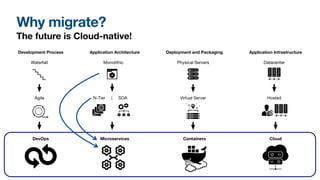
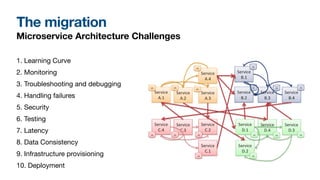
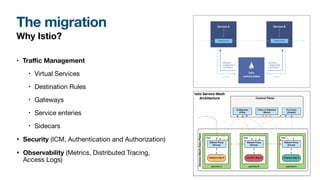
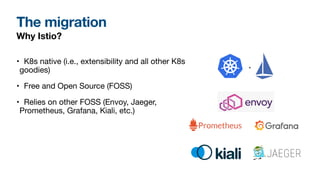
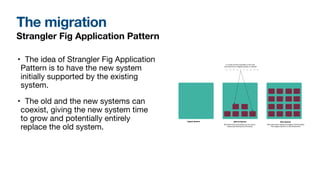
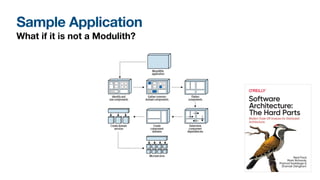
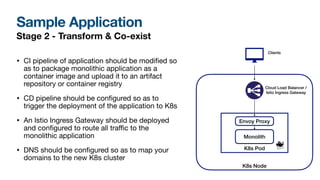
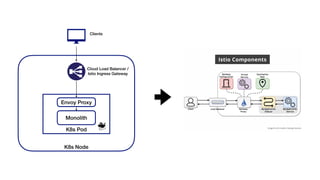
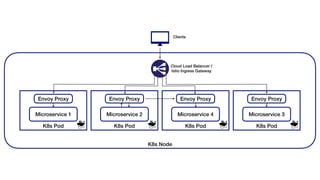
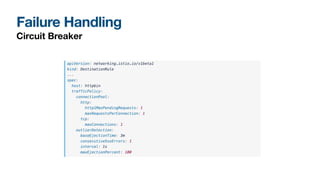
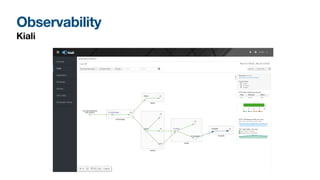
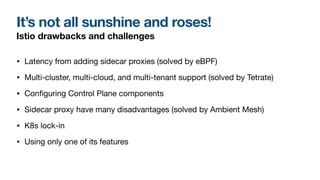
The document outlines a presentation by Ahmed Misbah on migrating to microservices, emphasizing the benefits, challenges, and various migration strategies like the incremental approach and strangler fig pattern. It covers the advantages of microservices such as independent deployability and reduced team dependencies, as well as the technologies involved, particularly Istio for service mesh management. The presentation also addresses potential challenges and the solutions for successful migration, including observability and security aspects.