Proj Geom Computing(Siggraph2000)
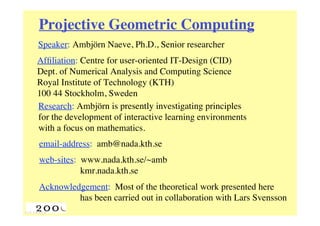
- 1. Projective Geometric Computing Speaker: Ambjörn Naeve, Ph.D., Senior researcher Affiliation: Centre for user-oriented IT-Design (CID) Dept. of Numerical Analysis and Computing Science Royal Institute of Technology (KTH) 100 44 Stockholm, Sweden Research: Ambjörn is presently investigating principles for the development of interactive learning environments with a focus on mathematics. email-address: amb@nada.kth.se web-sites: www.nada.kth.se/~amb kmr.nada.kth.se Acknowledgement: Most of the theoretical work presented here has been carried out in collaboration with Lars Svensson
- 2. Projective Drawing Board (PDB) PDB is an interactive program for doing plane projective geometry that will be used to illustrate this lecture. PDB has been developed by Harald Winroth and Ambjörn Naeve as a part of Harald’s doctoral thesis work at the Computational Vision and Active Perception (CVAP) laboratory at KTH . PDB is avaliable as freeware under Linux. www.nada.kth.se/~amb/pdb-dist/linux/pdb2.5.tar.gz
- 5. Geometric algebra in n-dim Euclidean space n Underlying vector space V with ON-basis e1,...,en. n G = G n ! G(V ) has 2n dimensions. Geometric algebra: n M = k=0 M A multivector is a sum of k-vectors: ! k M k = Ak + Bk +K A k-vector is a sum of k-blades: Bk = b1 ! b2 !K! bk A k-blade = blade of grade k : Bk ! 0 quot; b1 ,K,bk Note: are linearly independent. Hence: the grade of a blade is the dimension of the subspace that it spans.
- 6. Blades correspond to geometric objects equivalence class equal orientation blade of directed and of grade line segments length 1 area 2 surface regions 3 volume 3-dim regions ... ... ... k k-dim regions k-volume
- 7. Some equivalence operations on 2-blades ^ a b a a^ ^ ab aa ⁄ ⁄ = = a b ^ ^ ab bb b b ⁄ = ⁄ = a R b aR ^ b b R a b ab R ⁄ ⁄ = a
- 8. Pseudoscalars and duality Gn Def: A n-blade in is called a pseudoscalar. P = p1 ! p2 !K ! pn A pseudoscalar: I = e1 ! e2 !K! en A unit pseudoscalar: !1 The bracket of P: [ P] = PI The dual of a multivector x: !1 Dual( x) = xI Dual( x) ! x ˜ Notation: ˜ If A is a k-blade, then A is a (n-k)-blade. Note:
- 9. The subspace of a blade B = b1 !K ! bm Fact: To every non-zero m-blade n there corresponds a m-dim subspace B ! V with B = Linspan{b1 ,K,bm} n = Linspan{b ! V : b quot; B = 0}. e1 ,e2 ,K,em is an ON-basis for B Fact: If m and if bi = ! bik ek for i = 1,…,m , k=1 B = (det bik )e1 ! e2 !K! em then = (det bik )e1e2 Kem .
- 10. Dual subspaces <=> orthogonal complements ˜ = A !. A If A is a non-zero m-blade Fact: n Proof: We can WLOG choose an ON-basis for V such that I = e1e2 Ken . A = !e1e2 Kem and We then have ˜ = AI !1= ±!em+1 Ken A which implies that ˜ = A !. A
- 11. The join and the meet of two blades Def: Given blades A and B, if there exists a blade C A = BC = B ! C we say that such that A is a dividend of B and B is a divisor of A. Def: The join of blades A and B is a common dividend of lowest grade. Def: The meet of blades A and B is a common divisor of greatest grade. The join and meet provide a representation in geometric n algebra of the lattice algebra of subspaces of V .
- 12. Join of two blades <=> sum of their subspaces A! Bquot; 0 For two blades A and B with Def: Join( A, B) = A ! B . we can define: A ! B = A + B and A ! B = 0 . In this case: 3 Example: 0 ! a,b quot; V a!b a b a!b =0 a ! b = a + b = {!a + µb : !, µ quot; R}
- 13. Meet of blades <=> intersection of subspaces n A, B ! 0 and A + B = V Def: If blades ˜˜ Meet( A, B) ! A quot; B = ( A # B)I . then: A! B = Aquot; B . In this case: Note: The meet product is related to the outer product by duality: ( A ! B) I = ( A ˜ ˜ # B)II quot;1 = A # B ˜˜ quot;1 Dual( A ! B) = Dual( A) quot; Dual(B)
- 14. Dual outer product Dualisation: ~ G!G !1 x a x = xI ˜ Dual outer product: ⁄ !1 !1 x ! y = ((xI ) quot; (yI ))I G! G quot; G ~ ~ ~ ~ ⁄ x ! y = (x ! y) ˜˜ G! G quot; G
- 15. Example: V 3 , I = e1 ! e2 ! e3 = e1e2e3 A = e1 ! e2 = e1e2 , B = e2 ! e3 = e2 e3 ˜ = (e1 ! e2 )I quot;1 = (e1e2 )(e3e2 e1 ) = (!1)2 e3e1e2e2 e1 = e3 A ˜ = (e2 ! e3 )I quot;1 = (e2 e3 )(e3e2e1 ) = e1 B ˜˜ A ! B = ( A quot; B)I = (e3 ! e1 )(e1e2e3 )= !e2 ˜ A = e3 B e2 = ! A quot; B Hence: A A! B = Aquot; B ˜ e1 = B
- 16. Projective geometry - historical perspective 1-d subspace parallell to the ground plane ity fin t in point at infinity on ea riz lin ho eye parallell lines point ground plane 1-dim subspace through the eye
- 17. n n-dimensional projective space P n+1 P = P(V ) = the set of non-zero subspaces of V . n n+1 A point p is a 1-dim subspace (spanned by a 1-blade a). p = a = {!a : ! quot; 0} = a = !a , ! quot; 0 . ˙˙ A line l is a 2-dim subspace (spanned by a 2-blade B2). l = B2 = {!B2 : ! quot; 0} = B2 . ˙ Let B denote the set of non-zero blades of the geometric n+1 G(V ) . algebra Hence we have the mapping n P B B B Œ Œ .
- 18. The projective plane P2 3 0 ! a,b, x quot;V {x ! 0 : x quot; a = 0} a!b Line: 2 P a {x ! 0 : x quot; a quot; b = 0} b
- 19. The intersection of two lines in P2 A, B ! {non-zero 2-blades in G3}. A B 2 P A! B
- 20. Collinear points p!q p q r The points p, q, r are collinear p ! q ! r = 0. if and only if
- 21. Concurrent lines Q R P P!Q The lines P, Q, R are concurrent (P ! Q) quot; R = 0 . if and only if
- 22. Desargues’ configuration Q = b! quot; b A= b!c p = A ! Aquot; A! = b ! quot; c ! a! p c! B= c!a q = B ! Bquot; b! B! = c ! quot; a ! cq C = a!b r r = C ! Cquot; b a C ! = a ! quot; b! P = a! quot; a R = c! quot; c
- 23. Desargues’ configuration (cont.) P = a! quot; a p = A ! Aquot; = (b ! c) quot; (b# ! c# ) Q = b! quot; b q = B ! Bquot; = (c ! a) quot; (c# ! a# ) R = c! quot; c r = C ! Cquot; = (a ! b) quot; ( a# ! b# ) J = a ! b ! c = [abc]I J ! = a ! quot; b ! quot; c ! = [ a !b !c ! ] I p ! q ! r quot; JJ # (P $ Q) ! R Leads to: = 0 if and only if = 0 if and only if p,q,r are collinear P,Q,R are concurrent
- 24. Desargues’ theorem B C A P B’ A’ C’ R L Q p, q, r are collinear iff P, Q, R are concurrent.
- 25. Pascal’s theorem 2 Let a,b,c, a !, b ! be five given points in P . Consider the second degree polynomial given by p(x) = ((a ! bquot; ) # ( aquot; ! b)) ! ((b ! x) quot; (b# ! c)) ! ((c ! aquot; ) # (x ! a)) . It is obvious that p(a) = p(b) = 0 and easy to verify that p(c) = p( a ! ) = p(b ! ) = 0. p(x) = 0 must be the equation Hence: of the conic on the 5 given points.
- 26. Verifying that p(a´) = 0 p(a! ) = same line = ((a ! bquot; ) # (aquot; ! b)) ! ((b ! aquot; ) # (bquot; ! c)) ! = a! quot; b ˙ same point ((c ! aquot; ) # ( aquot; ! a)) = (a! quot; b) quot; a! = 0 ˙ = a! ˙
- 27. Pascal’s theorem (cont.) c! Hence, a sixth point lies on this conic if and only if p(c! ) = ((a quot; b! ) # ( a! quot; b)) quot; ((b ! cquot; ) # (bquot; ! c)) ! ((c ! aquot; ) # (cquot; ! a)) = 0 . Geometric formulation: The three points of intersection of opposite sides of a hexagon inscribed in a conic are collinear. This is a property of the hexagrammum mysticum, which Blaise Pascal discovered in 1640, at the age of 16.
- 28. Pascal’s theorem (cont.) r = (a ! bquot; ) # (aquot; ! b) 1⁄ 4 = s = (b ! c quot; ) # (bquot; ! c) = 2⁄ 5 = 3⁄ 6 t = (c ! aquot; ) # (cquot; ! a) b a c 5 3 1 r t s 4 6 r !s !t = 0 a! 2 c! b!
- 29. Pascal’s theorem (cont.) L Q P’ P Q’ R’ R The three points of intersection of opposite sides of a hexagon inscribed in a conic are collinear.
- 30. Pappus’ theorem (ca 350 A.D.) Q R P’ P Q’ L R’ If the conic degenerates into two straight lines, Pappus’ theorem emerges as a special case of Pascal’s.
- 31. Outermorphisms A mapping f : G ! G Def: is called an outermorphism if f (i) is linear. f (t) = t !t quot; R (ii) f (x ! y) = f (x) ! f (y) !x, y quot; G (iii) k k f (G ) ! G !k quot; 0 (iv)
- 32. The induced outermorphism T : V ! V denote a linear mapping. Let T induces an outermorphism T : G ! G Fact: given by T(a1 !K! ak ) = T(a1 ) !K! T(ak ) T(!) = ! , ! quot; R and linear extension. T maps the blades of V Interpretation: in accordance with how T maps the vectors of V.
- 33. n Polarization with respect to a quadric in P n+1 n+1 T :V ! V denote a symmetric linear map, Let n+1 which means that T(x) ! y = x ! T(y) , !x, y quot; V . n Q in P The corresponding quadric (hyper)surface n+1 Q = {x ! V : x quot; T(x) = 0 , x # 0}. is given by The polar of the k-blade A with respect to Q Def: is the (n+1-k)-blade defined by ˜ (A) ! T(A)I quot;1 Pol Q ( A) ! T .
- 34. Polarization (cont.) n+1 T = id ! Q = {x ! V : x quot; x = 0 , x # 0}. Note: ˜ quot;1 In this case Pol Q ( A) ! AI ! A and polarization becomes identical to dualization. Fact: For a blade A we have Pol Q (Pol Q (A)) = A ˙ (i) If A is tangent to Q (ii) then PolQ(A) is tangent to Q . Especially: If x is a point on Q, then PolQ(x) is the hyperplane which is tangent to Q at the point x.
- 35. Pol Q (x) x
- 36. x Pol Q (x) Q
- 37. Q Pol Q (x) x
- 38. Polarity with respect to a conic y x x!y 2 P Pol Q (x) Pol Q (y) Pol Q (x) ! Pol Q (y) Q The polar of the join of x and y = Pol Q (x ! y) is the meet of the polars of x and y = Pol Q (x) ! Pol Q (y)
- 39. Pol Q (x) ! Pol Q (y) x Q y x!y
- 40. Polar reciprocity n+1 n x, y ! V P. Let represent two points in T : Then we have from the symmetry of ~ y ! T(x) = y ! (T(x)I quot;1 ) quot;1 quot;1 = (y ! T(x))I = (x ! T(y))I ~ quot;1 = x ! (T(y)I ) = x ! T(y) . y ! Pol Q (x) = 0 ! x ! PolQ (y) = 0 Hence: i.e. the point y lies on the polar of the point x if and only if x lies on the polar of y.
- 41. Brianchon’s theorem 1 Pascal line 4 1 (1640) 2 3 Q 2 Brianchon point 5 4 (1810) 5 3 6 6
- 42. The dual map f f : G ! G be linear, G G Let 2 and assume that I ! 0 . ~ ~ ˜ f ˜ G ~G f :G ! G Def: The dual map ˜˜ f ( x ) = f ( x) is the linear map given by ~ ~ ˜ ˜ f =f ˜ !1 f (x) = f (xI)I G G ˜ (xI !1 )I = f (xI !1 )I 2 I !2 I ˜ f (x) = f Note: ˜ ˜ (xI !1 I 2 )I !1 = f (xI)I !1 = f (x) ˜ =f
- 43. Polarizing a quadric with respect to another Let S : G ! G and T : G ! G be symmetric outermorphisms, and let P = {x ! G : x quot; S(x) = 0 , x # 0} , Q = {x !G : x quot; T(x) = 0 , x # 0} be the corresponding two quadrics. Polarizing the multivectors of the quadric P Fact: with respect to the quadric Q gives a quadric R ˜ with equation x ! (T o S o T(x)) = 0 x ! P ! PolQ (x) ! R . and we have
- 44. The reciprocal quadric P : x ! S(x) = 0 Polarizing the quadric Q : x ! T(x) = 0 with respect to the quadric ˜ R : x ! (T o S o T(x)) = 0 generates the quadric R Q P
- 45. Cartesian-Affine-Projective relationships n n V x x = x + en+1 Œ A * Œ quot;1 n+1 n y = (y ! en+1 ) y quot; en+1 n y V V ŒV Œ * well The affine part of n y n defined P V Œ Projective Space: en+1 n x y n P V * Œ quot;1 (y ! en+1 ) y x * n space A fine Af n+1 V en e1 y n space V x = * *x * sian Carte
- 46. The intersection of two lines in the plane *( ) a,b,c,d A,B,C,D *( ) p P = (A B) ⁄ (C D) ⁄ ⁄ e3 C B P A e plan ne Affi D c b p a e n 2 n pla R d ia artes C
- 47. The intersection of two lines (cont.) P = (A ! B) quot; (C ! D) = [ A ! B ! C ]D quot; [ A ! B ! D ]C = !D quot; #C [ A ! B ! C ] = ( A ! B ! C) I quot;1 = ((a + e ) ! (b + e ) ! (c + e ))e e e 3 3 3 3 21 = ((a ! c) quot; (b ! c) quot; (c + e ))e e e 0= 3 3 2 1 = ((a ! c) quot; (b ! c) quot; c)e3e2e1 + ((a ! c) quot; (b ! c) quot; e3 )e3e2 e1 = ((a ! c) quot; (b ! c)e3 )e3e2e1 does not contain e3 = (a ! c) quot; (b ! c)e2 e1 ! quot;
- 48. The intersection of two lines (cont.) does not In the same way we get contain e3 ! = [ A quot; B quot; D ] = ( A ! B ! D) I quot;1 = (a ! d) quot; (b ! d)e2e1 Hence we can write p as: p = * P = * (!D quot; #C) quot;1 = ((!D quot; #C) $e3 ) (!D quot; #C) quot; e3 quot;1 = (! quot; #) (!d + !e3 quot; #c quot; #e3 ) quot; e3 quot;1 = (! quot; #) (!d quot; #c) does not e3 contain
- 49. Reflection in a plane-curve mirror m(s+ds) m m1 t = m(s) = m(s) = . s t1 = t(s+ds) M u -t(p-m)t = p u1 = - t1(p-m1)t1 in-caustic q = lim (m u) ⁄ (m1 u1) ⁄ ⁄ 0 ds r out-caustic curvature centre of the mirror
- 50. Reflection in a plane-curve mirror (cont.) Making use of the intersection formula deduced earlier ˙ t n= and introducing for the unit mirror normal ˙ t we get (( p ! m)quot; t)t ! ( p ! m) quot; n)n q!m= 2 ( p ! m) 1! 2m˙˙ ( p ! m) quot; n This is an expression of Tschirnhausen’s reflection law.
- 51. Reflection in a plane-curve mirror (cont.) m u p v Tschirnhausens q reflection formula r 1 1 2 ± = u!m q!m v!m
- 52. References: Hestenes, D. & Ziegler, R., Projective Geometry with Clifford Algebra, Acta Applicandae Mathematicae 23, pp. 25-63, 1991. Naeve, A. & Svensson, L., Geo-Metric-Affine-Projective Unification, Sommer (ed.), Geometric Computations with Clifford Algebra, Chapter 5, pp.99-119, Springer, 2000. Winroth, H., Dynamic Projective Geometry, TRITA-NA-99/01, ISSN 0348-2953, ISRN KTH/NA/R--99/01--SE, Dissertation, The Computational Vision and Active Perception Laboratory, Dept. of Numerical Analysis and Computing Science, KTH, Stockholm, March 1999.
