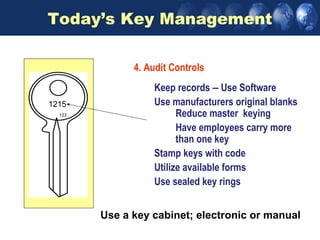
This document provides an overview of access control systems. It discusses key aspects such as defining who is requesting access, where they are requesting access to, and when access is allowed. It also covers credential technologies like smart cards and biometrics. Proper key and credential management is emphasized as the most basic way to control physical access. Standards like HSPD-12 aim to increase security by establishing government-wide identification protocols.