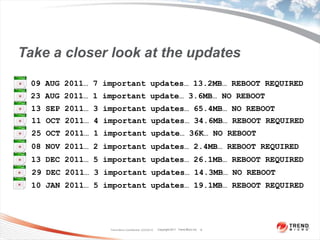
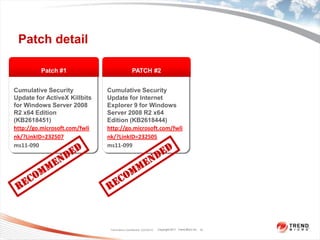
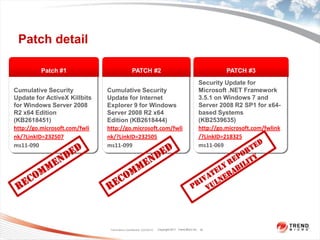
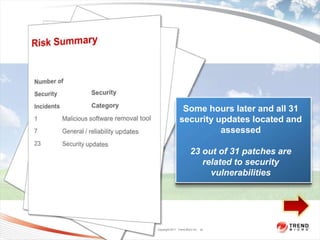
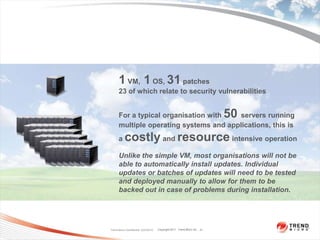
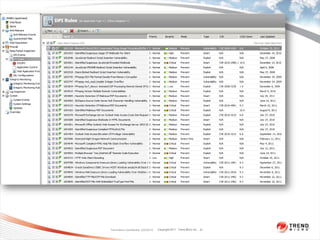
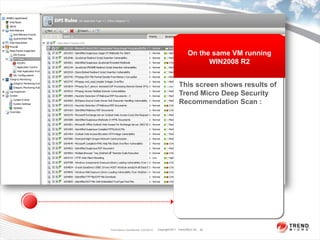
The document discusses the extensive overhead and challenges of applying patches to a Windows Server 2008 R2 virtual machine, which revealed 31 important security updates over a six-month period, with many requiring system reboots. It highlights the difficulty of managing patch updates in mission-critical systems and suggests the use of virtual patching as an alternative solution to enhance security without the need for immediate system downtime. Recommendations are provided for improving patch management processes and assessing associated costs and risks.