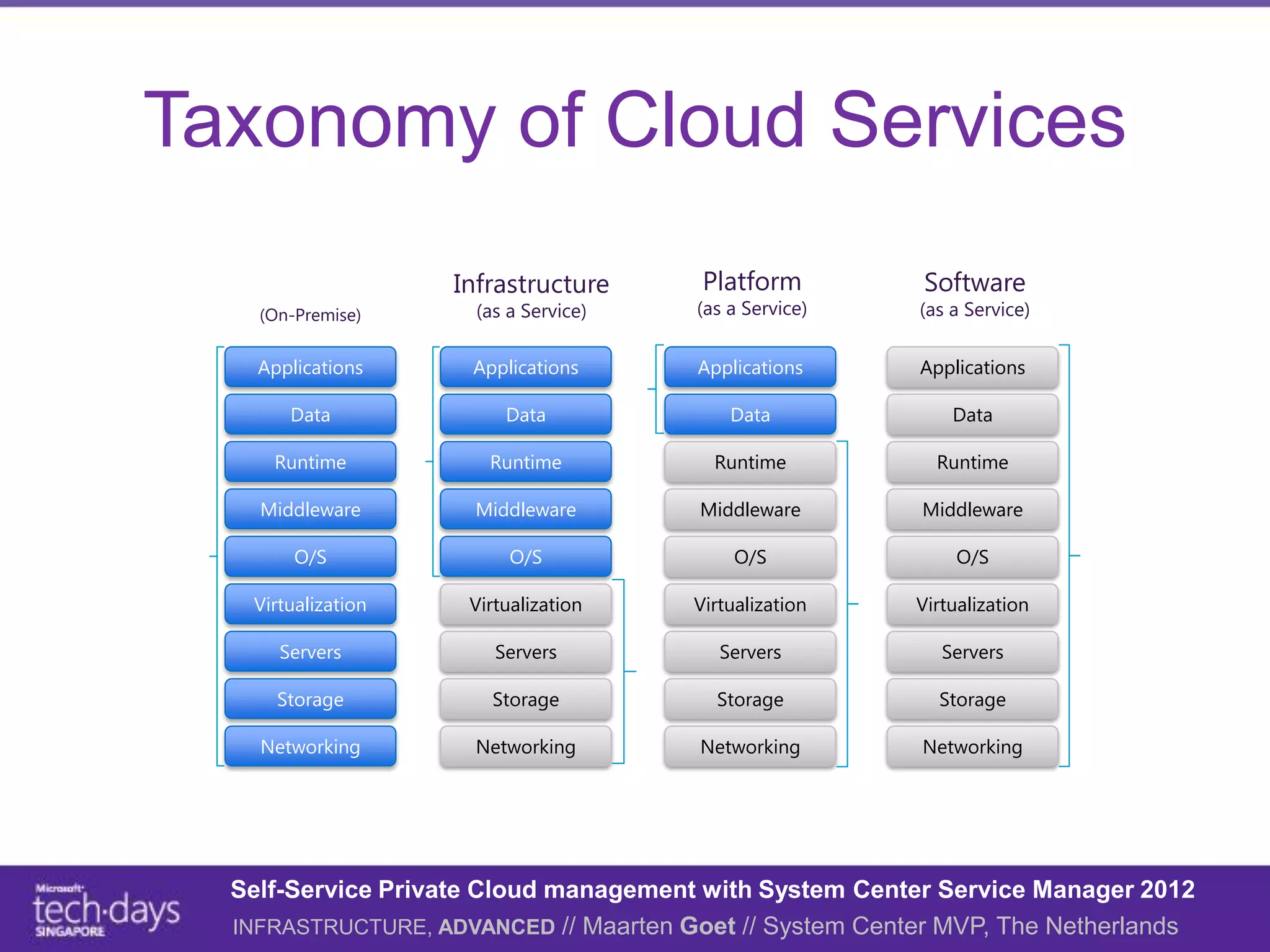
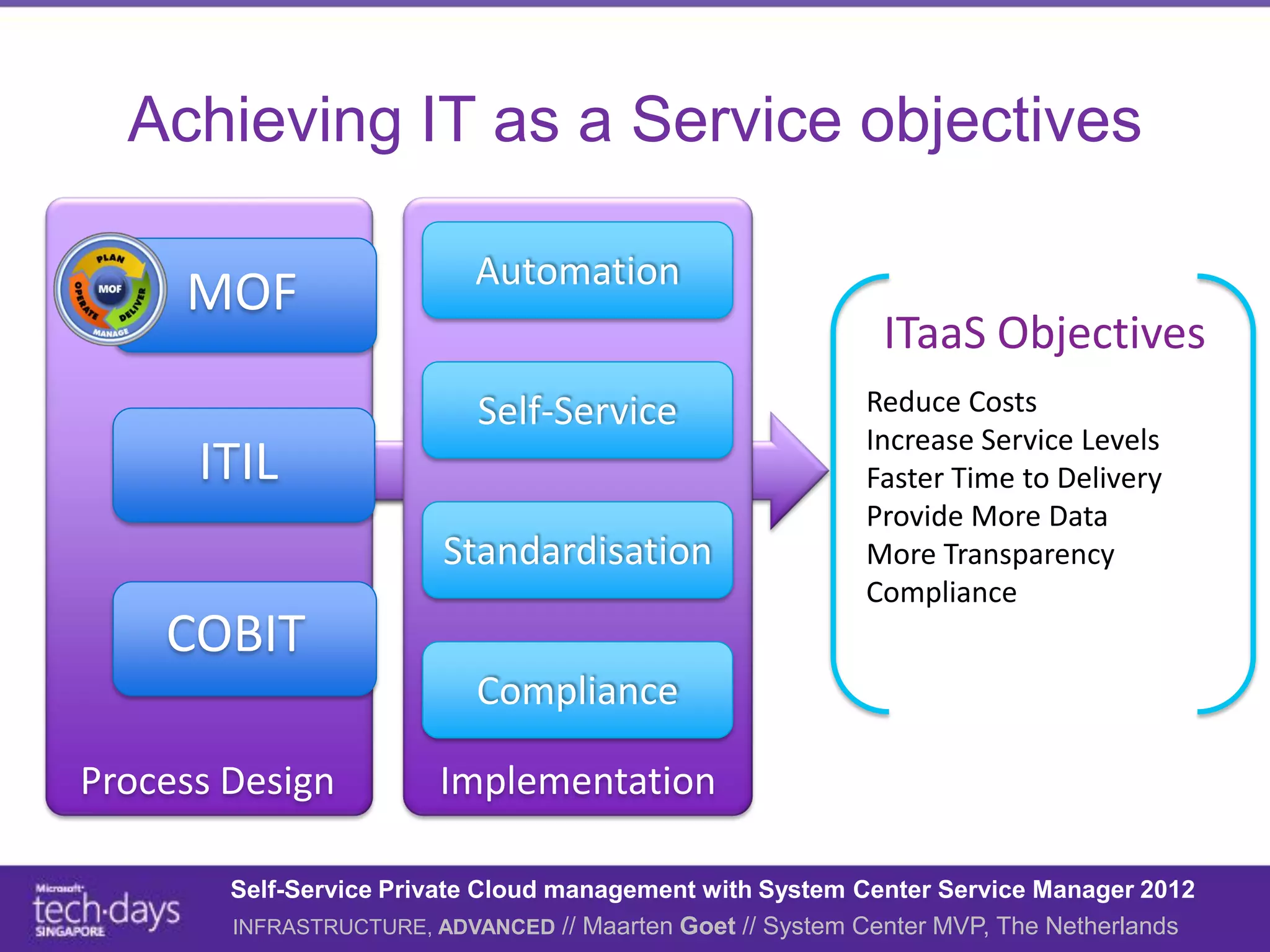
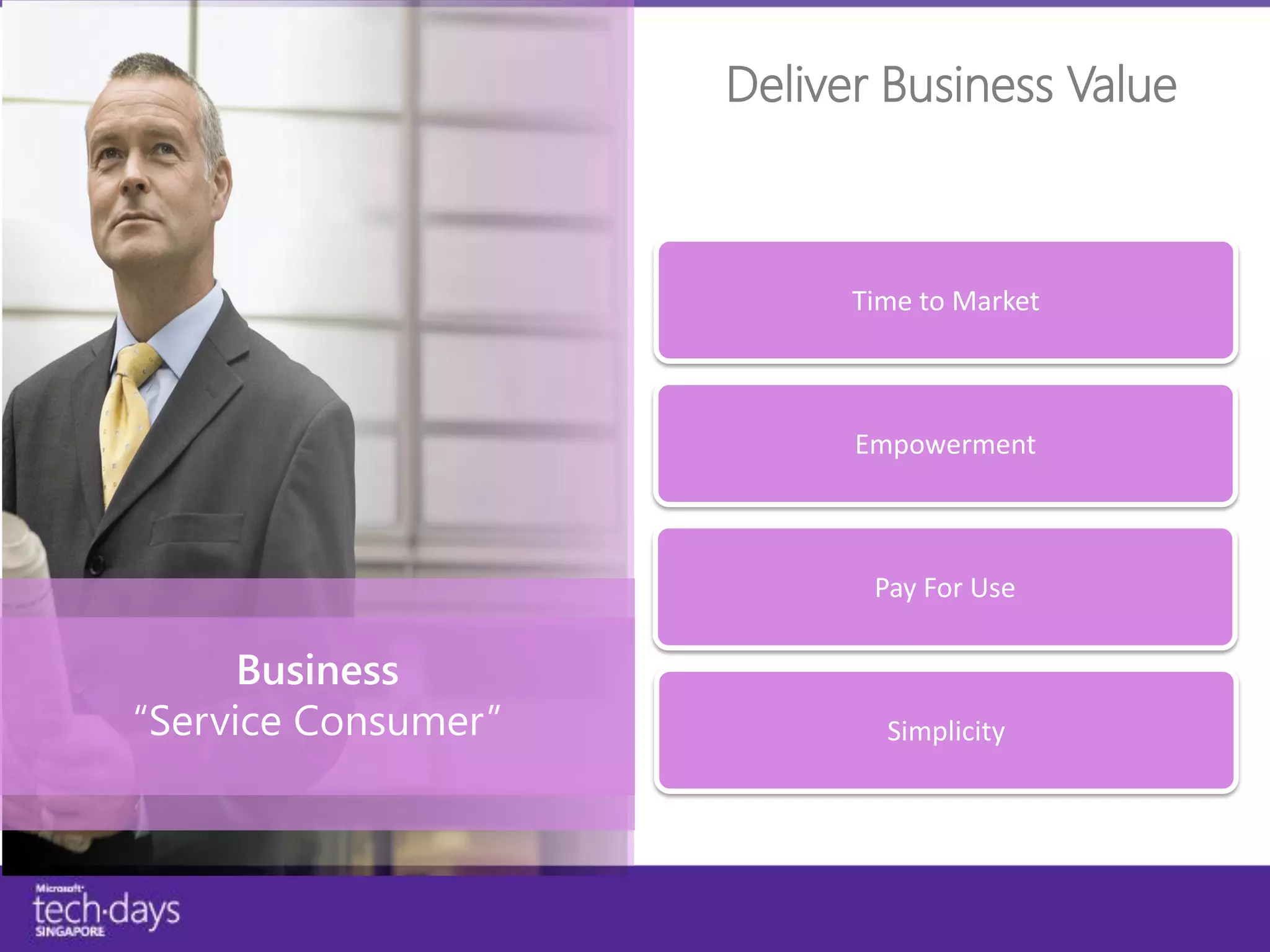
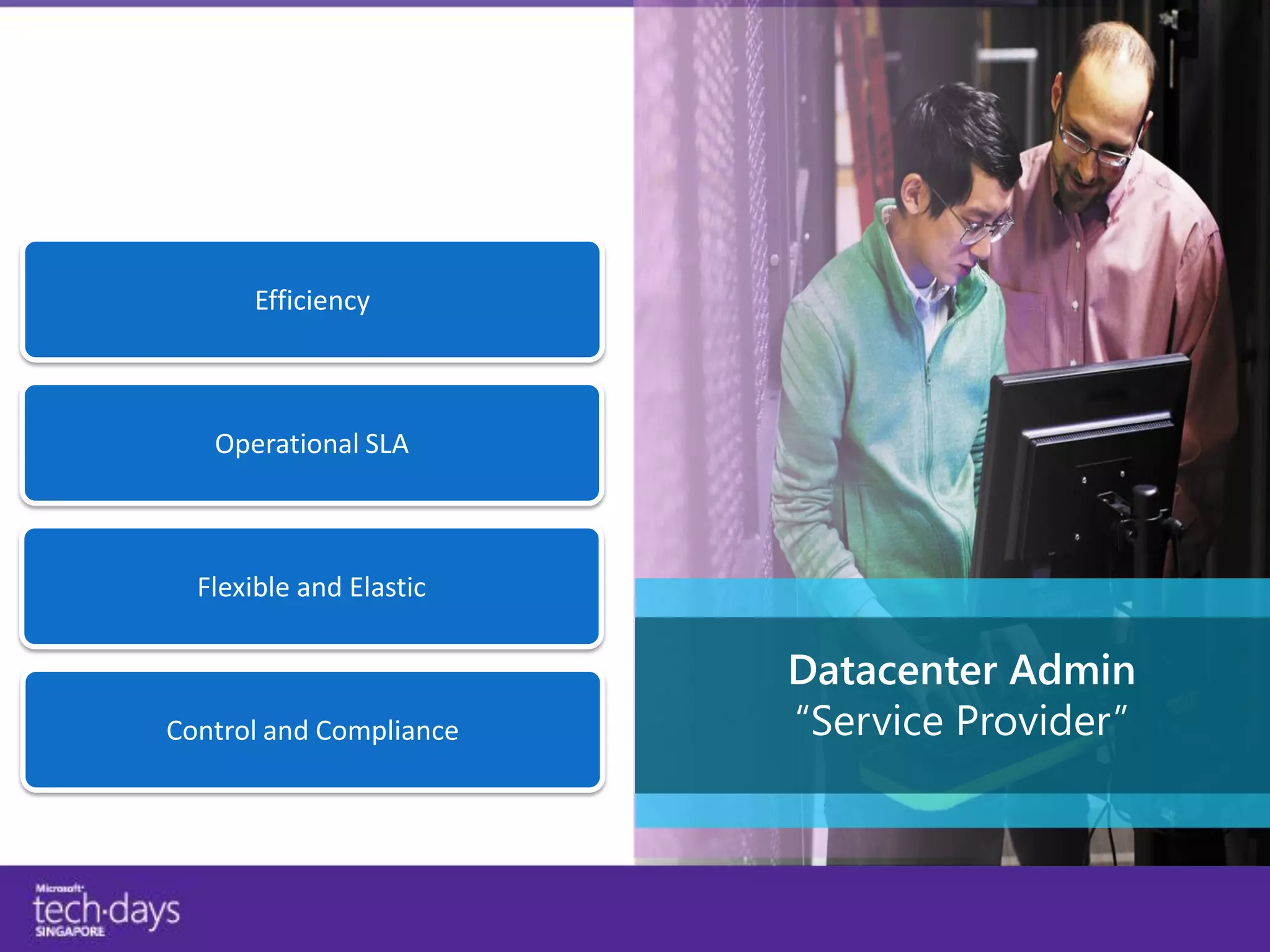
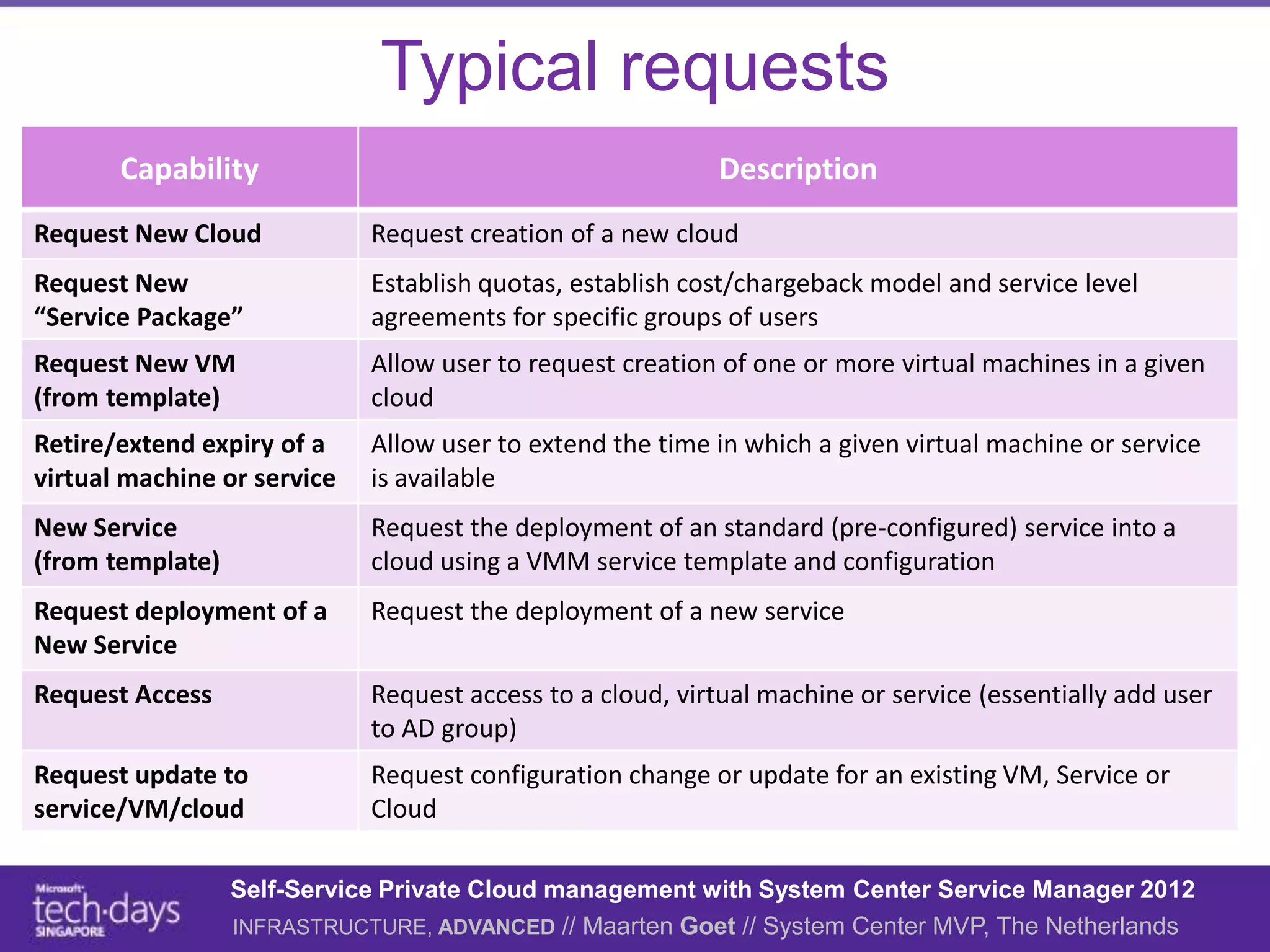
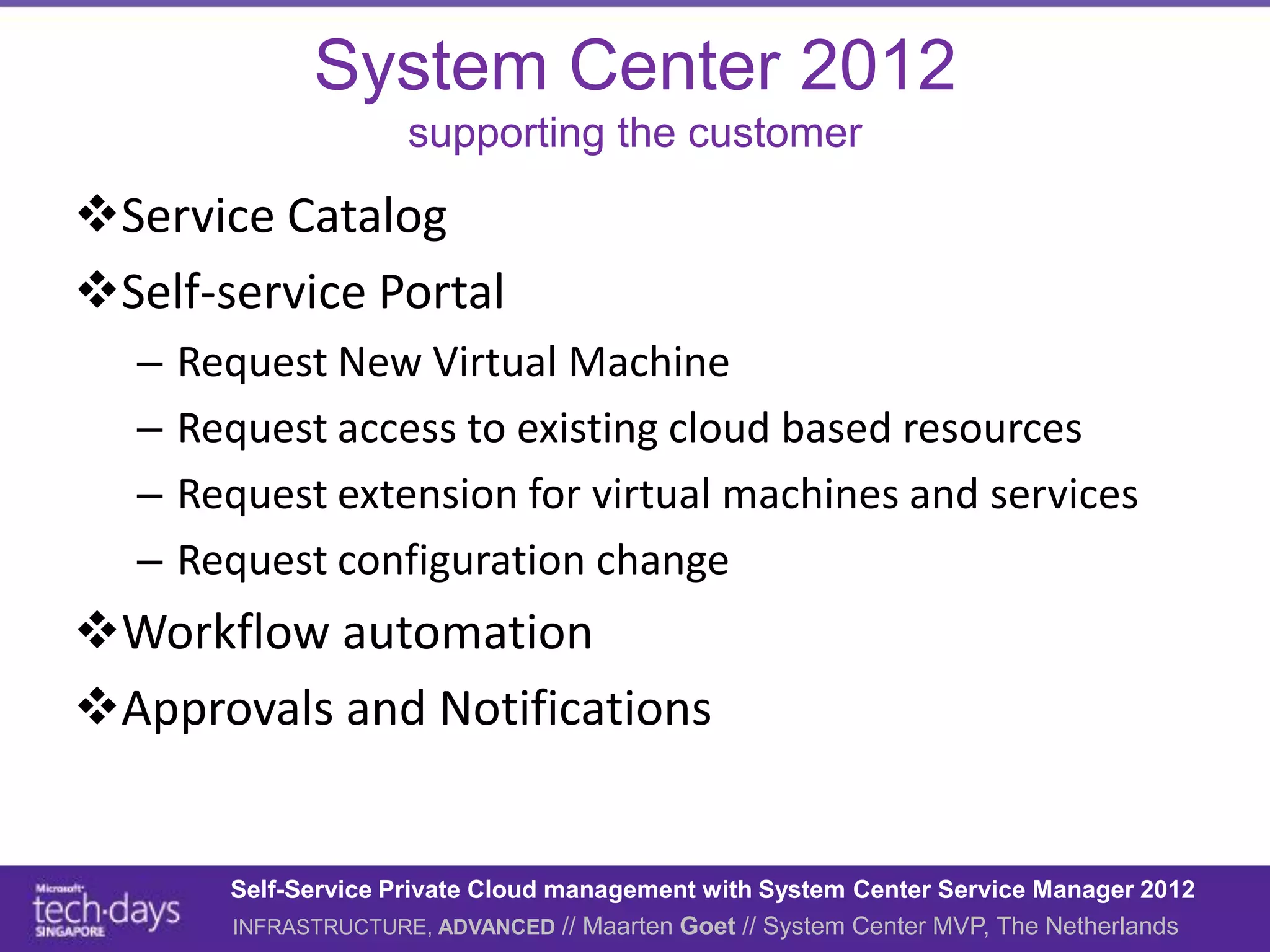
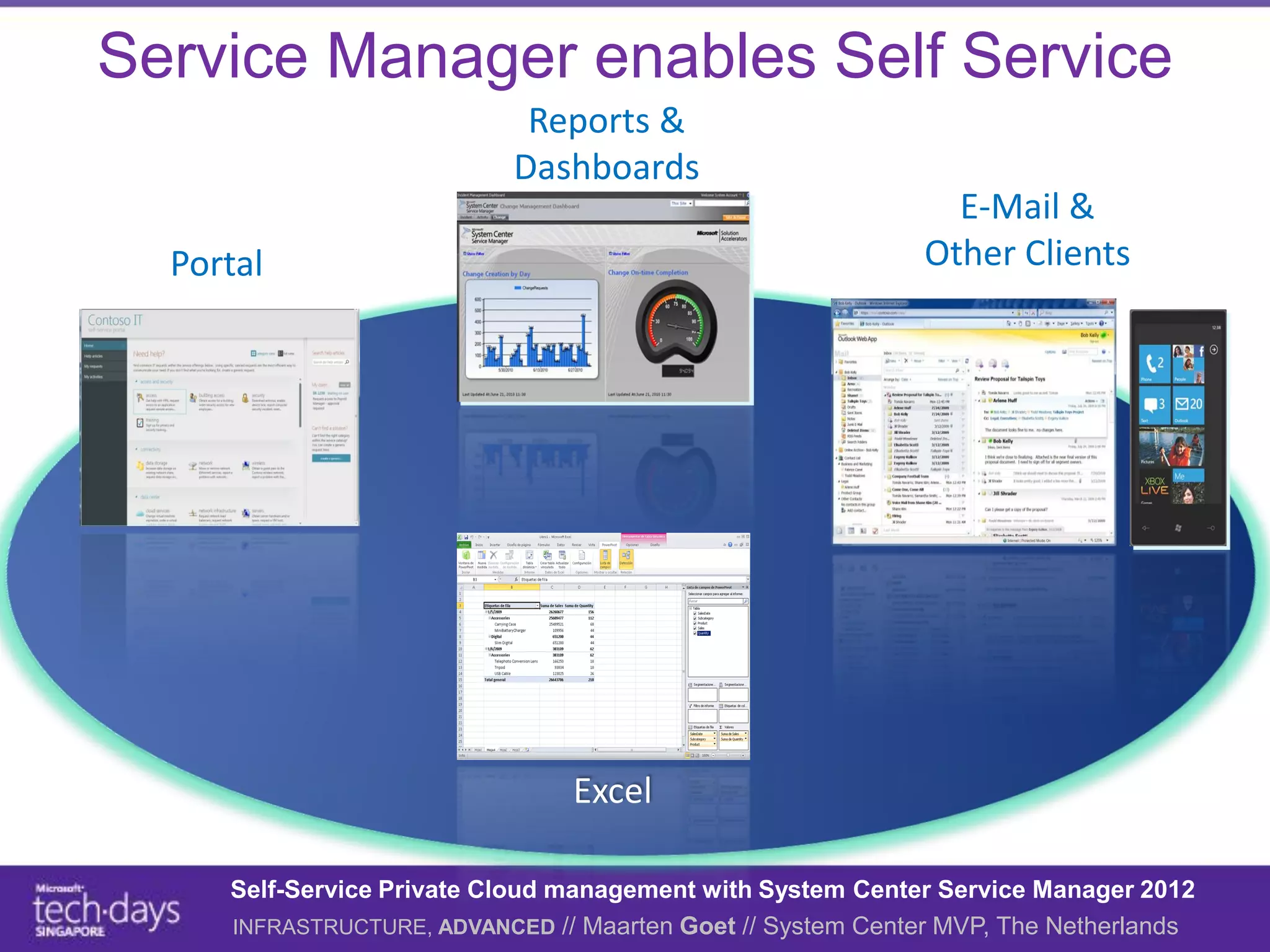
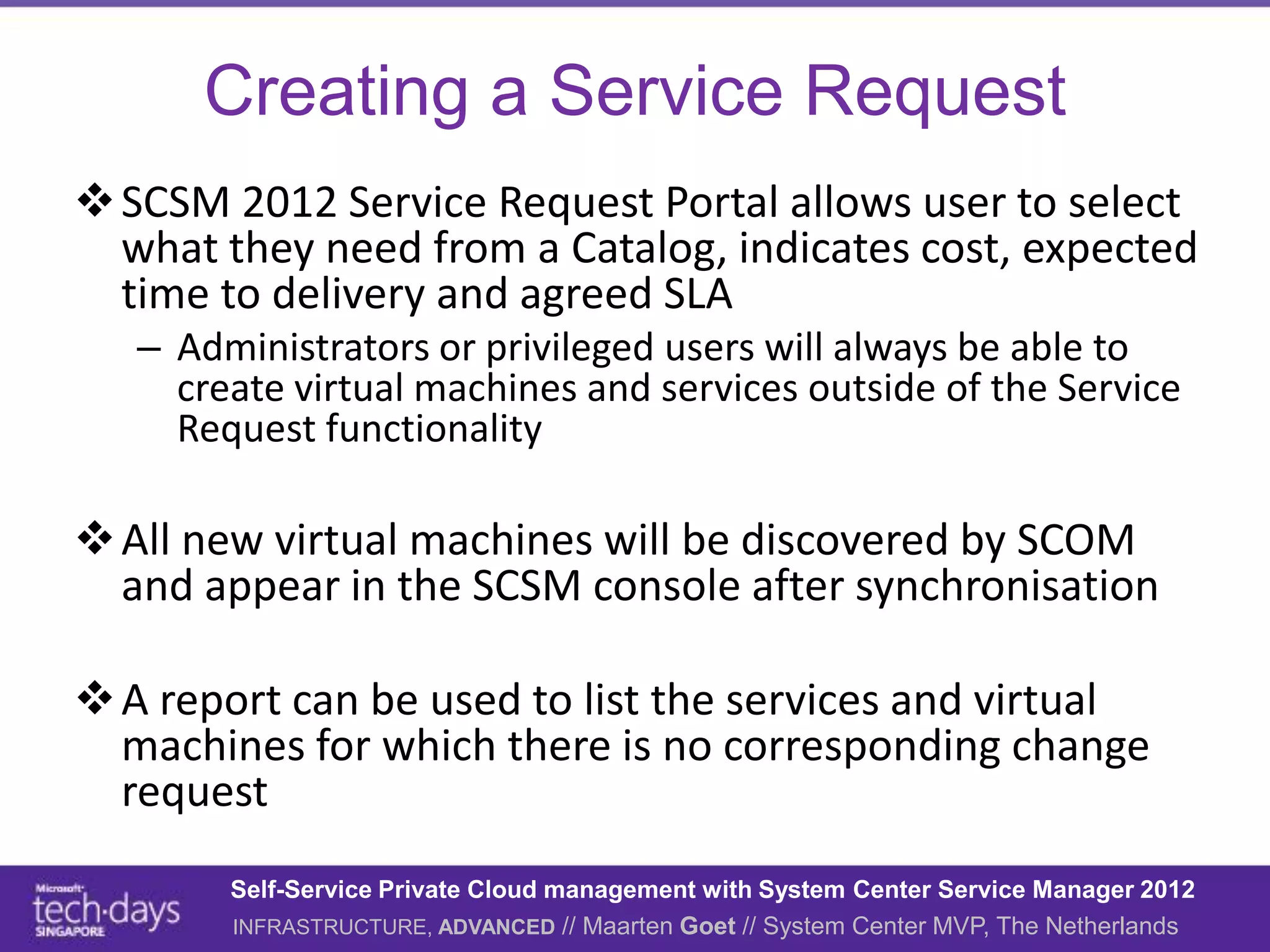
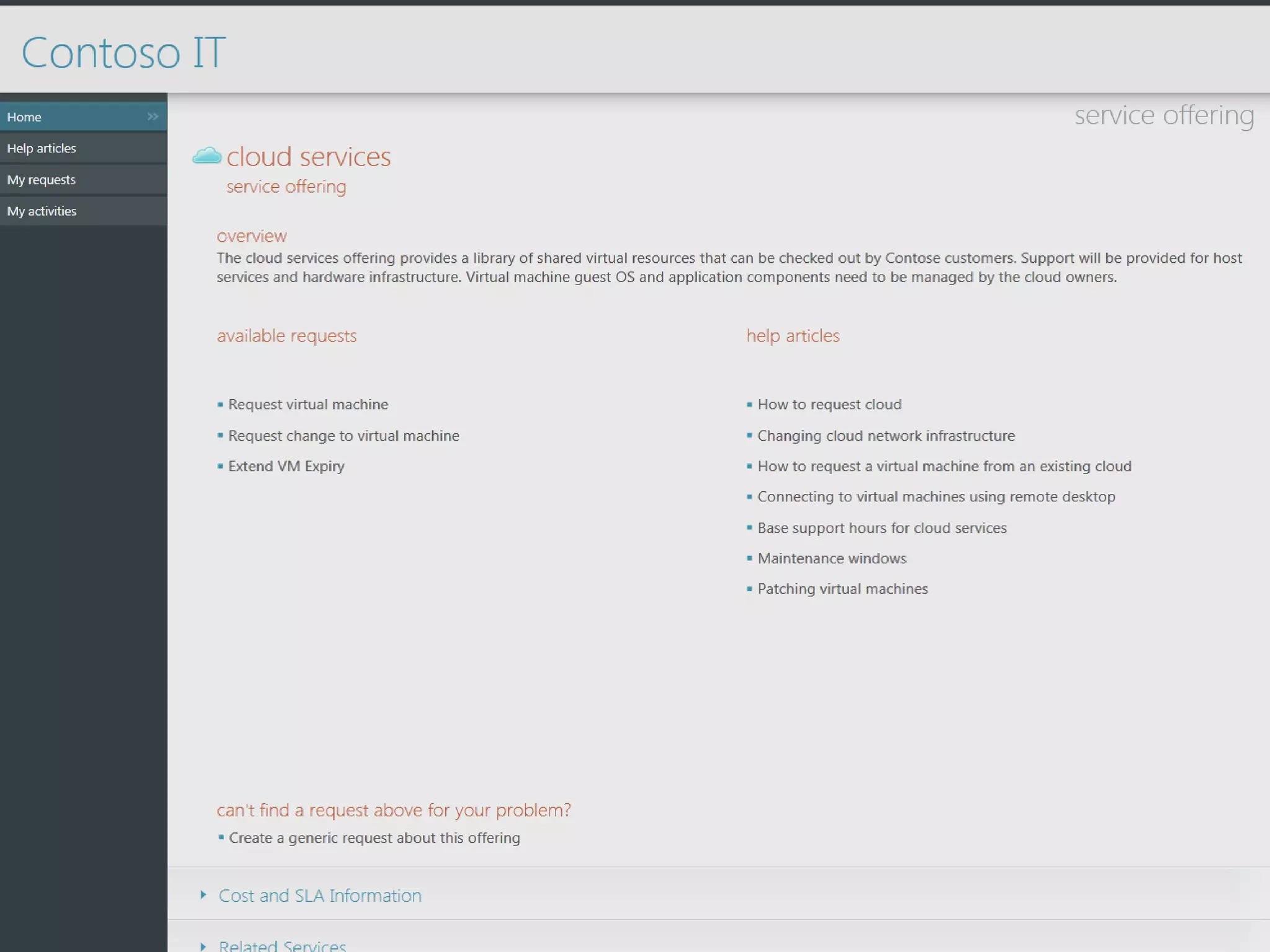
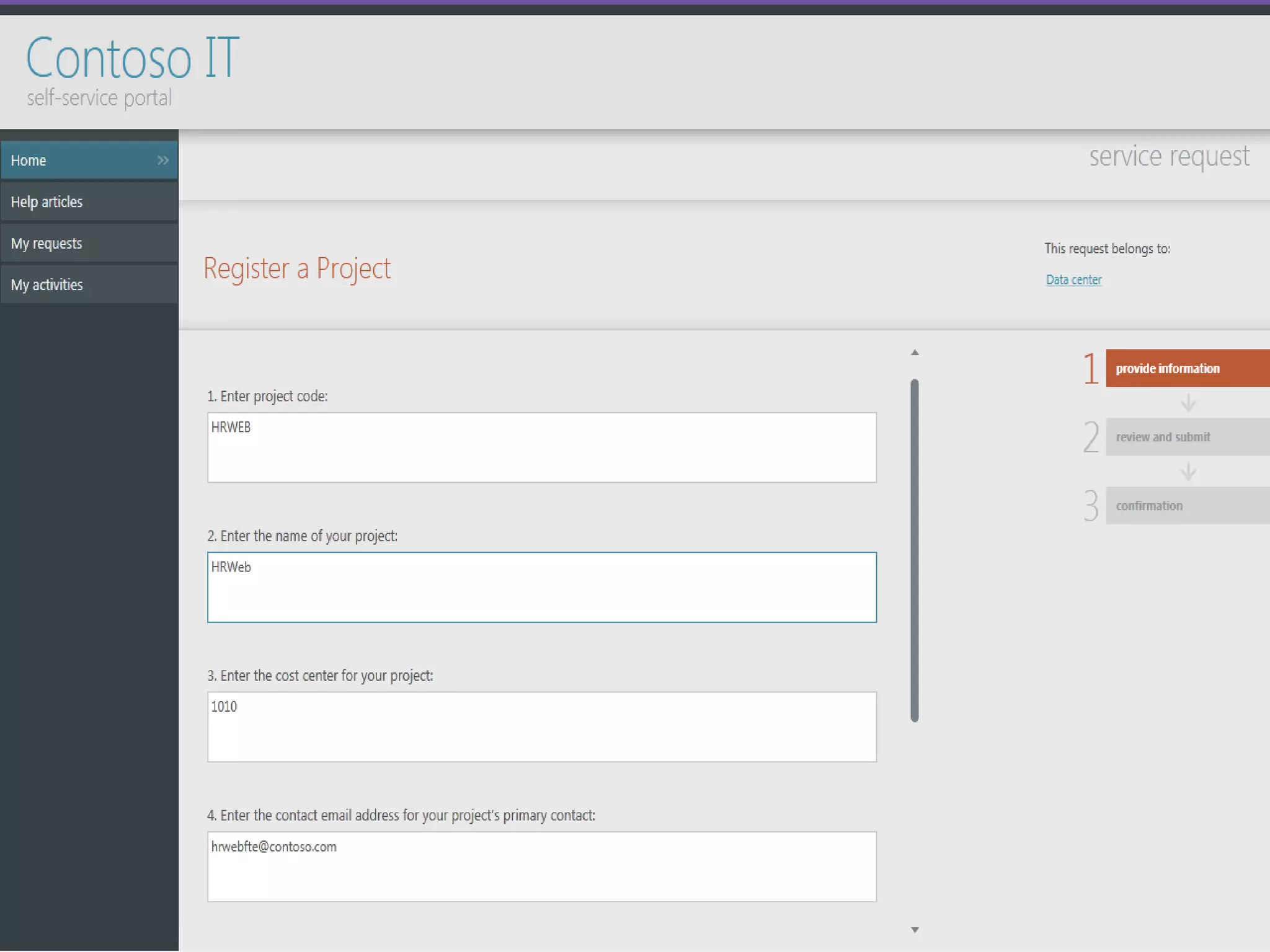
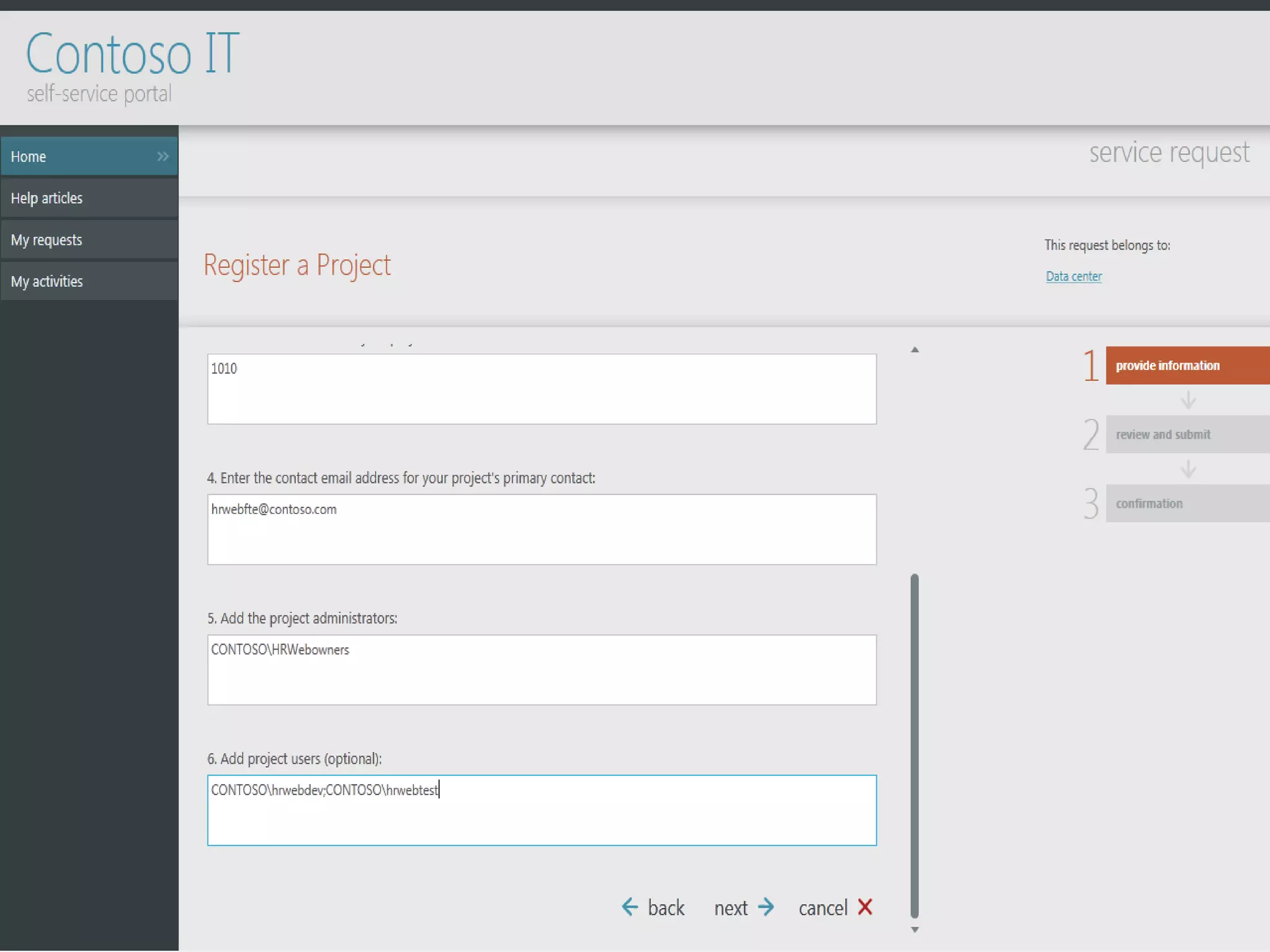
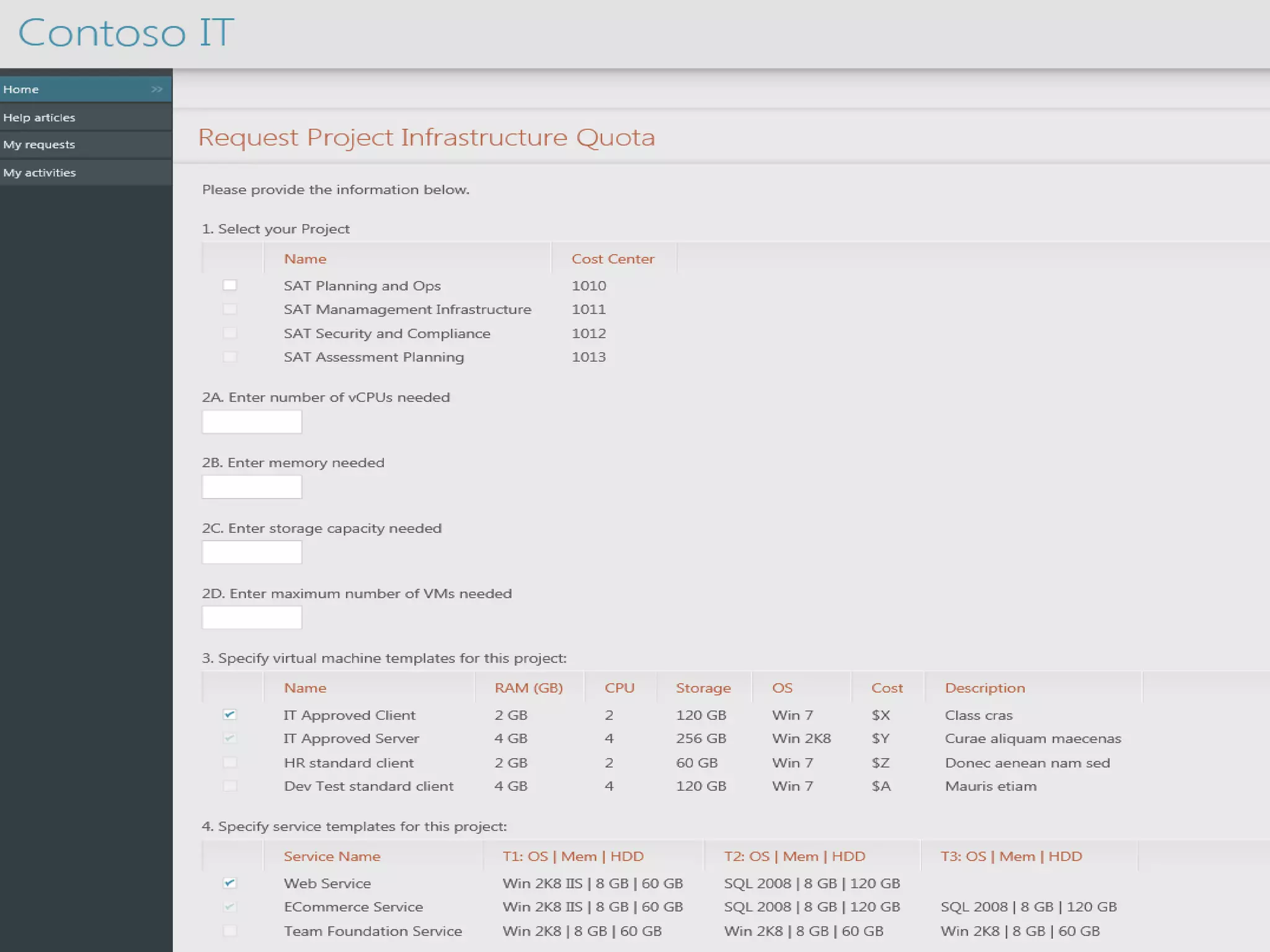
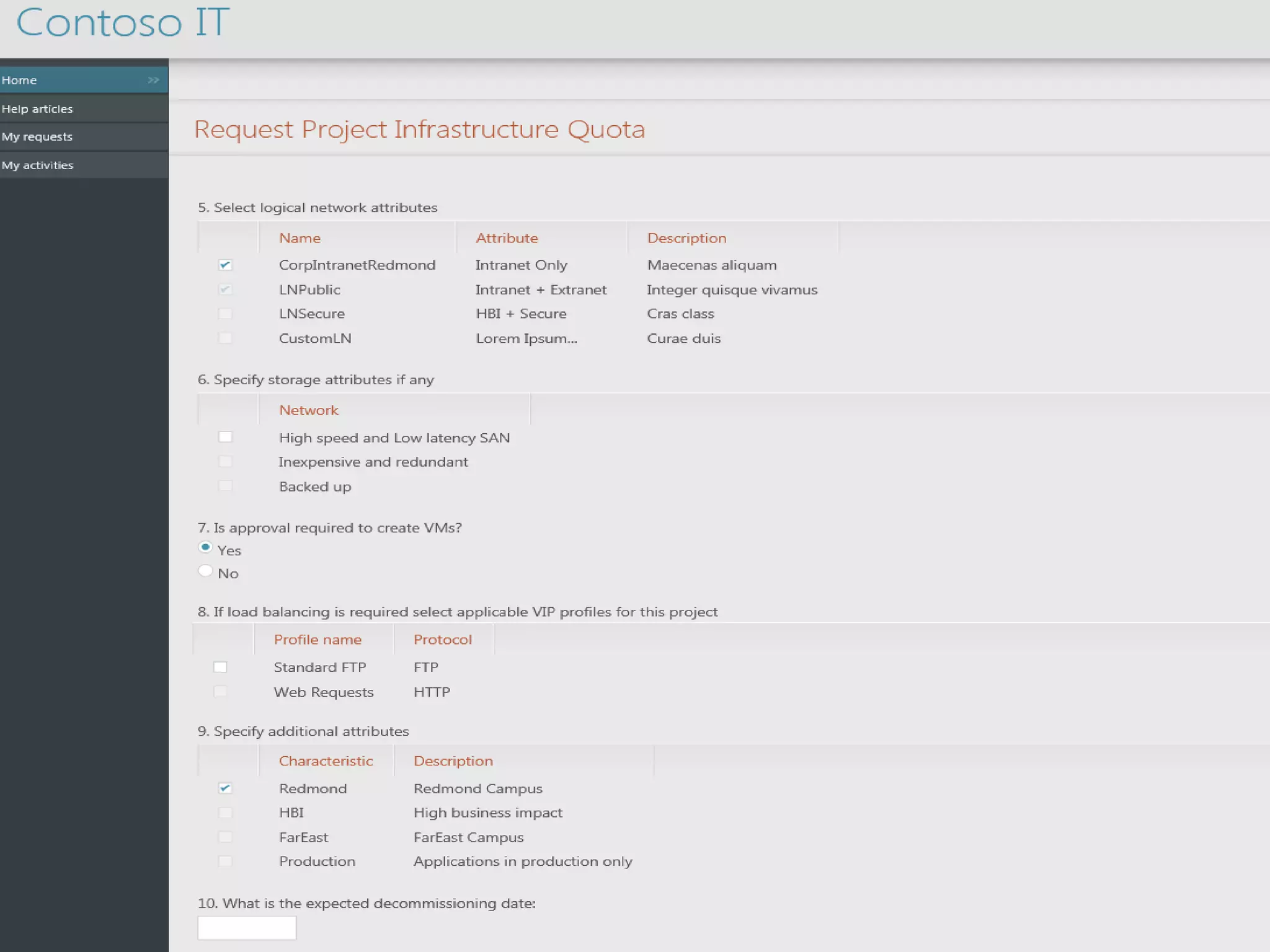
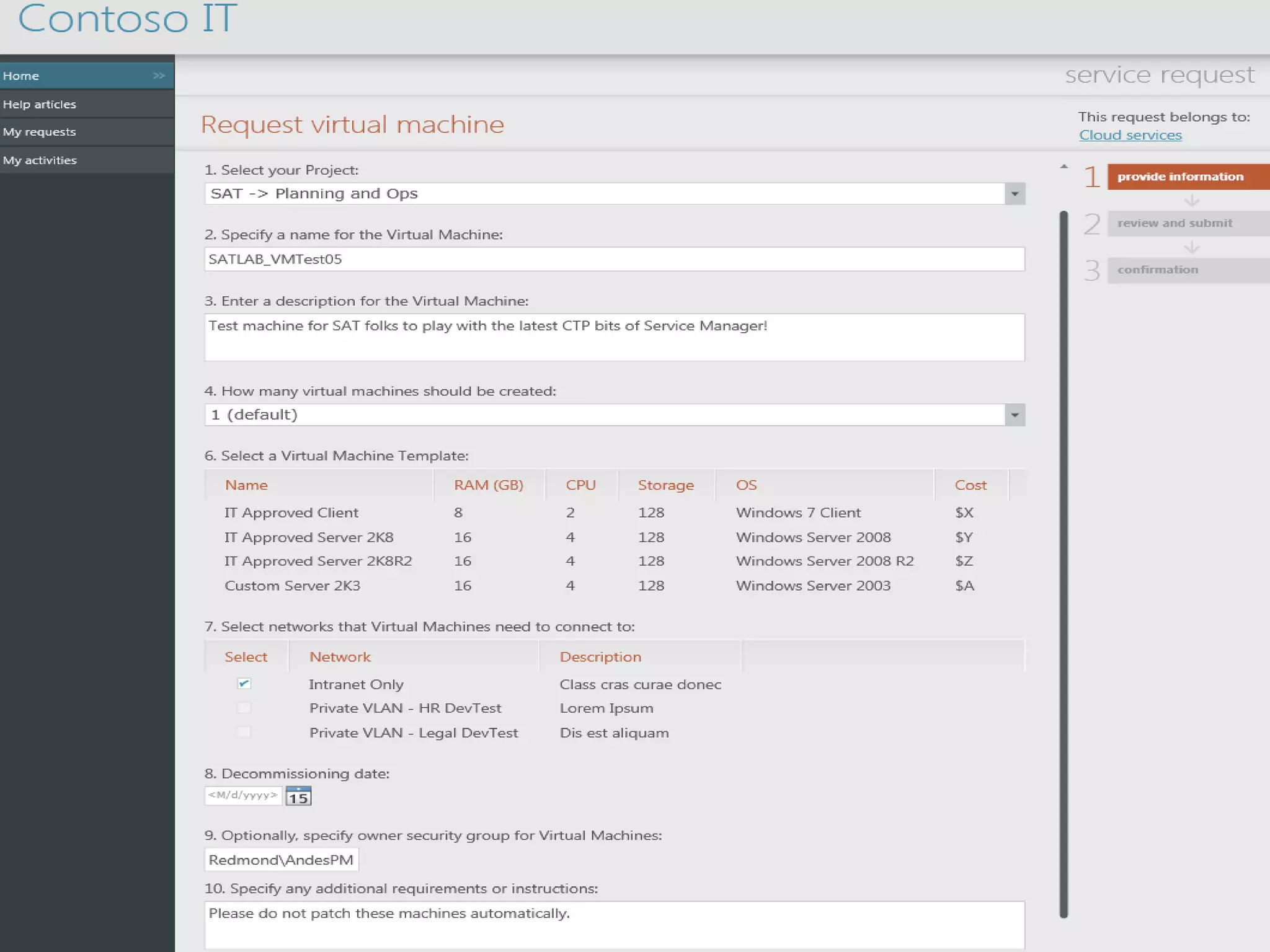
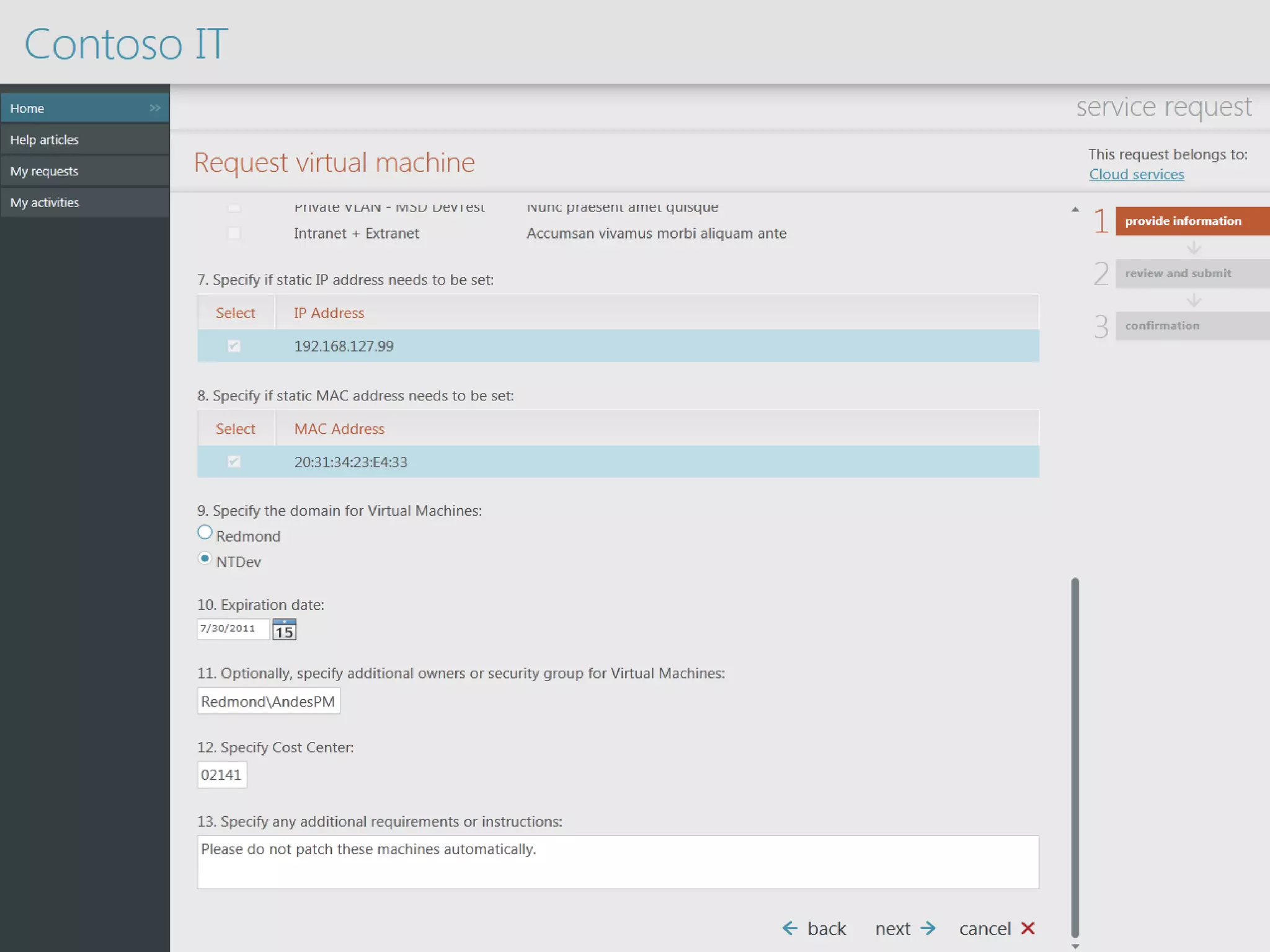
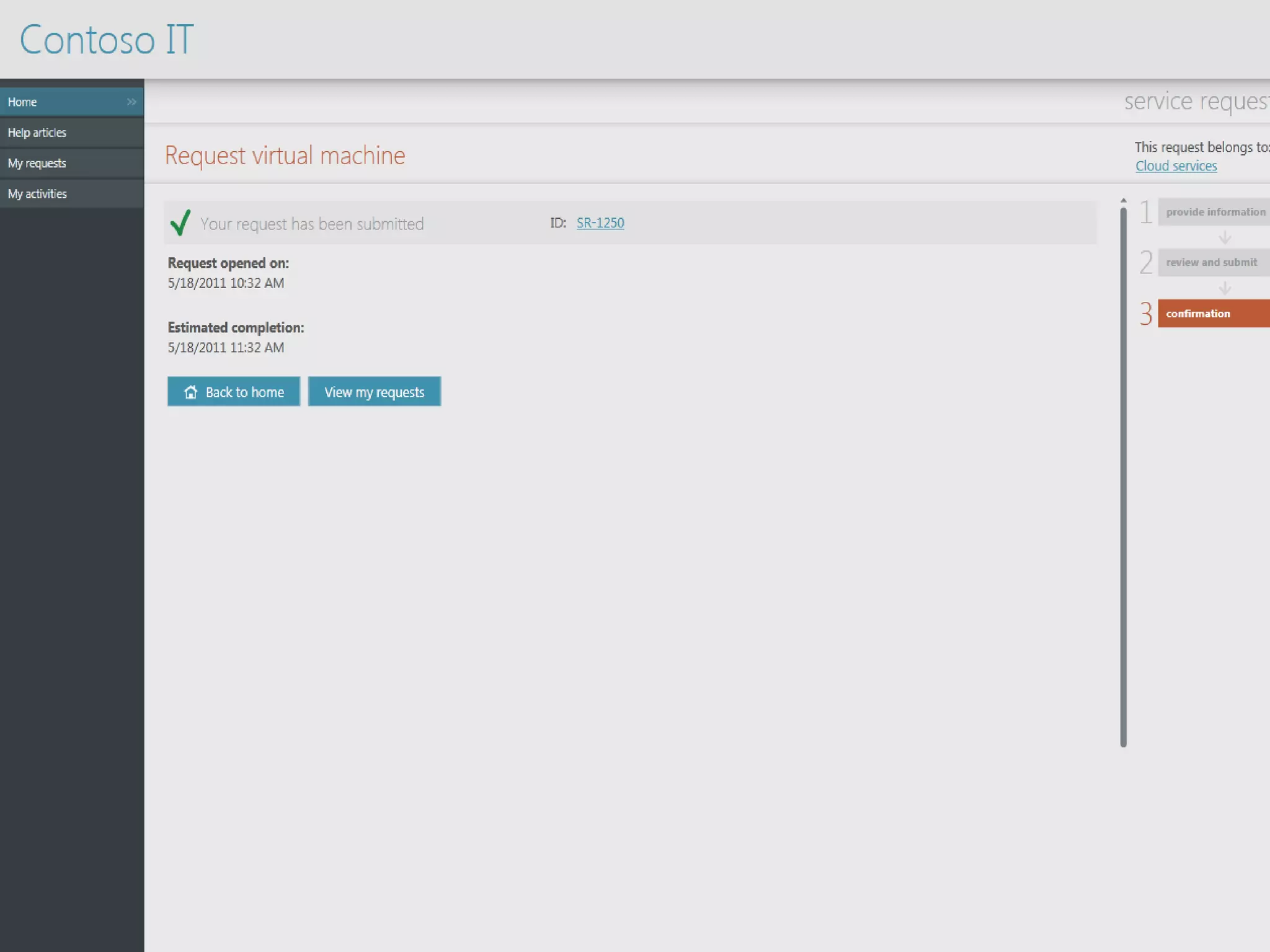
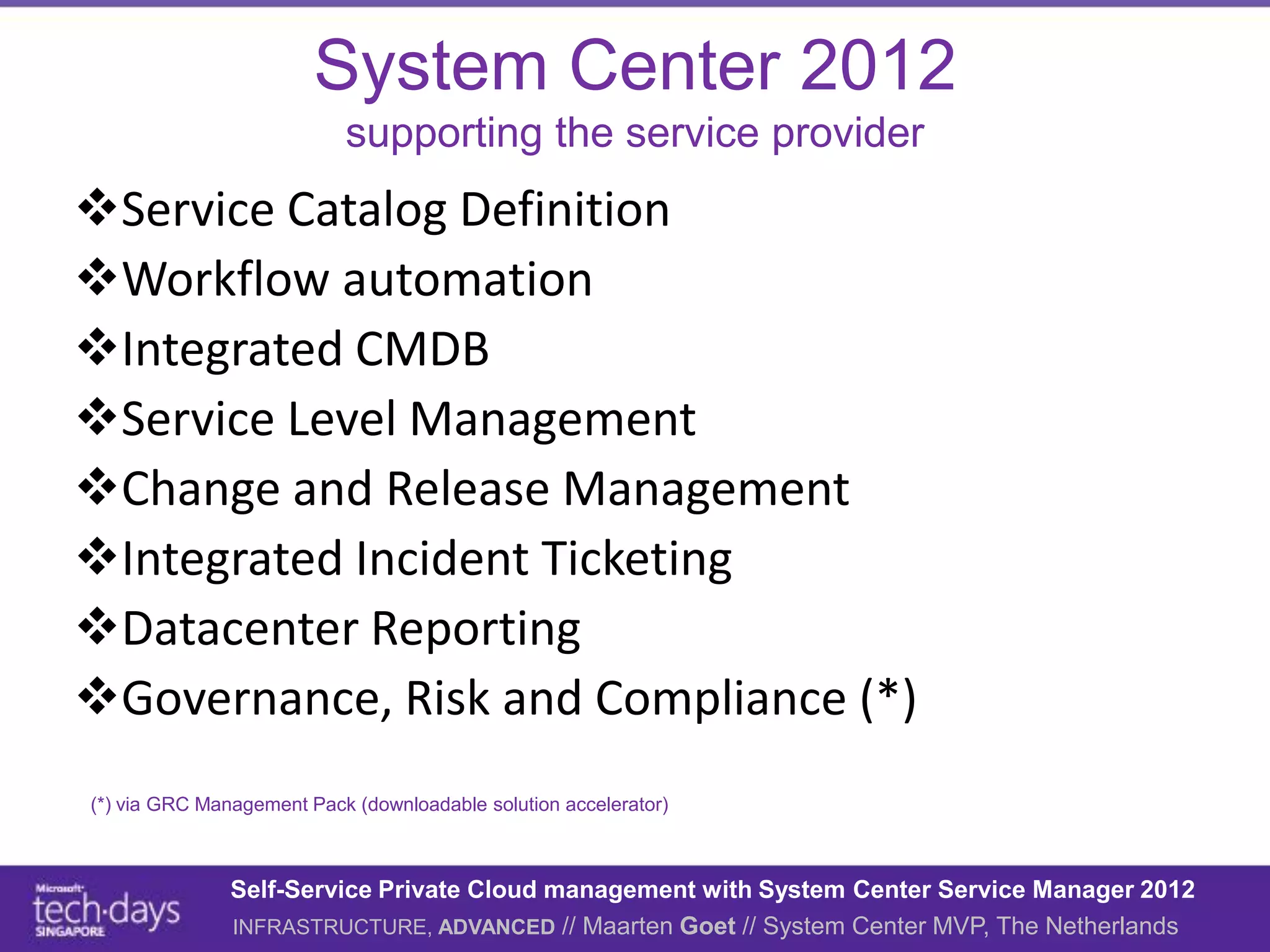
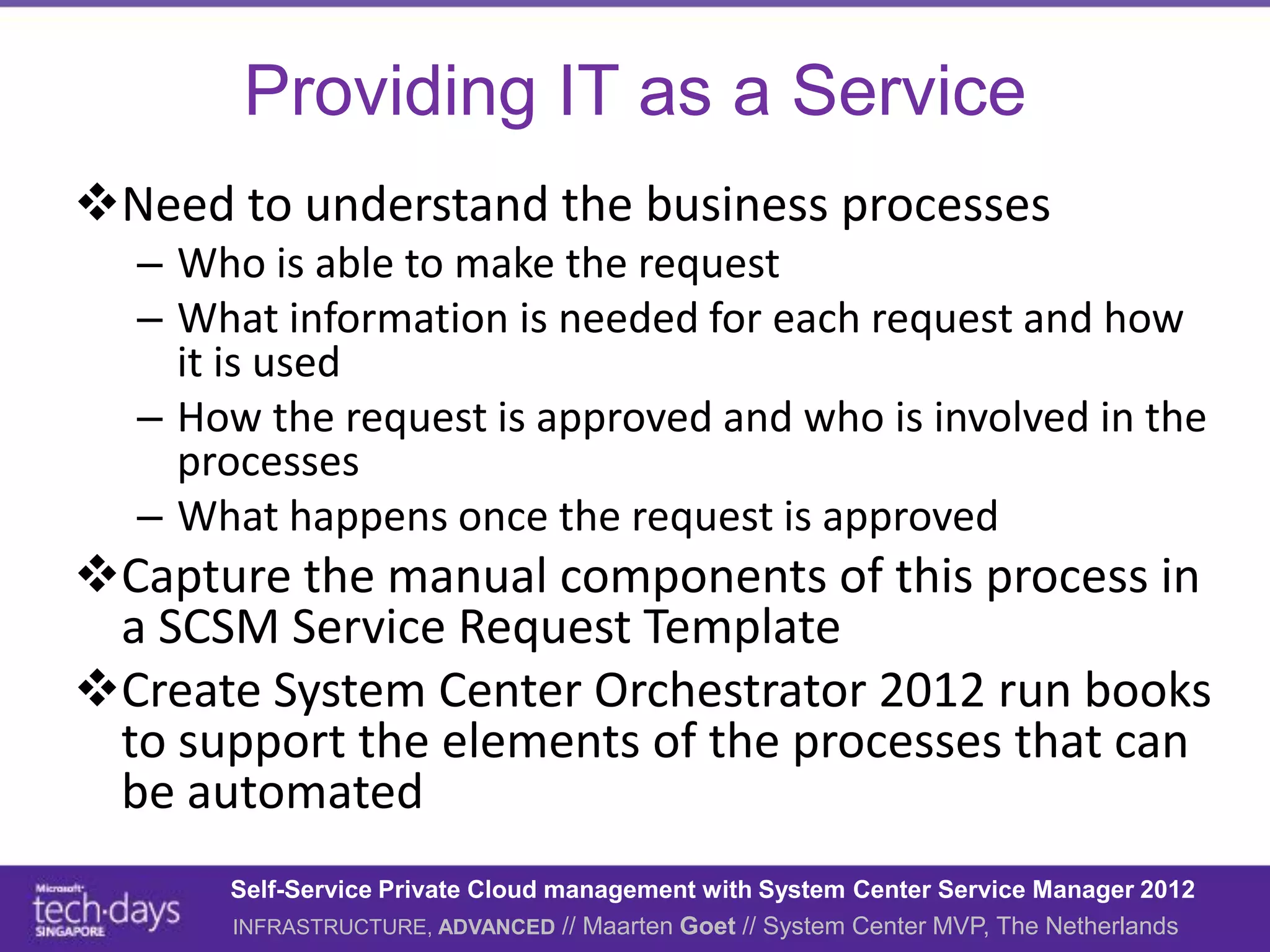
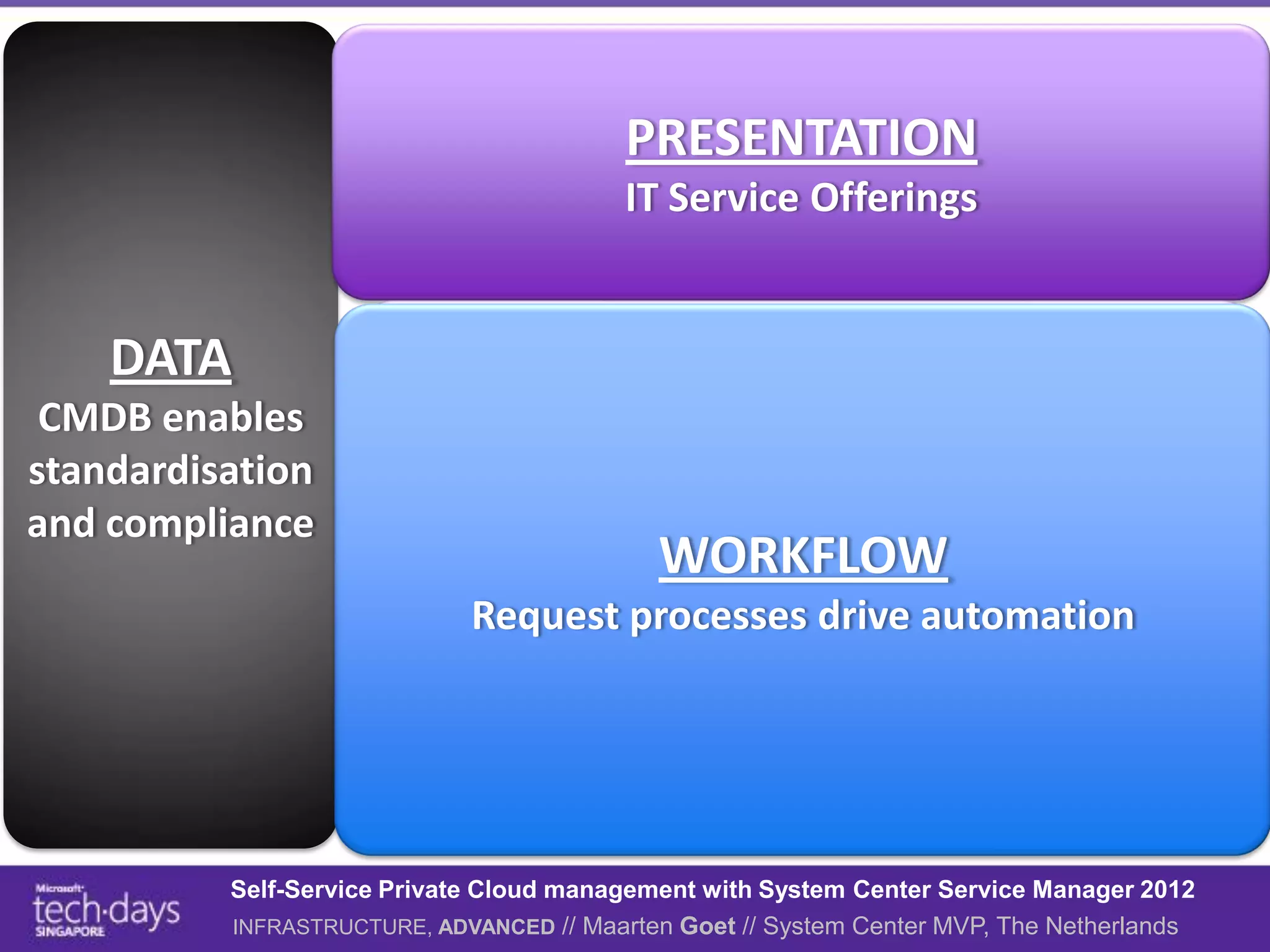
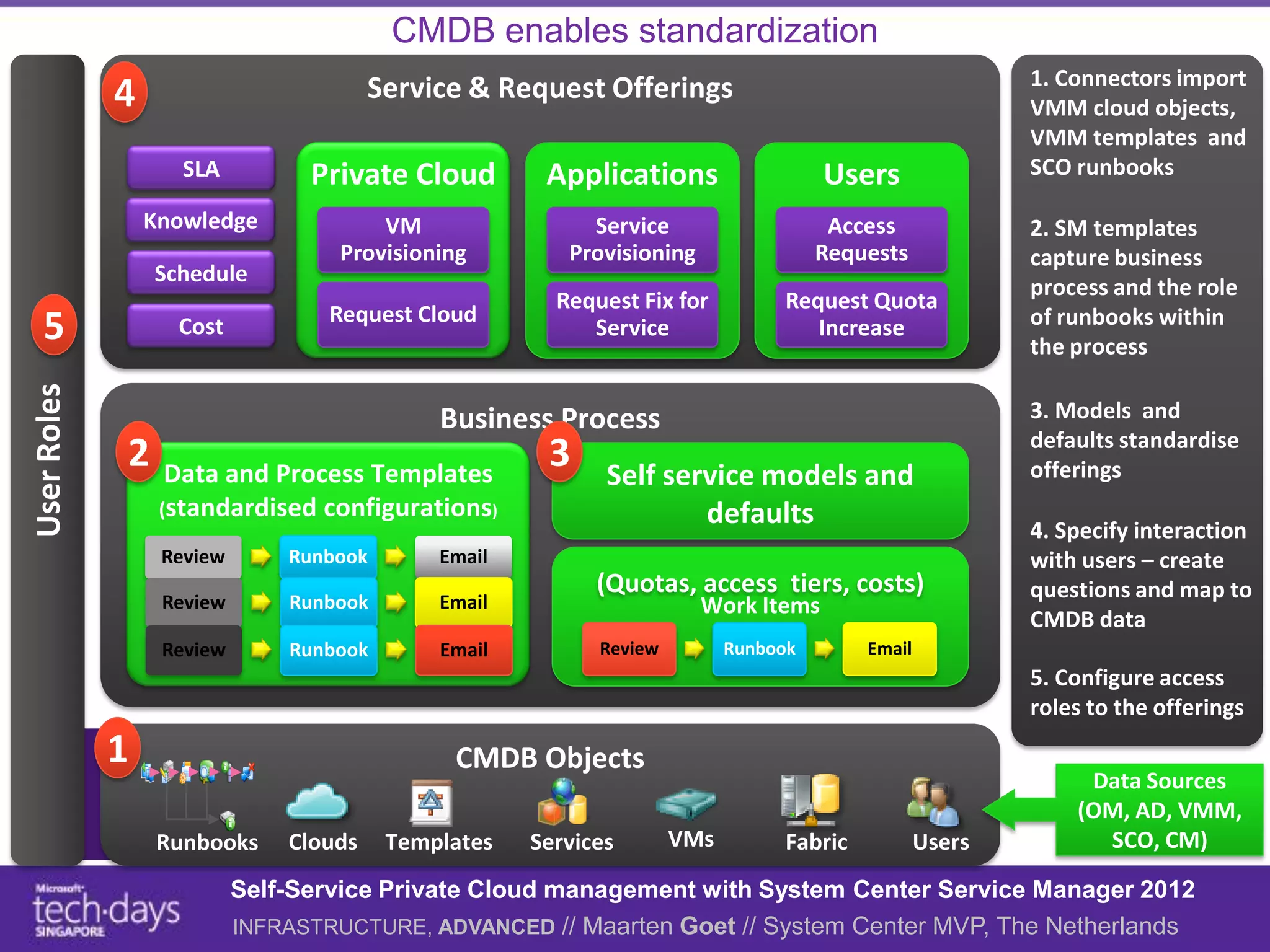
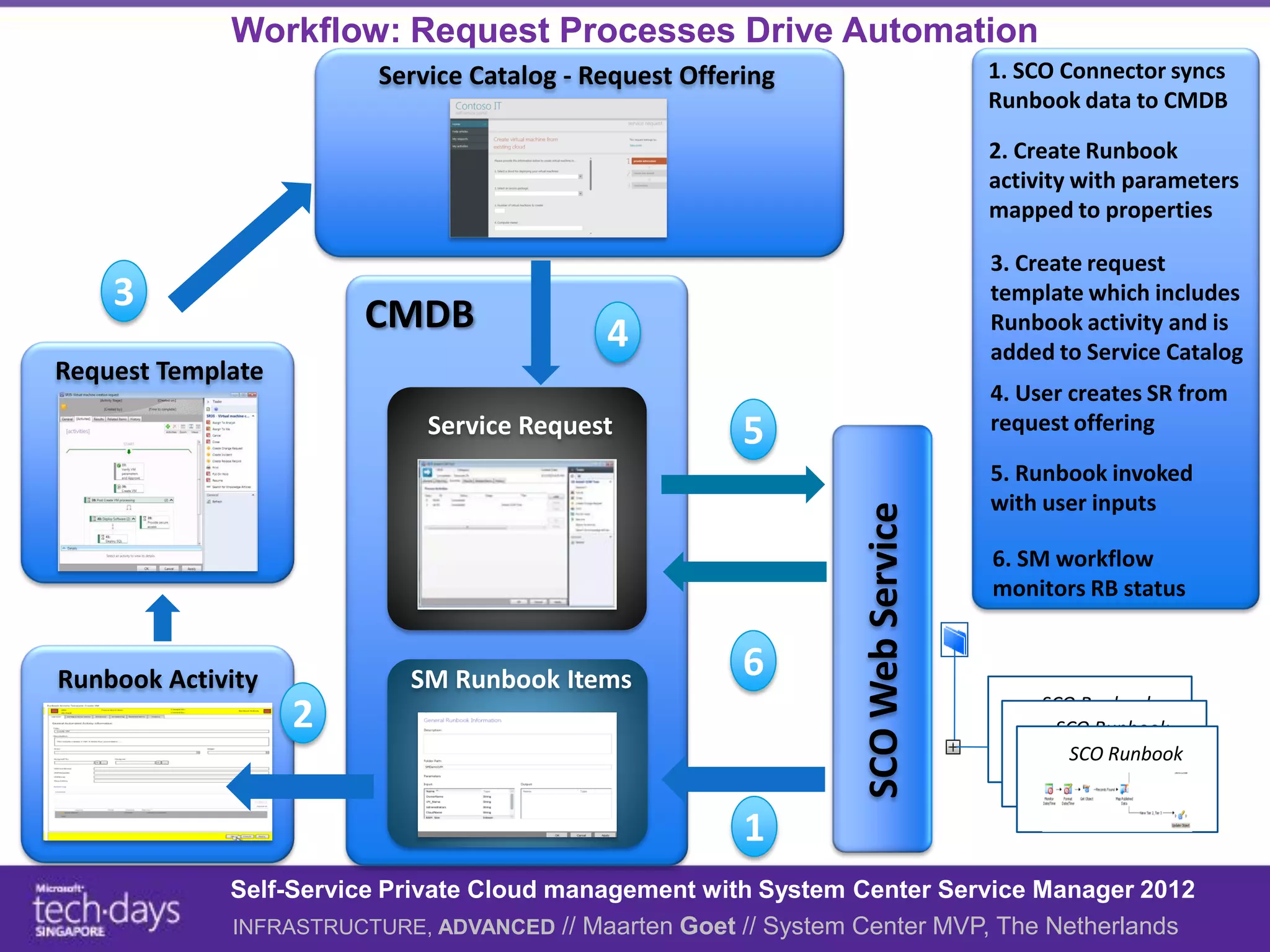
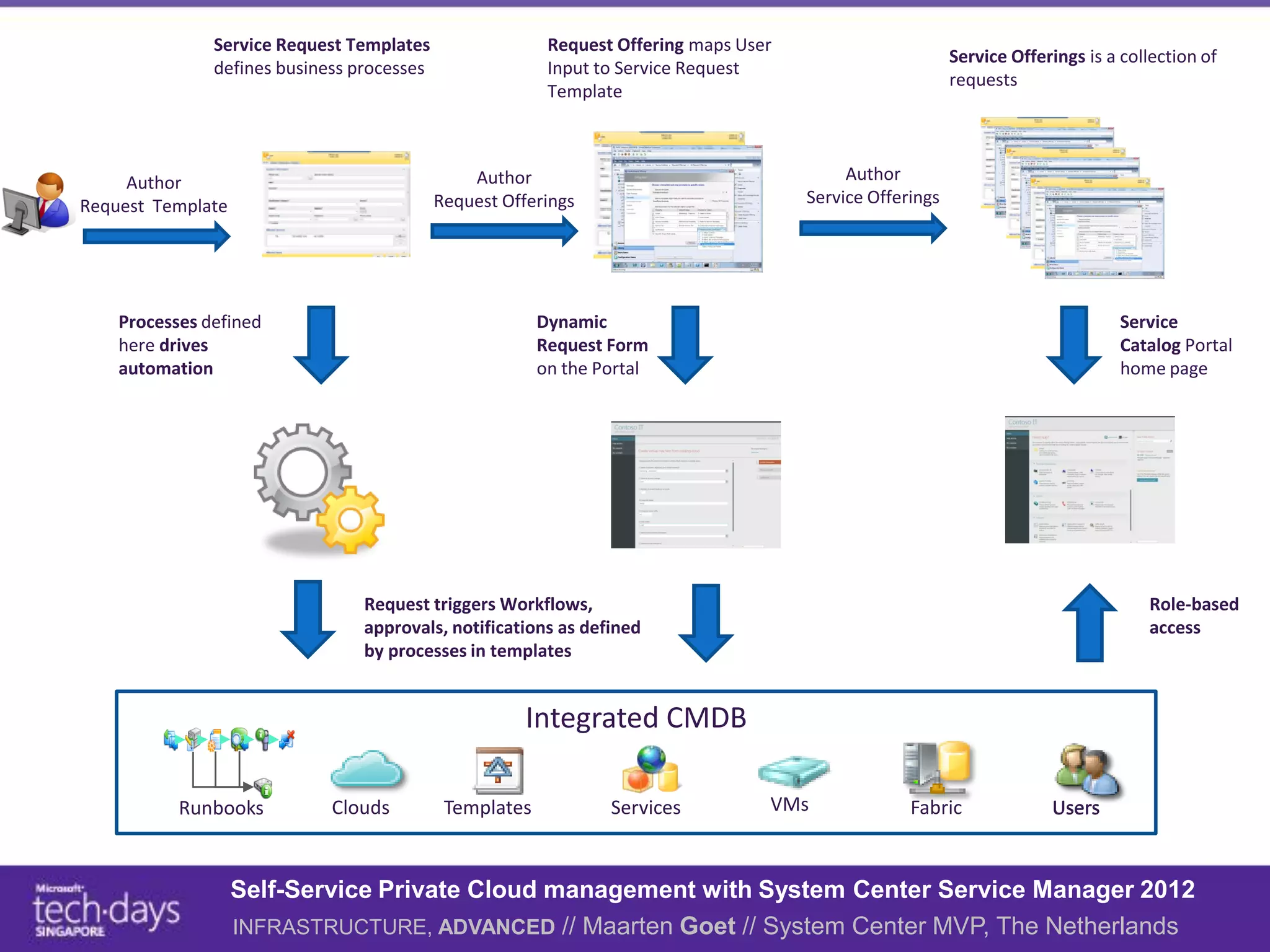
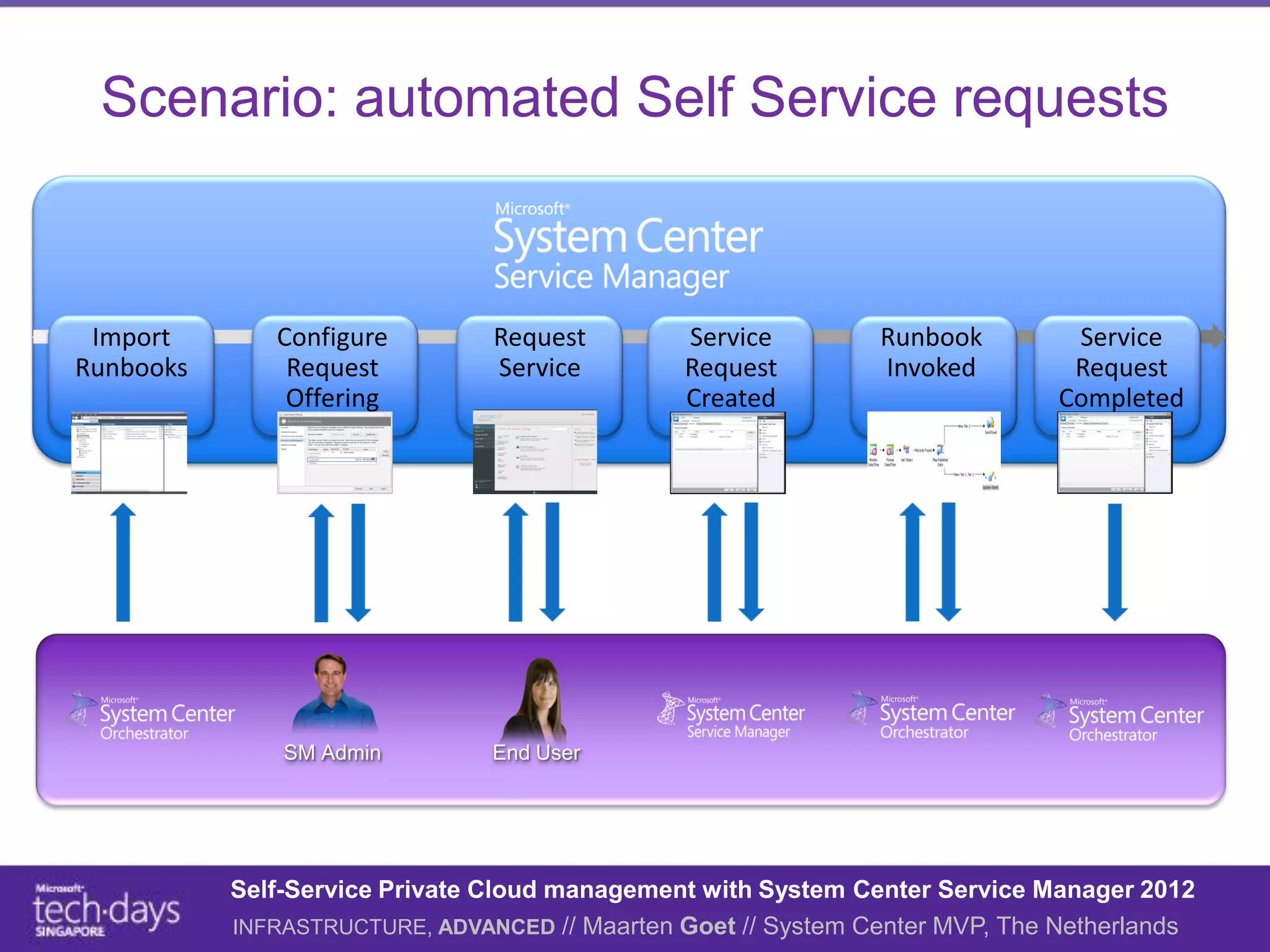
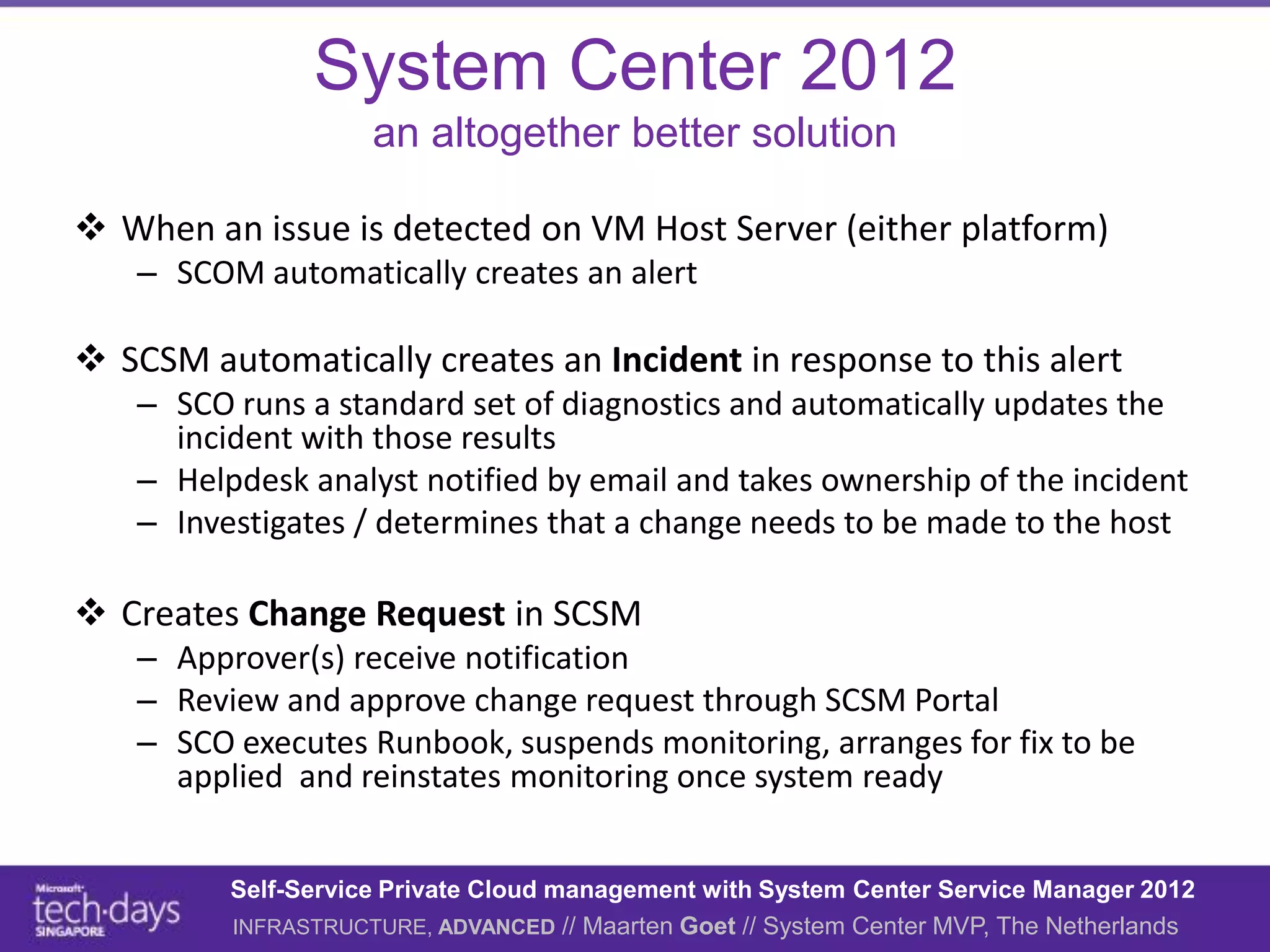
This document discusses using System Center Service Manager 2012 to enable self-service private cloud management. It provides an overview of IT service management for the cloud and how ITSM can support both business users and datacenter administrators. It demonstrates how Service Manager can be used to define service catalogs, automate request workflows using Orchestrator runbooks, and integrate with other System Center products like Virtual Machine Manager to deploy virtual machines and services. The goal is to provide IT as a service and enable self-service provisioning and management of cloud resources through standardized and automated processes.