Mca2020 advanced data structure
•Download as DOCX, PDF•
0 likes•136 views
Dear students get fully solved assignments Send your semester & Specialization name to our mail id : help.mbaassignments@gmail.com or call us at : 08263069601
Report
Share
Report
Share
Recommended
Quantum Deep Learning

In recent years, deep learning has had a profound impact on machine learning and artificial intelligence. At the same time, algorithms for quantum computers have been shown to efficiently solve some problems that are intractable on conventional, classical computers. We show that quantum computing not only reduces the time required to train a deep restricted Boltzmann machine, but also provides a richer and more comprehensive framework for deep learning than classical computing and leads to significant improvements in the optimization of the underlying objective function. Our quantum methods also permit efficient training of full Boltzmann machines and multilayer, fully connected models and do not have well known classical counterparts.
Gans - Generative Adversarial Nets

Generative adversarial networks (GANs) are a class of machine learning frameworks where two neural networks compete against each other. A generator network produces synthetic data to fool a discriminator network, while the discriminator learns to assess whether samples are real or generated. This adversarial process allows GANs to learn the true data distribution and generate highly realistic synthetic examples. The document provides background on machine learning, artificial intelligence, computer vision, and GANs. It explains how GANs work mathematically through a minimax game and value function, and shows how the generator and discriminator improve through training. The document discusses advantages like sharp representations, discusses challenges like training instability, and provides examples of GAN applications.
Bt0065 c programming and data structures - theory-de

The document provides information about getting fully solved assignments for the B.Sc IT program. It lists the semester as the first semester, the subject as Programming and Data Structures, and provides the subject code, credit hours, and maximum marks. It then lists 6 questions related to data types, C program structure, recursion, dynamic memory allocation, implementing a stack using arrays, and binary trees. It provides answers to each question explaining the relevant concepts. Students are instructed to send their semester and specialization details to the given email ID or call the provided phone number to get solved assignments.
A Survey of Deep Learning Algorithms for Malware Detection

Deep learning algorithms have drawn the attention of researchers working in the field of computer vision, speech
recognition, malware detection, pattern recognition and natural language processing. In this paper, we present an overview of
deep learning techniques like Convolutional neural network, deep belief network, Autoencoder, Restricted Boltzmann machine
and recurrent neural network. With this, current work of deep learning algorithms on malware detection is shown with the
help of literature survey. Suggestions for future research are given with full justification. We also showed the experimental
analysis in order to show the importance of deep learning techniques.
support vector machine and associative classification

This document discusses support vector machines (SVM) and associative classification. It introduces SVM as a classifier derived from statistical learning theory that finds the maximal margin hyperplane to classify data. It also explains how SVM can perform linear and non-linear classification using kernels. The document then introduces associative classification, which uses association rule mining to extract classification rules from training data and evaluates rules containing attribute conjunctions to perform classification. Associative classification is shown to potentially overcome some decision tree limitations and produce accurate models.
Basics of Machine Learning

This document provides an overview of machine learning concepts including supervised and unsupervised learning. It defines machine learning as a branch of artificial intelligence that uses data to learn. Unsupervised learning can learn more complex models than supervised learning from unlabeled data without explanations. Dimensionality reduction and density estimation are two types of unsupervised learning. Locally linear embedding (LLE) is a nonlinear dimensionality reduction technique that converts high-dimensional data into a lower-dimensional representation while preserving local neighborhoods. The LLE algorithm involves computing neighbors of each data point, weights between points, and vectors to perform the dimensionality reduction.
llorma_jmlr copy

This document summarizes a research paper that proposes two approaches called LLORMA for constructing local low-rank matrix approximations. The approaches approximate an observed matrix M as a weighted sum of several low-rank matrices, where each low-rank matrix is accurate in a local region of M. This relaxes the assumption that M has global low-rank structure. The paper analyzes the accuracy of the local low-rank modeling approaches and shows they improve prediction accuracy over classical low-rank approximation methods on recommendation tasks.
Unsupervised learning clustering

This document discusses unsupervised learning and clustering. It defines unsupervised learning as modeling the underlying structure or distribution of input data without corresponding output variables. Clustering is described as organizing unlabeled data into groups of similar items called clusters. The document focuses on k-means clustering, describing it as a method that partitions data into k clusters by minimizing distances between points and cluster centers. It provides details on the k-means algorithm and gives examples of its steps. Strengths and weaknesses of k-means clustering are also summarized.
Recommended
Quantum Deep Learning

In recent years, deep learning has had a profound impact on machine learning and artificial intelligence. At the same time, algorithms for quantum computers have been shown to efficiently solve some problems that are intractable on conventional, classical computers. We show that quantum computing not only reduces the time required to train a deep restricted Boltzmann machine, but also provides a richer and more comprehensive framework for deep learning than classical computing and leads to significant improvements in the optimization of the underlying objective function. Our quantum methods also permit efficient training of full Boltzmann machines and multilayer, fully connected models and do not have well known classical counterparts.
Gans - Generative Adversarial Nets

Generative adversarial networks (GANs) are a class of machine learning frameworks where two neural networks compete against each other. A generator network produces synthetic data to fool a discriminator network, while the discriminator learns to assess whether samples are real or generated. This adversarial process allows GANs to learn the true data distribution and generate highly realistic synthetic examples. The document provides background on machine learning, artificial intelligence, computer vision, and GANs. It explains how GANs work mathematically through a minimax game and value function, and shows how the generator and discriminator improve through training. The document discusses advantages like sharp representations, discusses challenges like training instability, and provides examples of GAN applications.
Bt0065 c programming and data structures - theory-de

The document provides information about getting fully solved assignments for the B.Sc IT program. It lists the semester as the first semester, the subject as Programming and Data Structures, and provides the subject code, credit hours, and maximum marks. It then lists 6 questions related to data types, C program structure, recursion, dynamic memory allocation, implementing a stack using arrays, and binary trees. It provides answers to each question explaining the relevant concepts. Students are instructed to send their semester and specialization details to the given email ID or call the provided phone number to get solved assignments.
A Survey of Deep Learning Algorithms for Malware Detection

Deep learning algorithms have drawn the attention of researchers working in the field of computer vision, speech
recognition, malware detection, pattern recognition and natural language processing. In this paper, we present an overview of
deep learning techniques like Convolutional neural network, deep belief network, Autoencoder, Restricted Boltzmann machine
and recurrent neural network. With this, current work of deep learning algorithms on malware detection is shown with the
help of literature survey. Suggestions for future research are given with full justification. We also showed the experimental
analysis in order to show the importance of deep learning techniques.
support vector machine and associative classification

This document discusses support vector machines (SVM) and associative classification. It introduces SVM as a classifier derived from statistical learning theory that finds the maximal margin hyperplane to classify data. It also explains how SVM can perform linear and non-linear classification using kernels. The document then introduces associative classification, which uses association rule mining to extract classification rules from training data and evaluates rules containing attribute conjunctions to perform classification. Associative classification is shown to potentially overcome some decision tree limitations and produce accurate models.
Basics of Machine Learning

This document provides an overview of machine learning concepts including supervised and unsupervised learning. It defines machine learning as a branch of artificial intelligence that uses data to learn. Unsupervised learning can learn more complex models than supervised learning from unlabeled data without explanations. Dimensionality reduction and density estimation are two types of unsupervised learning. Locally linear embedding (LLE) is a nonlinear dimensionality reduction technique that converts high-dimensional data into a lower-dimensional representation while preserving local neighborhoods. The LLE algorithm involves computing neighbors of each data point, weights between points, and vectors to perform the dimensionality reduction.
llorma_jmlr copy

This document summarizes a research paper that proposes two approaches called LLORMA for constructing local low-rank matrix approximations. The approaches approximate an observed matrix M as a weighted sum of several low-rank matrices, where each low-rank matrix is accurate in a local region of M. This relaxes the assumption that M has global low-rank structure. The paper analyzes the accuracy of the local low-rank modeling approaches and shows they improve prediction accuracy over classical low-rank approximation methods on recommendation tasks.
Unsupervised learning clustering

This document discusses unsupervised learning and clustering. It defines unsupervised learning as modeling the underlying structure or distribution of input data without corresponding output variables. Clustering is described as organizing unlabeled data into groups of similar items called clusters. The document focuses on k-means clustering, describing it as a method that partitions data into k clusters by minimizing distances between points and cluster centers. It provides details on the k-means algorithm and gives examples of its steps. Strengths and weaknesses of k-means clustering are also summarized.
ssc_icml13

This document proposes a novel framework called smooth sparse coding for learning sparse representations of data. It incorporates feature similarity or temporal information present in data sets via non-parametric kernel smoothing. The approach constructs codes that represent neighborhoods of samples rather than individual samples, leading to lower reconstruction error. It also proposes using marginal regression rather than lasso for obtaining sparse codes, providing a dramatic speedup of up to two orders of magnitude without sacrificing accuracy. The document contributes a framework for incorporating domain information into sparse coding, sample complexity results for dictionary learning using smooth sparse coding, an efficient marginal regression training procedure, and successful application to classification tasks with improved accuracy and speed.
Introduction to Convolutional Neural Networks

This document provides an introduction and overview of convolutional neural networks (CNNs). It discusses the key operations in a CNN including convolution, nonlinearity, pooling, and fully connected layers. Convolution extracts features from input images using small filters that preserve spatial relationships between pixels. Pooling reduces the dimensionality of feature maps. The network is trained end-to-end using backpropagation to update filter weights and minimize errors between predicted and true outputs. Visualizing CNNs helps understand how they learn features from images to perform classification.
lcr

This paper proposes a new method called Local Collaborative Ranking (LCR) for recommender systems. LCR assumes the user-item rating matrix is locally low-rank, meaning the matrix is low-rank within neighborhoods defined by a distance metric on user-item pairs. LCR combines a recent local low-rank approximation approach with empirical risk minimization for ranking losses. Experiments show LCR outperforms other state-of-the-art recommendation methods. LCR is also easily parallelizable, making it suitable for large-scale industrial applications.
Person re-identification, PhD Day 2011

Awarded presentation of my research activity, PhD Day 2011, February 23th 2011, Cagliari, Italy.
This presentation has been awarded as the best one of the track on information engineering.
Want to know more?
see my publications at
http://prag.diee.unica.it/pra/ita/people/satta
Hierarchical Clustering

This document discusses hierarchical clustering methods, which arrange clusters in a nested tree structure. It describes bottom-up and top-down approaches for hierarchical clustering. Bottom-up starts with each object as a cluster and merges them into larger clusters, while top-down separates all objects into distinct clusters that are successively merged. Various distance measures for determining cluster similarity are presented, such as distance between centroids and Ward's method which minimizes variance.
Transcription Factor DNA Binding Prediction

This project aims to build a binary classifier model to label unlabeled DNA sequences as either positive (p) or negative (n) based on labeled training sequences. The team will take two approaches: 1) A k-mer approach that generates all DNA sequence fragments of length K and counts frequencies to use as attributes for classification models. 2) A PWM approach that uses motif finding tools to generate position weight matrices and score sequences to use as attributes. The approaches will be evaluated individually and combined to obtain the best performing model. Key challenges include deriving meaningful attributes from the sequence data alone. Parameters like k-mer length, number of motifs, and motif lengths will be tuned to optimize model performance.
A few approaches to cope with crash/byzantine failures in communication netwo...

Poster used for the poster session of the 1st GSSI Summer Meetings on Algorithm. Held on 9th of July 2016 at GSSI, L'Aquila, Italy
Dissimilarity-based people re-identification and search for intelligent video...

Slides of my PhD thesis, available at:
http://pralab.diee.unica.it/satta_phdthesis2013
http://pralab.diee.unica.it/en/AmbientIntelligence
Applications of Matrices

The document discusses matrices and their applications. It begins by defining what a matrix is and some basic matrix operations like addition, scalar multiplication, and transpose. It then discusses matrix multiplication and how it can be used to represent systems of linear equations. The document lists several applications of matrices, including representing graphs, transformations in computer graphics, solving systems of linear equations, cryptography, and secret communication methods like steganography. It provides some high-level details about using matrices for secret codes and hiding messages in digital files like images and audio.
SVM

Support Vector Machines (SVMs) are a supervised machine learning method used for classification and regression analysis. SVMs find a hyperplane that separates clusters of data points and maximizes the margin between the clusters. The maximal margin hyperplane is the solution to an optimization problem that maximizes the margin and minimizes a cost function accounting for misclassifications. Kernels can be used to project data into a higher dimensional space to allow for separation of data that is not linearly separable in the original space. SVMs have been applied to problems such as computer-aided diagnosis of Alzheimer's disease from medical images and ranking models.
15857 cse422 unsupervised-learning

This document provides an overview of supervised and unsupervised learning, with a focus on clustering as an unsupervised learning technique. It describes the basic concepts of clustering, including how clustering groups similar data points together without labeled categories. It then covers two main clustering algorithms - k-means, a partitional clustering method, and hierarchical clustering. It discusses aspects like cluster representation, distance functions, strengths and weaknesses of different approaches. The document aims to introduce clustering and compare it with supervised learning.
Exploiting Dissimilarity Representations for Person Re-Identification

The document discusses person re-identification through dissimilarity representations. It proposes representing each person as a vector of dissimilarity values compared to visual prototypes, rather than traditional descriptors. This reduces storage requirements and allows extremely fast matching. The Multiple Component Dissimilarity framework is presented, which defines prototypes, and represents templates and queries as dissimilarity vectors for efficient matching in the dissimilarity space. Preliminary experiments applying this framework to a specific method show improvements in computational time and storage over the original method.
CC282 Unsupervised Learning (Clustering) Lecture 7 slides for ...

This document provides an overview of unsupervised learning techniques, specifically clustering algorithms. It discusses three main approaches to clustering: exclusive clustering using k-means, agglomerative clustering using hierarchical algorithms, and overlapping clustering using fuzzy c-means. It provides examples and explanations of how k-means and hierarchical clustering work, including the steps involved in each algorithm. It also discusses strengths and weaknesses of different clustering methods.
IRJET- Chatbot Using Gated End-to-End Memory Networks

The document describes a proposed chatbot system that uses a gated end-to-end memory network model for hospital appointment booking. The model is trained on dialog data consisting of user utterances and bot responses related to booking appointments. It uses an attention mechanism over the dialog memory to select relevant parts of the conversation. The model is trained end-to-end to dynamically regulate interactions with the memory. Experiments show it can handle new combinations of fields when booking appointments in a simulated hospital reservation scenario.
Convolutional Neural Networks for Sentence Classification

This document discusses convolutional neural networks for sentence classification. It begins with introducing automated text classification and definitions of key concepts like deep learning, language models, neural language models, and convolutional neural networks. It then discusses various datasets used for evaluating models. Several CNN models are described and their results on different datasets are presented, outperforming other methods. The document concludes by showing the most similar words learned by static and non-static CNN channels.
X-TREPAN : A Multi Class Regression and Adapted Extraction of Comprehensible ...

The document describes an algorithm called X-TREPAN that extracts decision trees from trained neural networks. X-TREPAN is an enhancement of the TREPAN algorithm that allows it to handle both multi-class classification and multi-class regression problems. It can also analyze generalized feed forward networks. The algorithm was tested on several real-world datasets and was found to generate decision trees with good classification accuracy while also maintaining comprehensibility.
Image Generation from Caption 

Generating images from a text description is as challenging as it is interesting. The Adversarial network
performs in a competitive fashion where the networks are the rivalry of each other. With the introduction of
Generative Adversarial Network, lots of development is happening in the field of Computer Vision. With
generative adversarial networks as the baseline model, studied Stack GAN consisting of two-stage GANS
step-by-step in this paper that could be easily understood. This paper presents visual comparative study of
other models attempting to generate image conditioned on the text description. One sentence can be related
to many images. And to achieve this multi-modal characteristic, conditioning augmentation is also
performed. The performance of Stack-GAN is better in generating images from captions due to its unique
architecture. As it consists of two GANS instead of one, it first draws a rough sketch and then corrects the
defects yielding a high-resolution image.
Recommendation system

The document discusses recommendation systems and machine learning models for recommendations. It covers the goals of recommendation systems, basic models including collaborative filtering, content-based, and knowledge-based systems. Neighborhood-based collaborative filtering is explained along with matrix factorization models. Deep learning methods for recommendations are also summarized, including neural collaborative filtering, graph-based models, and temporal models that handle dynamic graphs.
Linear Algebra – A Powerful Tool for Data Science

Analysis of data is an important task in data managements systems. Many mathematical tools are used in data analysis. A new division of data management has appeared in machine learning, linear algebra, an optimal tool to analyse and manipulate the data. Data science is a multi-disciplinary subject that uses scientific methods to process the structured and unstructured data to extract the knowledge by applying suitable algorithms and systems. The strength of linear algebra is ignored by the researchers due to the poor understanding. It powers major areas of Data Science including the hot fields of Natural Language Processing and Computer Vision. The data science enthusiasts finding the programming languages for data science are easy to analyze the big data rather than using mathematical tools like linear algebra. Linear algebra is a must-know subject in data science. It will open up possibilities of working and manipulating data. In this paper, some applications of Linear Algebra in Data Science are explained.
Attention Is All You Need

Attention Is All You Need (NIPS 2017)
(Ashish Vaswani, Noam Shazeer, Niki Parmar, Jakob Uszkoreit, Llion Jones, Aidan N. Gomez, Łukasz Kaiser, Illia Polosukhin)
paper link: https://arxiv.org/pdf/1706.03762.pdf
Reference:
https://youtu.be/mxGCEWOxfe8 (by Minsuk Heo)
https://youtu.be/5vcj8kSwBCY (Stanford CS224N: NLP with Deep Learning | Winter 2019 | Lecture 14 – Transformers and Self-Attention)
COBUS KRUGER CV

The candidate has over 30 years of experience in both electrical and mechanical fields, including extensive managerial experience. He holds qualifications in electrical work and has knowledge of mechanical products and theory. As an electrical foreman and area sales manager, he gained experience in project management, time management, and business skills. More recently, he owned his own bearing and transmission business for 10 years. He is a strong leader with excellent communication and problem-solving abilities who is looking for a new opportunity to contribute his skills.
Ml0017 mall management

This document provides sample questions and answers for a Master of Business Administration course on Mall Management. It includes questions and multi-paragraph answers on topics like economic factors that affect commercial real estate, types of psychographic segmentation, concepts of "build to sell" and "build to rent" business models, the 10 steps of hazardous material management, factors that influence mall maintenance, and the 5 stages of emergency response in a mall according to FEMA.
More Related Content
What's hot
ssc_icml13

This document proposes a novel framework called smooth sparse coding for learning sparse representations of data. It incorporates feature similarity or temporal information present in data sets via non-parametric kernel smoothing. The approach constructs codes that represent neighborhoods of samples rather than individual samples, leading to lower reconstruction error. It also proposes using marginal regression rather than lasso for obtaining sparse codes, providing a dramatic speedup of up to two orders of magnitude without sacrificing accuracy. The document contributes a framework for incorporating domain information into sparse coding, sample complexity results for dictionary learning using smooth sparse coding, an efficient marginal regression training procedure, and successful application to classification tasks with improved accuracy and speed.
Introduction to Convolutional Neural Networks

This document provides an introduction and overview of convolutional neural networks (CNNs). It discusses the key operations in a CNN including convolution, nonlinearity, pooling, and fully connected layers. Convolution extracts features from input images using small filters that preserve spatial relationships between pixels. Pooling reduces the dimensionality of feature maps. The network is trained end-to-end using backpropagation to update filter weights and minimize errors between predicted and true outputs. Visualizing CNNs helps understand how they learn features from images to perform classification.
lcr

This paper proposes a new method called Local Collaborative Ranking (LCR) for recommender systems. LCR assumes the user-item rating matrix is locally low-rank, meaning the matrix is low-rank within neighborhoods defined by a distance metric on user-item pairs. LCR combines a recent local low-rank approximation approach with empirical risk minimization for ranking losses. Experiments show LCR outperforms other state-of-the-art recommendation methods. LCR is also easily parallelizable, making it suitable for large-scale industrial applications.
Person re-identification, PhD Day 2011

Awarded presentation of my research activity, PhD Day 2011, February 23th 2011, Cagliari, Italy.
This presentation has been awarded as the best one of the track on information engineering.
Want to know more?
see my publications at
http://prag.diee.unica.it/pra/ita/people/satta
Hierarchical Clustering

This document discusses hierarchical clustering methods, which arrange clusters in a nested tree structure. It describes bottom-up and top-down approaches for hierarchical clustering. Bottom-up starts with each object as a cluster and merges them into larger clusters, while top-down separates all objects into distinct clusters that are successively merged. Various distance measures for determining cluster similarity are presented, such as distance between centroids and Ward's method which minimizes variance.
Transcription Factor DNA Binding Prediction

This project aims to build a binary classifier model to label unlabeled DNA sequences as either positive (p) or negative (n) based on labeled training sequences. The team will take two approaches: 1) A k-mer approach that generates all DNA sequence fragments of length K and counts frequencies to use as attributes for classification models. 2) A PWM approach that uses motif finding tools to generate position weight matrices and score sequences to use as attributes. The approaches will be evaluated individually and combined to obtain the best performing model. Key challenges include deriving meaningful attributes from the sequence data alone. Parameters like k-mer length, number of motifs, and motif lengths will be tuned to optimize model performance.
A few approaches to cope with crash/byzantine failures in communication netwo...

Poster used for the poster session of the 1st GSSI Summer Meetings on Algorithm. Held on 9th of July 2016 at GSSI, L'Aquila, Italy
Dissimilarity-based people re-identification and search for intelligent video...

Slides of my PhD thesis, available at:
http://pralab.diee.unica.it/satta_phdthesis2013
http://pralab.diee.unica.it/en/AmbientIntelligence
Applications of Matrices

The document discusses matrices and their applications. It begins by defining what a matrix is and some basic matrix operations like addition, scalar multiplication, and transpose. It then discusses matrix multiplication and how it can be used to represent systems of linear equations. The document lists several applications of matrices, including representing graphs, transformations in computer graphics, solving systems of linear equations, cryptography, and secret communication methods like steganography. It provides some high-level details about using matrices for secret codes and hiding messages in digital files like images and audio.
SVM

Support Vector Machines (SVMs) are a supervised machine learning method used for classification and regression analysis. SVMs find a hyperplane that separates clusters of data points and maximizes the margin between the clusters. The maximal margin hyperplane is the solution to an optimization problem that maximizes the margin and minimizes a cost function accounting for misclassifications. Kernels can be used to project data into a higher dimensional space to allow for separation of data that is not linearly separable in the original space. SVMs have been applied to problems such as computer-aided diagnosis of Alzheimer's disease from medical images and ranking models.
15857 cse422 unsupervised-learning

This document provides an overview of supervised and unsupervised learning, with a focus on clustering as an unsupervised learning technique. It describes the basic concepts of clustering, including how clustering groups similar data points together without labeled categories. It then covers two main clustering algorithms - k-means, a partitional clustering method, and hierarchical clustering. It discusses aspects like cluster representation, distance functions, strengths and weaknesses of different approaches. The document aims to introduce clustering and compare it with supervised learning.
Exploiting Dissimilarity Representations for Person Re-Identification

The document discusses person re-identification through dissimilarity representations. It proposes representing each person as a vector of dissimilarity values compared to visual prototypes, rather than traditional descriptors. This reduces storage requirements and allows extremely fast matching. The Multiple Component Dissimilarity framework is presented, which defines prototypes, and represents templates and queries as dissimilarity vectors for efficient matching in the dissimilarity space. Preliminary experiments applying this framework to a specific method show improvements in computational time and storage over the original method.
CC282 Unsupervised Learning (Clustering) Lecture 7 slides for ...

This document provides an overview of unsupervised learning techniques, specifically clustering algorithms. It discusses three main approaches to clustering: exclusive clustering using k-means, agglomerative clustering using hierarchical algorithms, and overlapping clustering using fuzzy c-means. It provides examples and explanations of how k-means and hierarchical clustering work, including the steps involved in each algorithm. It also discusses strengths and weaknesses of different clustering methods.
IRJET- Chatbot Using Gated End-to-End Memory Networks

The document describes a proposed chatbot system that uses a gated end-to-end memory network model for hospital appointment booking. The model is trained on dialog data consisting of user utterances and bot responses related to booking appointments. It uses an attention mechanism over the dialog memory to select relevant parts of the conversation. The model is trained end-to-end to dynamically regulate interactions with the memory. Experiments show it can handle new combinations of fields when booking appointments in a simulated hospital reservation scenario.
Convolutional Neural Networks for Sentence Classification

This document discusses convolutional neural networks for sentence classification. It begins with introducing automated text classification and definitions of key concepts like deep learning, language models, neural language models, and convolutional neural networks. It then discusses various datasets used for evaluating models. Several CNN models are described and their results on different datasets are presented, outperforming other methods. The document concludes by showing the most similar words learned by static and non-static CNN channels.
X-TREPAN : A Multi Class Regression and Adapted Extraction of Comprehensible ...

The document describes an algorithm called X-TREPAN that extracts decision trees from trained neural networks. X-TREPAN is an enhancement of the TREPAN algorithm that allows it to handle both multi-class classification and multi-class regression problems. It can also analyze generalized feed forward networks. The algorithm was tested on several real-world datasets and was found to generate decision trees with good classification accuracy while also maintaining comprehensibility.
Image Generation from Caption 

Generating images from a text description is as challenging as it is interesting. The Adversarial network
performs in a competitive fashion where the networks are the rivalry of each other. With the introduction of
Generative Adversarial Network, lots of development is happening in the field of Computer Vision. With
generative adversarial networks as the baseline model, studied Stack GAN consisting of two-stage GANS
step-by-step in this paper that could be easily understood. This paper presents visual comparative study of
other models attempting to generate image conditioned on the text description. One sentence can be related
to many images. And to achieve this multi-modal characteristic, conditioning augmentation is also
performed. The performance of Stack-GAN is better in generating images from captions due to its unique
architecture. As it consists of two GANS instead of one, it first draws a rough sketch and then corrects the
defects yielding a high-resolution image.
Recommendation system

The document discusses recommendation systems and machine learning models for recommendations. It covers the goals of recommendation systems, basic models including collaborative filtering, content-based, and knowledge-based systems. Neighborhood-based collaborative filtering is explained along with matrix factorization models. Deep learning methods for recommendations are also summarized, including neural collaborative filtering, graph-based models, and temporal models that handle dynamic graphs.
Linear Algebra – A Powerful Tool for Data Science

Analysis of data is an important task in data managements systems. Many mathematical tools are used in data analysis. A new division of data management has appeared in machine learning, linear algebra, an optimal tool to analyse and manipulate the data. Data science is a multi-disciplinary subject that uses scientific methods to process the structured and unstructured data to extract the knowledge by applying suitable algorithms and systems. The strength of linear algebra is ignored by the researchers due to the poor understanding. It powers major areas of Data Science including the hot fields of Natural Language Processing and Computer Vision. The data science enthusiasts finding the programming languages for data science are easy to analyze the big data rather than using mathematical tools like linear algebra. Linear algebra is a must-know subject in data science. It will open up possibilities of working and manipulating data. In this paper, some applications of Linear Algebra in Data Science are explained.
Attention Is All You Need

Attention Is All You Need (NIPS 2017)
(Ashish Vaswani, Noam Shazeer, Niki Parmar, Jakob Uszkoreit, Llion Jones, Aidan N. Gomez, Łukasz Kaiser, Illia Polosukhin)
paper link: https://arxiv.org/pdf/1706.03762.pdf
Reference:
https://youtu.be/mxGCEWOxfe8 (by Minsuk Heo)
https://youtu.be/5vcj8kSwBCY (Stanford CS224N: NLP with Deep Learning | Winter 2019 | Lecture 14 – Transformers and Self-Attention)
What's hot (20)
A few approaches to cope with crash/byzantine failures in communication netwo...

A few approaches to cope with crash/byzantine failures in communication netwo...
Dissimilarity-based people re-identification and search for intelligent video...

Dissimilarity-based people re-identification and search for intelligent video...
Exploiting Dissimilarity Representations for Person Re-Identification

Exploiting Dissimilarity Representations for Person Re-Identification
CC282 Unsupervised Learning (Clustering) Lecture 7 slides for ...

CC282 Unsupervised Learning (Clustering) Lecture 7 slides for ...
IRJET- Chatbot Using Gated End-to-End Memory Networks

IRJET- Chatbot Using Gated End-to-End Memory Networks
Convolutional Neural Networks for Sentence Classification

Convolutional Neural Networks for Sentence Classification
X-TREPAN : A Multi Class Regression and Adapted Extraction of Comprehensible ...

X-TREPAN : A Multi Class Regression and Adapted Extraction of Comprehensible ...
Viewers also liked
COBUS KRUGER CV

The candidate has over 30 years of experience in both electrical and mechanical fields, including extensive managerial experience. He holds qualifications in electrical work and has knowledge of mechanical products and theory. As an electrical foreman and area sales manager, he gained experience in project management, time management, and business skills. More recently, he owned his own bearing and transmission business for 10 years. He is a strong leader with excellent communication and problem-solving abilities who is looking for a new opportunity to contribute his skills.
Ml0017 mall management

This document provides sample questions and answers for a Master of Business Administration course on Mall Management. It includes questions and multi-paragraph answers on topics like economic factors that affect commercial real estate, types of psychographic segmentation, concepts of "build to sell" and "build to rent" business models, the 10 steps of hazardous material management, factors that influence mall maintenance, and the 5 stages of emergency response in a mall according to FEMA.
360 Degrees of Digital Engagement

The document discusses digital engagement and customer lifecycles. It explains that successful engagement requires understanding customers at different stages (leads, buyers, defecting) and treating them appropriately. Predictive technologies can help close the gap between a "1-to-1 dream" of personalized engagement and reality. The document provides examples of how product recommendations on websites, in emails and on other pages can significantly increase customer engagement and revenue. A case study shows how personalized recommendations increased click-through rates and conversions for a restaurant review site. The key takeaways are that digital engagement requires understanding customer stages and communicating across channels in a personalized way using predictive technologies.
Mf0016 treasury management

This document provides information about getting fully solved assignments for the MBA semester 4 course MF 0016 – Treasury Management. It includes 6 questions related to treasury functions, commodity markets, risk management, interest rate risk, the relationship between treasury and asset-liability management (ALM), and how ALM contributes to balance sheet management risks. Students are instructed to answer all questions, with 10-mark questions being approximately 400 words each. Contact information is provided to send assignment details or call for assistance.
TDD Projeto e Estrategias

O documento discute estratégias e princípios para desenvolvimento baseado em testes, como separação de preocupações, níveis de abstração, encapsulamento, tipos de vizinhança entre objetos e uso de testes dublês.
R2 creative portfólio_02

O documento apresenta um portfólio de projetos de uma empresa de design gráfico localizada em Pernambuco. O portfólio inclui exemplos de trabalhos realizados para clientes em diferentes áreas com foco em design e criação visual. O endereço eletrônico da empresa é fornecido para que interessados possam entrar em contato.
Viewers also liked (7)
Similar to Mca2020 advanced data structure
Bsc it winter 2013 2nd sem

Dear students get fully solved assignments
Send your semester & Specialization name to our mail id :
help.mbaassignments@gmail.com
or
call us at : 08263069601
Mca1040 system analysis and design

Dear students get fully solved assignments
Send your semester & Specialization name to our mail id :
“ help.mbaassignments@gmail.com ”
or
Call us at : 08263069601
Mit102 data & file structures

Dear students get fully solved assignments
Send your semester & Specialization name to our mail id :
“ help.mbaassignments@gmail.com ”
or
Call us at : 08263069601
Mi0034 database management system

Dear students get fully solved assignments by professionals
Send your semester & Specialization name to our mail id :
stuffstudy5@gmail.com
or
call us at : 098153-33456
Mit103 object oriented programming

This document provides information about getting fully solved assignments by emailing or calling a provided contact. It includes an assignment for the subject Master of Science in Information Technology (MSc IT) Semester 1 course OBJECT ORIENTED PROGRAMMING. The assignment contains 6 questions asking about topics like multi-threading, Java bytecode, break and continue statements, packages vs interfaces, applets, JDBC vs ODBC, and Java Beans. It provides the evaluation scheme and asks students to answer all questions, with longer answers of approximately 400 words for 10 mark questions.
Mi0035 computer networks

This document provides information about an assignment for a computer networks course. It includes 6 questions to answer about computer networks concepts like types of networks, OSI reference model, subnets, dynamic NAT, DNS, CSMA/CD protocol, and network management functions. Students are asked to answer each question in 300-400 words and submit their responses to the provided email or phone number to receive solved assignments at a nominal price of Rs. 125 each.
Bca winter 2013 2nd sem

The document provides information about fully solved assignments for the winter 2013 semester in the BCA program. It lists the subject code and name as BCA2030 - Object Oriented Programming - C++. It provides 6 questions related to the subject and asks students to send their semester and specialization details to the provided email ID or call the given phone number to get the solved assignments. It provides answers to the 6 questions related to topics like objects and classes, friend functions, constructors vs destructors, operator overloading, virtual functions and polymorphism, and exception handling models.
The summary highlights that the document discusses getting fully solved winter 2013 semester assignments for the BCA program's subject on Object Oriented Programming - C
Mit202 data base management system(dbms)

Dear students get fully solved assignments
Send your semester & Specialization name to our mail id :
“ help.mbaassignments@gmail.com ”
or
Call us at : 08263069601
Mi0034 – database management system

Dear students get fully solved assignments
Send your semester & Specialization name to our mail id :
help.mbaassignments@gmail.com
or
call us at : 08263069601
Fashion AI

This document summarizes a research paper on Fashion AI. It proposes a new Group Decreasing Network (GroupDNet) that uses group convolutions in the generator and gradually reduces the percentage of groups in the decoder's convolutions. This allows the model to have more control over generating images from semantic labels and produce high-quality, multi-modal outputs. The paper describes GroupDNet's architecture, compares it to other approaches like using multiple generators, and shows it outperforms other methods on challenging datasets based on metrics like FID and mIoU. Potential applications discussed include mixed fashion styles, semantic manipulation, and tracking fashion trends over time. The conclusion discusses GroupDNet's performance but notes room for improving computational efficiency
Mi0034 database management system

Dear students get fully solved assignments
Send your semester & Specialization name to our mail id :
“ help.mbaassignments@gmail.com ”
or
Call us at : 08263069601
Mapping objects to_relational_databases

The document discusses various strategies for mapping object-oriented classes and relationships to relational databases. It describes mapping class attributes to database columns, implementing inheritance through single-table or multiple-table approaches, and mapping relationships like associations through foreign keys or associative tables. The strategies each have advantages and disadvantages related to ease of implementation, data access speed, coupling between classes, and support for polymorphism. There is no single best approach, and the optimal strategy depends on the specific application.
IRJET- Visual Question Answering using Combination of LSTM and CNN: A Survey

This document discusses using a combination of long short-term memory (LSTM) and convolutional neural networks (CNN) for visual question answering (VQA). It proposes extracting image features from CNNs and encoding question semantics with LSTMs. A multilayer perceptron would then combine the image and question representations to predict answers. The methodology aims to reduce statistical biases in VQA datasets by focusing attention on relevant image regions. It was implemented in Keras with TensorFlow using pre-trained CNNs for images and word embeddings for questions. The proposed approach analyzes local image features and question semantics to improve VQA classification accuracy over methods relying solely on language.
Bt0066 dbms

Dear students get fully solved assignments
Send your semester & Specialization name to our mail id :
“ help.mbaassignments@gmail.com ”
or
Call us at : 08263069601
Mi0034 – database management system

Dear students get fully solved assignments
Send your semester & Specialization name to our mail id :
help.mbaassignments@gmail.com
or
call us at : 08263069601
Mi0034 database management system

This document provides details of an assignment for a Database Management Systems course. It includes 6 questions to answer about key DBMS concepts like the definition of a database, relational algebra operations, the client-server model, SQL, locking protocols, and object-oriented data models. Students are instructed to answer each question in 300-400 words and submit their responses to the provided email or phone number for grading.
Mit4021–%20 c# and .net

Dear students get fully solved assignments
Send your semester & Specialization name to our mail id :
“ help.mbaassignments@gmail.com ”
or
Call us at : 08263069601
(Prefer mailing. Call in emergency )
Bca3020 database management system

Dear students get fully solved assignments
Send your semester & Specialization name to our mail id :
“ help.mbaassignments@gmail.com ”
or
Call us at : 08263069601
dbms final.pdf

This document contains questions and answers related to database management systems (DBMS). It begins by defining DBMS and listing some of its key functions like data definition, data manipulation, data security and integrity, etc. It then discusses SQL statements, data independence, entity relationship diagrams, and database concepts like attributes, hashing, keys, projections, transactions, ACID properties, and starvation. The document also includes questions about database administrators (DBAs), schema architectures, data types, and PL/SQL.
Mca winter 2013 2nd sem

Dear students get fully solved assignments
Send your semester & Specialization name to our mail id :
help.mbaassignments@gmail.com
or
call us at : 08263069601
Similar to Mca2020 advanced data structure (20)
IRJET- Visual Question Answering using Combination of LSTM and CNN: A Survey

IRJET- Visual Question Answering using Combination of LSTM and CNN: A Survey
Mca2020 advanced data structure
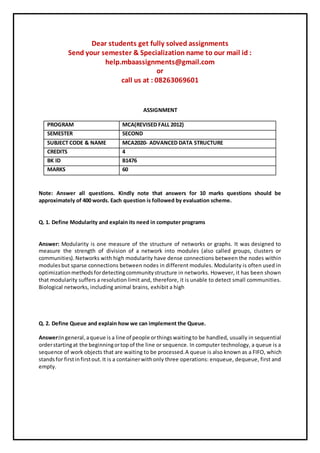
- 1. Dear students get fully solved assignments Send your semester & Specialization name to our mail id : help.mbaassignments@gmail.com or call us at : 08263069601 ASSIGNMENT PROGRAM MCA(REVISED FALL 2012) SEMESTER SECOND SUBJECT CODE & NAME MCA2020- ADVANCED DATA STRUCTURE CREDITS 4 BK ID B1476 MARKS 60 Note: Answer all questions. Kindly note that answers for 10 marks questions should be approximately of 400 words. Each question is followed by evaluation scheme. Q. 1. Define Modularity and explain its need in computer programs Answer: Modularity is one measure of the structure of networks or graphs. It was designed to measure the strength of division of a network into modules (also called groups, clusters or communities).Networks with high modularity have dense connections between the nodes within modulesbut sparse connections between nodes in different modules. Modularity is often used in optimizationmethodsfordetectingcommunitystructure in networks. However, it has been shown that modularity suffers a resolution limit and, therefore, it is unable to detect small communities. Biological networks, including animal brains, exhibit a high Q. 2. Define Queue and explain how we can implement the Queue. Answer:Ingeneral,aqueue is a line of people orthingswaitingto be handled, usually in sequential orderstartingat the beginningortopof the line or sequence. In computer technology, a queue is a sequence of work objects that are waiting to be processed.A queue is also known as a FIFO, which standsfor firstinfirstout.It is a containerwithonly three operations: enqueue, dequeue, first and empty.
- 2. Q. 3. List the Advantages and Disadvantages of Linear and linked representation of tree. Answer:Binarytree traversal is definedasa processof visiting all the nodes in the binary tree once. The visit always starts from the root node. Q. 4. List and explain any Five types of graph. Answer:Graphsare picture representativesfor1or more setsof informationandhow these visually relate to one another. There are many types of charts and graphs of varied complexity. For almost any numerical dataset,there isa graph type thatis appropriate forrepresenting it. Graphs help you present data in a meaningful way. It is one thing to see a data listed on a page and it’s another to actuallyunderstandthe detailsandtrends of the data. A lot of the time, sets of data involve values in the millions or billions. This is far too many to print out in a magazine or journal article. Using a graph can help depict data and a well-made graph Q. 5. Explain 1. Fixed block storage allocation. Answer:Fixed-size blocksallocation,alsocalledmemorypool allocation,usesa free list of fixed-size blocksof memory(oftenall of the same size).Thisworkswell for simple embedded systems where no large objectsneedtobe allocated,butsuffersfromfragmentation, especially with long memory addresses. However, due to the significantly reduced overhead this method can substantially improve performance forobjectsthatneed frequent allocation / de-allocation and is often used in video games. 2. Variable block storage allocation Answer:In computer programming, an automatic variable is a local variable which is allocated and deallocatedautomatically when program flow enters and leaves the variable's scope. The scope is the lexical context, particularly the function or block in which a variable is defined. Local data is typically(inmostlanguages)invisibleoutside the functionorlexical contextwhere itisdefined.Local data is also The term local variable is usually synonymous with automatic variable, since these are the same thinginmany programminglanguages,butlocal ismore general –mostlocal variablesare automatic local variables, but static local variables also exist, notably in C. For a static local variable, the allocation is static (the lifetime is the entire program execution), not automatic, but it is only in scope during the execution of the function.
- 3. Q. 6. What is the use of external Storage Devices? Explain any two external storage devices Answer:In computing, external storage comprises devices that temporarily store information for transportingfromcomputertocomputer.Suchdevicesare notpermanentlyfixedinsideacomputer. Semiconductor memories are not sufficient to provide the whole storage capacity required in computers.The major limitation in using semiconductor memories is the cost per bit of the stored information.Sotofulfill the large storage requirements of computers, magnetic disks, optical disks are generally used. Dear students get fully solved assignments Send your semester & Specialization name to our mail id : help.mbaassignments@gmail.com or call us at : 08263069601
