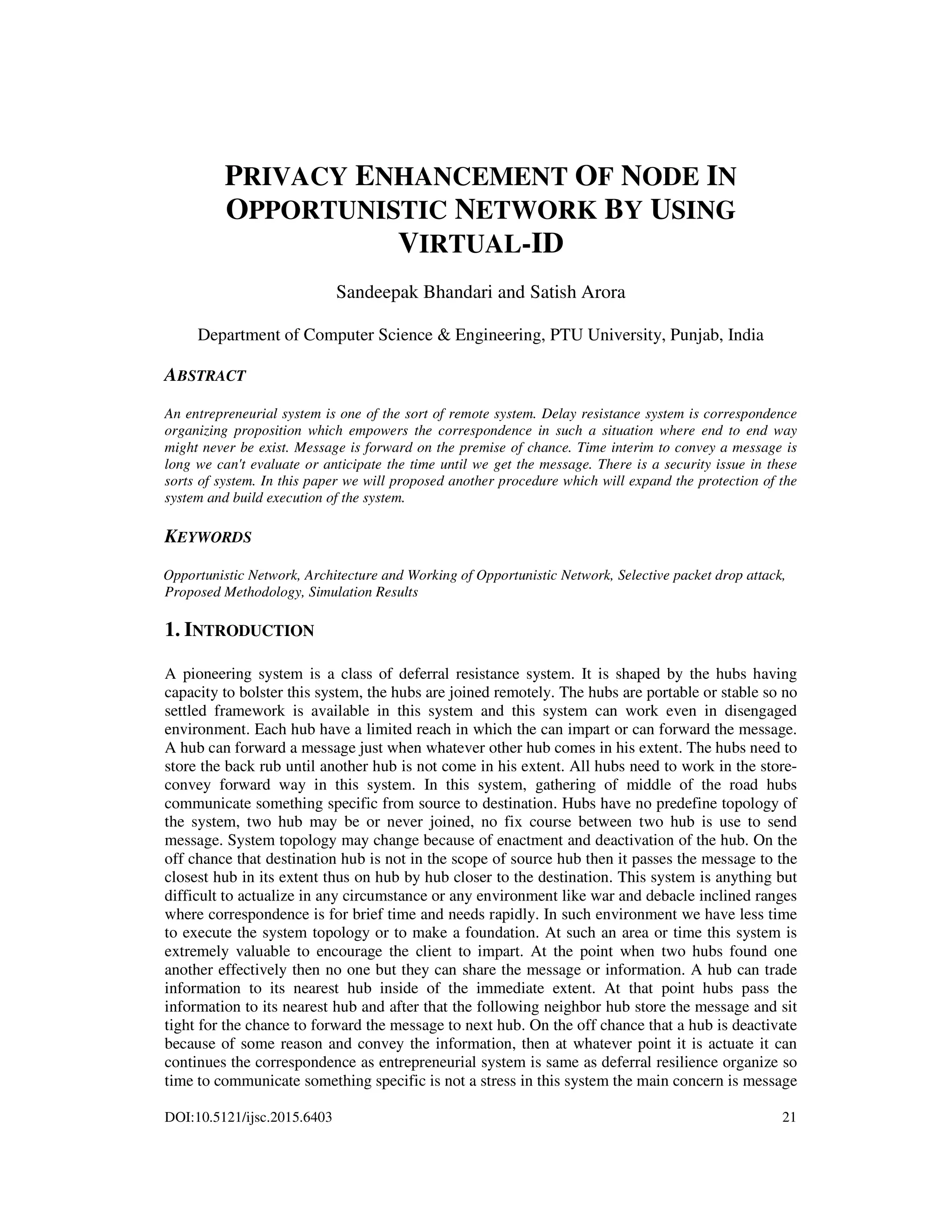
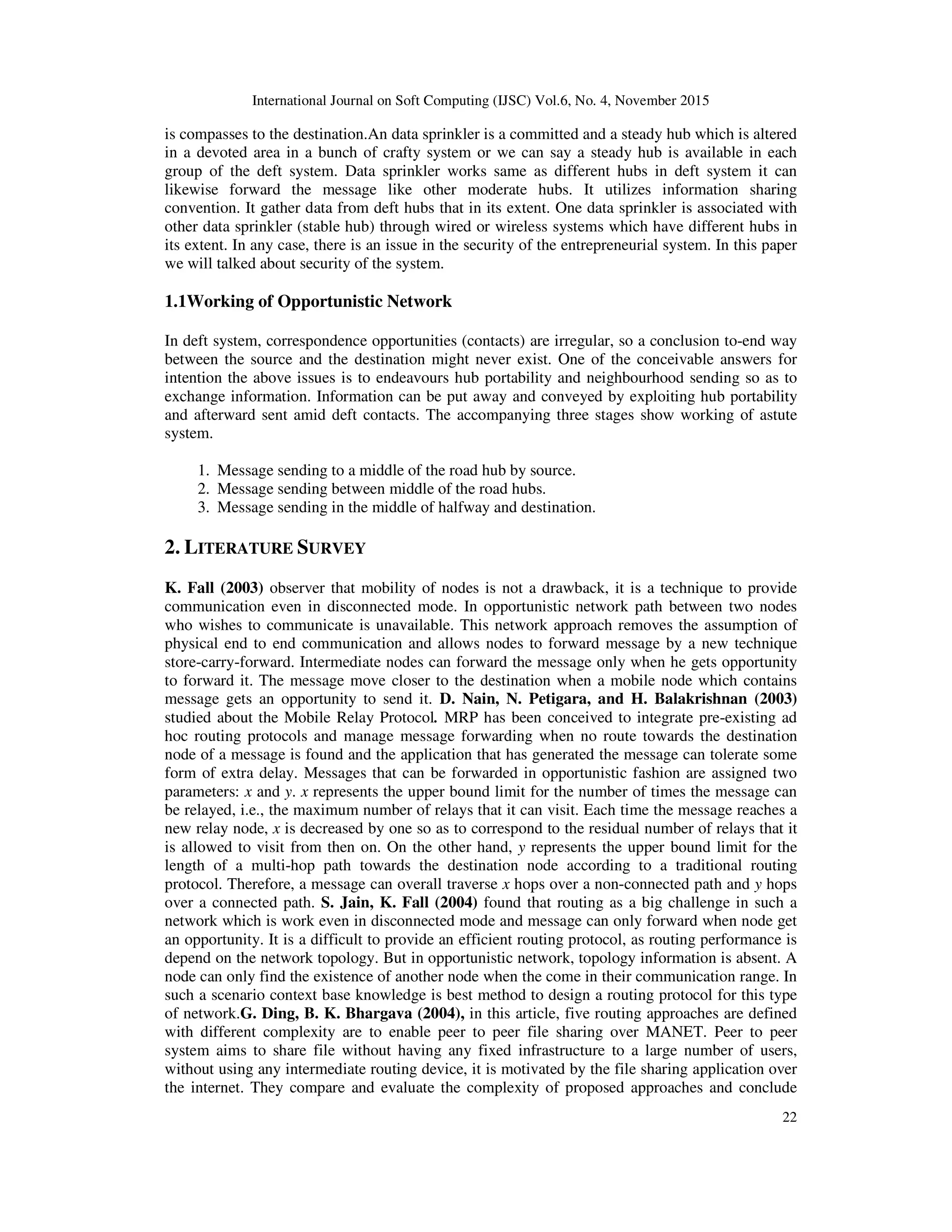
The paper presents a method to enhance privacy in opportunistic networks through the use of virtual IDs. It discusses the challenges of communication in such networks, including security vulnerabilities like selective packet drop attacks, and proposes a new approach that involves user authentication and secure data transmission via virtual IDs assigned by trusted nodes. Simulation results indicate that the proposed methodology improves privacy, reduces packet loss, and increases throughput compared to existing methods.
![International Journal on Soft Computing (IJSC) Vol.6, No. 4, November 2015
29
which diminishes the client work by giving some new instrument to conceal the id of client.
Because of foundation less building design and versatility of the hubs, sharp system faces
numerous issues identified with security, protection, hubs verification and proficient steering
convention.
REFERENCES
[1] Jia Jianbin, Chen Yingwen, Xu Ming, Xia Geming, and Xiao Xiaoqiang,(2013) “Towards the Benefit
of Multi-Hop Relaying in Opportunistic Networking”,IEEE International Conference on Green
Computing and Communications and IEEE Internet of Things and IEEE Cyber, Physical and Social
Computing ,pp.658-662.
[2] Augustin Chaintreau, Pan Hui, Jon Crowcroft, Christophe Diot, Richard Gass, and James Scott,(2006)
“ Impact of Human Mobility on the Design of Opportunistic Forwarding Algorithms”, IEEE Infocom.
IEEE Computer Society
[3] Papaj Jan, Dobos Eubomir and Cumar,(2012)“ Opportunistic Networks and Security”Journal of
Electrical and Electronics Engineering, vol. 5,no.1.
[4] L. Lilien, Z. H. Kamal, V. Bhuse, and A. Gupta,(2006) “The Concept of Opportunistic Network and
their Research Challenges in Privacy and Security”,”Mobile and Wireless Network Security and
Privacy”, Book Chapter, pp. 85-117.
[5] L. Pelusi, A. Passarella, and M. Conti,(2006) “Opportunistic Networking: data forwarding in
disconnected mobile ad hoc networks”, IEEE Communications Magazine, vol. 44, no.11, Nov.
[6] D. Nain, N. Petigara, and H. Balakrishnan,(2003) “Integrated Routing and Storage for Messaging
Applications in Mobile Ad Hoc Networks”, in Proceedings of WiOpt, Autiplis, France, March.
[7] S. Jain, K. Fall and R. Patra,(2004) “Routing in a delay tolerant network”, Proceedings of the ACM
Conference on Applications, Technologies, Architectures, and Protocols for Computer
Communications, pp.145–158.
[8] Abdullatif shikfa, Melek Onen and Refik Molva(2010),“Privacy and Confidentiality in context based
and epidemic forwarding” published by Elsevier,pp.1493-1504.
[9] Abdullatif shikfa,Melek Onen and Refik Molva,(2012)“ Local key management in Opportunistic
network”.International Journal Networks and distributed Systems,Vol.9,Nos.1/,pp.97-116.
[10] B.Poonguzharselvi1 and V.Vetriselvi,(2012) “Trust Framework for Data Forwarding in opportunistic
Network Using Mobile Traces”,International Journal of.Wireless Networks Vol.4,No.6.
[11] K. Fall,(2013) “ A delay-tolerant network architecture for challenged internets”, Paper presented in
the Proceedings of the ACM Conference on Applications, Technologies, Architectures, and Protocols
for Computer Communications , pp.27–34.
[12] Xingguang Xie, Yong Zhang, Chao Dai and Mei Song,(2011)"Social relationship enhanced
predicable routing in opportunistic network" Seventh International Conference on Mobile Ad-hoc and
Sensor Networks.
[13] L. Dora, T. Holczer ,Hide and Lie,"Enhancing(2010) Application-level Privacy in Opportunistic
Networks",Proceedings of the Second International Workshop on Mobile Opportunistic Networking
,pp.135-142..
[14] G. Costantino ,F. Martinelli and P.santi,(2012)“ Privacy-preserving interest-casting in opportunistic
networks”,IEEE wireless communications and networking conference: mobile and wireless networks.
AUTHORS
Sandeepak Bhandari seeking his Master of Technology in C.S.E from P.T.U University,
Punjab, India. This paper portrays the examination work Which he finished amid his expert
of innovation.](https://image.slidesharecdn.com/6415ijsc03-151216111704/75/PRIVACY-ENHANCEMENT-OF-NODE-IN-OPPORTUNISTIC-NETWORK-BY-USING-VIRTUAL-ID-9-2048.jpg)