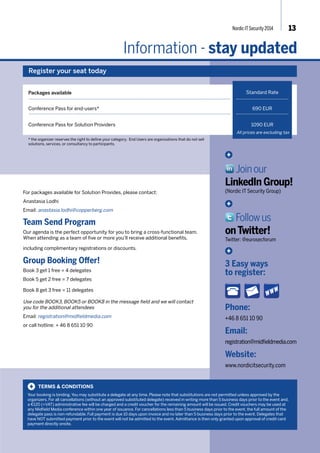
This document provides information about the Nordic IT Security 2014 conference that will take place on November 5th, 2014 in Stockholm, Sweden. The one-day conference will focus on key topics related to IT security, such as building security frameworks, automating compliance processes, and addressing security issues related to cloud environments, mobile devices, and the Internet of Things. It will include sessions, demonstrations, roundtable discussions, and a keynote on securing and protecting user information online. Over 300 security professionals from the Nordic region are expected to attend to learn and network.