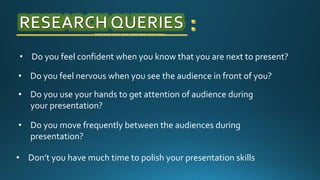
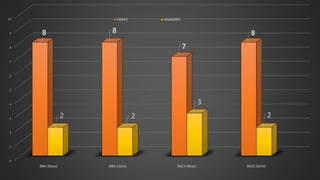
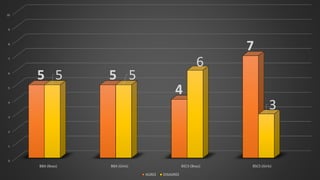
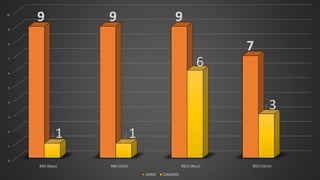
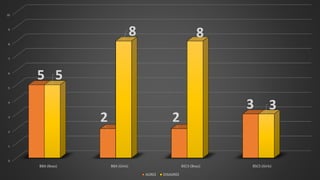
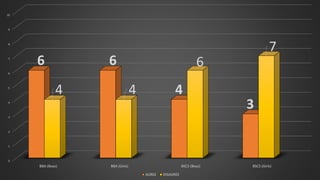
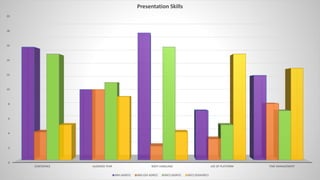
The document explores the presentation skills of business (BBA) and computer science (CS) students, analyzing factors like confidence, audience anxiety, body language, and preparation. It concludes that BBA students generally exhibit better presentation skills than CS students, demonstrating less fear of the audience and more effective engagement strategies. The study highlights the importance of presentation skills for career success and identifies areas for improvement among students in both fields.