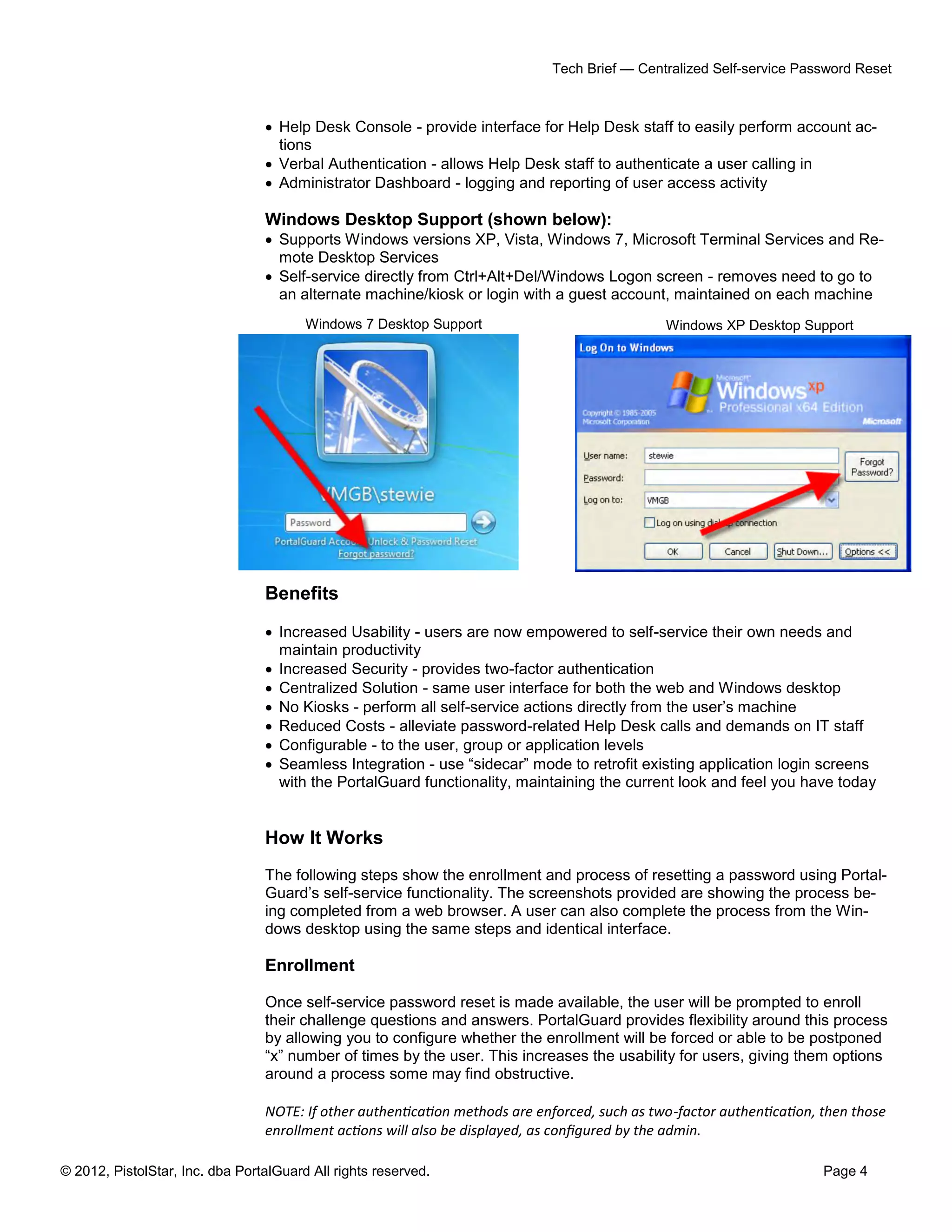
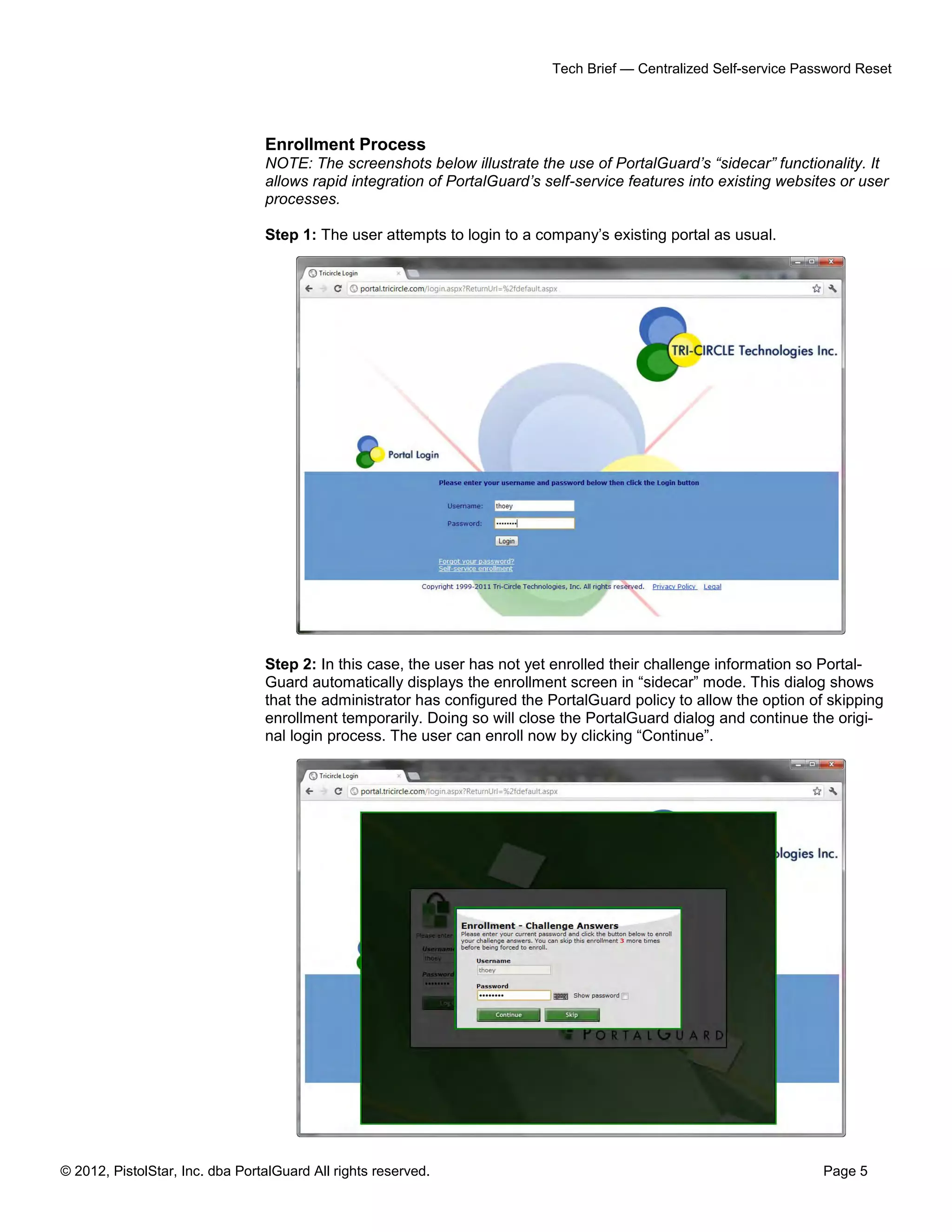
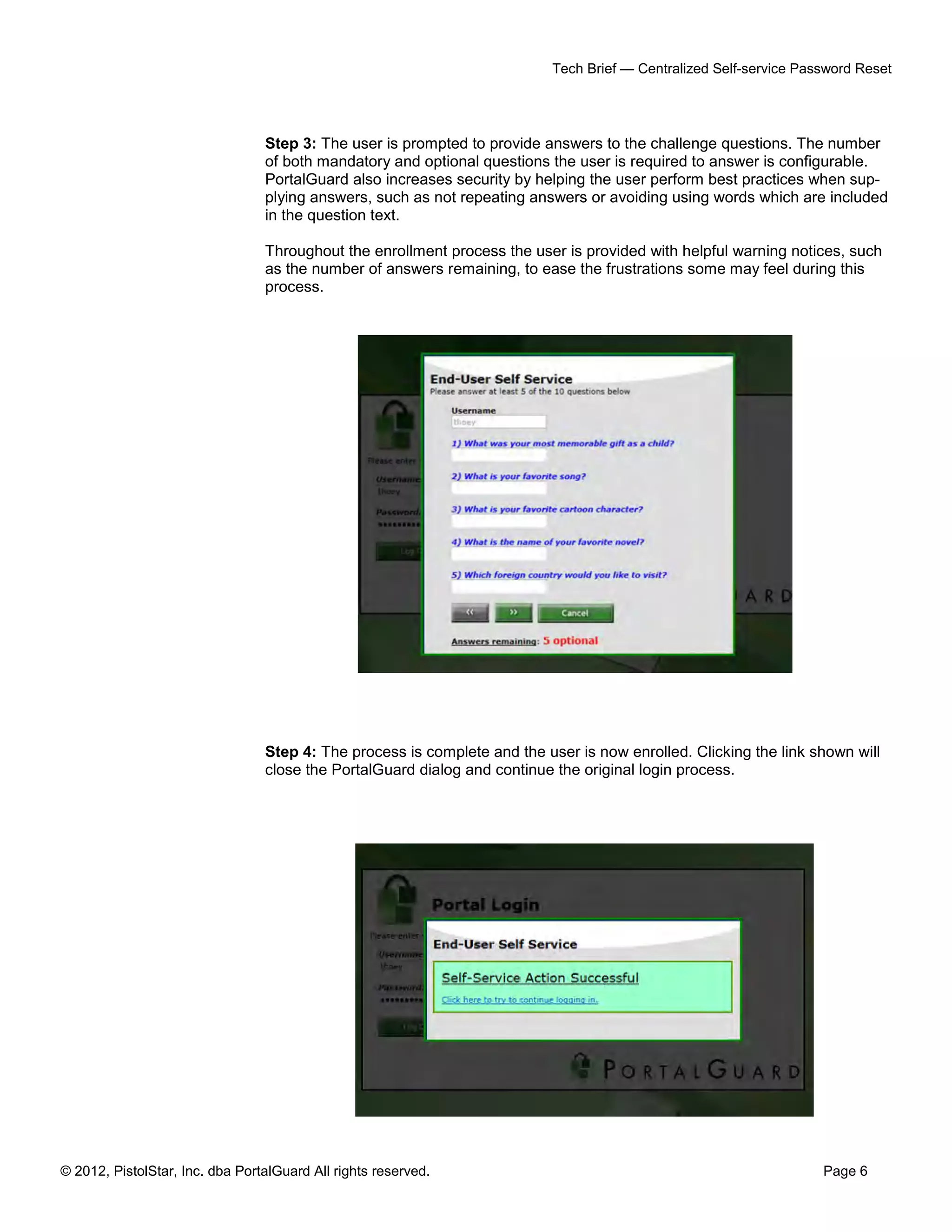
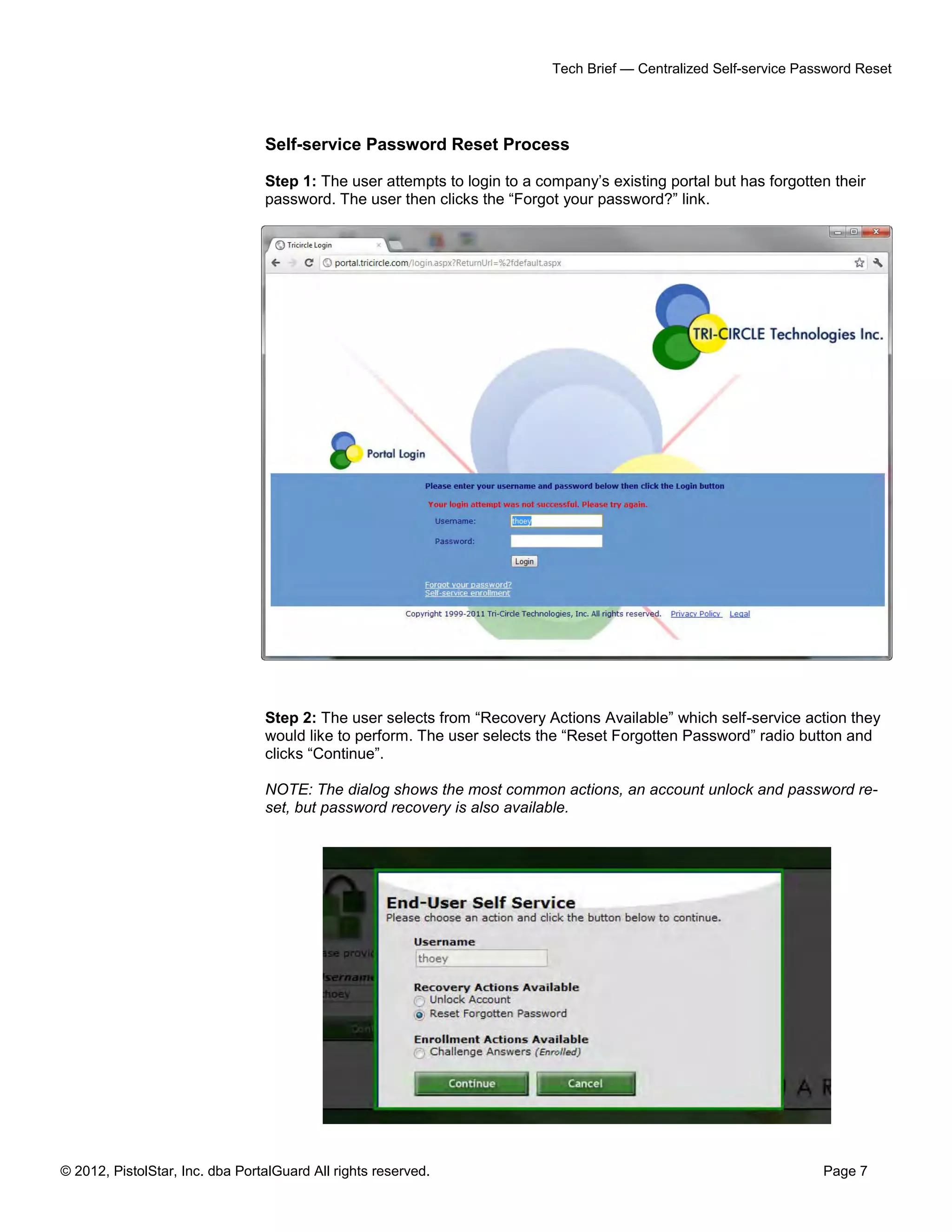
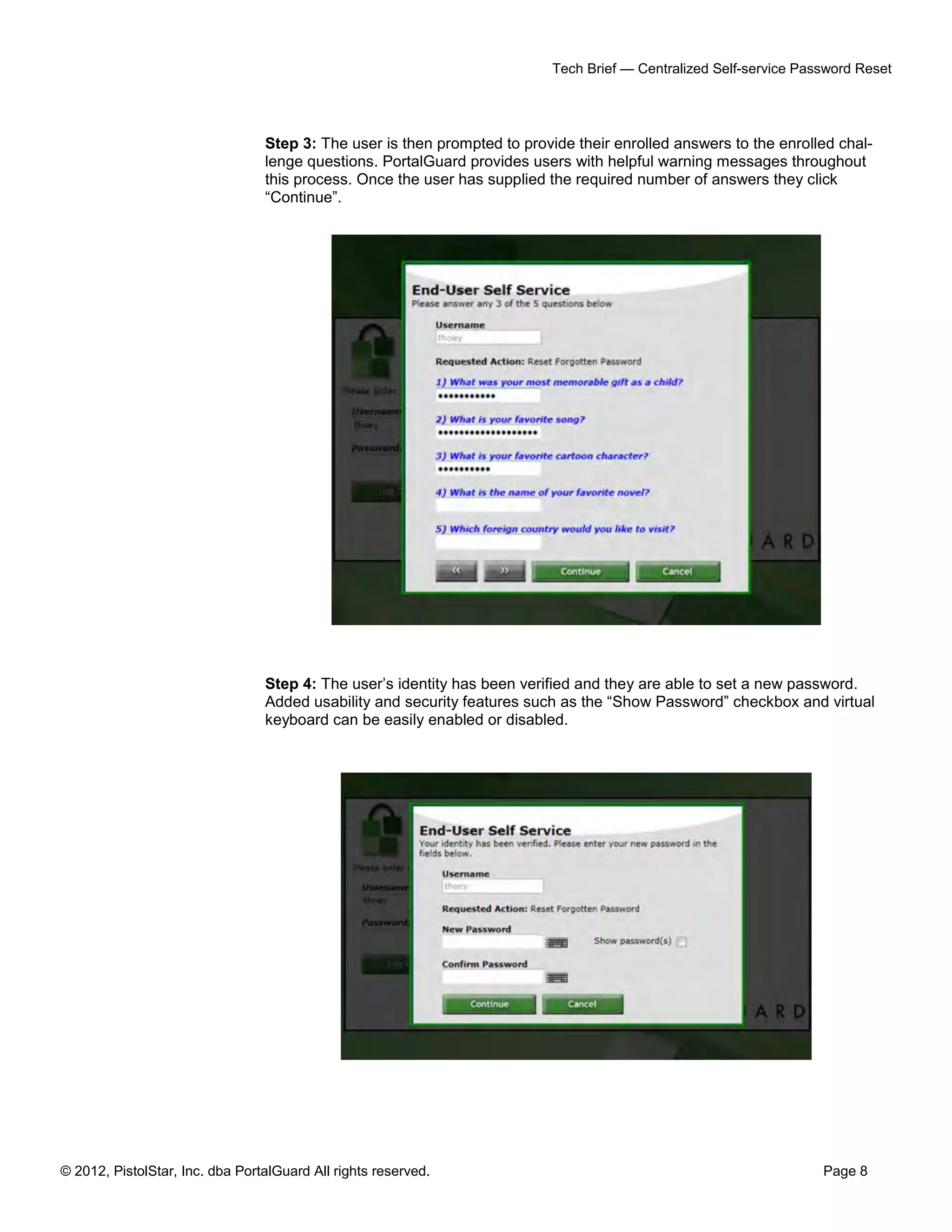
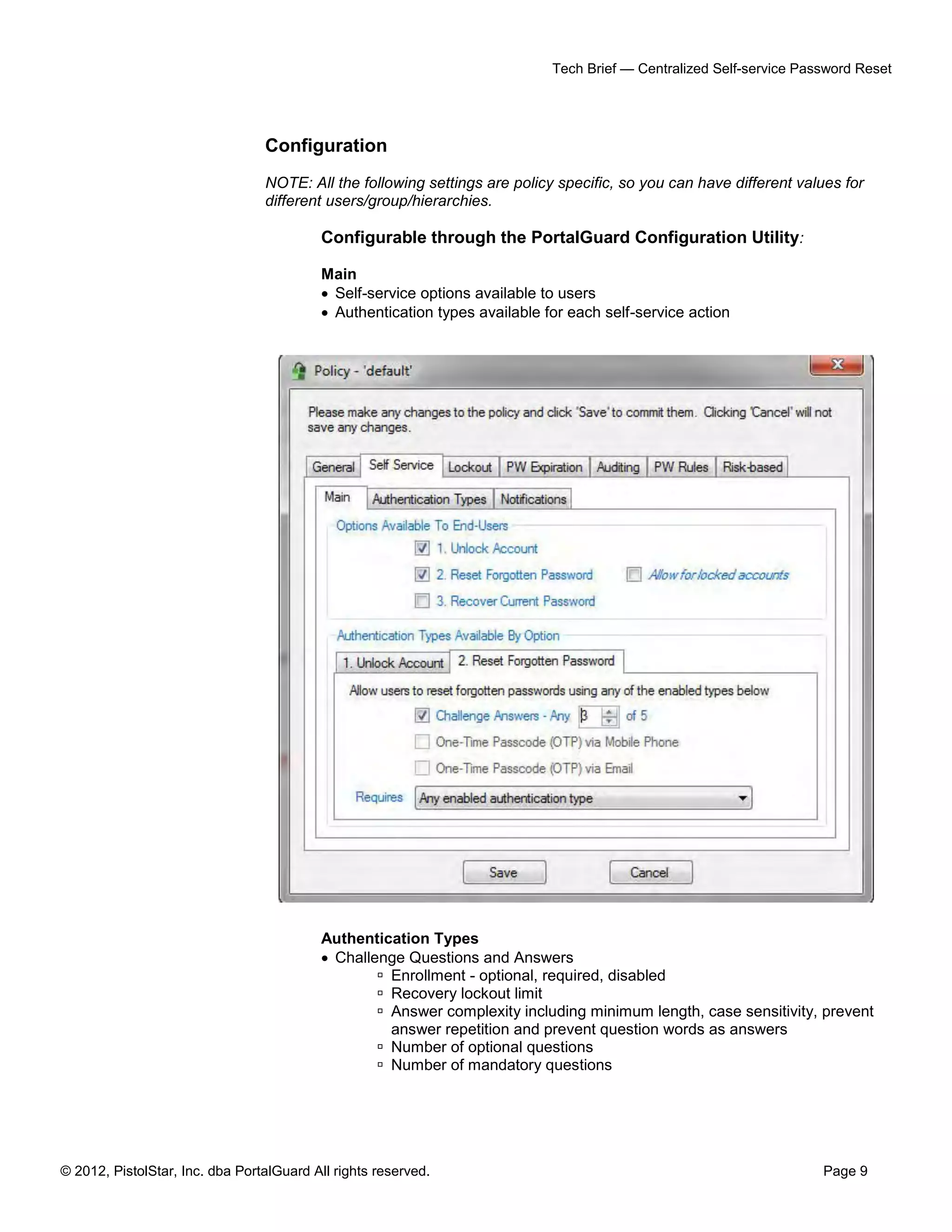
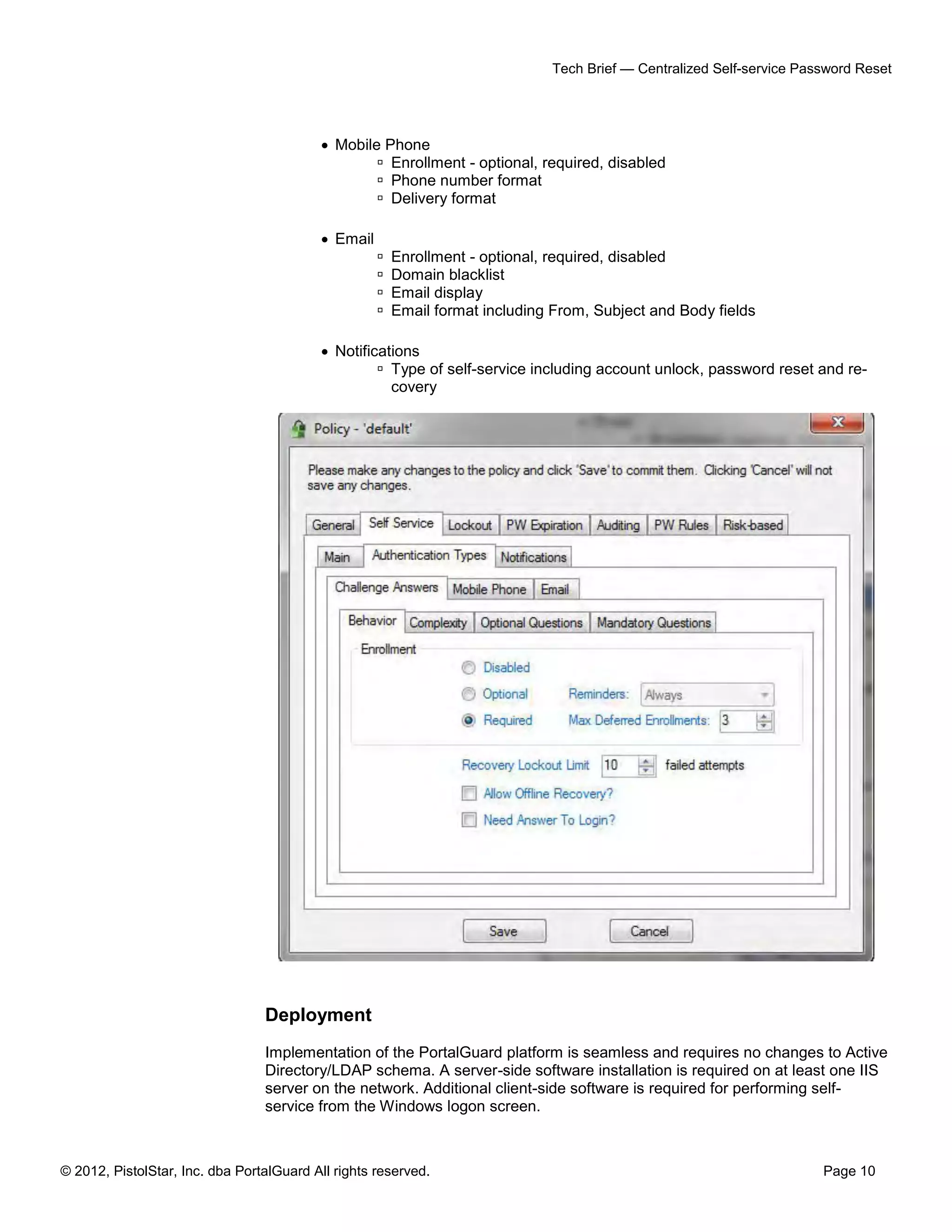
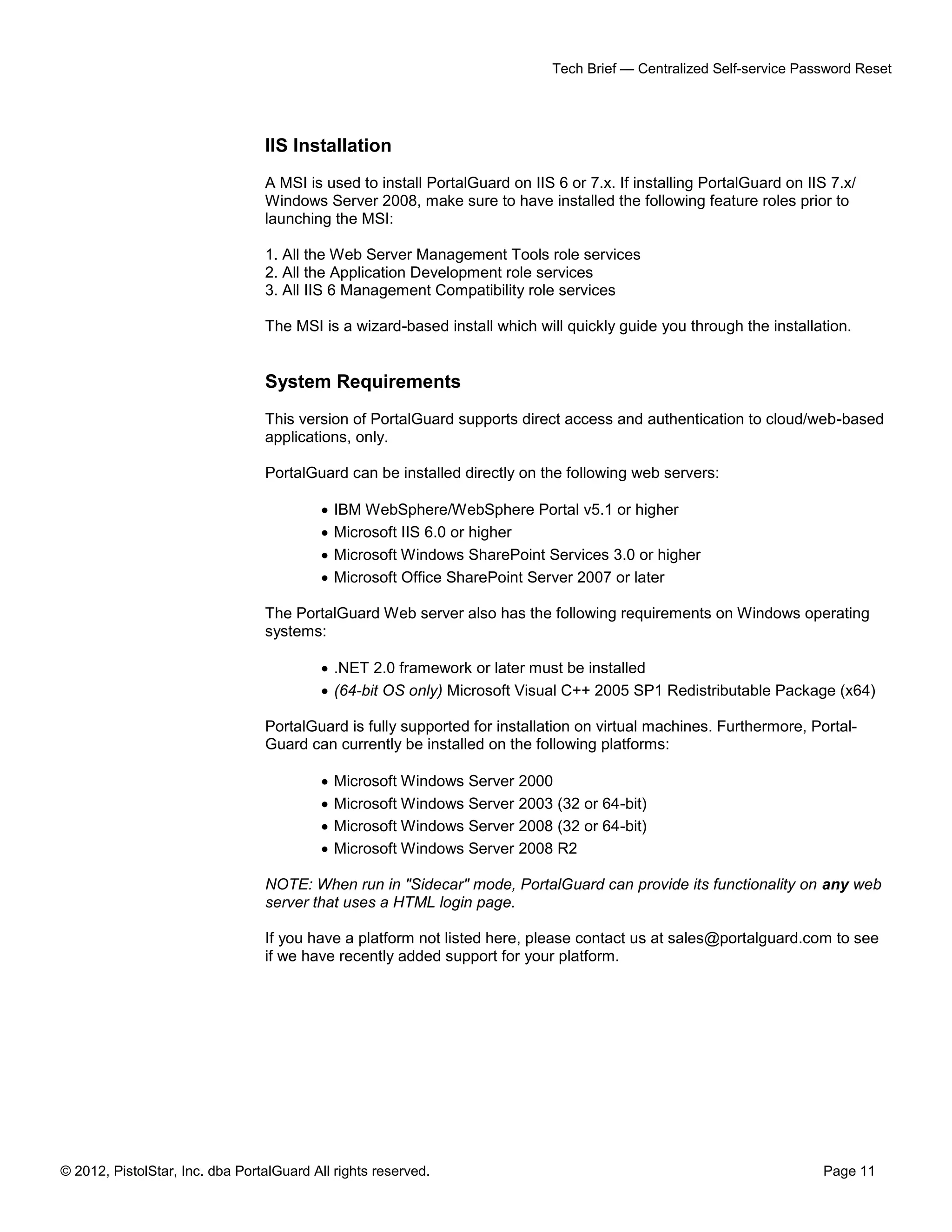
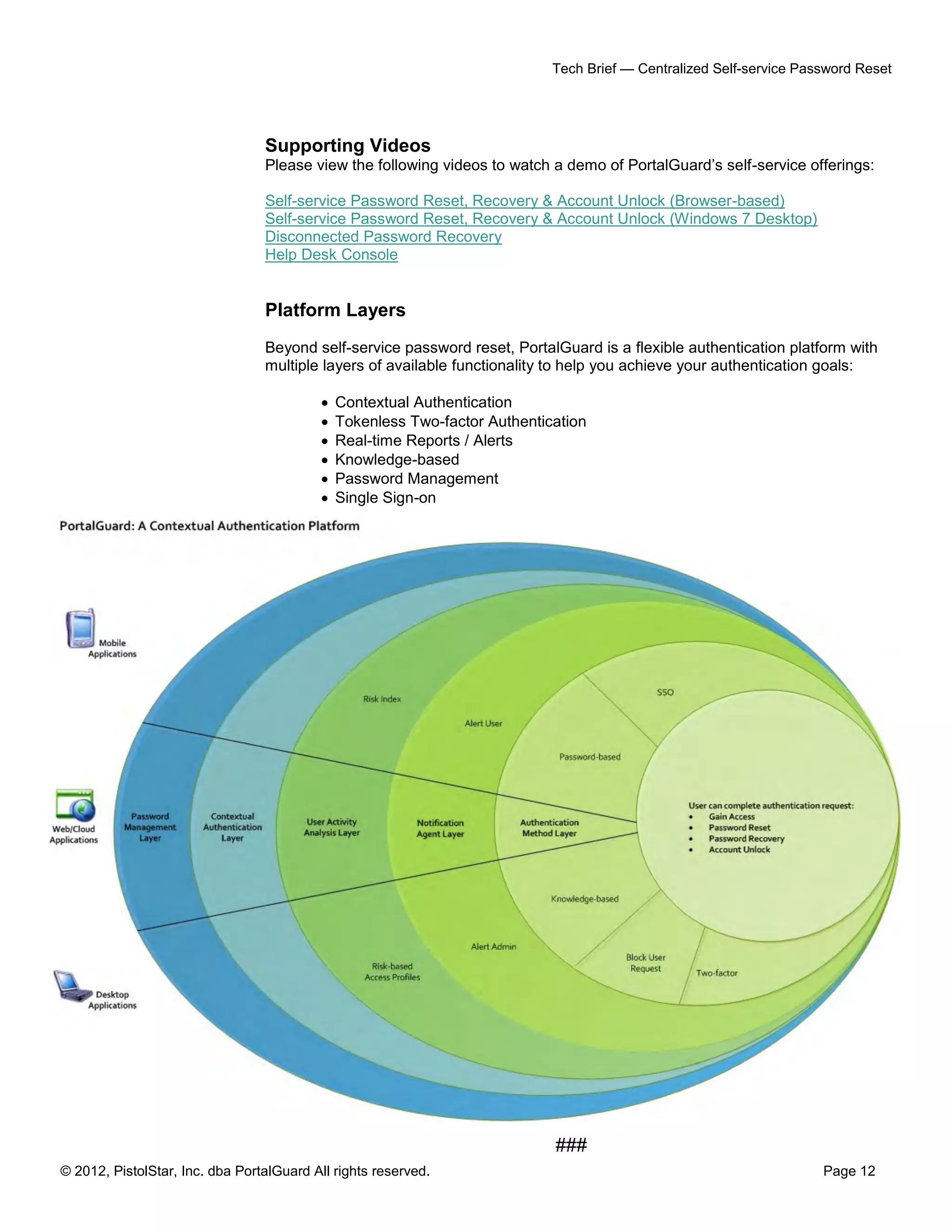
PortalGuard offers a centralized self-service password reset solution designed to reduce the burden on IT staff and help desks by allowing users to manage their own password recovery and account unlock processes. The system supports various authentication methods, including challenge questions and two-factor authentication, ensuring security while accommodating disconnected users. It integrates seamlessly with existing directories and can significantly lower help desk costs and improve user satisfaction.