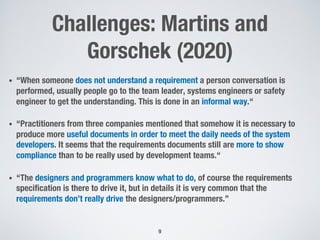
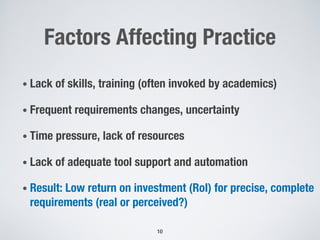
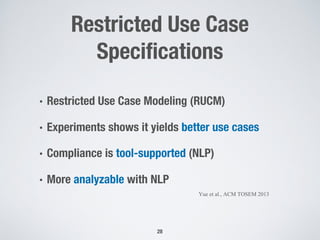
The document discusses the challenges of achieving precise and complete requirements upfront in software development projects. It notes that while academics assume detailed requirements are needed, practitioners find this difficult to achieve in reality due to limited resources, uncertainty, and changing needs. The document provides perspectives from practice that emphasize starting with prototypes and visions rather than detailed specifications. It also summarizes research finding diverse requirements practices across different domains and organizations. The document concludes that while precise requirements may be desirable, they are often elusive goals, and the focus should be on achieving compliance and delivering working software.




![Requirements-Requirements
39
Requirements
C
a
s
e
-
A
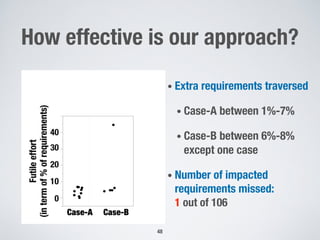
• 160 Requirements
• 9 change scenarios
C
a
s
e
-
B
• 72 Requirements
• 5 change scenarios
[RE 2015, TSE 2015, ESEM 2014, ESEM 2013]](https://image.slidesharecdn.com/briand-mo2re-2024-v2-240416093311-632e7909/85/Precise-and-Complete-Requirements-An-Elusive-Goal-35-320.jpg)

![Diagnostics Manager
<<Decision>>
Is position valid?
<<Decision>>
Over-Temperature
detected?
<<Assignment>>
Error = 1
B3
<<Assignment>>
MotorDriveMode = OFF
<<Assignment>>
MotorDriveMode = RUN
[yes] [no]
[yes]
[no]
Activity Diagrams (AD)](https://image.slidesharecdn.com/briand-mo2re-2024-v2-240416093311-632e7909/85/Precise-and-Complete-Requirements-An-Elusive-Goal-52-320.jpg)