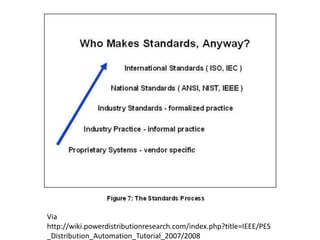
This document discusses open standards and open data. It provides background on open data initiatives in the UK from 2006 to 2012. It also discusses the definition and importance of open standards, giving examples of standards used for plug sockets, audio files and Microsoft Office documents. Open standards are defined as standards developed through an open process, published freely and able to be implemented by multiple vendors. The document advocates for open standards and data to ensure interoperability between systems.






![“Standard - codified knowledge providing
specifications for interfaces between software, systems
or the documents and data that pass between them.”
[Open Standards Consultation – Glossary]
“*O]penstandards must allow all possible competitors
to operate on a basis of equal access to the ability to
implement the standard” [An Economic Basis for Open
Standards, RA Ghosh]](https://image.slidesharecdn.com/openstandardsandopendata-120308102633-phpapp01/85/Open-standards-and-open-data-40-320.jpg)
![“ For the purpose of UK Government software
interoperability, data and document formats, the definition of
open standards is those standards which fulfil the
following[5] criteria:](https://image.slidesharecdn.com/openstandardsandopendata-120308102633-phpapp01/85/Open-standards-and-open-data-41-320.jpg)