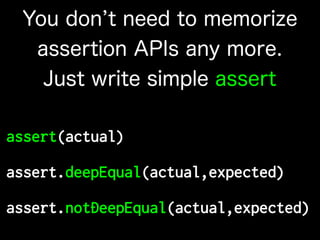
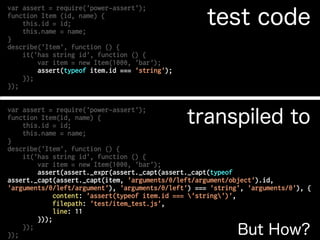
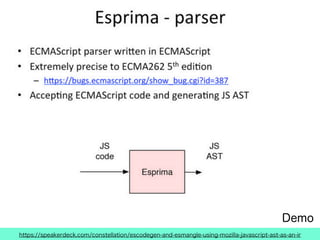
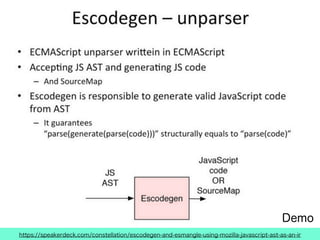
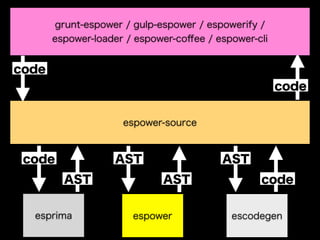
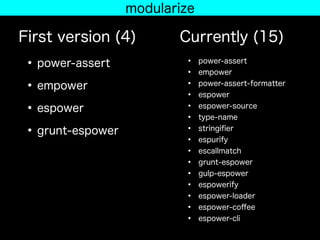
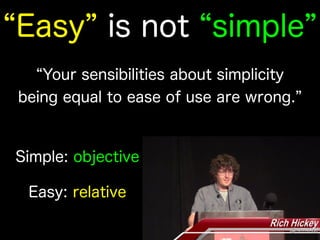
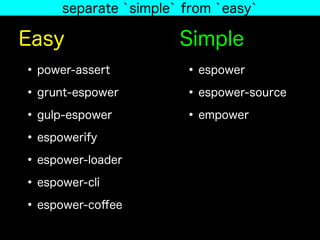
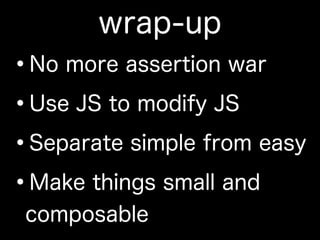
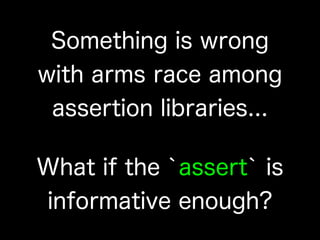
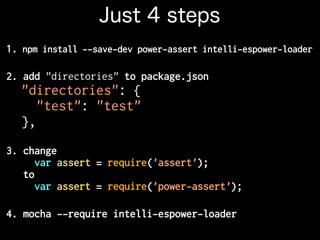
The document introduces power-assert, a testing library designed to simplify assertions in JavaScript tests, arguing against the complexity of numerous assertion libraries. It details the installation and usage of power-assert, emphasizing its ability to provide informative failure messages without requiring memorization of various assertion APIs. The document also discusses the underlying mechanism, design philosophy, and principles of modularity and simplicity in programming.


![assert(typeof item.id === 'strong')
| | | |
| | | false
| | "foo"
| Item{id:"foo",name:"bar"}
"string"
--- [string] 'strong'
+++ [string] typeof item.id
@@ -1,6 +1,6 @@
str
-o
+i
ng
You get this
work unobtrusively, fail noisily](https://image.slidesharecdn.com/power-assert-nodefest-2014-141115024050-conversion-gate01/85/power-assert-mechanism-and-philosophy-9-320.jpg)