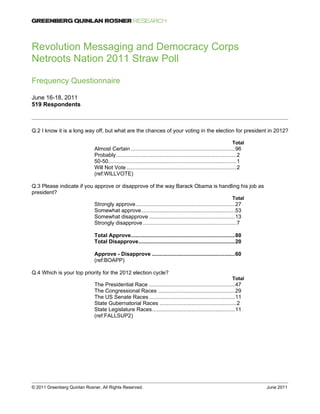
This document summarizes the results of a survey conducted at Netroots Nation 2011 with 519 respondents. It shows that 96% of respondents said they would "almost certainly" vote in the 2012 presidential election. 80% of respondents approved of the way Barack Obama is handling his job as president. The top priority for President Obama according to respondents was job growth at 66%. Respondents had very warm feelings toward Barack Obama, Netroots Nation, Rachel Maddow and labor unions. A plurality of respondents said they would most like to see Sarah Palin as the Republican presidential nominee in 2012.