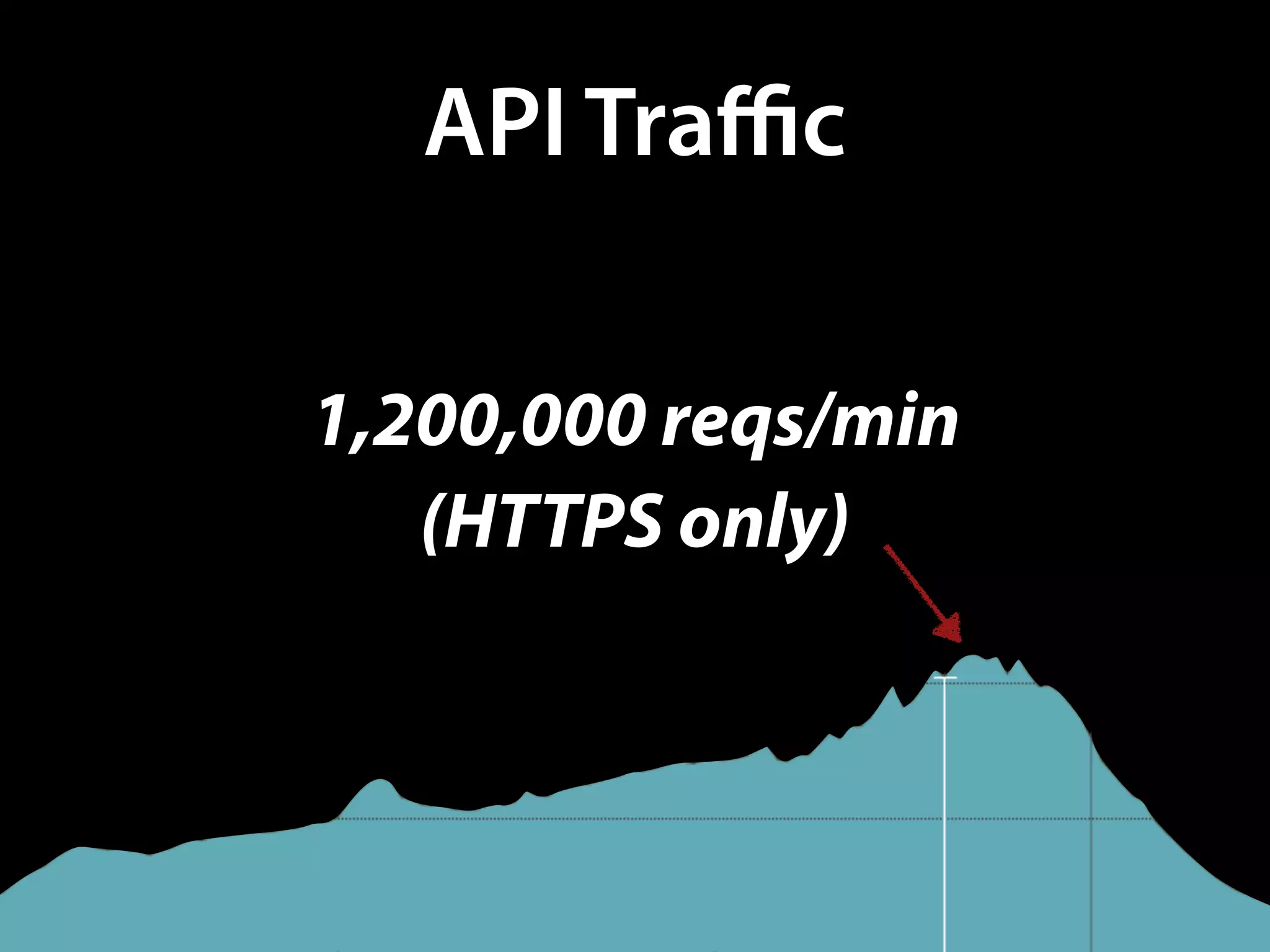
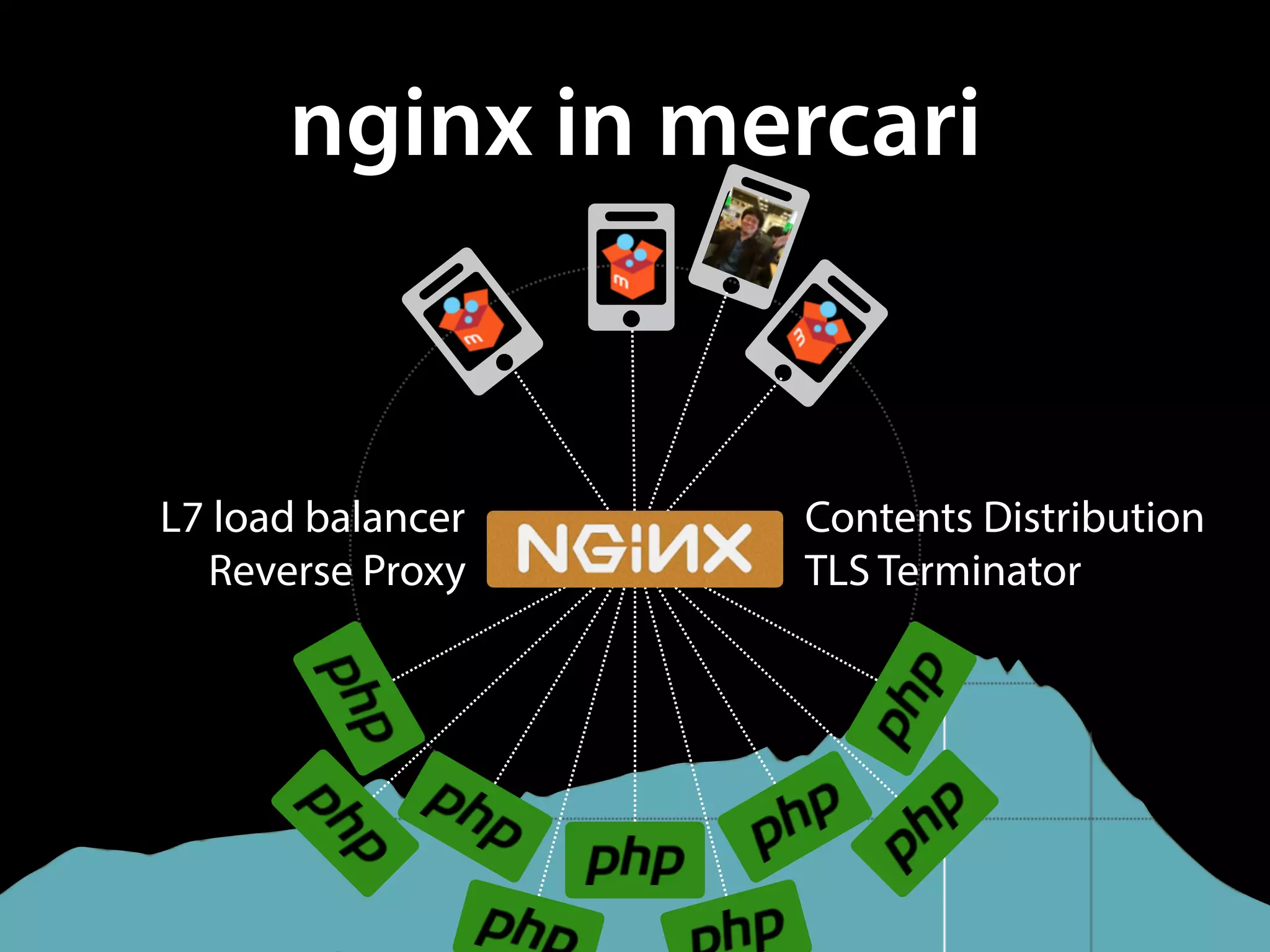
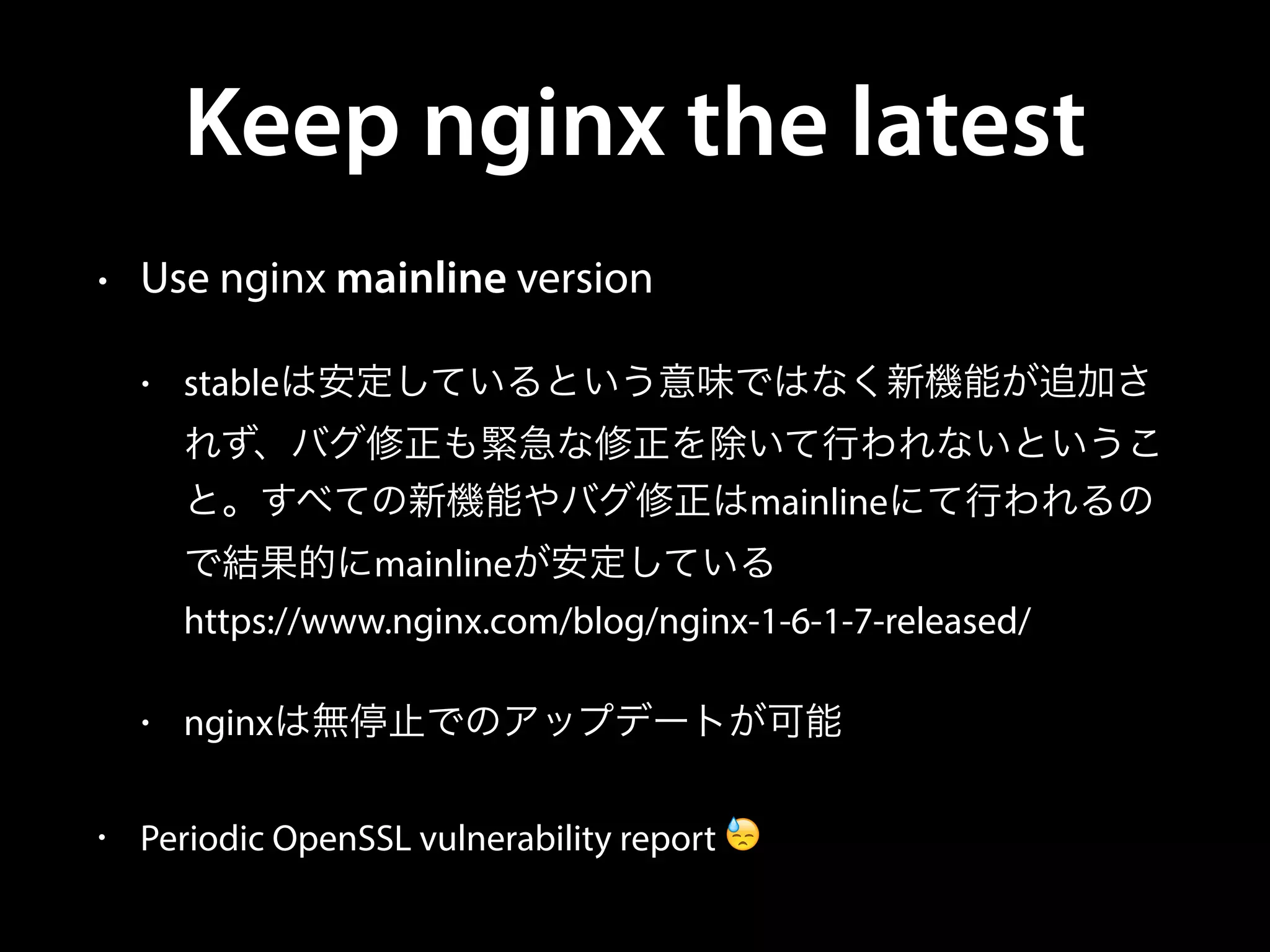
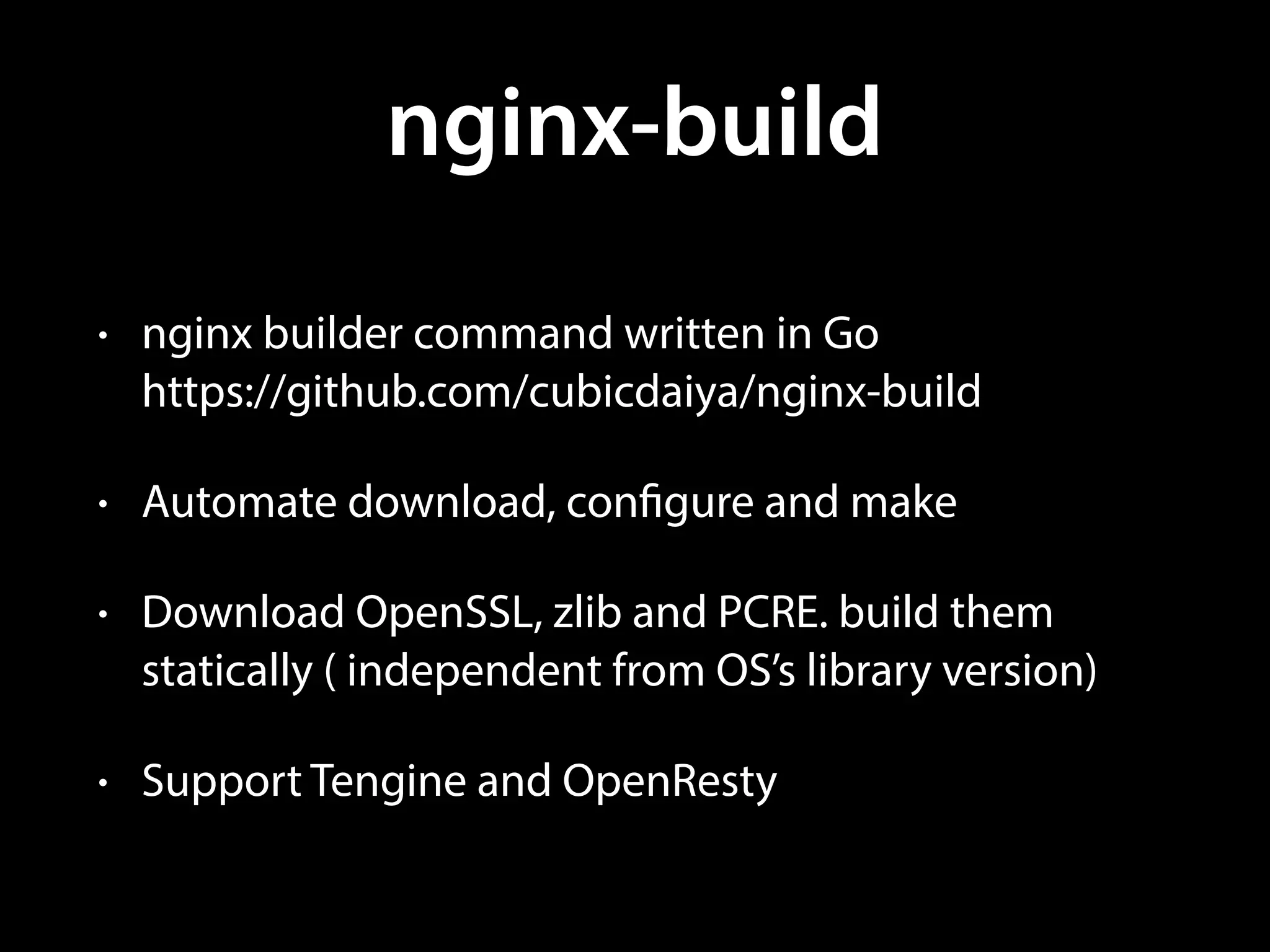
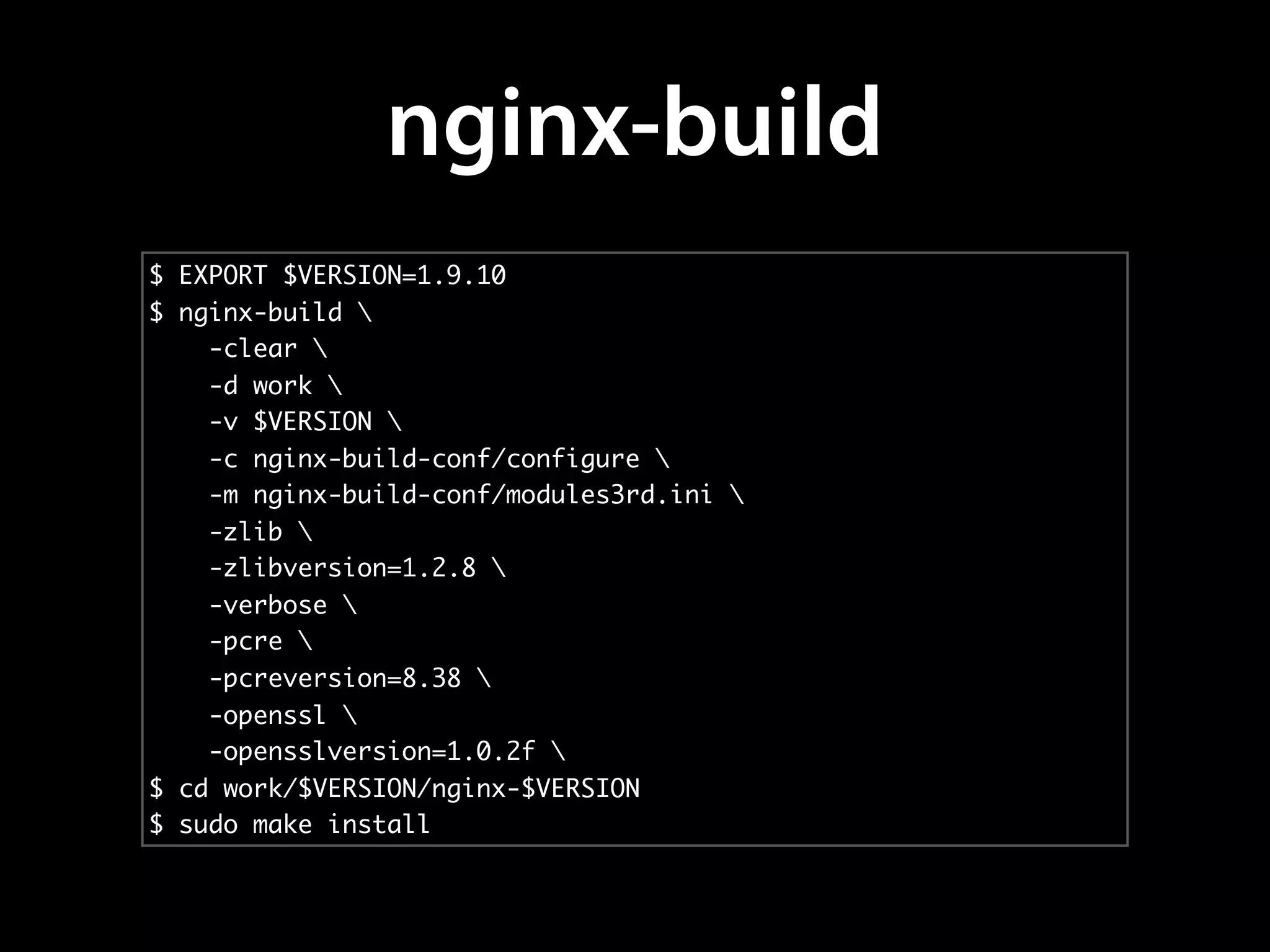
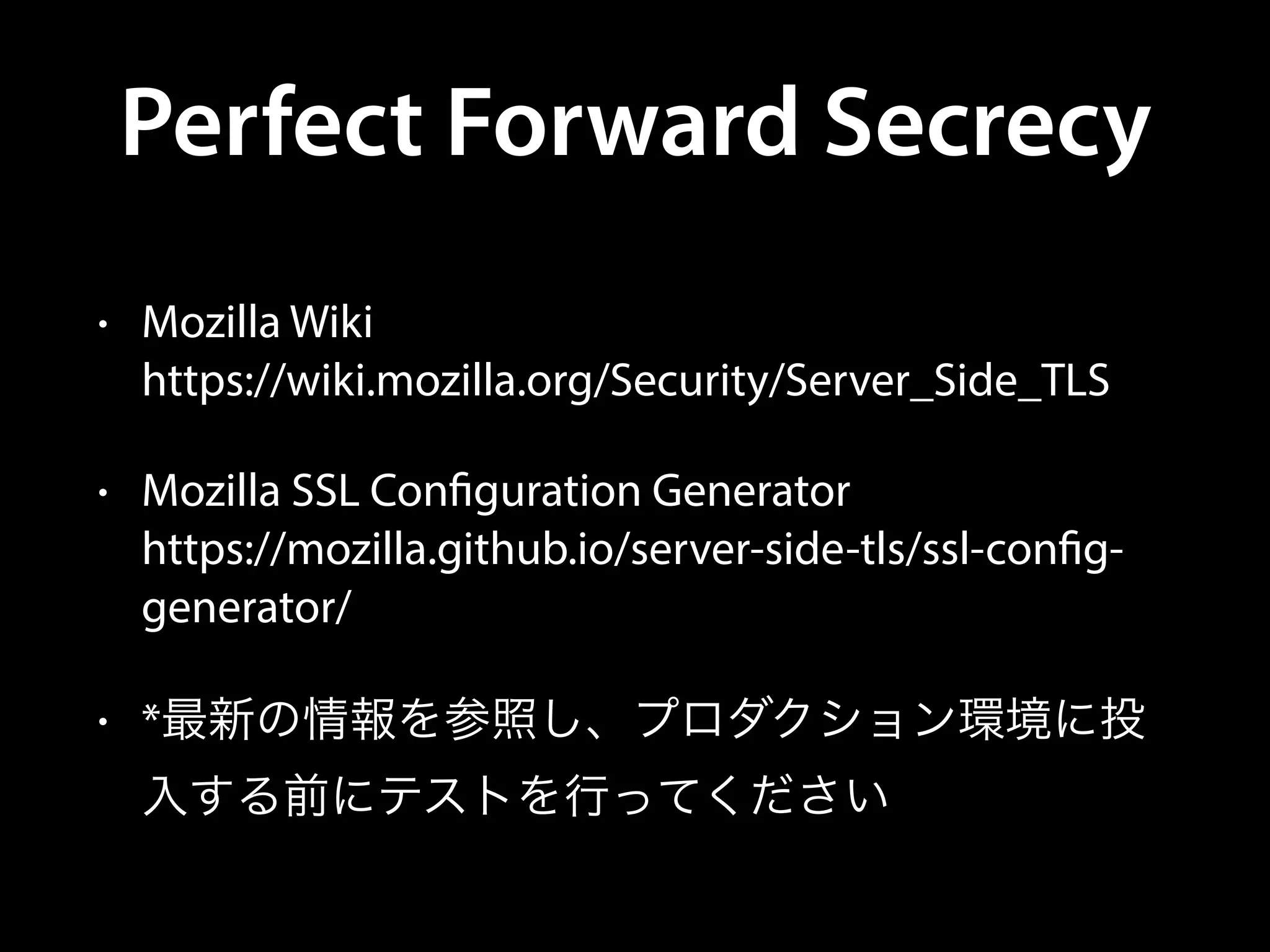
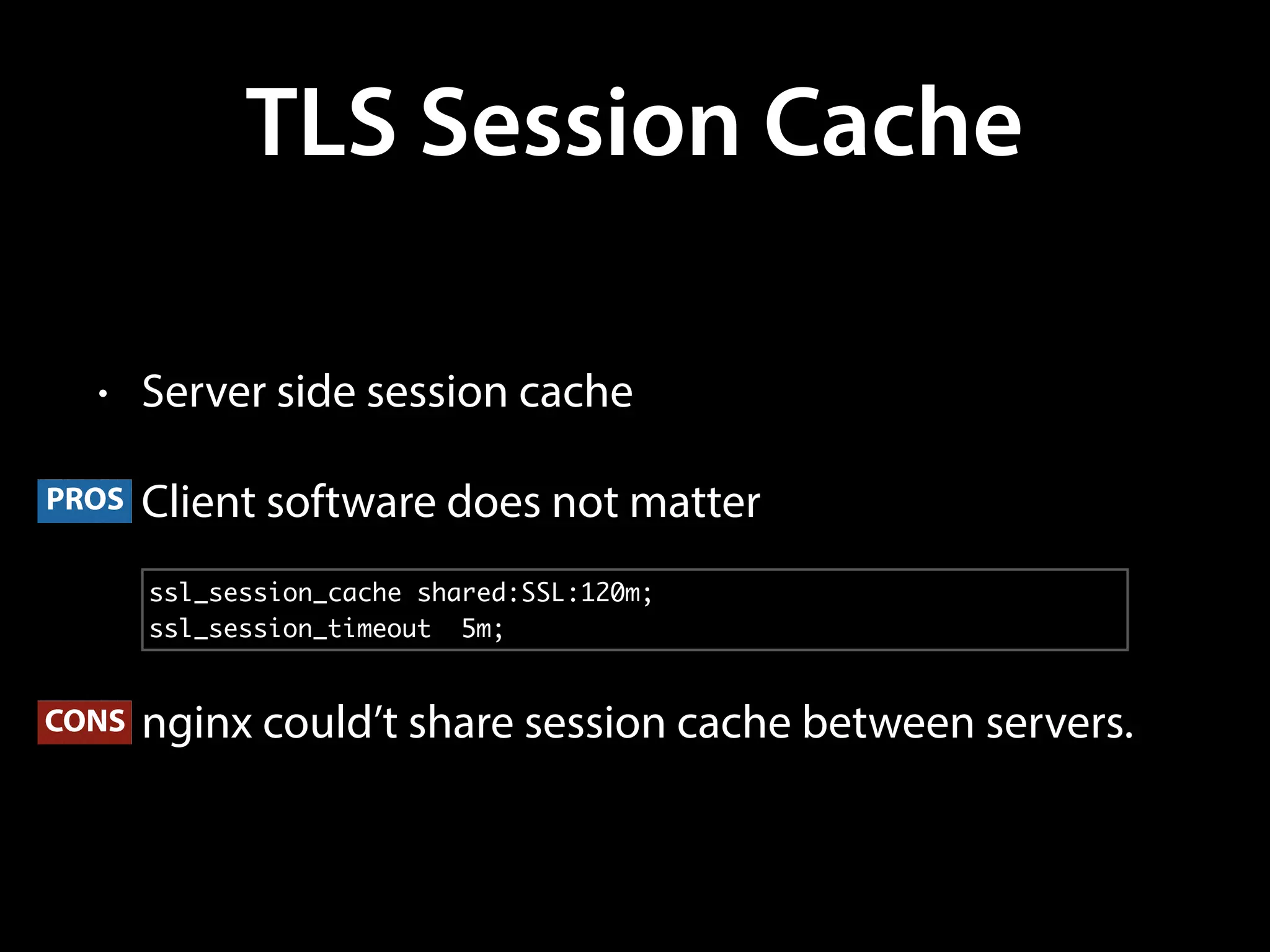
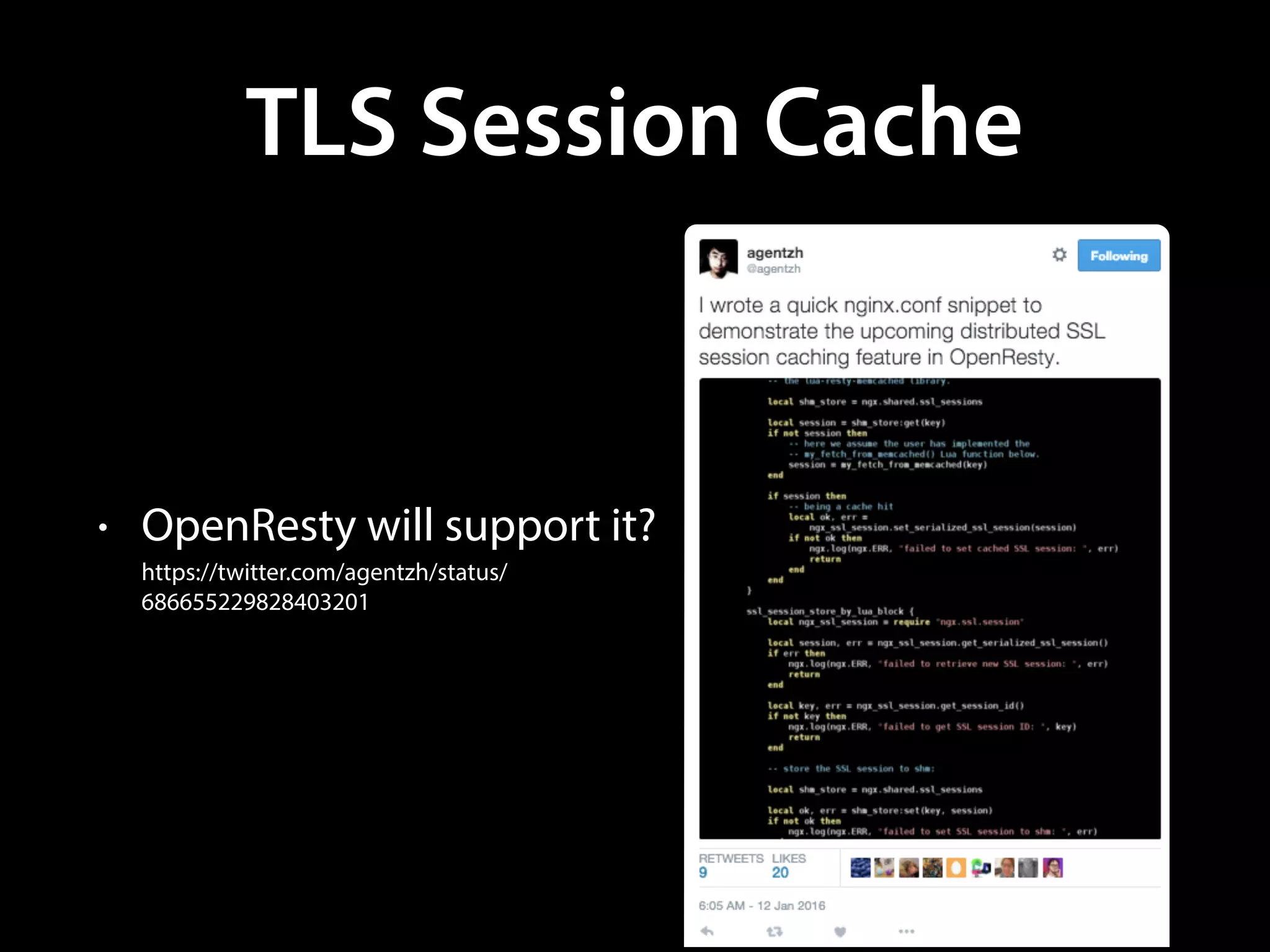
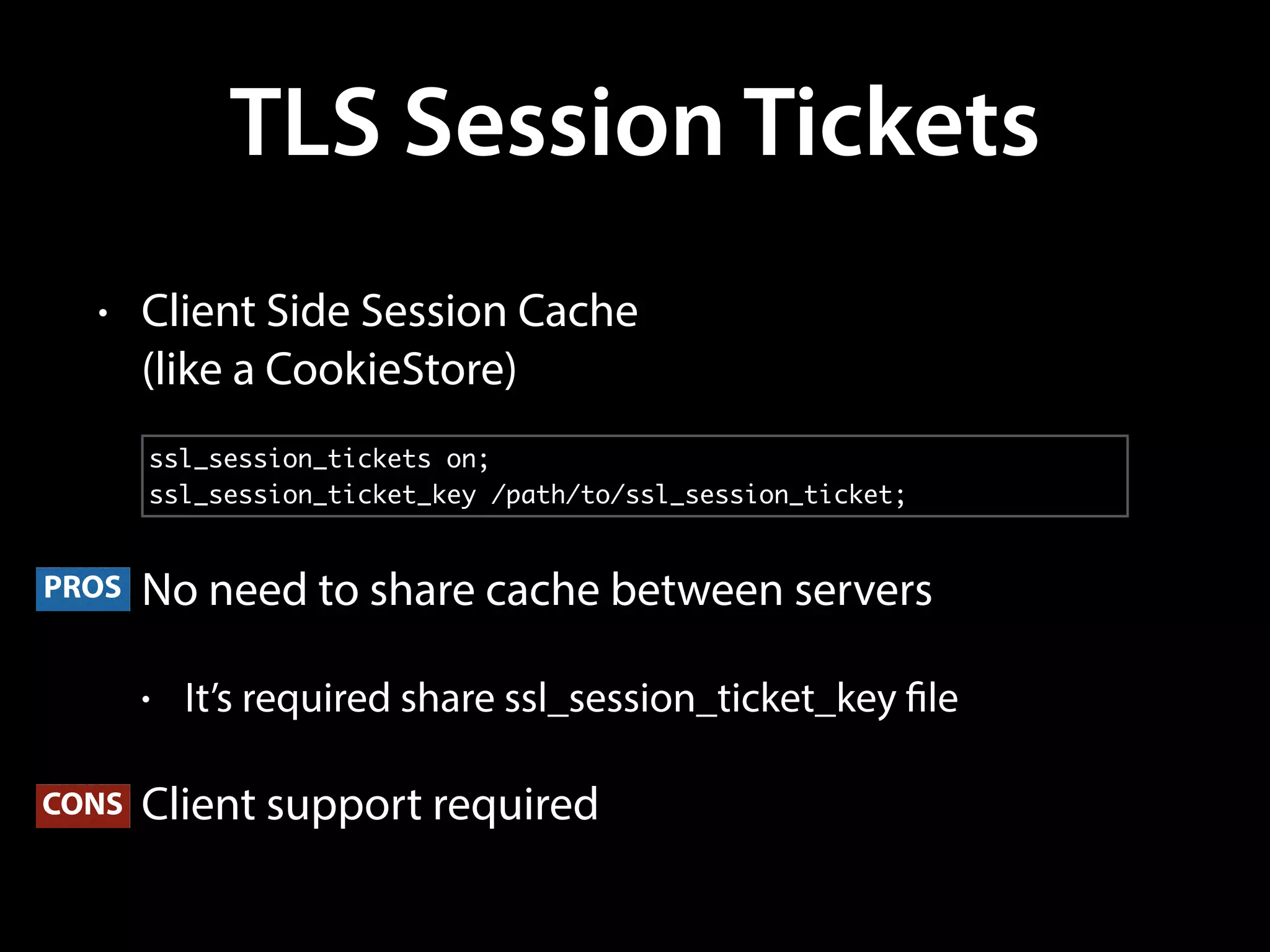
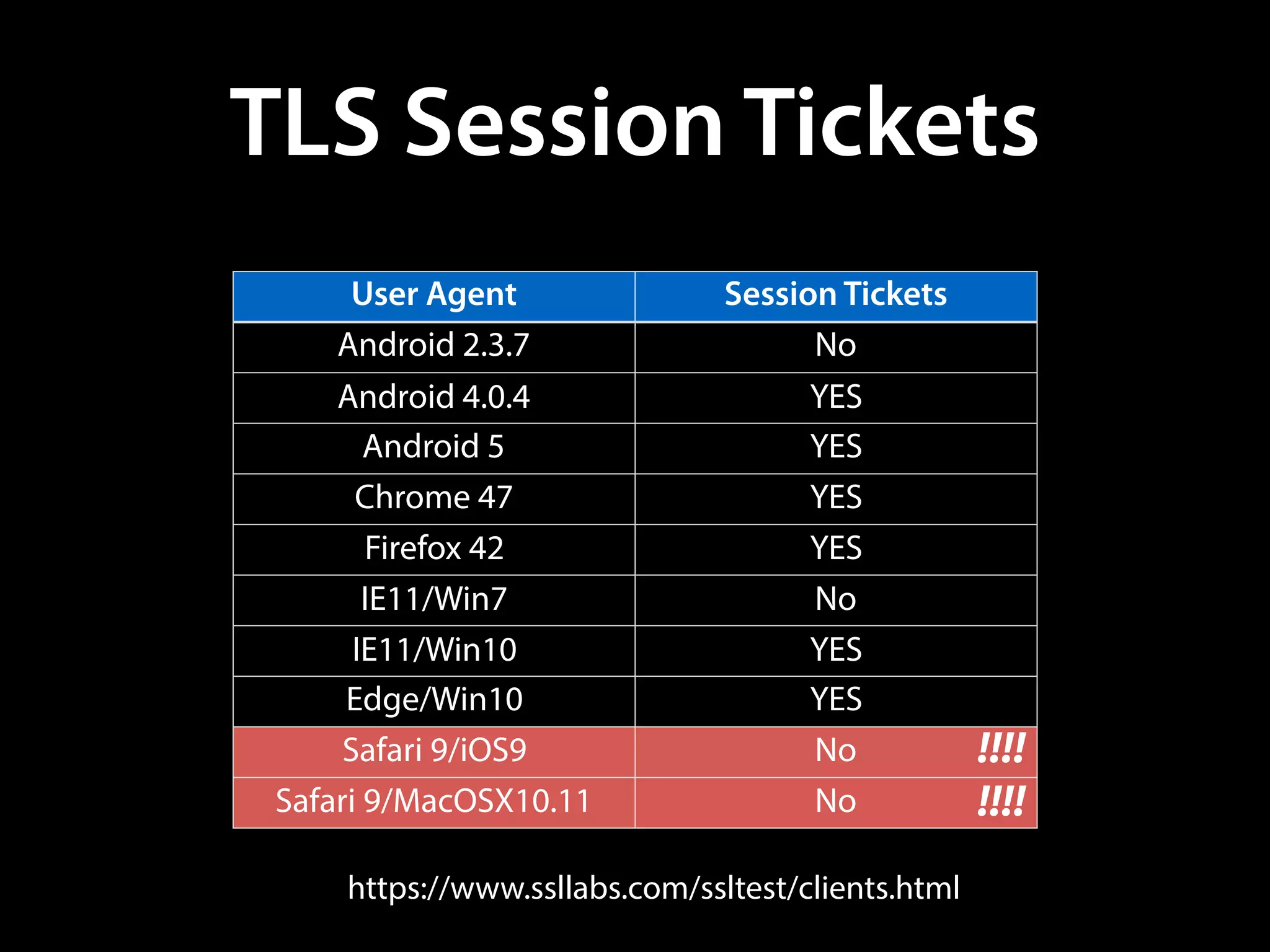
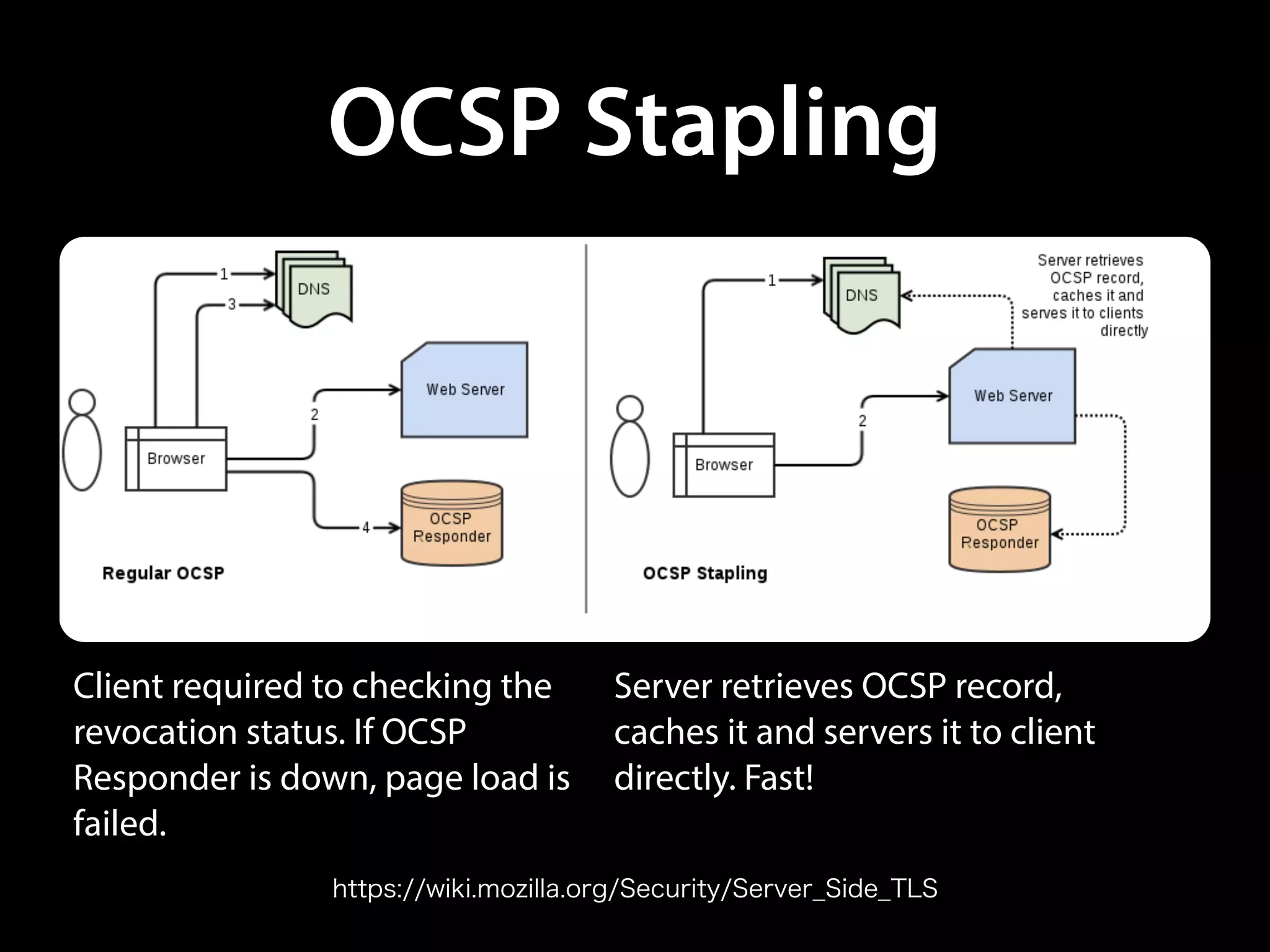
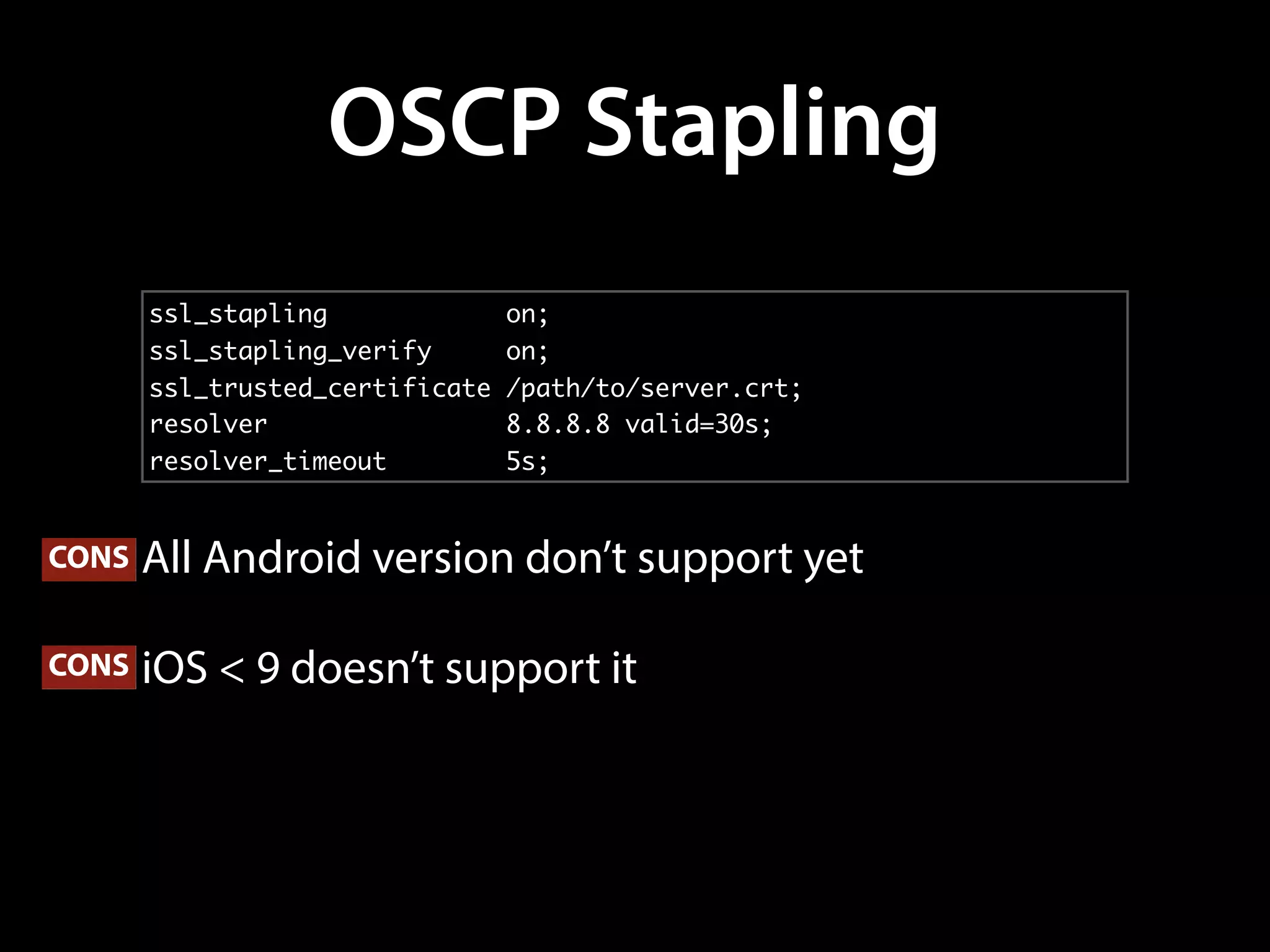
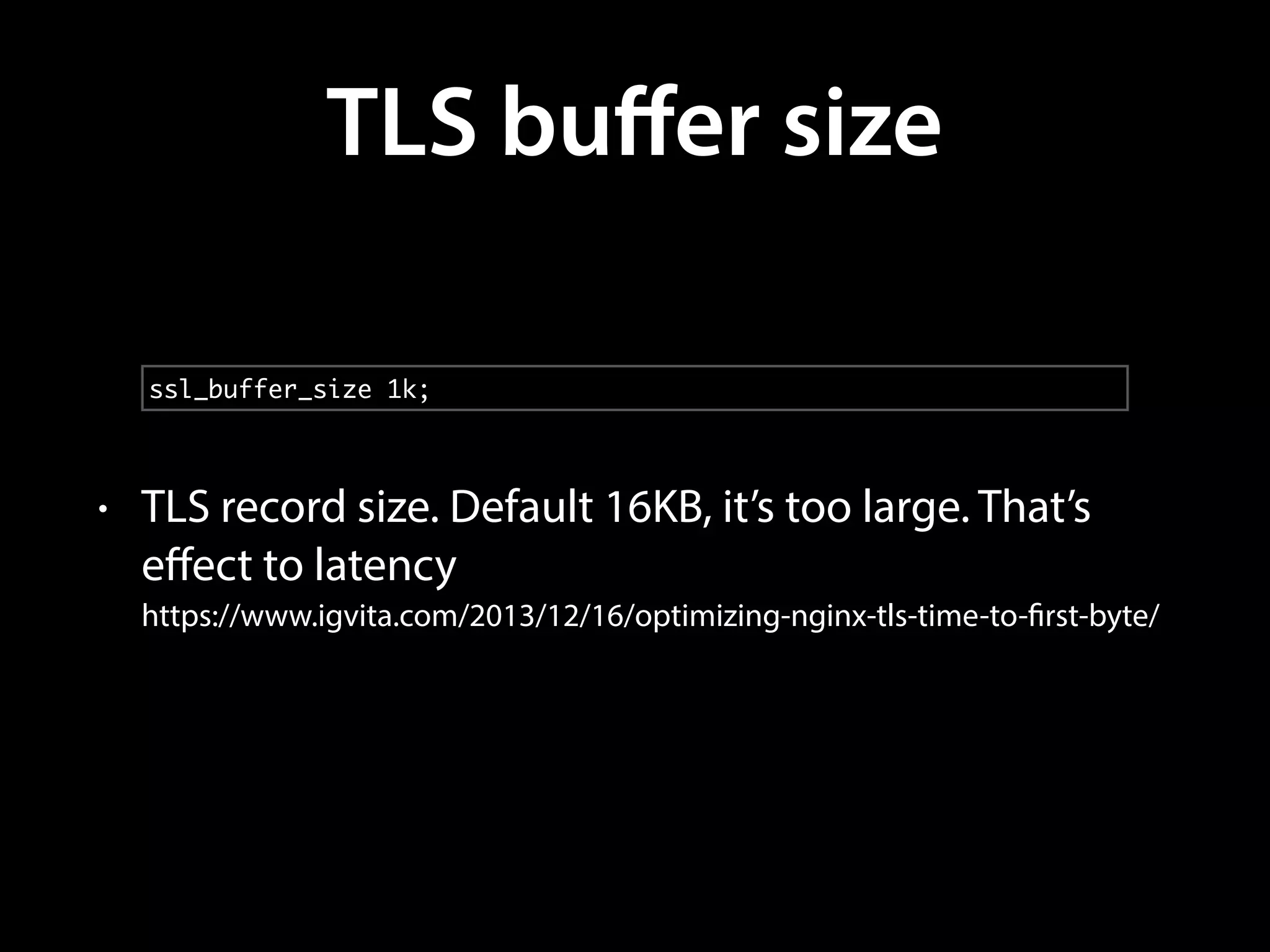
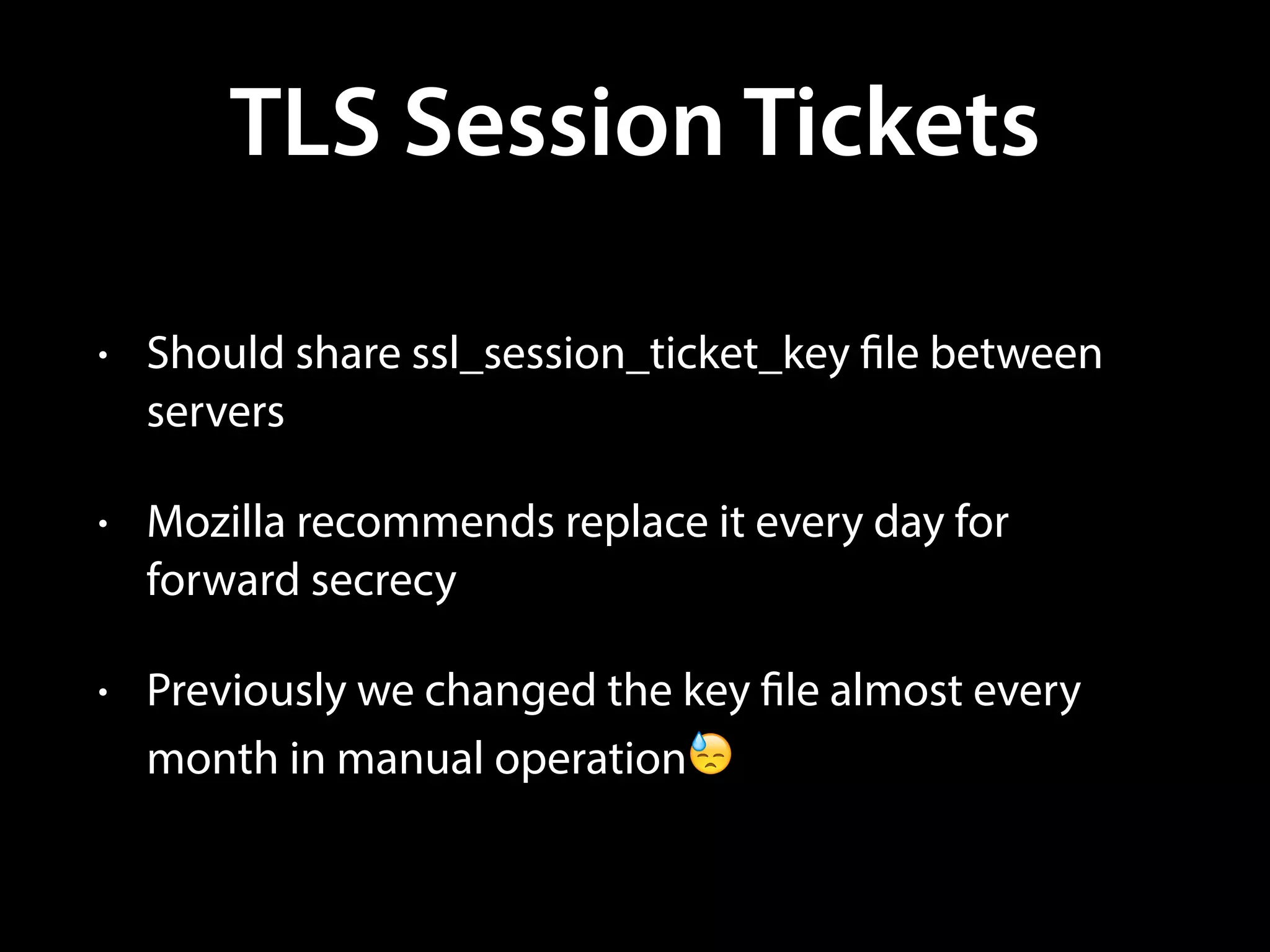
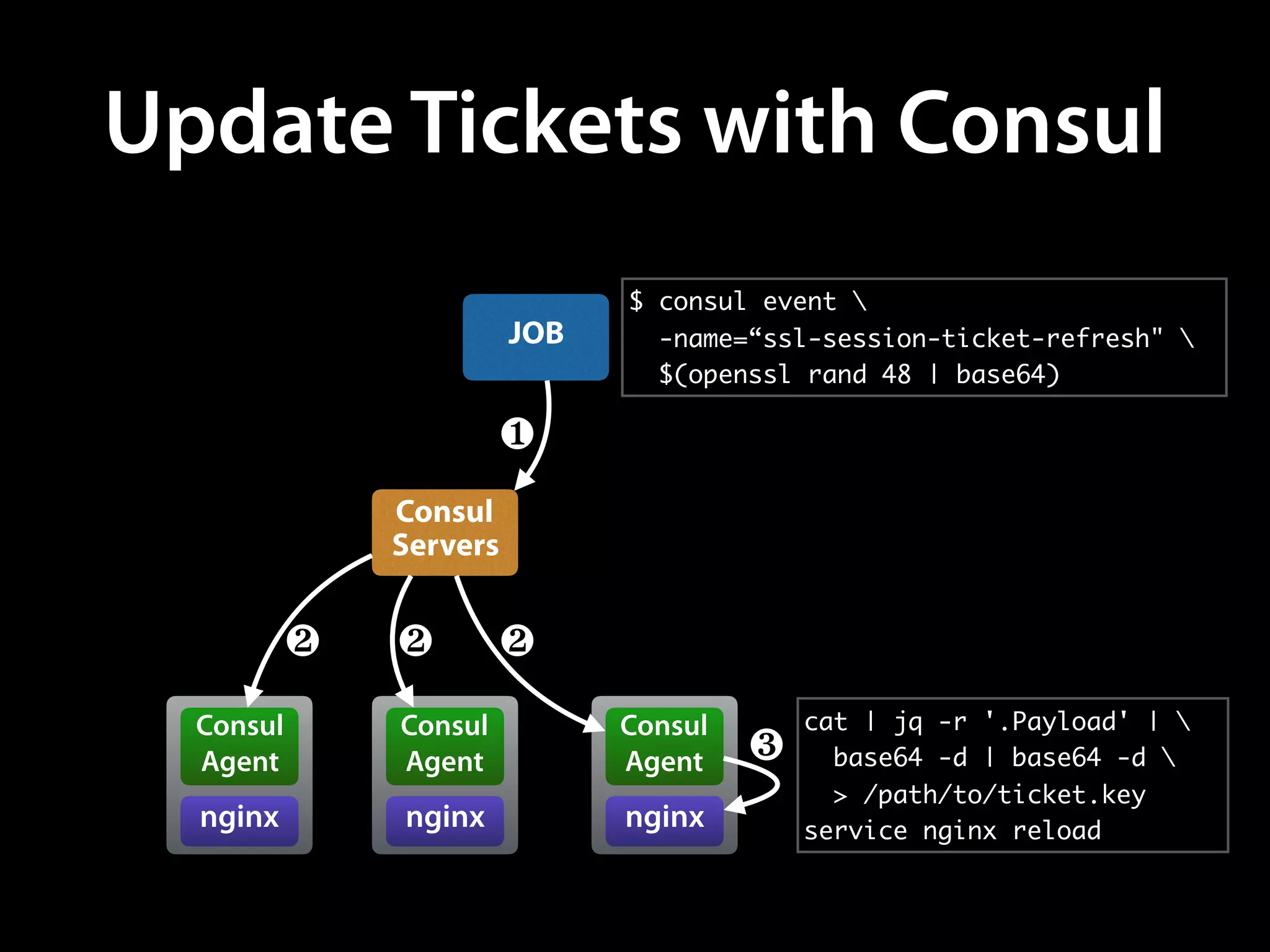
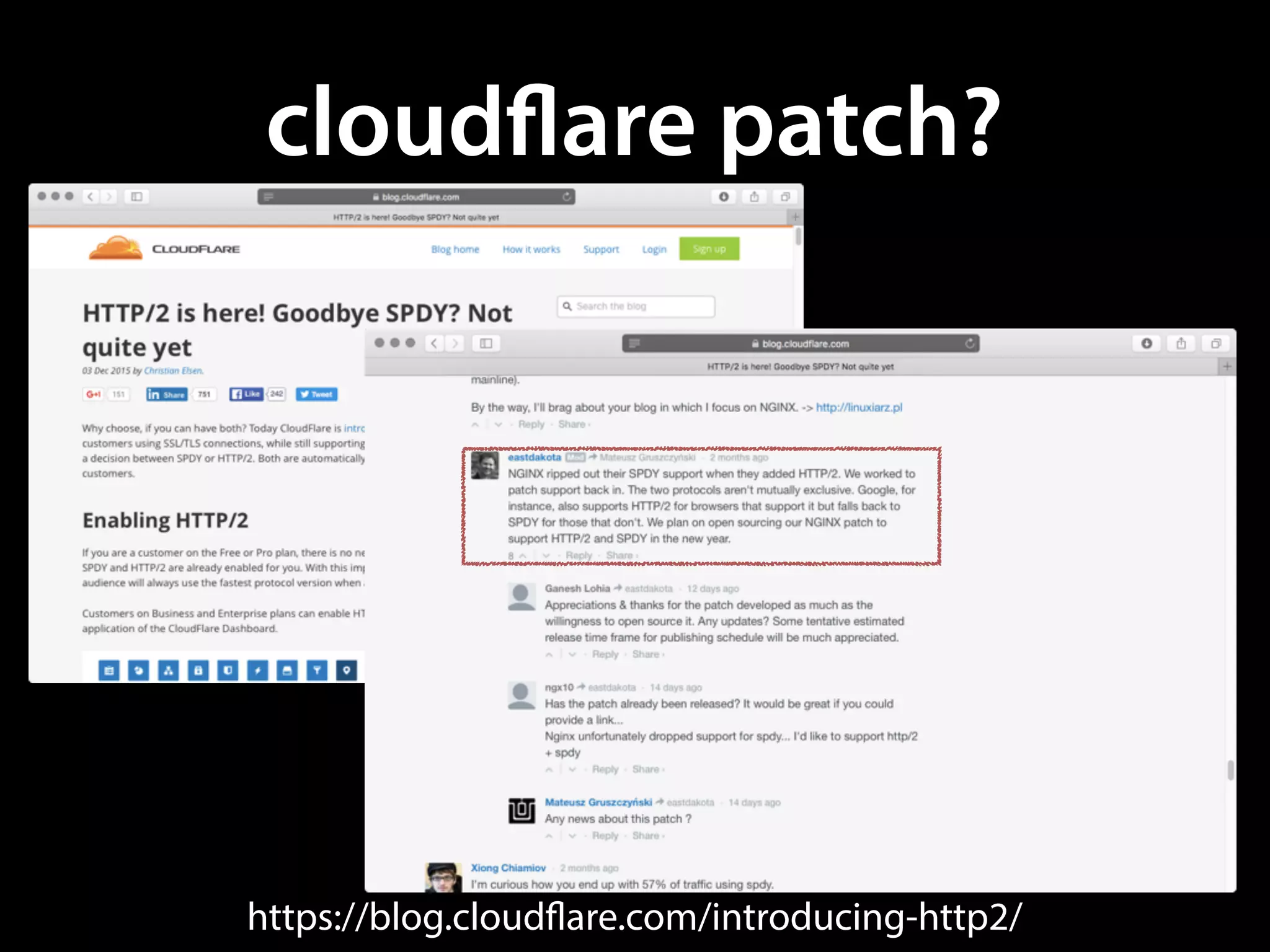
The document details an NGINX tech talk by Masahiro Nagano focused on the implementation and optimization of NGINX at Mercari, handling extensive API traffic of over 1,200,000 HTTPS requests per minute. Key topics include automatic TLS session ticket key updates, load balancing techniques using OpenResty, and security enhancements like TLS optimization and OCSP stapling. It emphasizes the need for continuous updating of NGINX and the transition from SPDY to HTTP/2 while ensuring service stability.