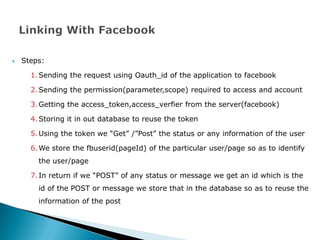
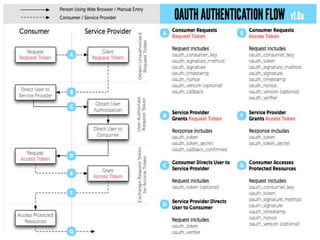
The document discusses the steps for implementing OAuth authentication with Facebook. It involves:
1. Sending an OAuth request to Facebook with the application ID.
2. Requesting required permissions/scopes to access the user's account.
3. Receiving an access token and access verifier from Facebook.
4. Storing the token in a database to reuse it for making API calls to get/post user status updates or other information.