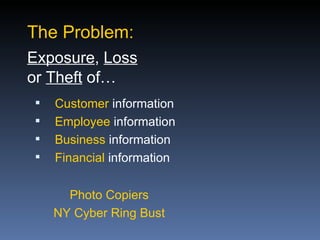
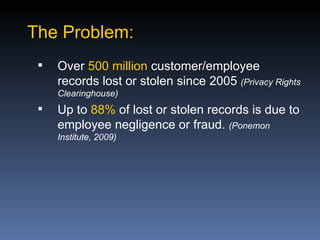
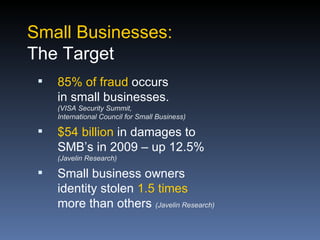
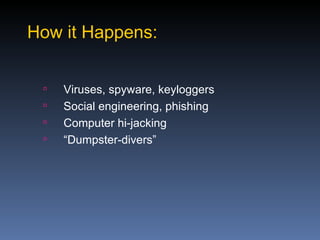
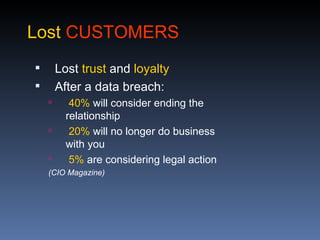
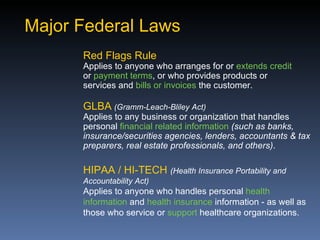
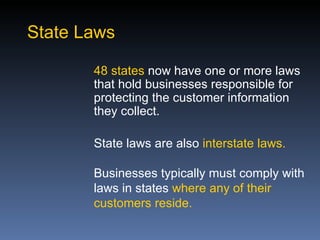
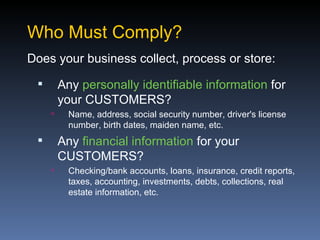
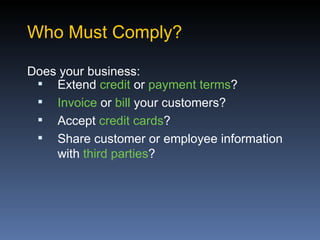
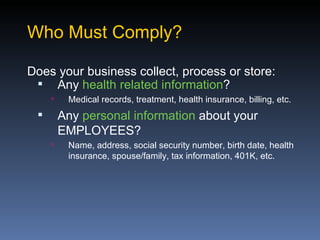
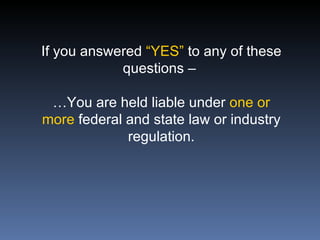
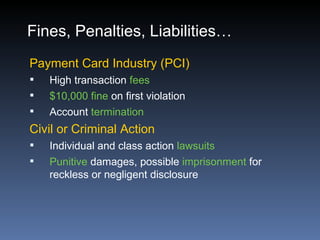
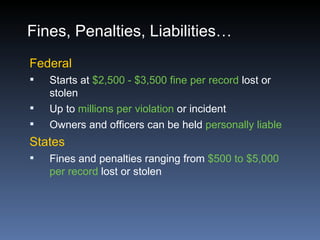
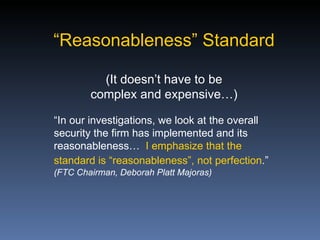
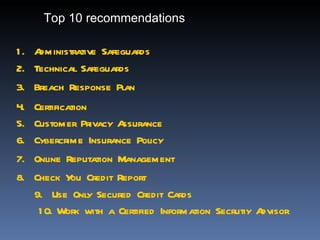
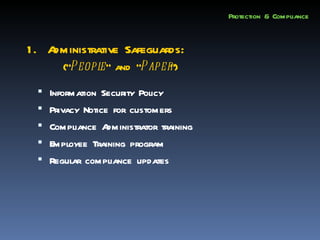
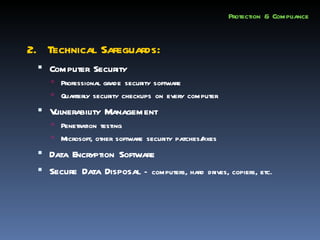
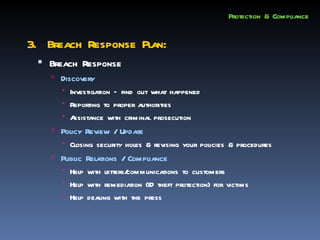
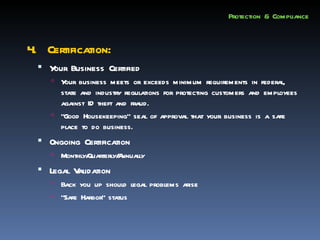
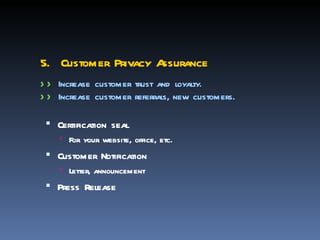
This document discusses protecting businesses from identity theft and fraud, which is described as the greatest threat of the 21st century. It notes that identity theft directly impacts businesses through their customers and employees. Businesses must comply with various federal and state regulations regarding privacy and security of personal and financial information. The document outlines how identity theft can occur and have devastating consequences for businesses through lost customers, damaged reputation, stolen money, and high costs of recovery. It recommends businesses take administrative, technical, and policy measures to protect against threats and comply with relevant laws.