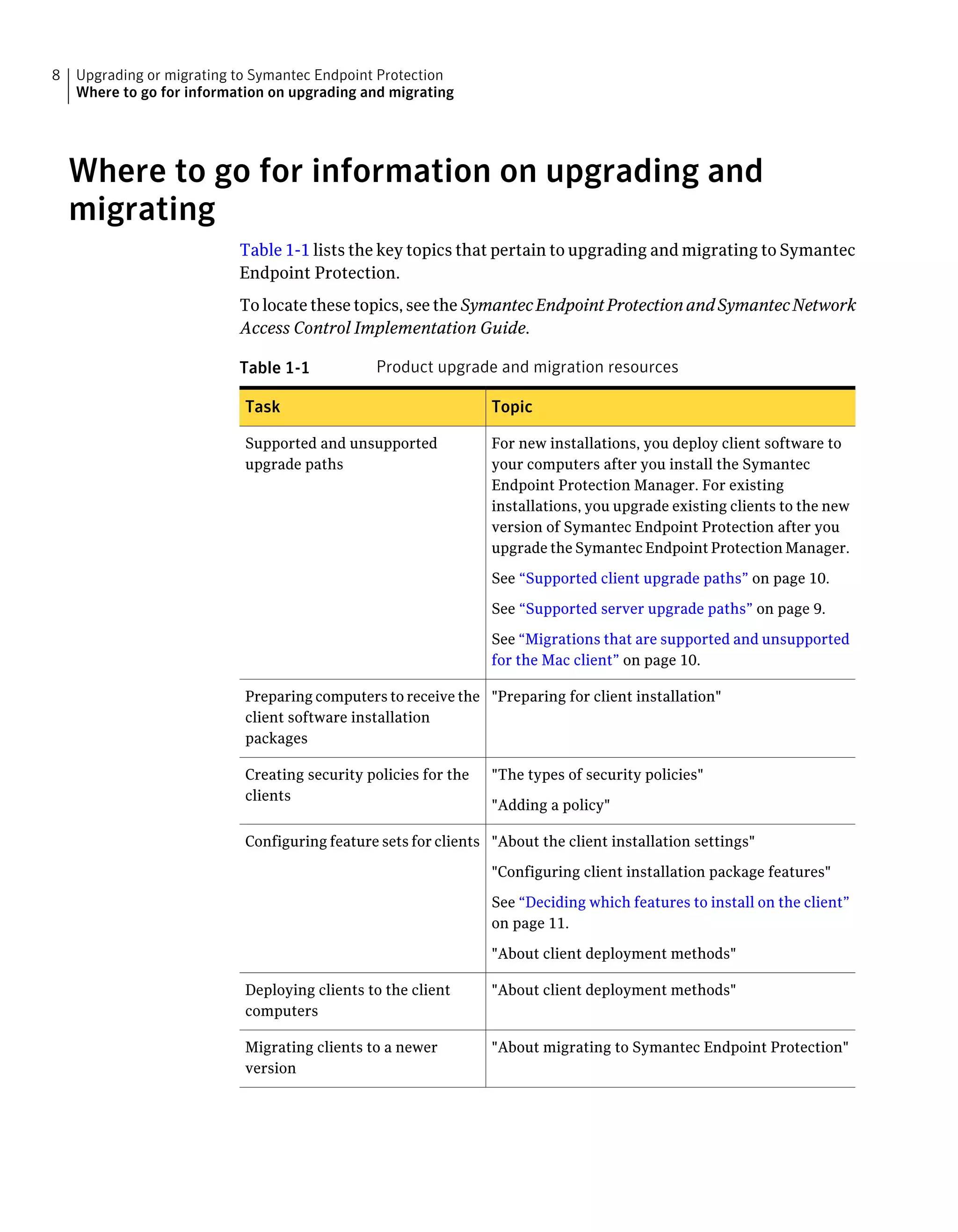
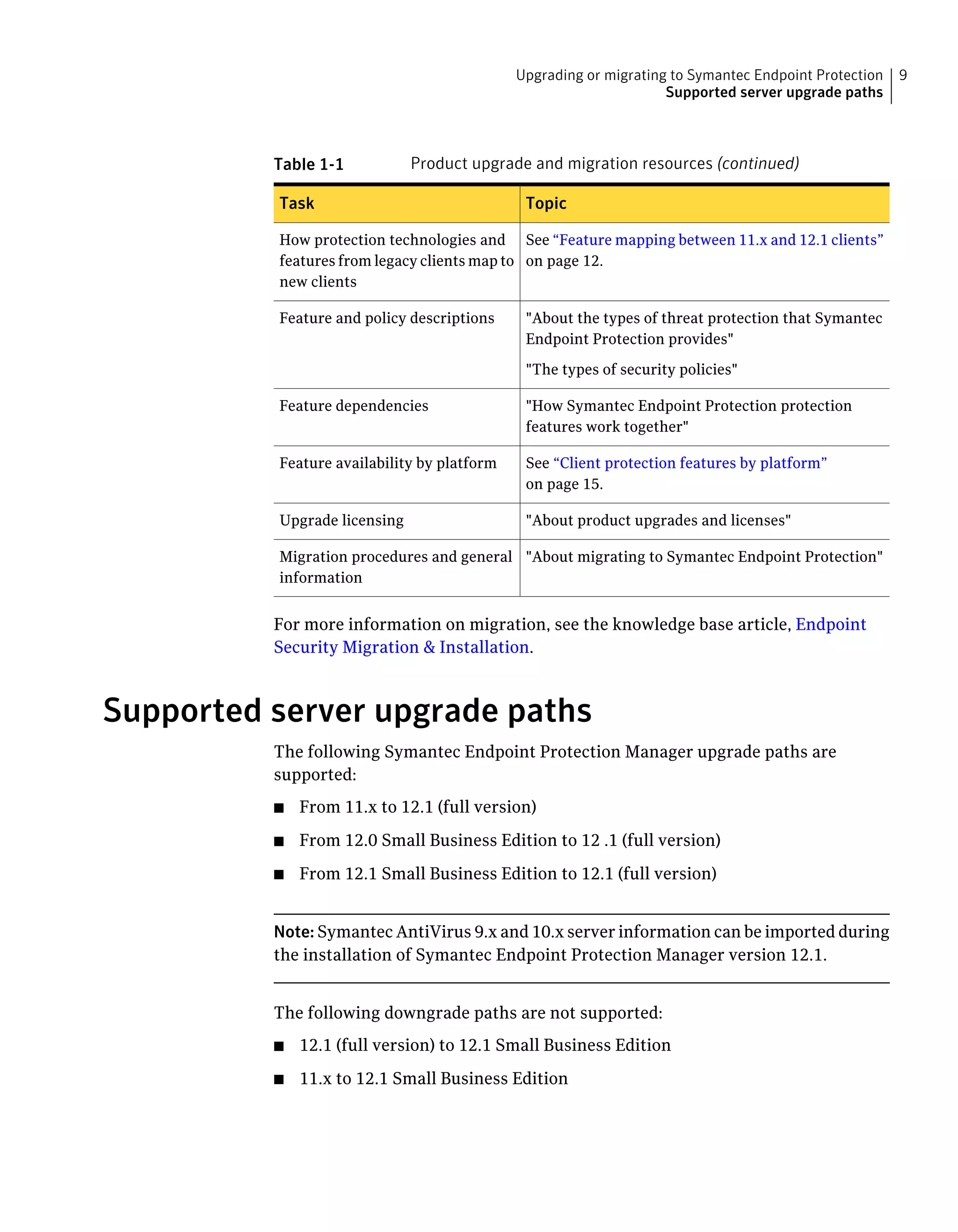
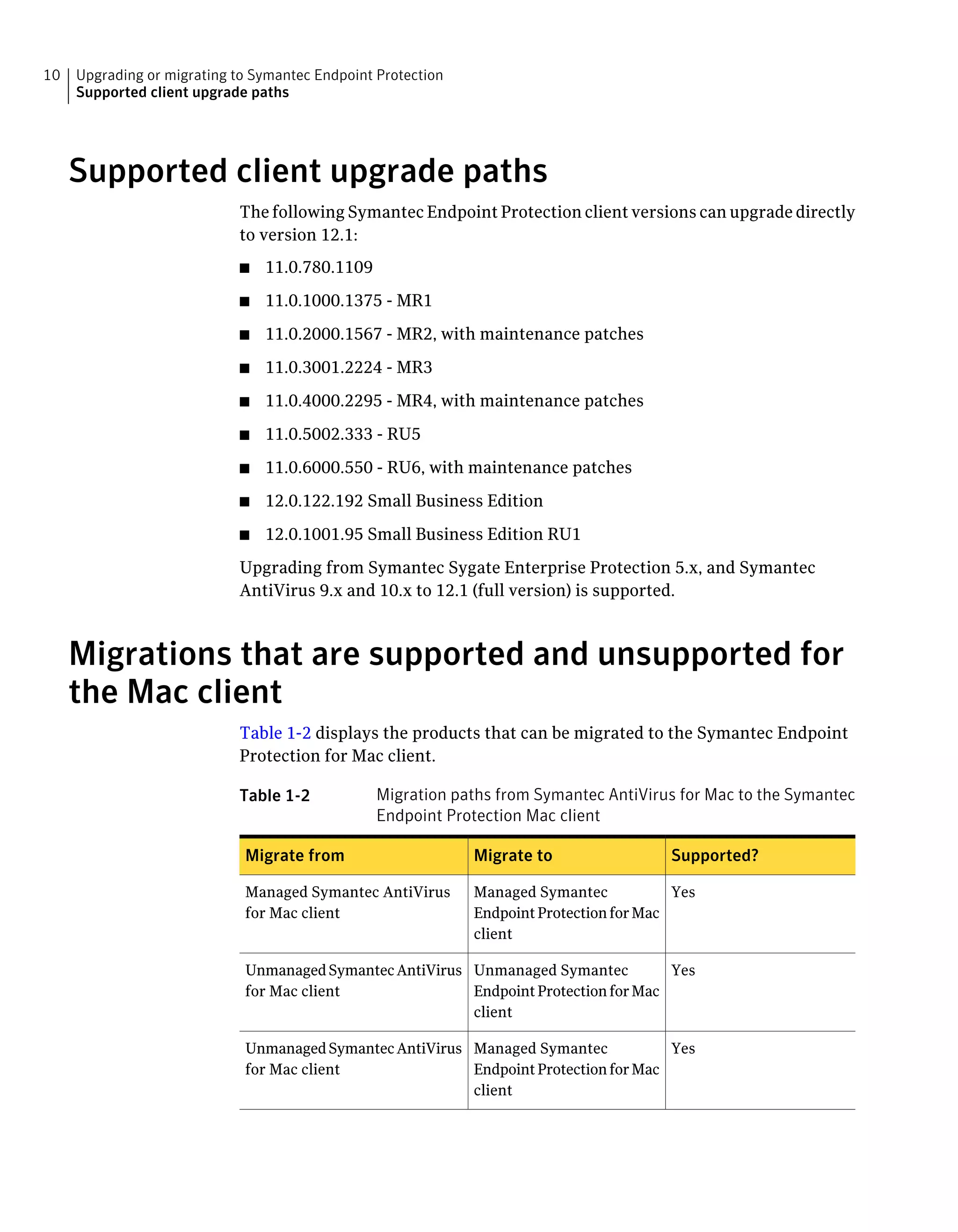
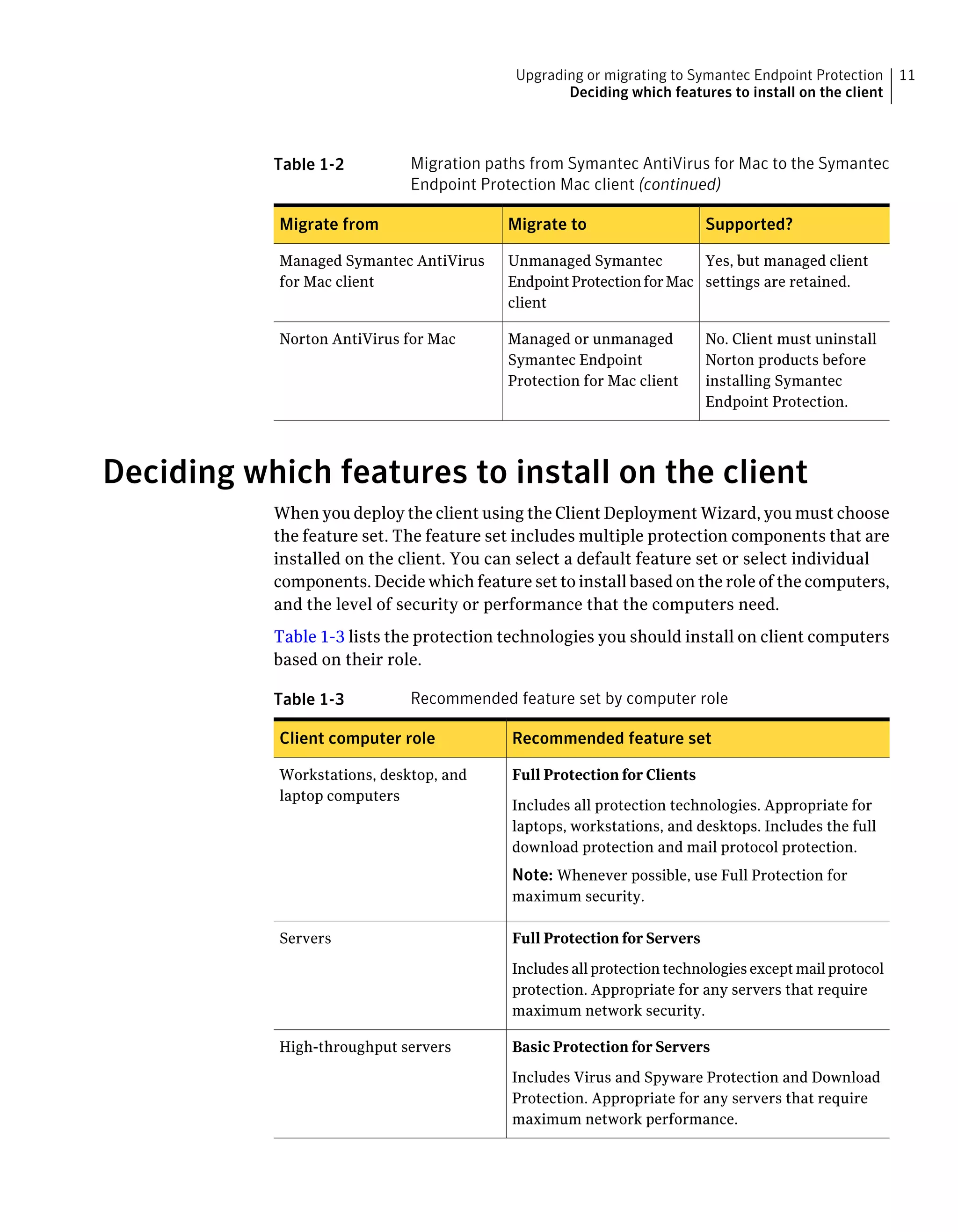
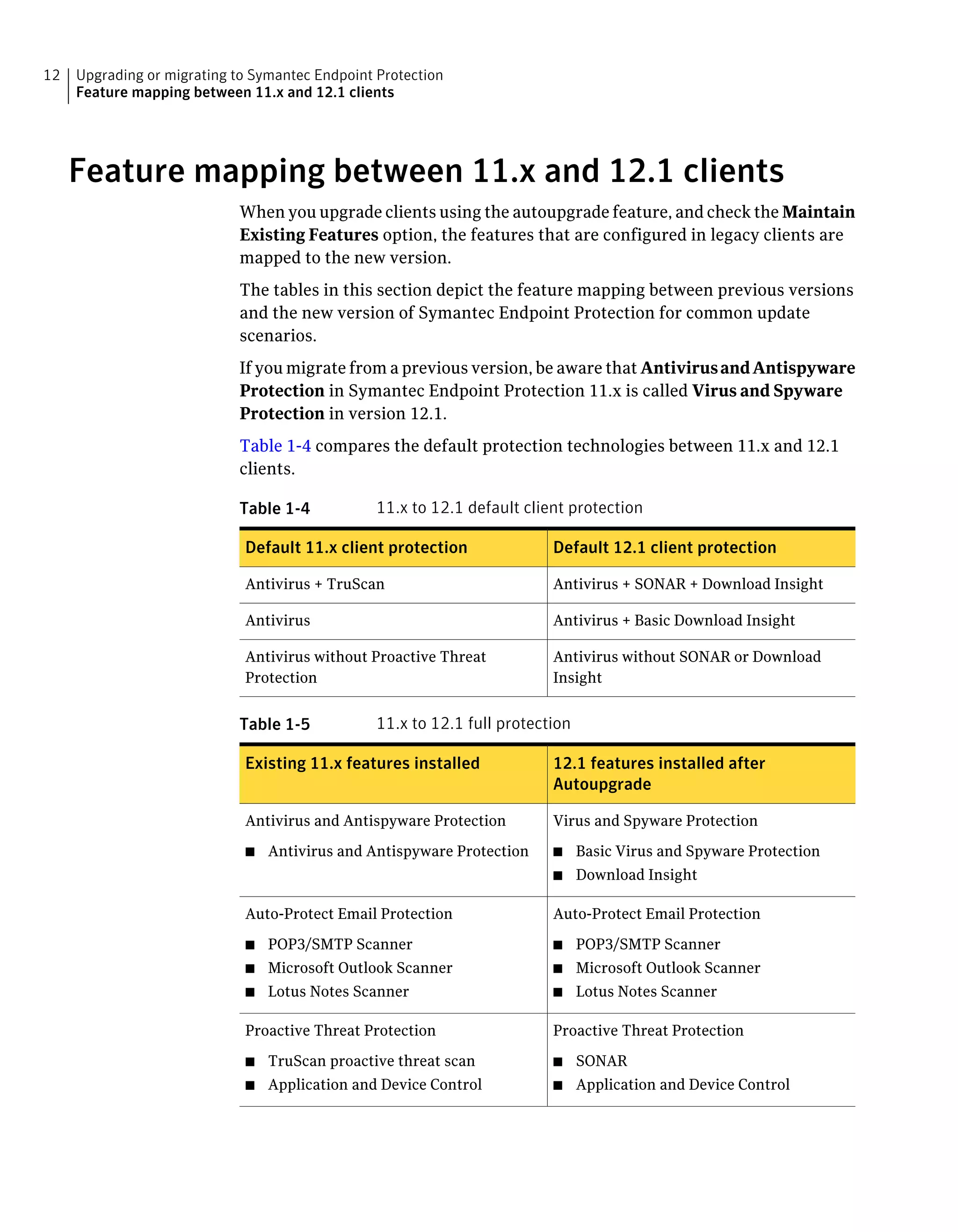
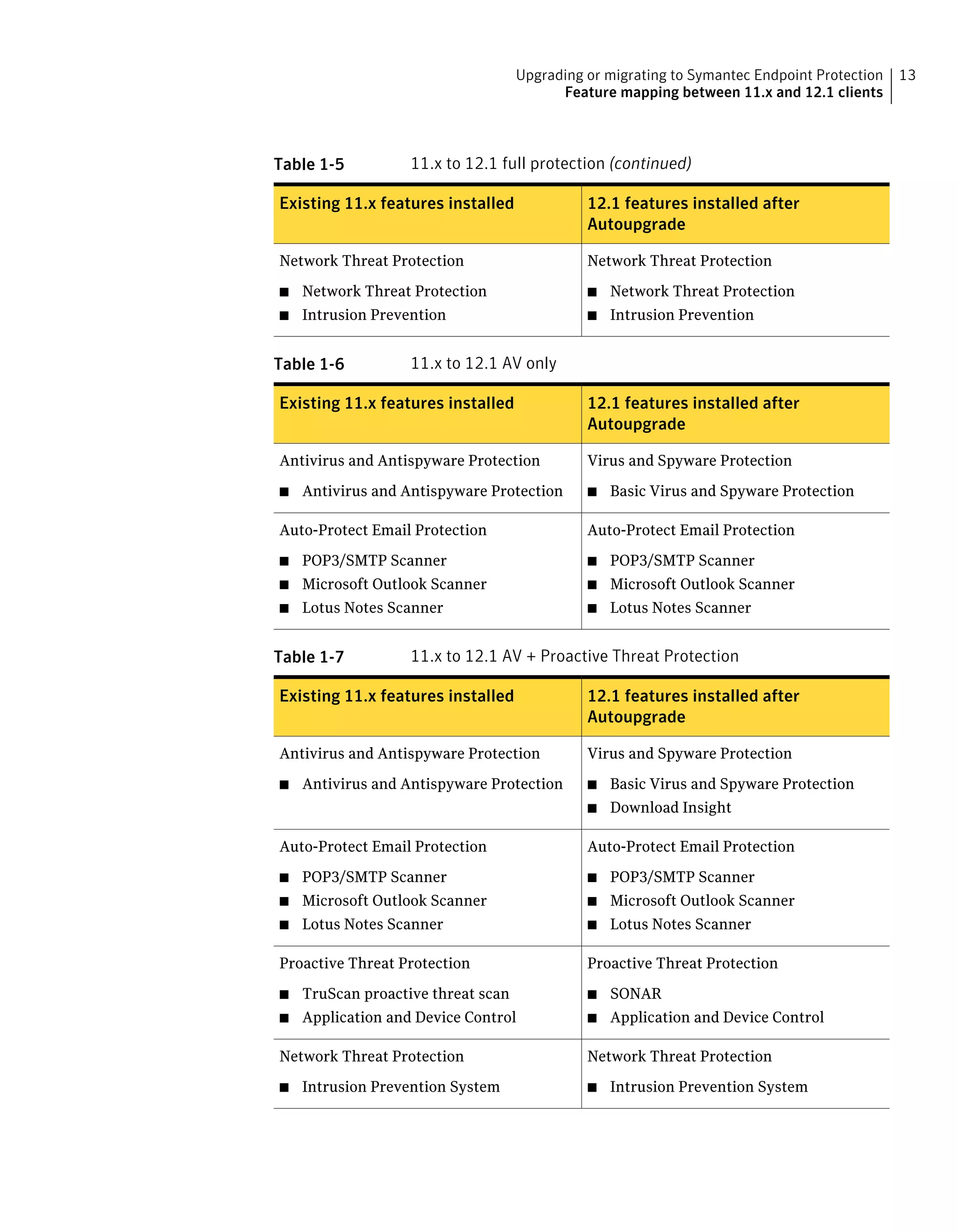
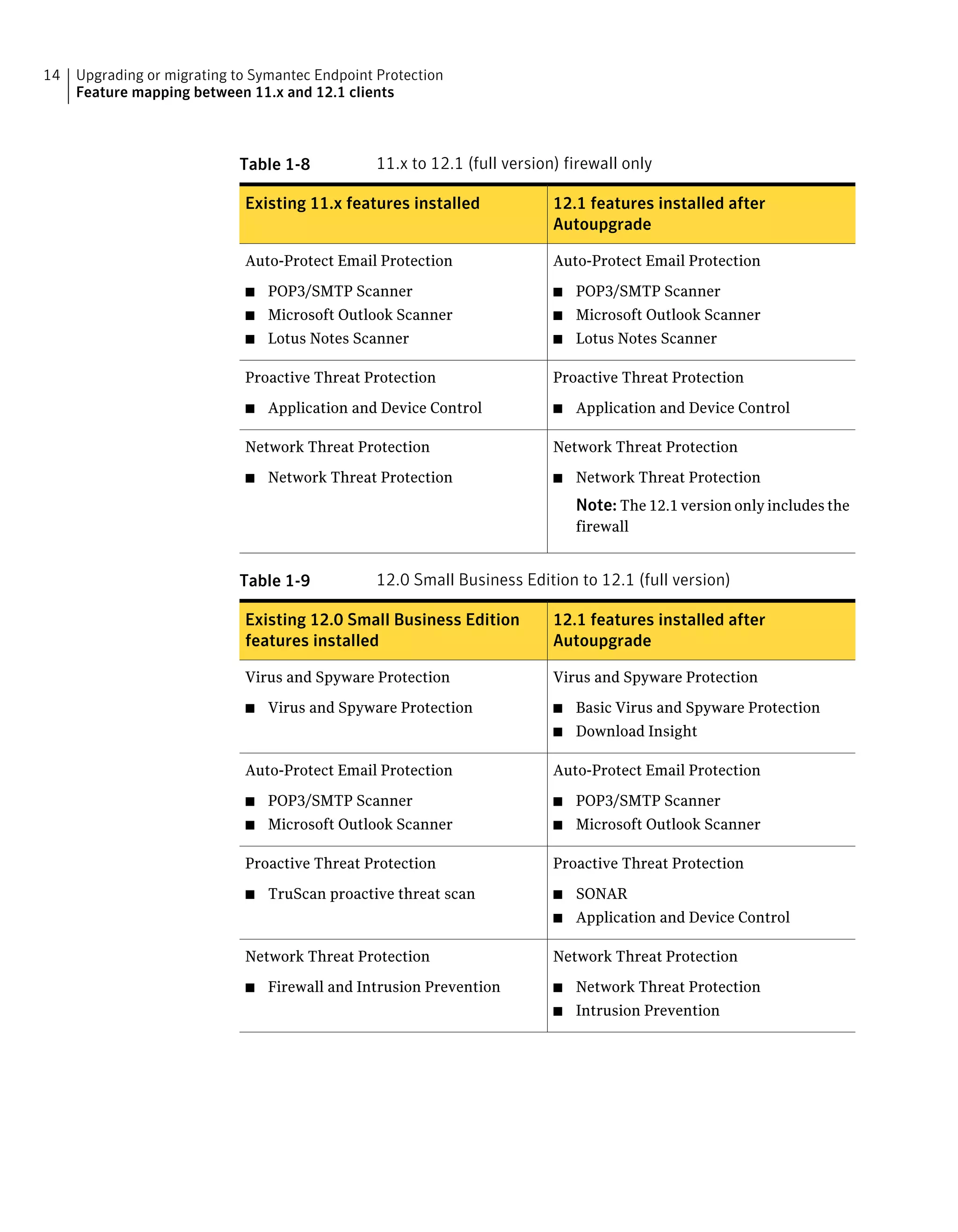
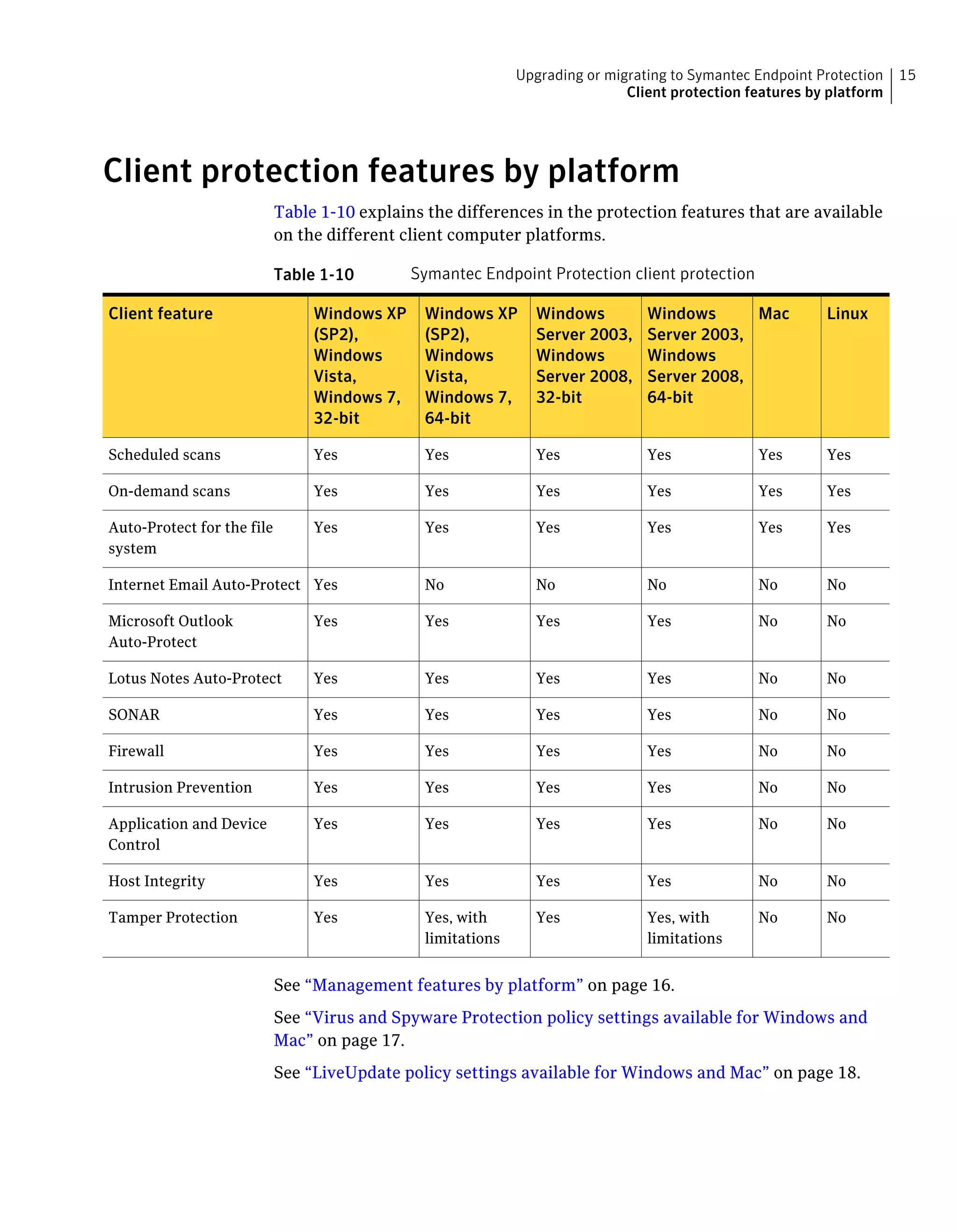
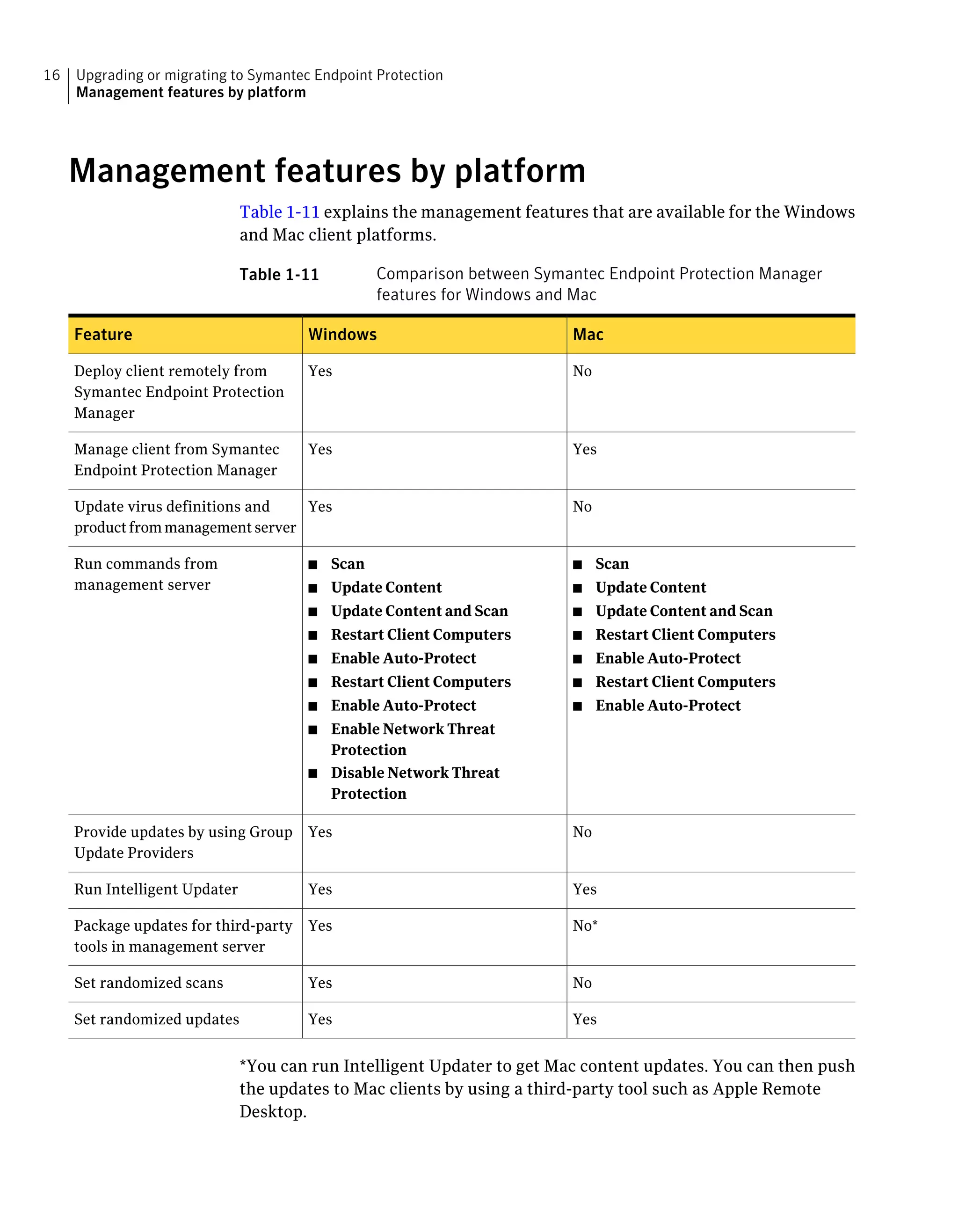
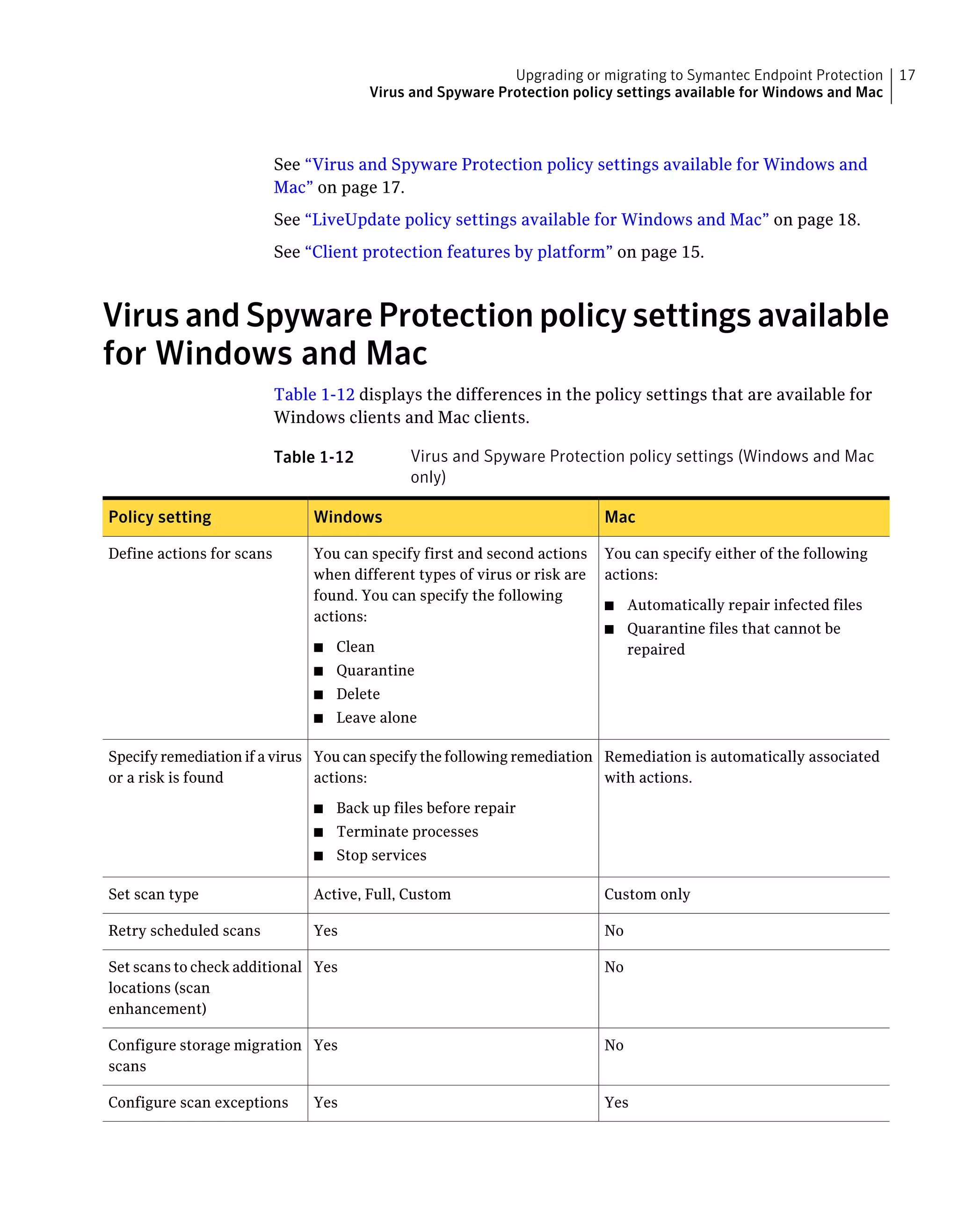
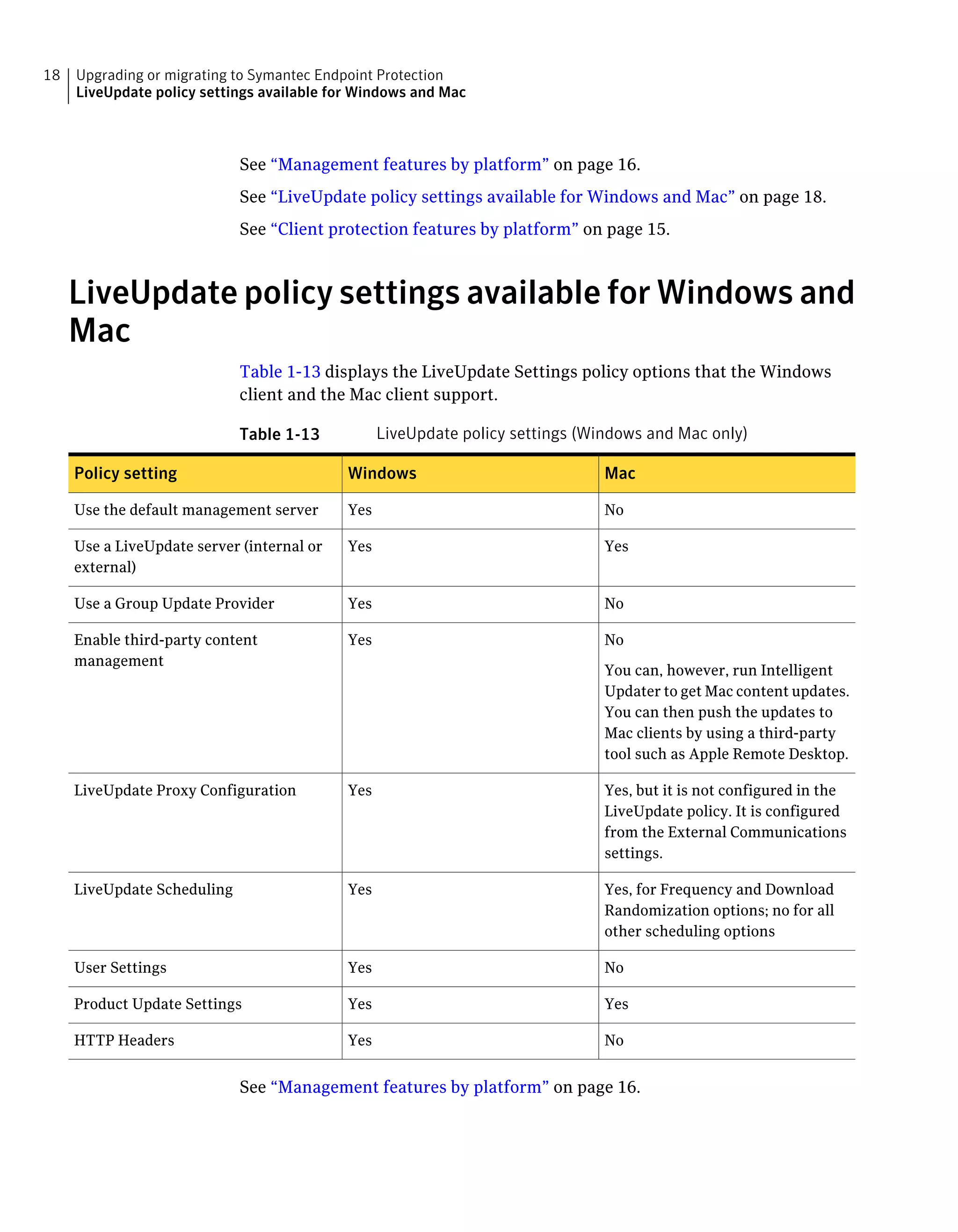
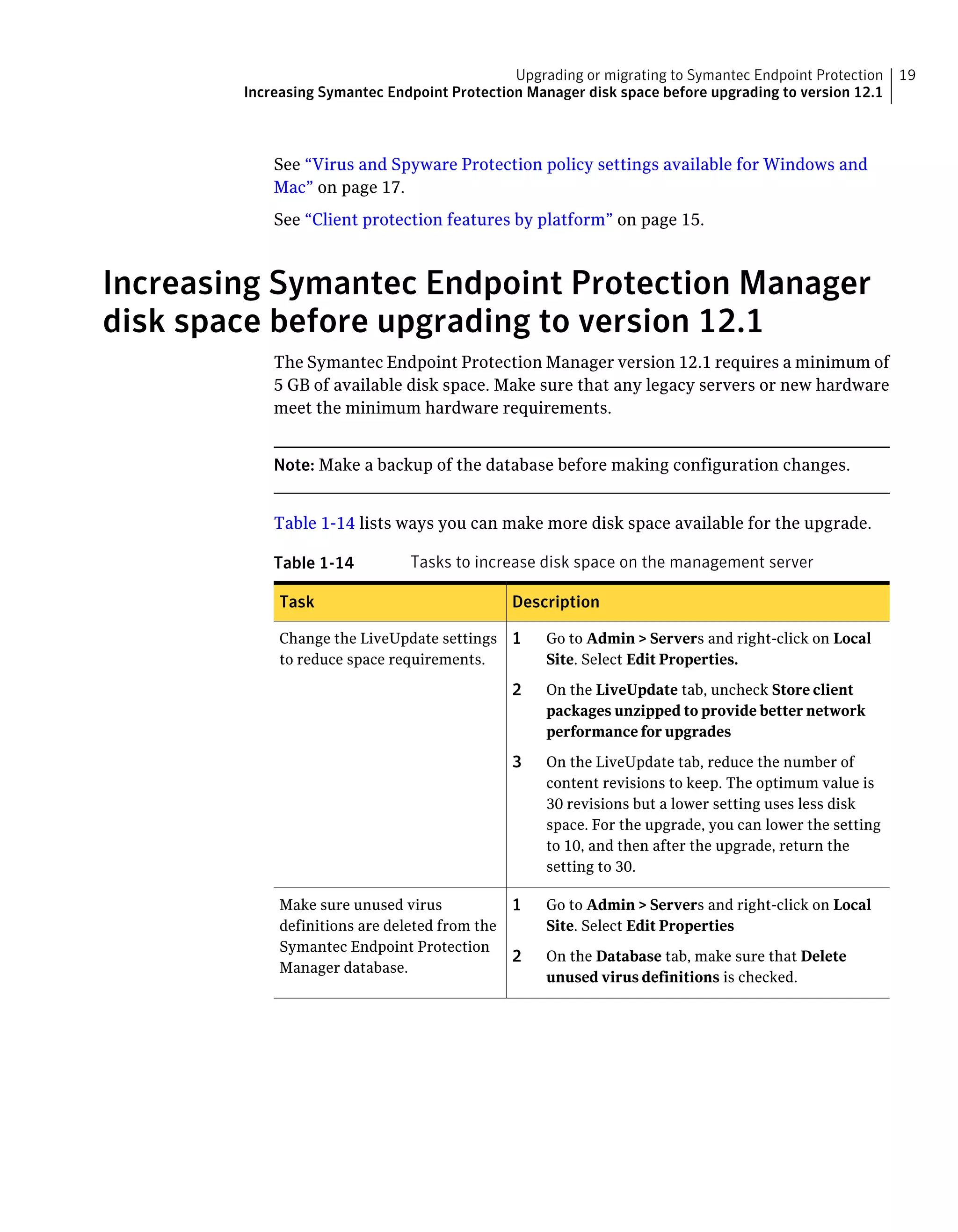
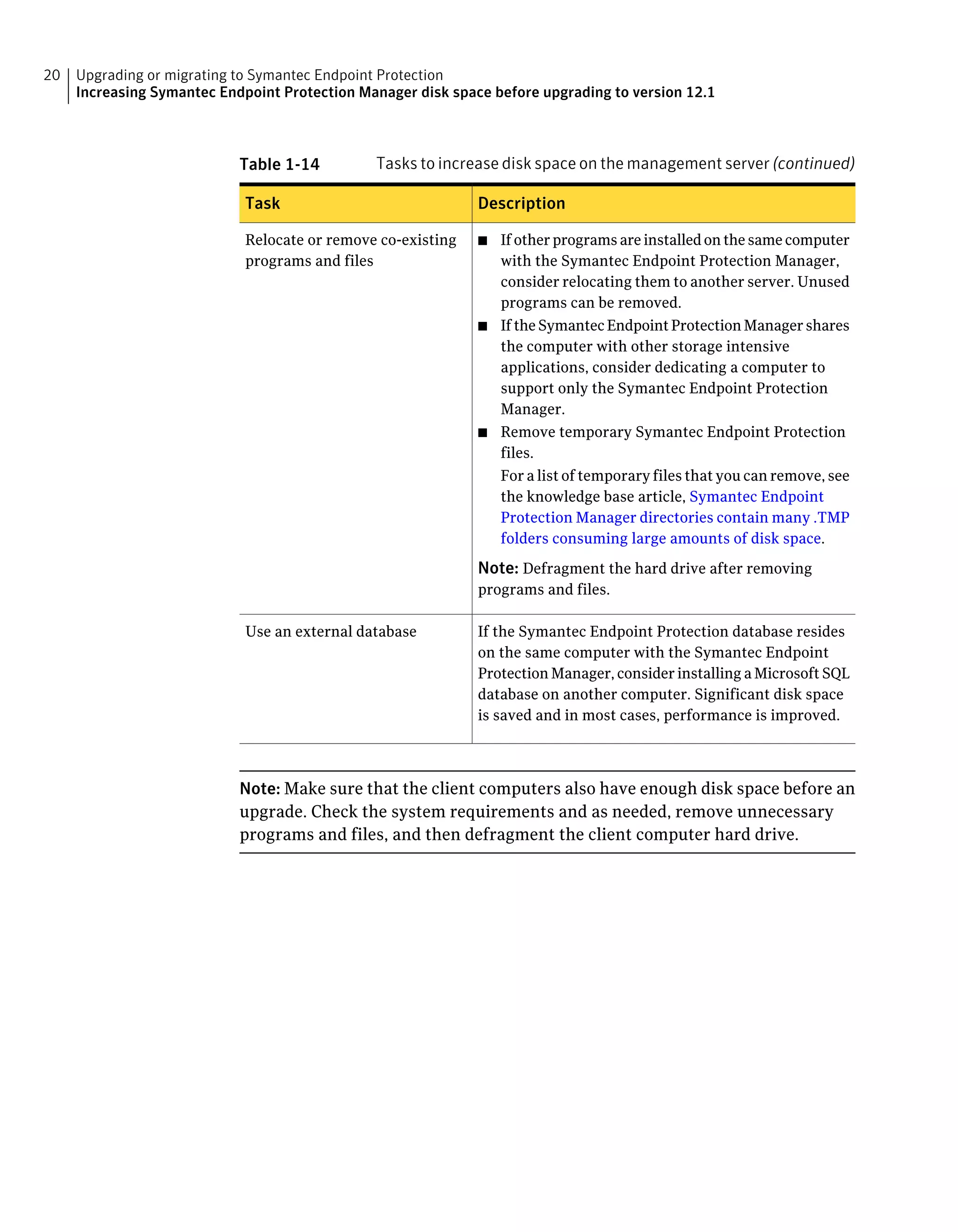
This document provides guidance on upgrading and migrating to Symantec Endpoint Protection 12.1 from previous versions. It outlines supported upgrade paths from versions 11.x and 12.0 to 12.1. It also discusses feature mapping when upgrading clients to maintain existing protections. Additionally, it provides recommendations on feature sets to install based on client computer roles.