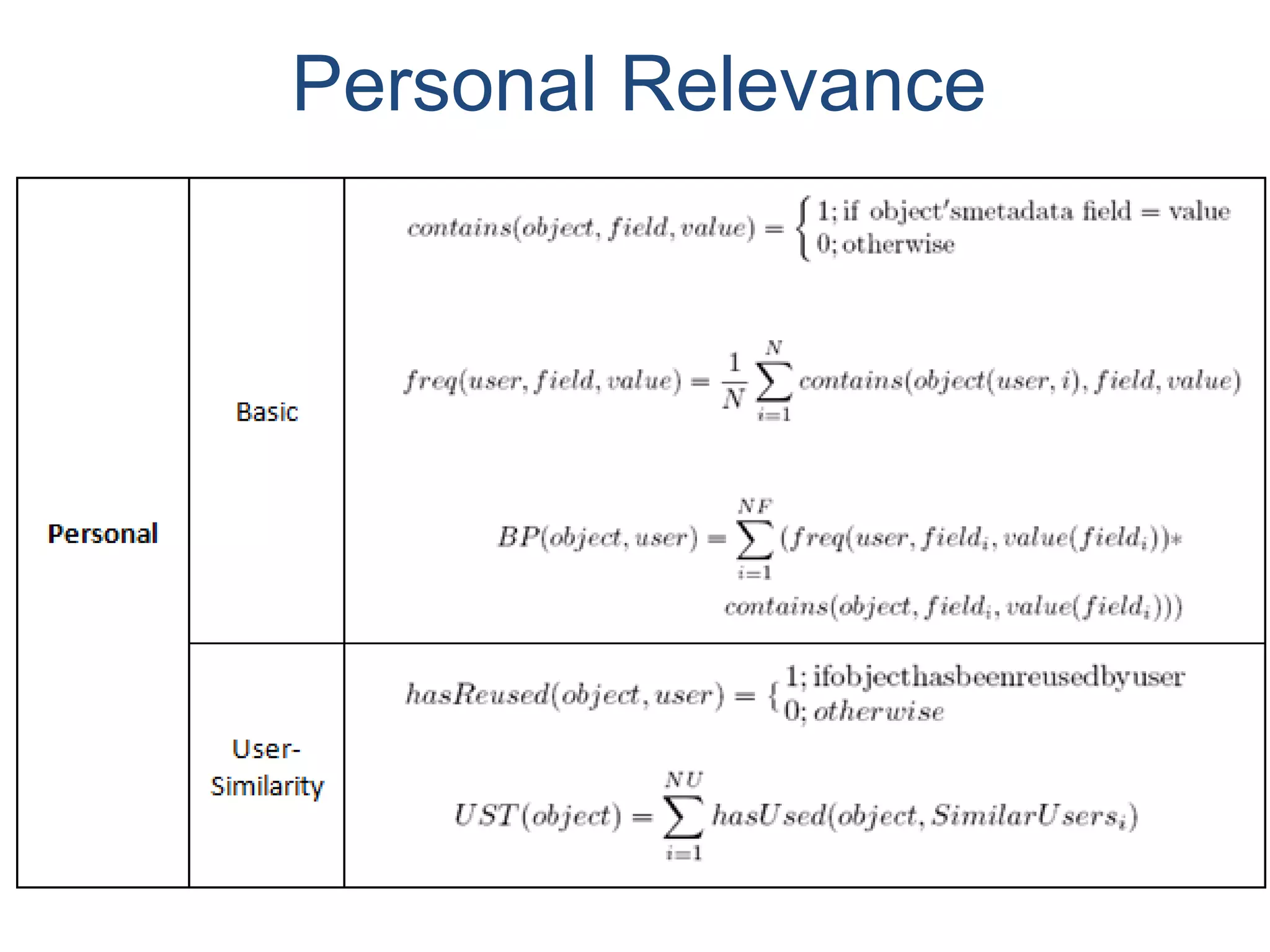
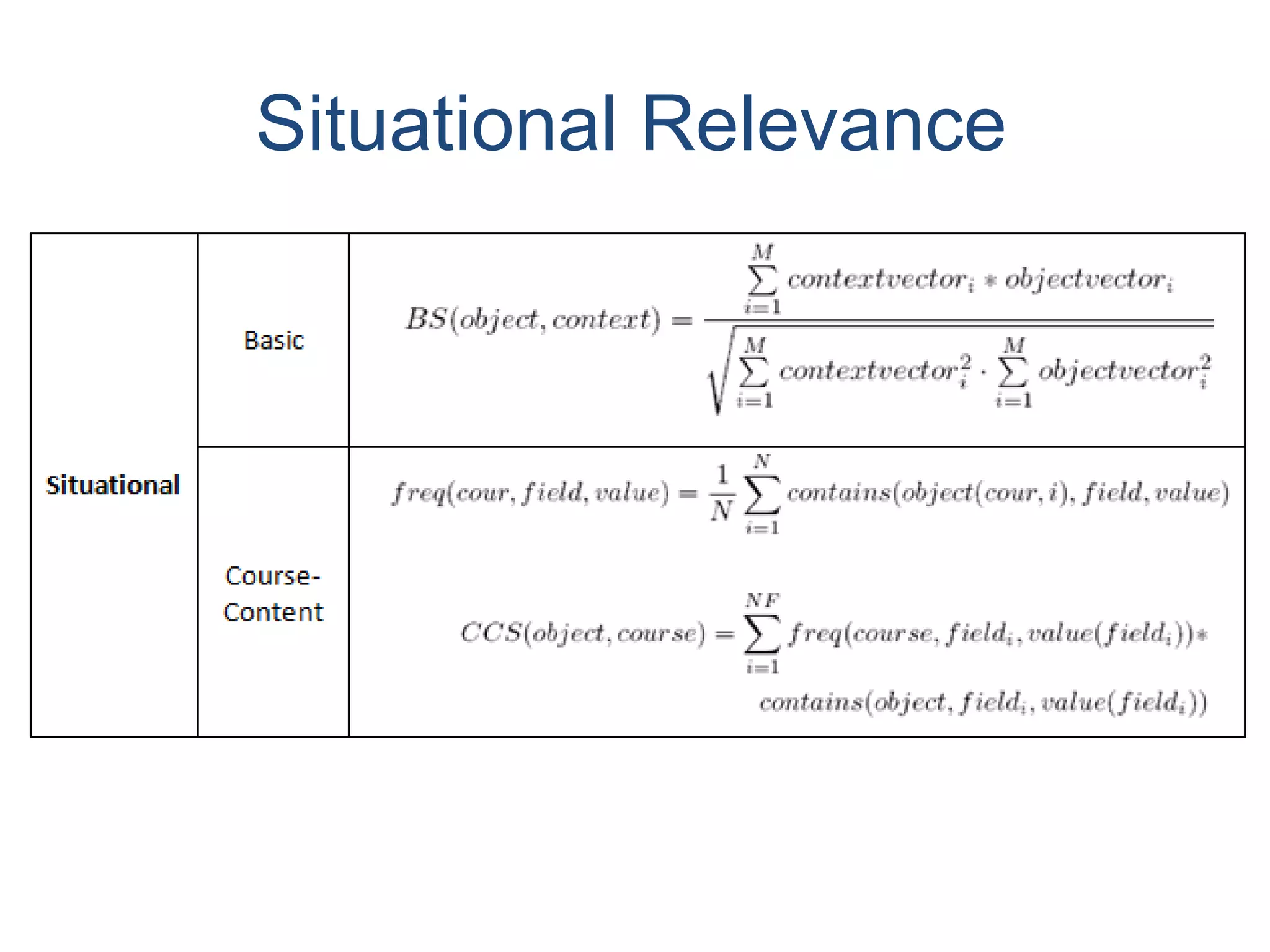
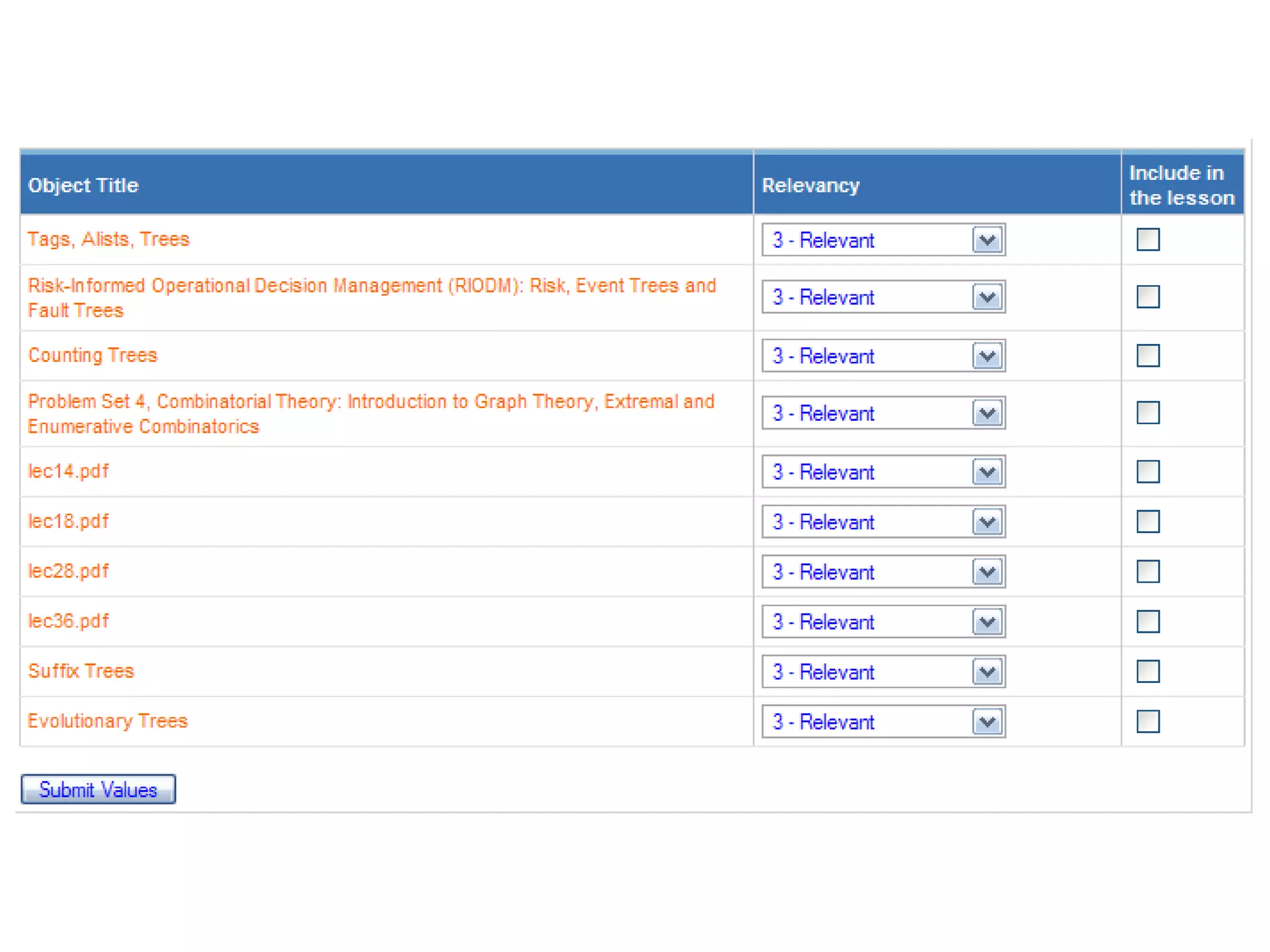
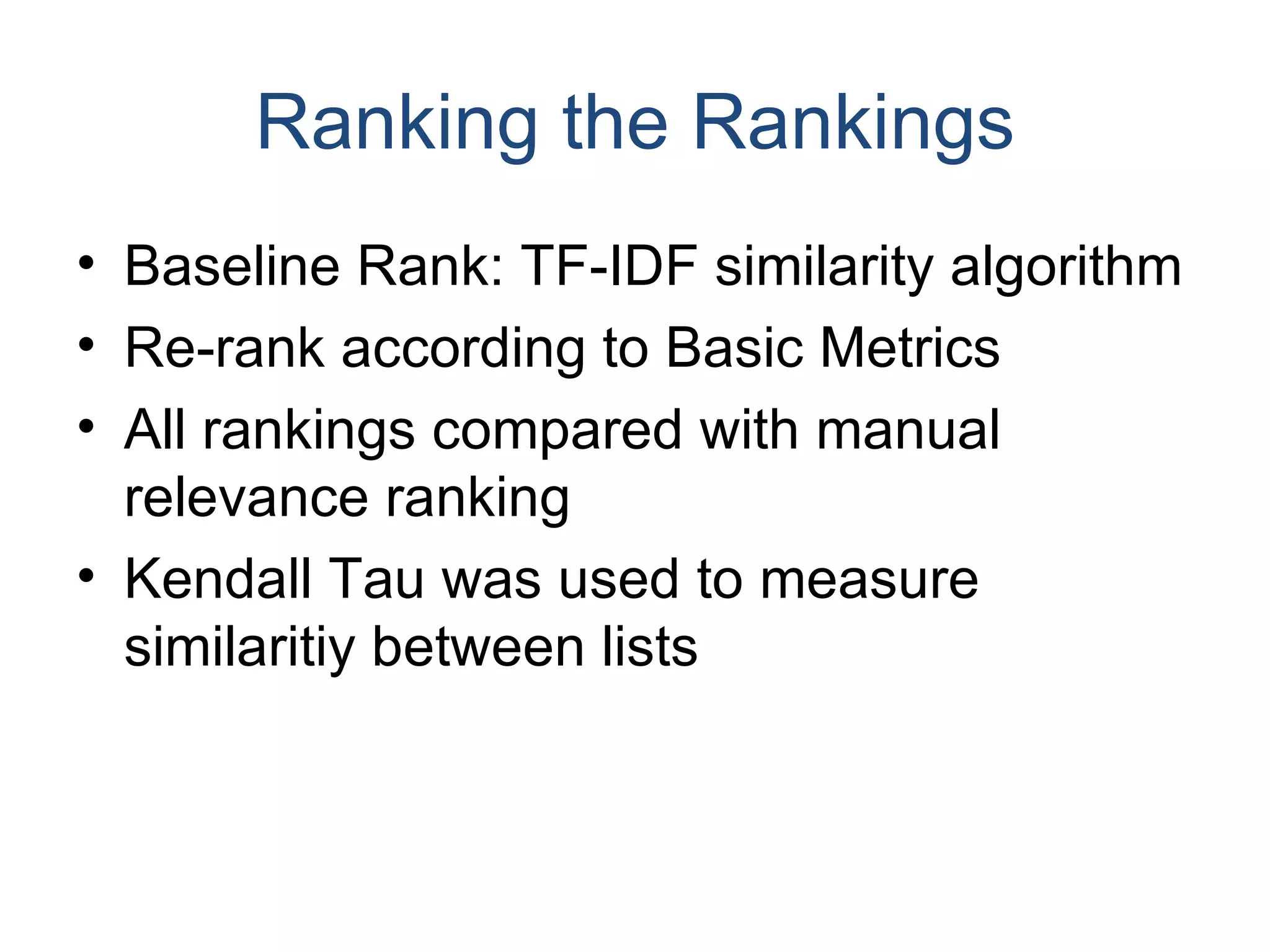
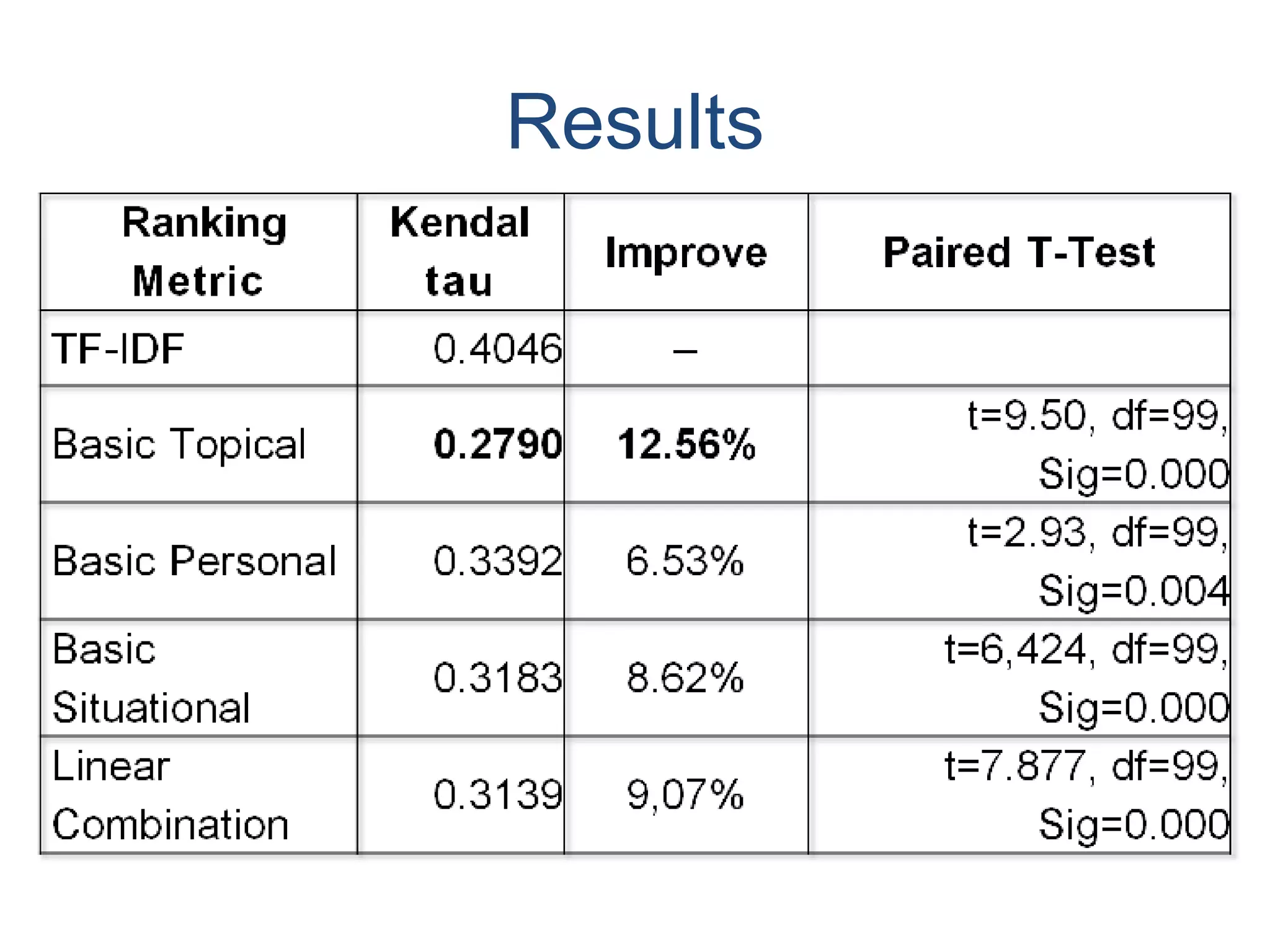
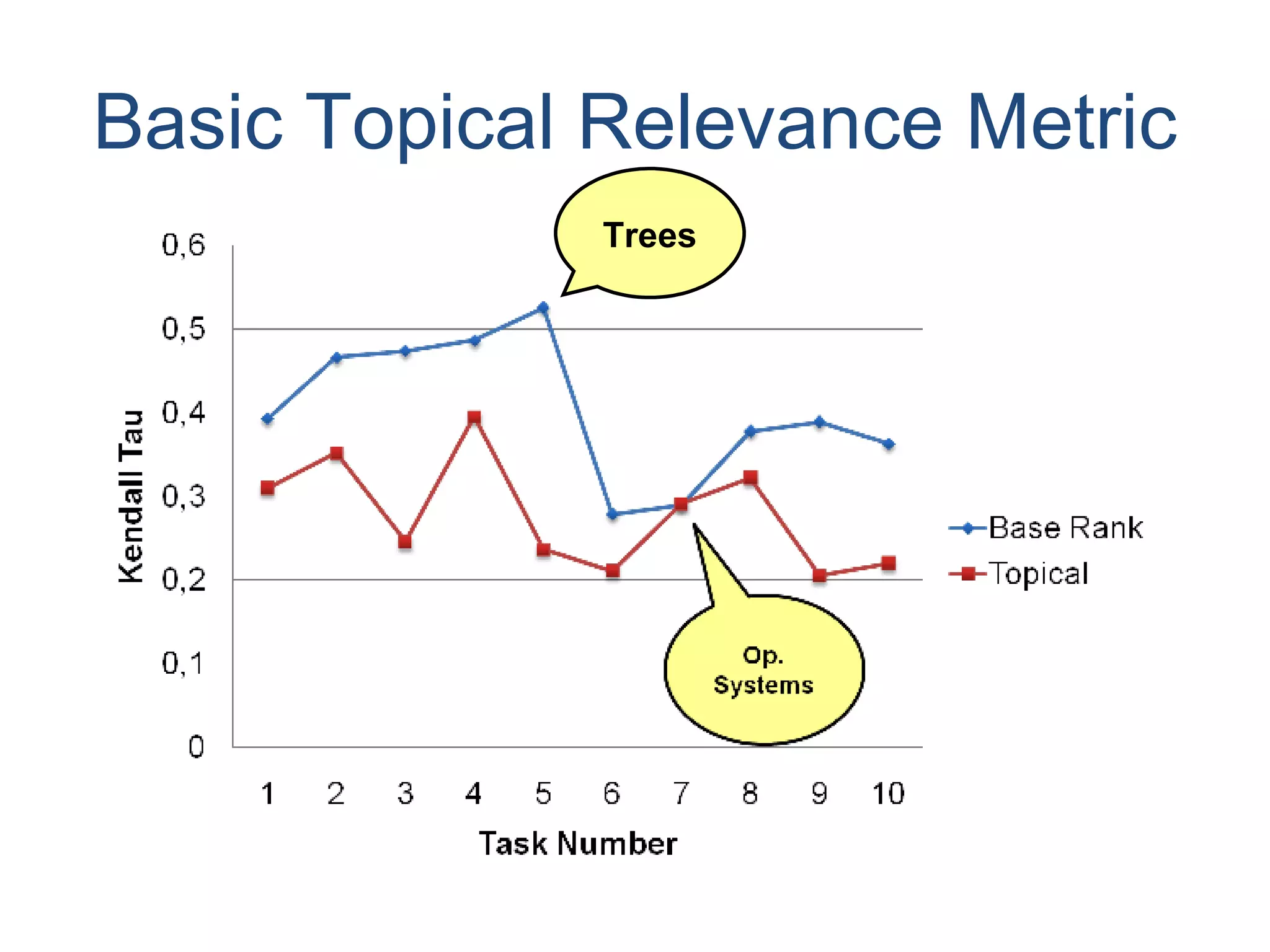
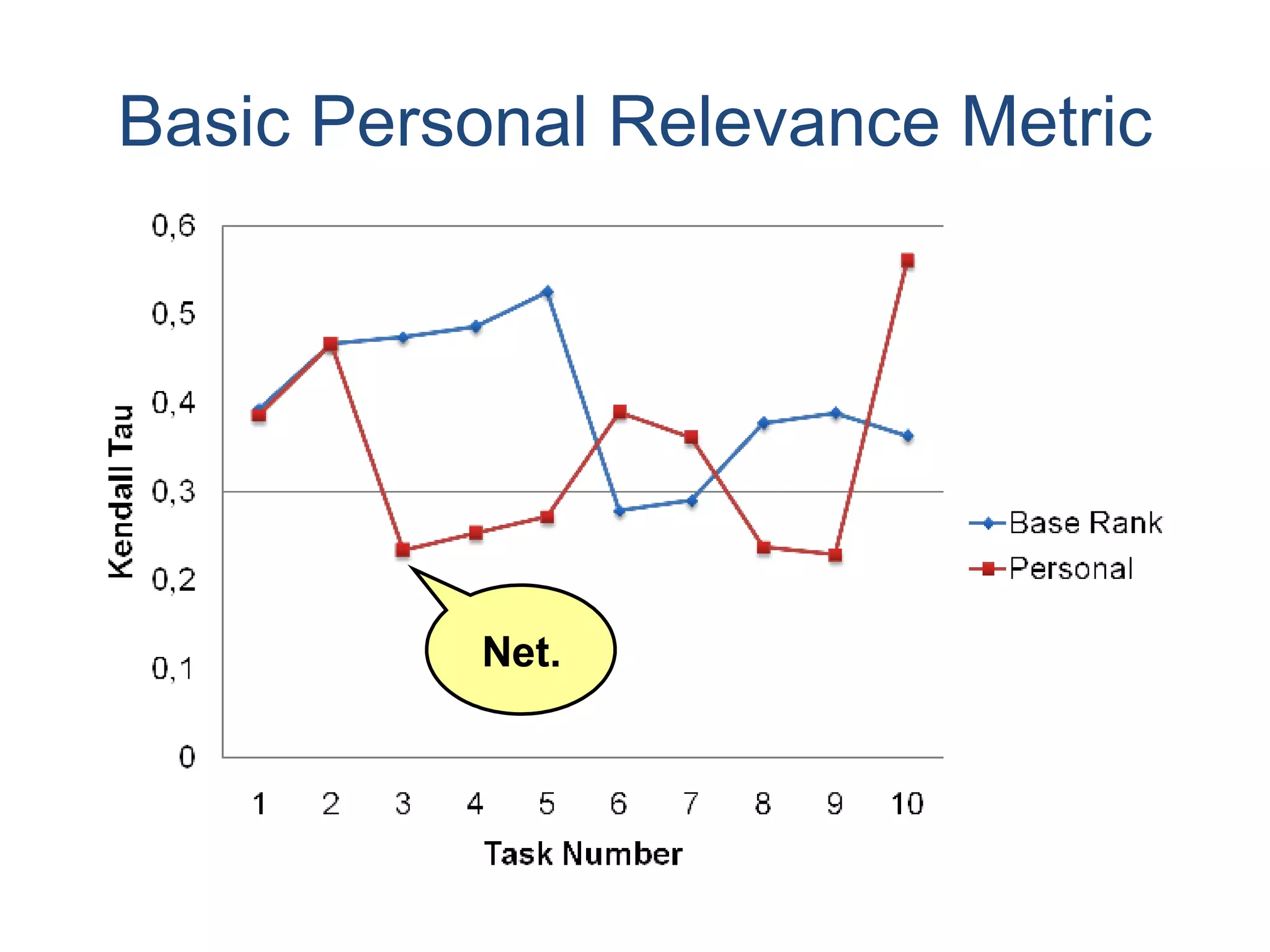
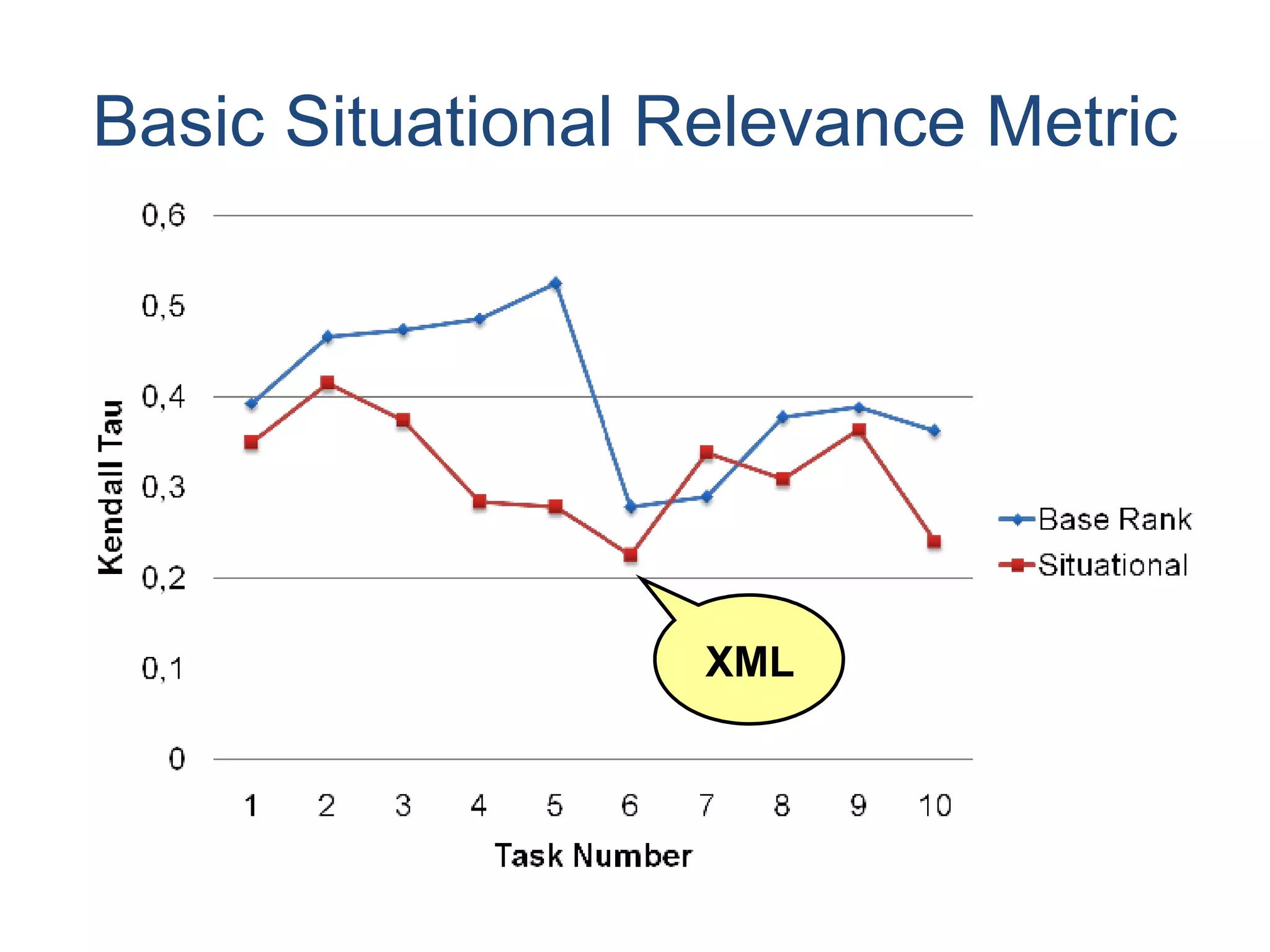
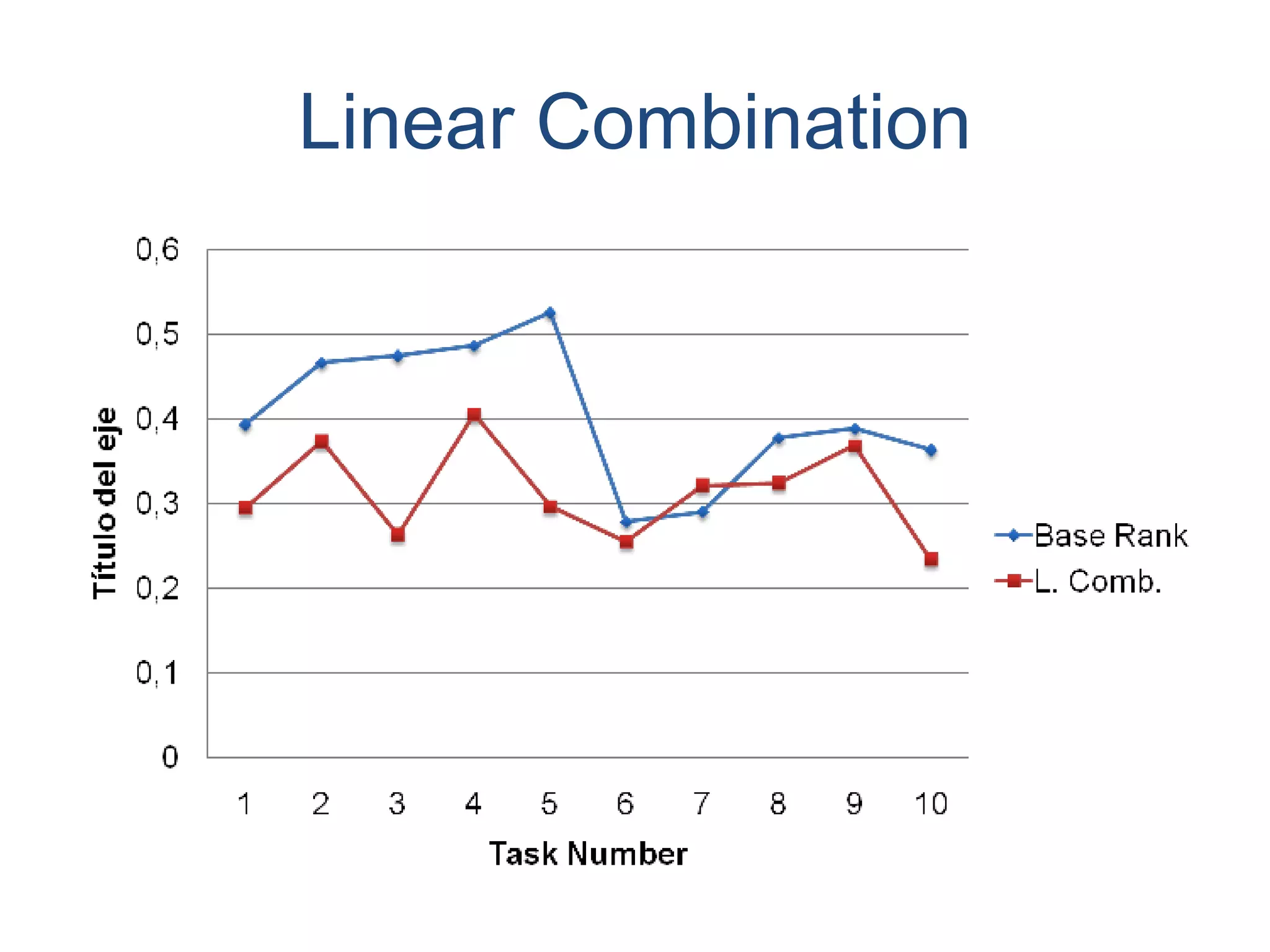
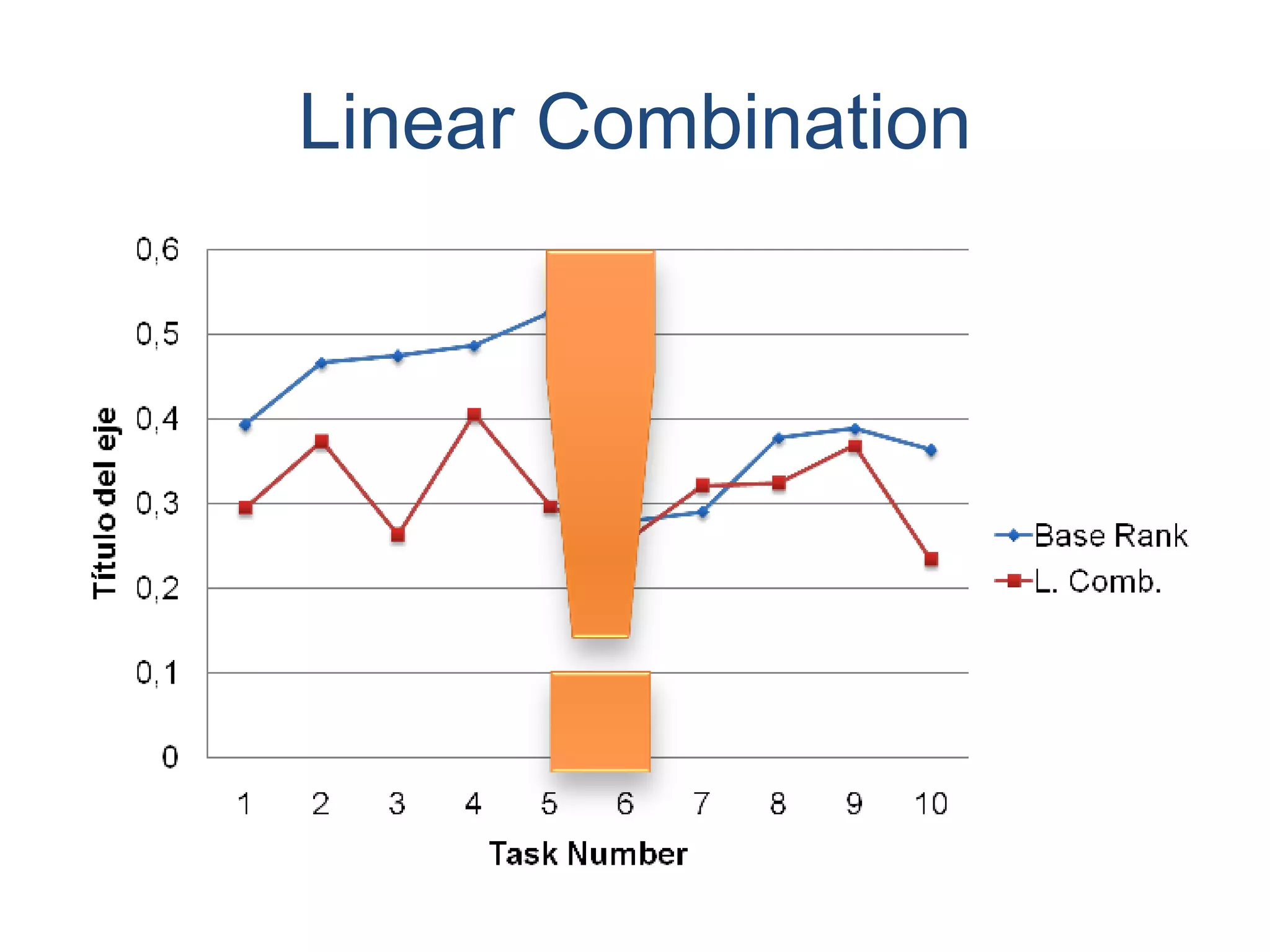
The document discusses the importance of relevance ranking metrics for learning objects, emphasizing the challenges posed by the abundance of resources. It outlines an exploratory study that tested various ranking algorithms against manual ratings, showing that basic metrics can enhance selection processes. The authors conclude that while current metrics are not optimal, they can serve as a foundational tool for future research and improvement.
![Thank You! Dank U! Gracias! Questions, Comments, Critics… are all welcome!! Xavier Ochoa [email_address] http://www.cti.espol.edu.ec/xavier Erik Duval Erik.Duval@cs.kuleuven.be http://www.cs.kuleuven.ac.be/~erikd](https://image.slidesharecdn.com/relevance-ranking-of-learning-objects3789/75/Relevance-Ranking-of-Learning-Objects-30-2048.jpg)