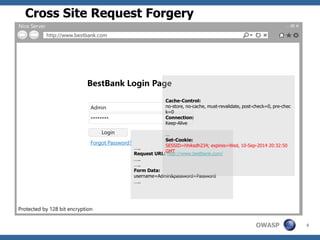
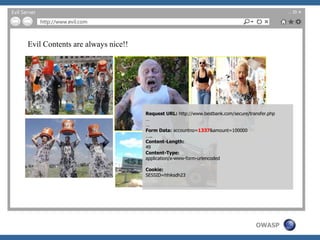
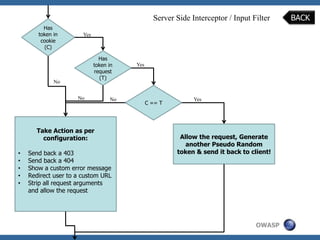
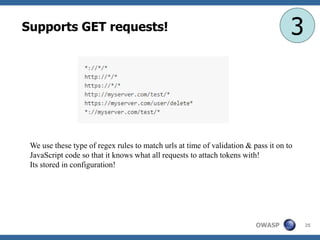
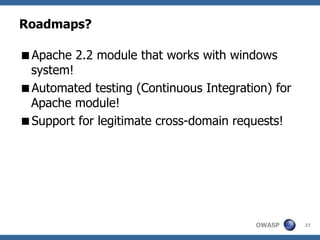
The document discusses the OWASP CSRF Protector project, which aims to mitigate cross-site request forgery (CSRF) vulnerabilities in web applications. It provides an overview of the CSRF concept, the architecture of the protector, its implementation, and future plans. Key features include a standalone PHP library and an Apache module, emphasizing customization and security measures to protect user requests.