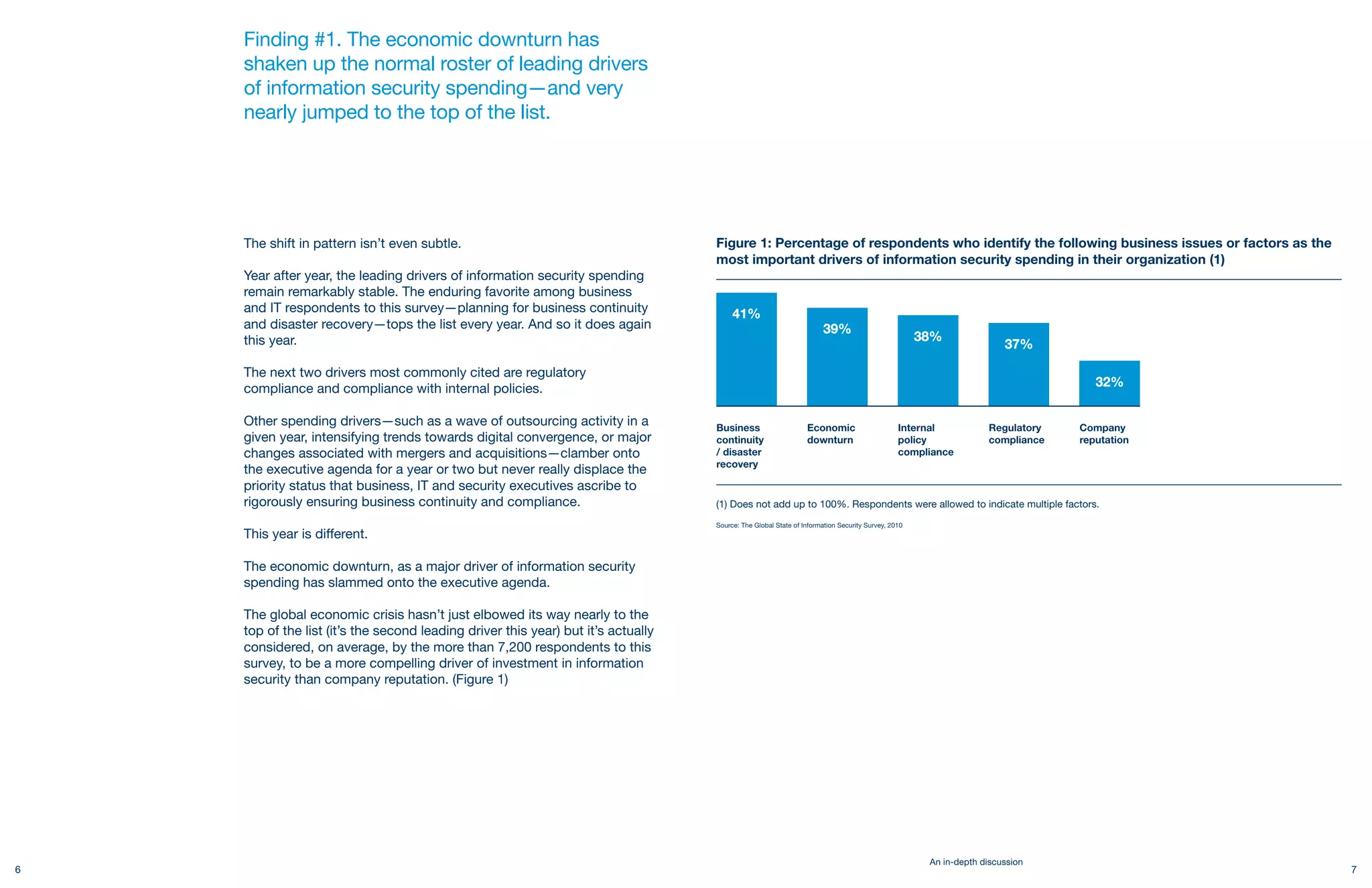
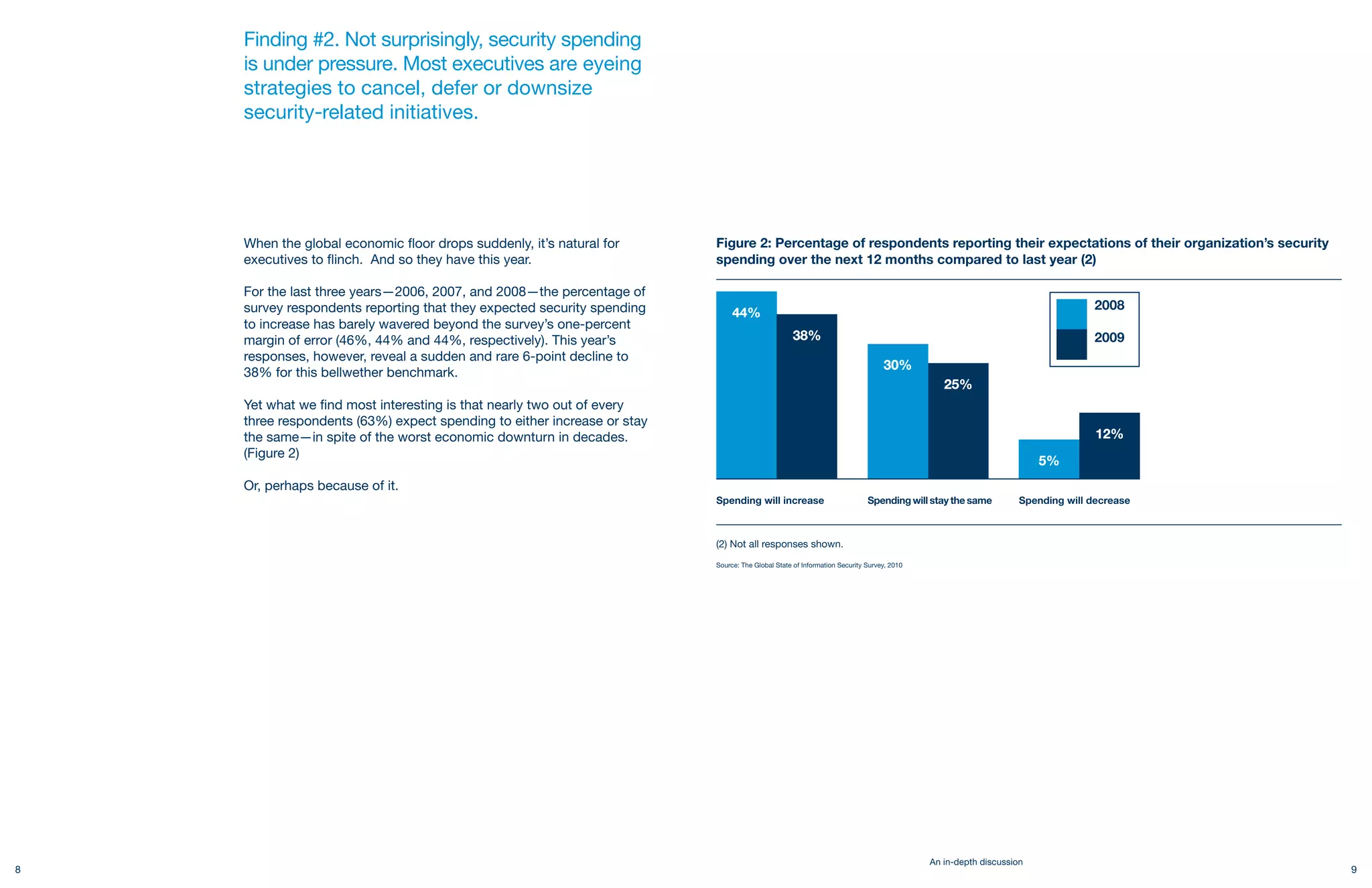
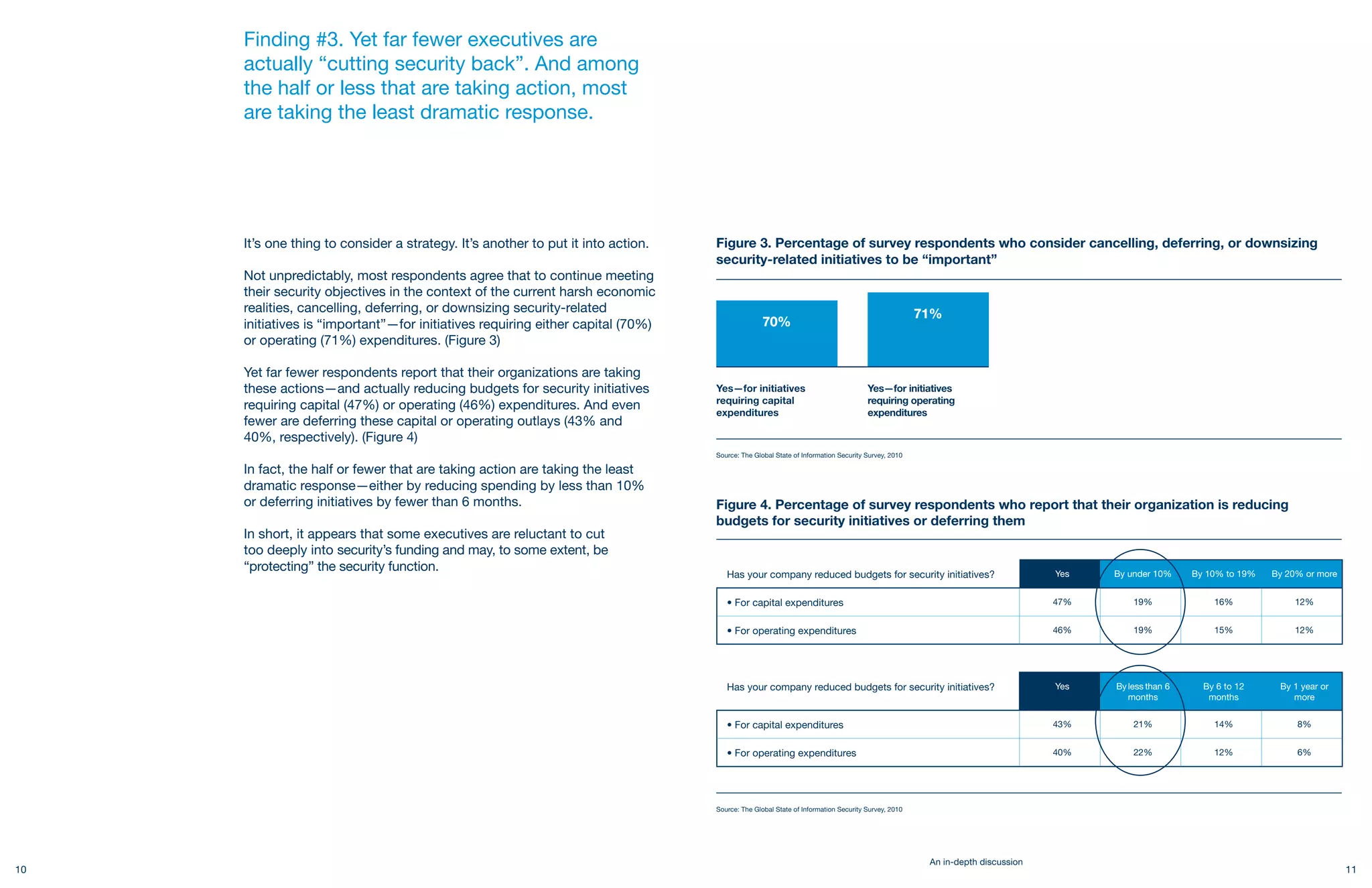
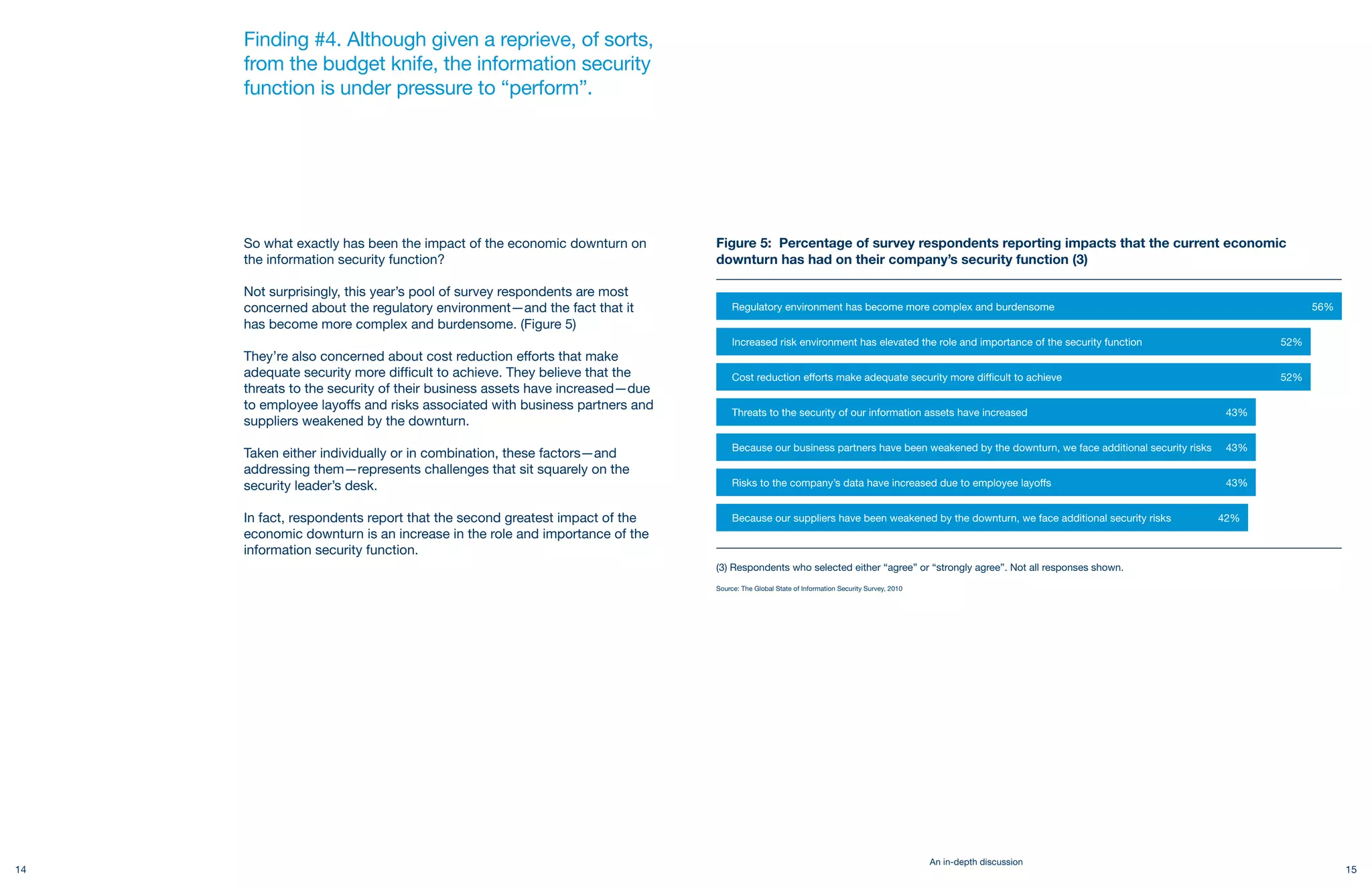
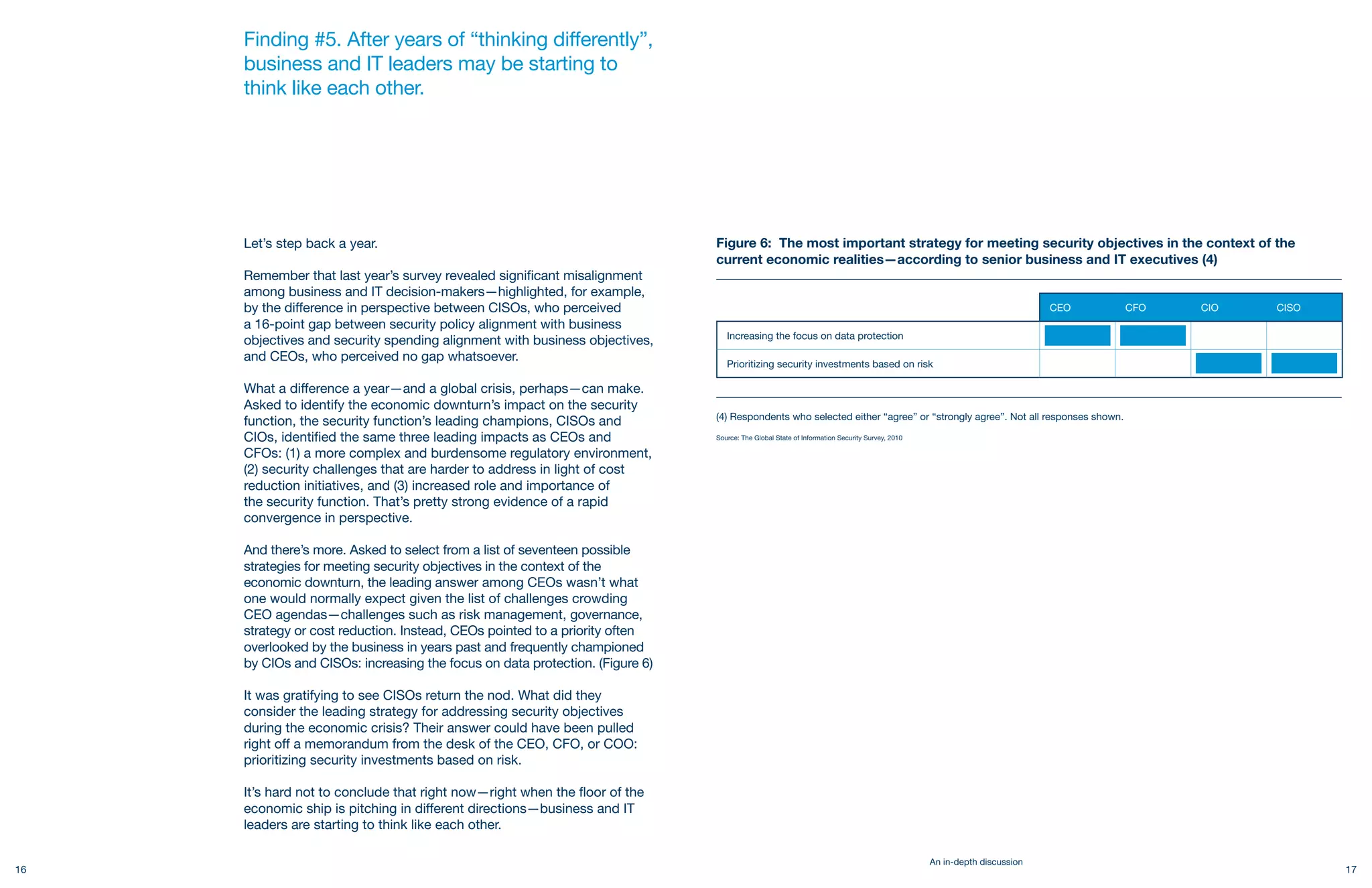
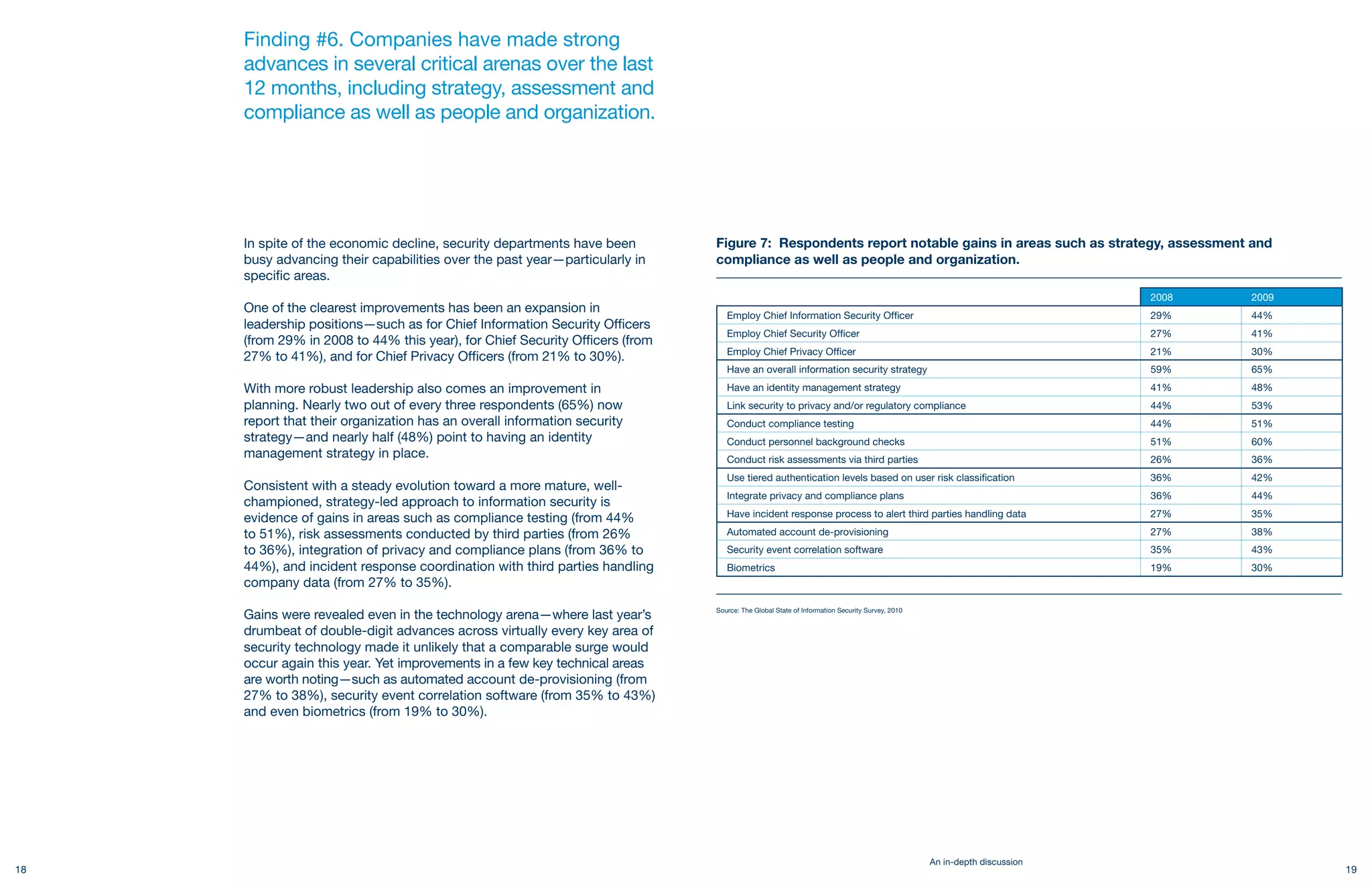
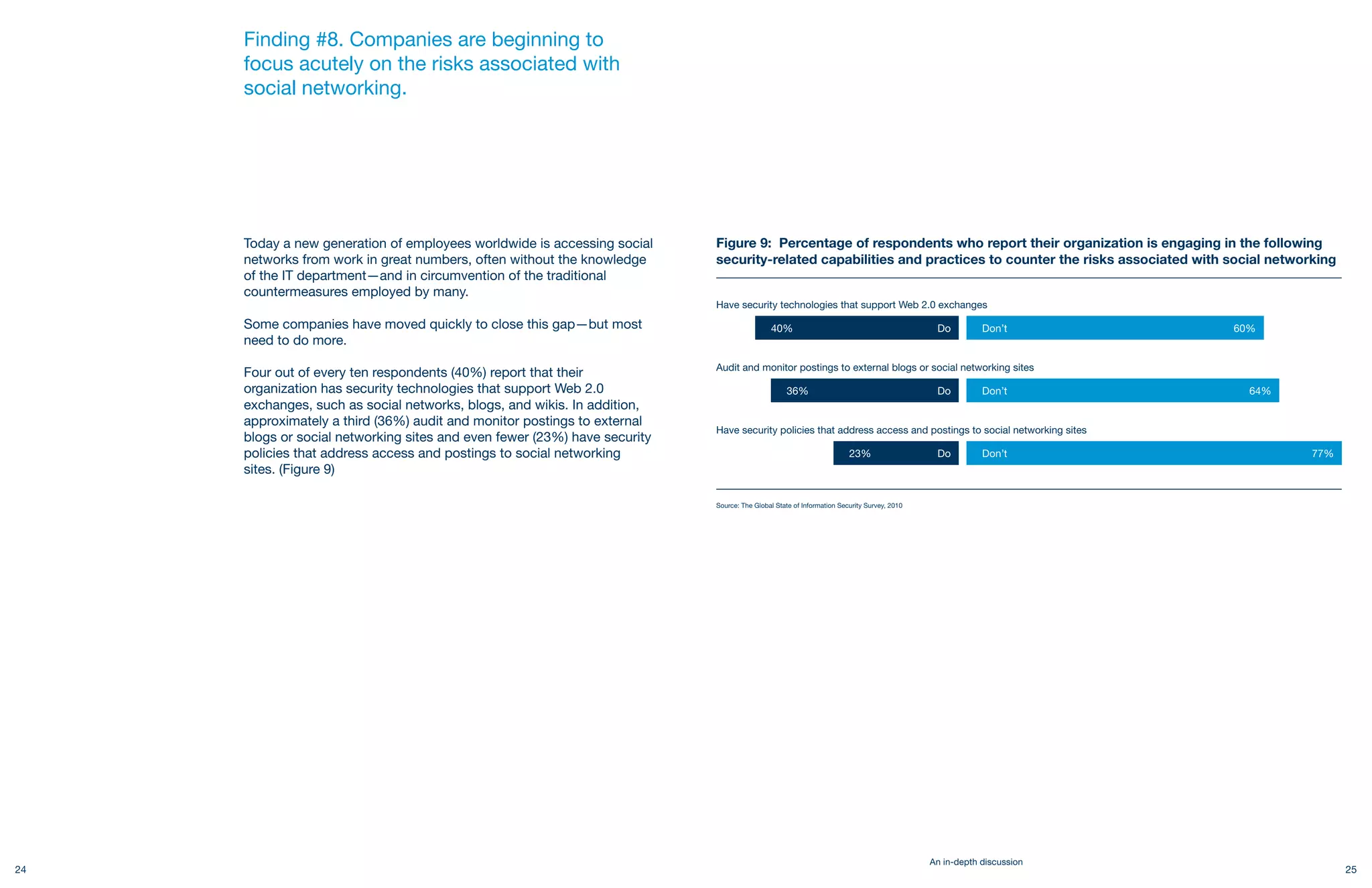
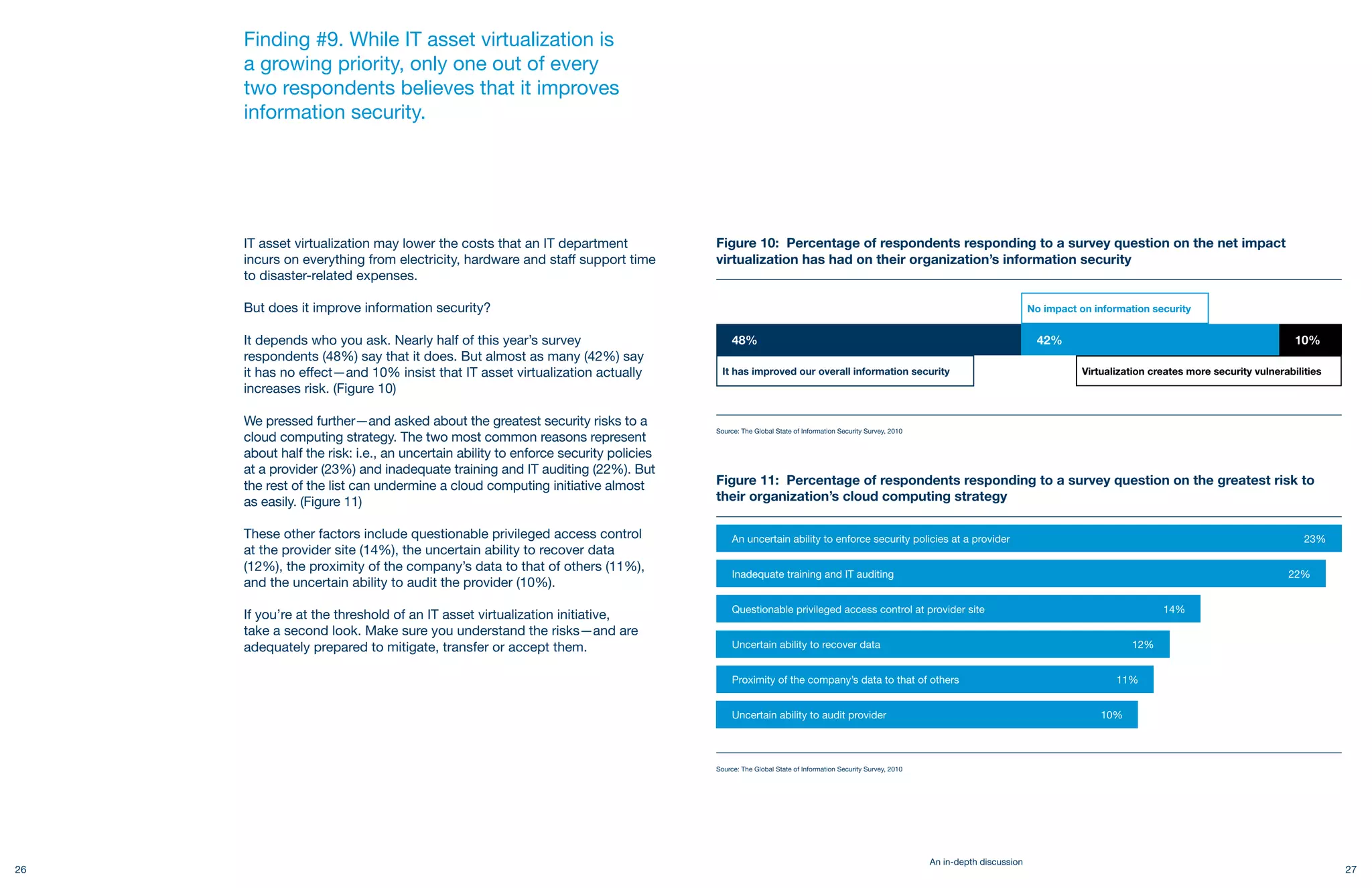
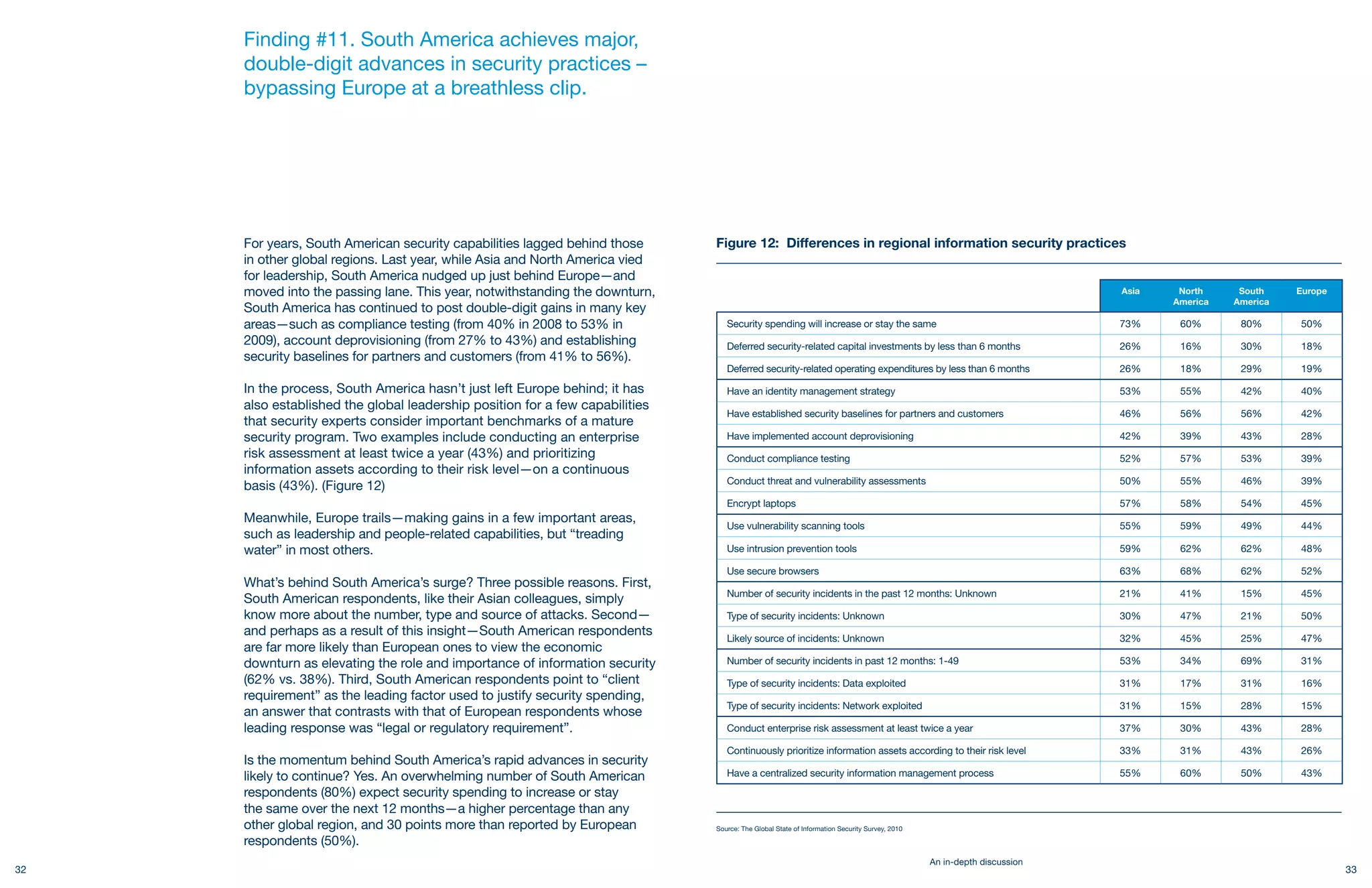
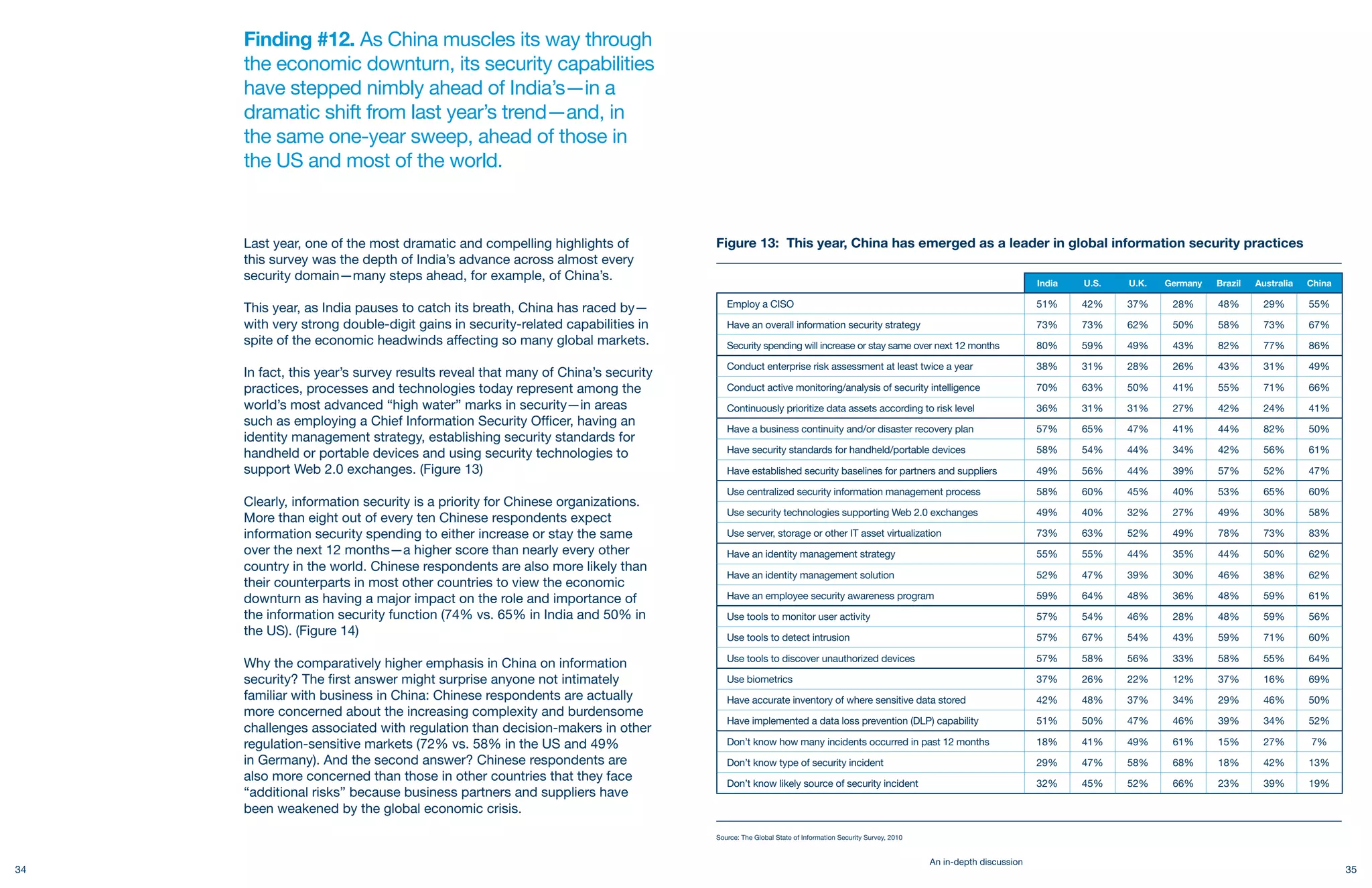
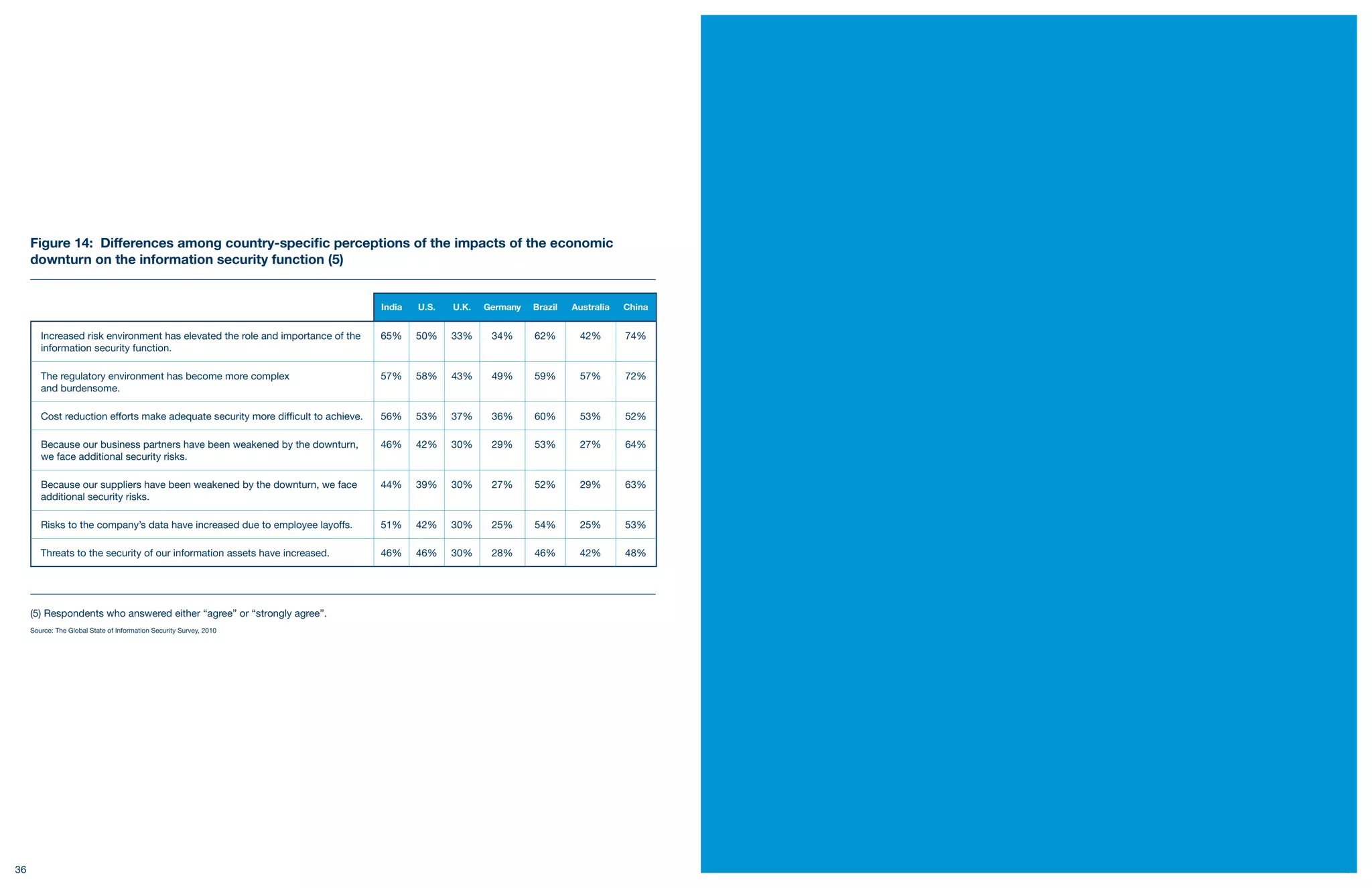
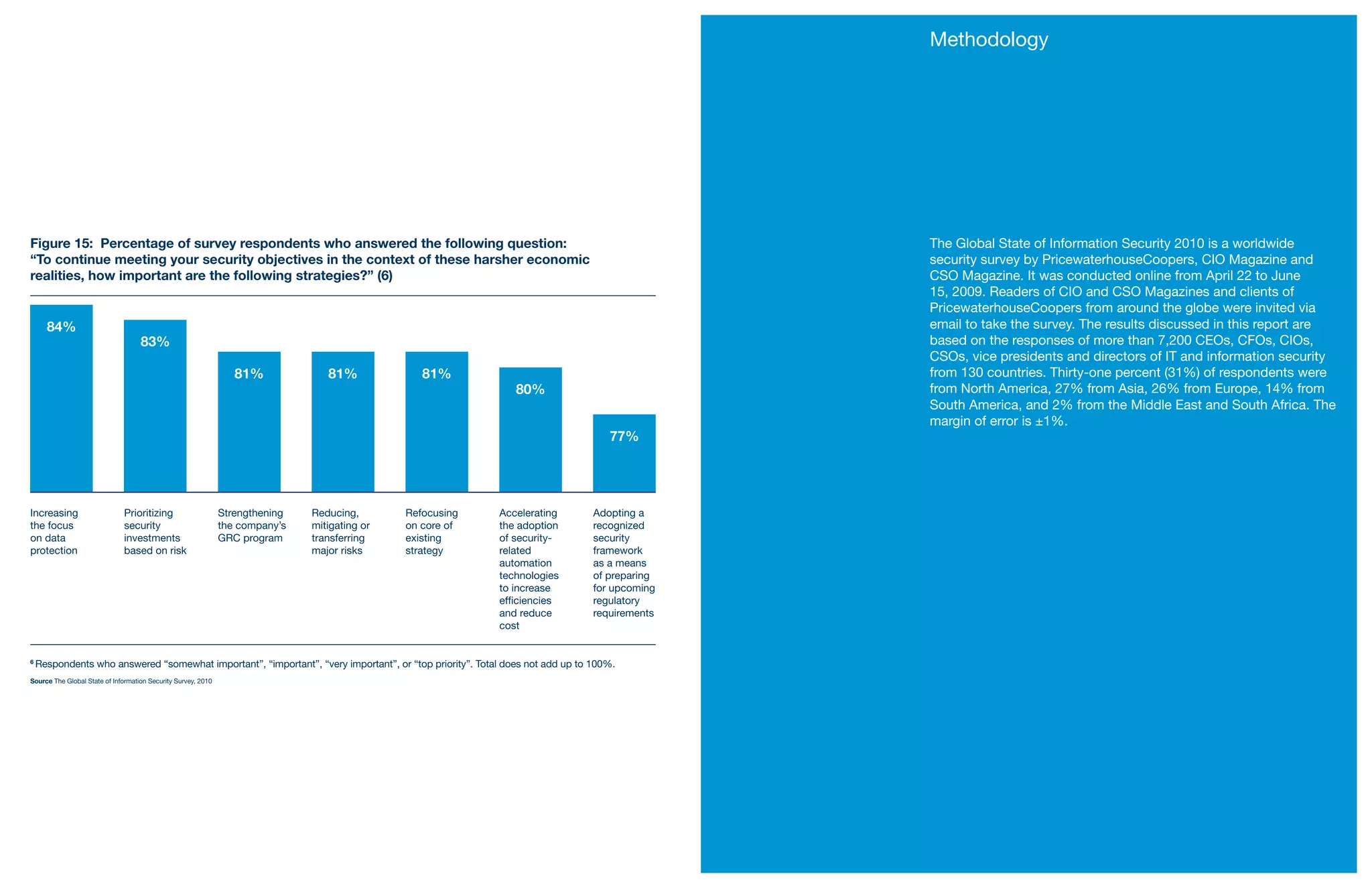
The document discusses the role of information security amid the economic downturn, highlighting the challenges and expectations for security functions in organizations. While executives are facing pressure to perform without significant budget cuts, there is evidence that companies are prioritizing security investments and making advancements in areas like strategy and compliance. The findings indicate a shift in perspective among business and IT leaders towards aligning security more closely with organizational goals.