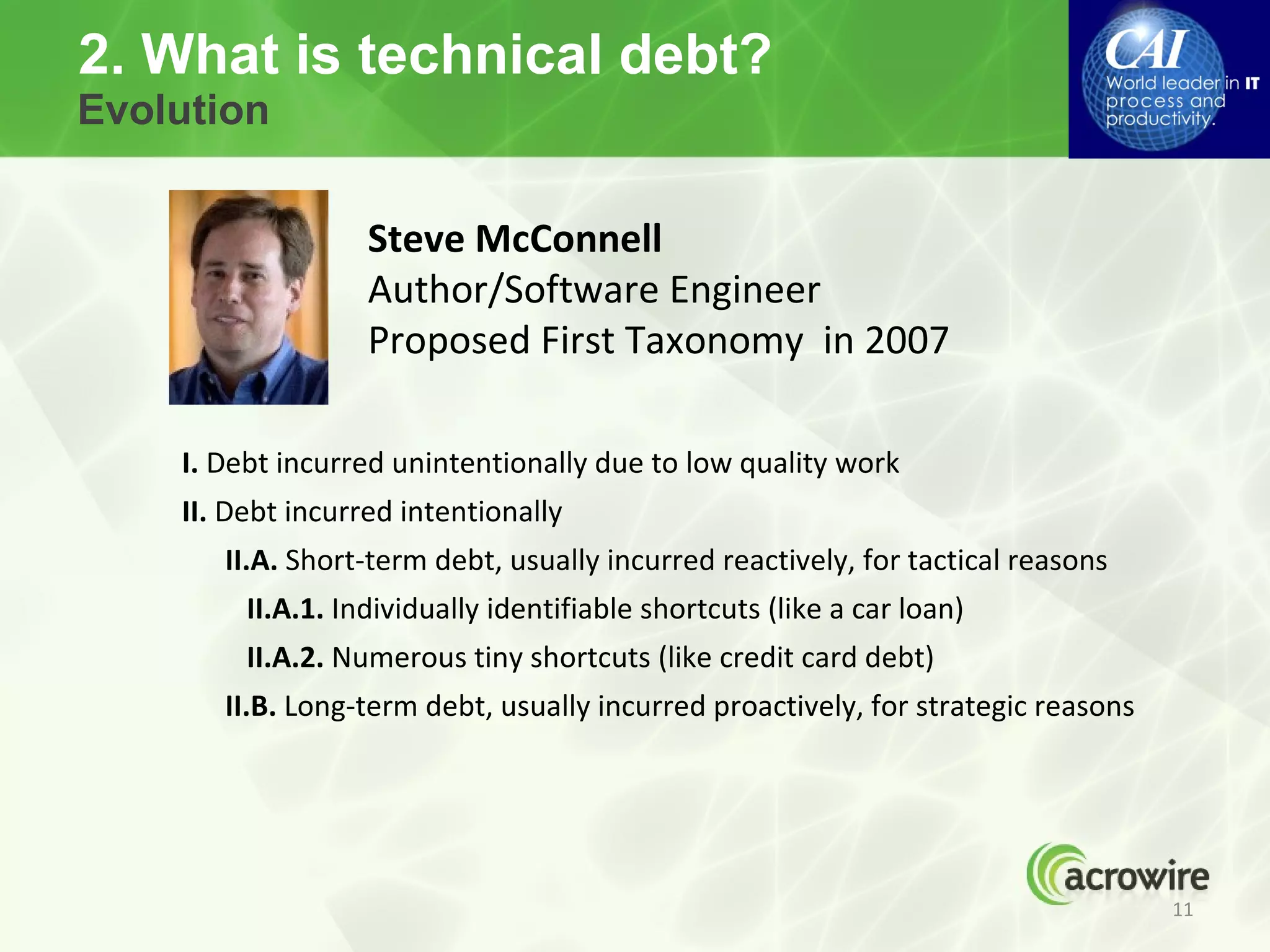
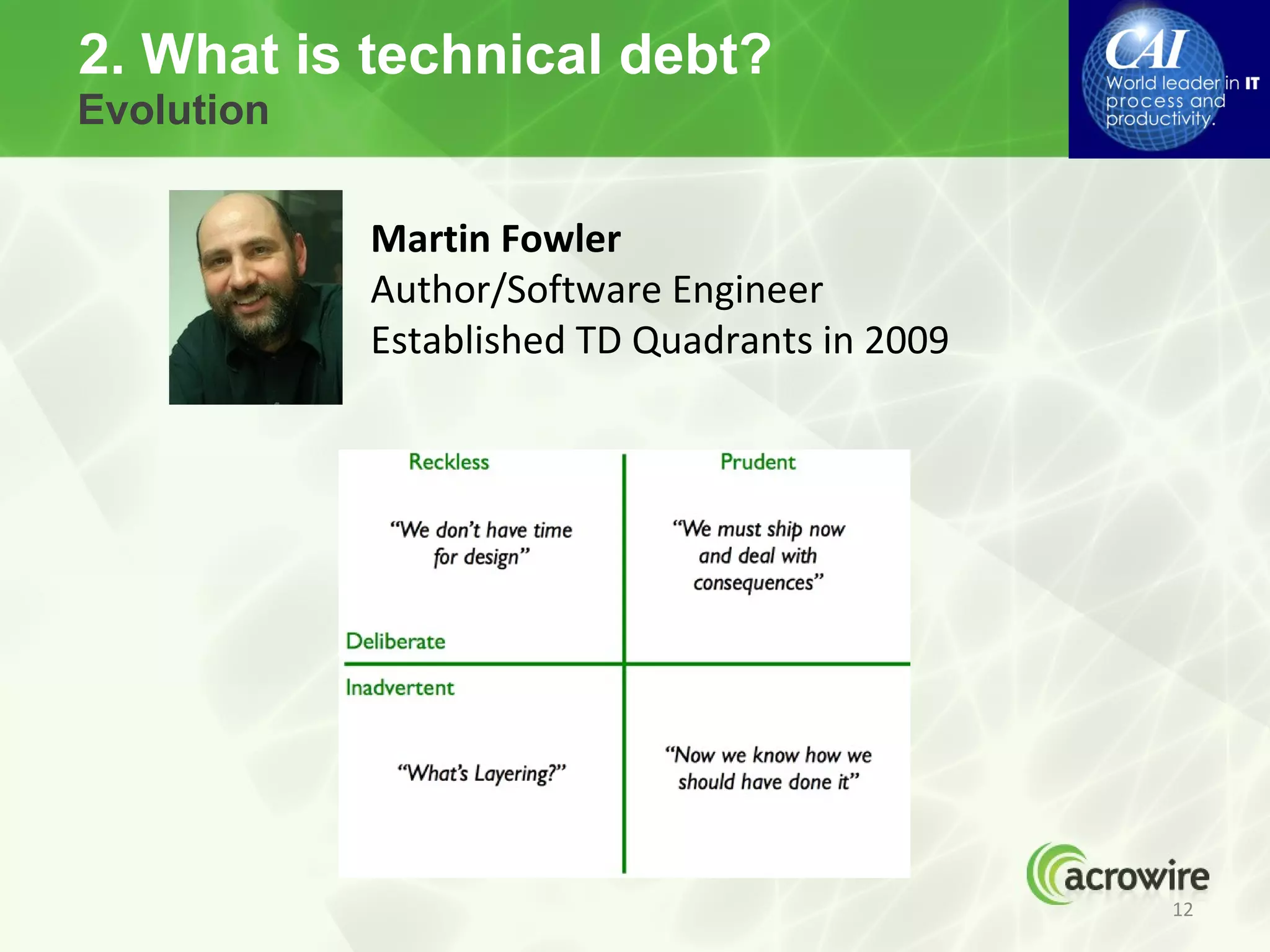
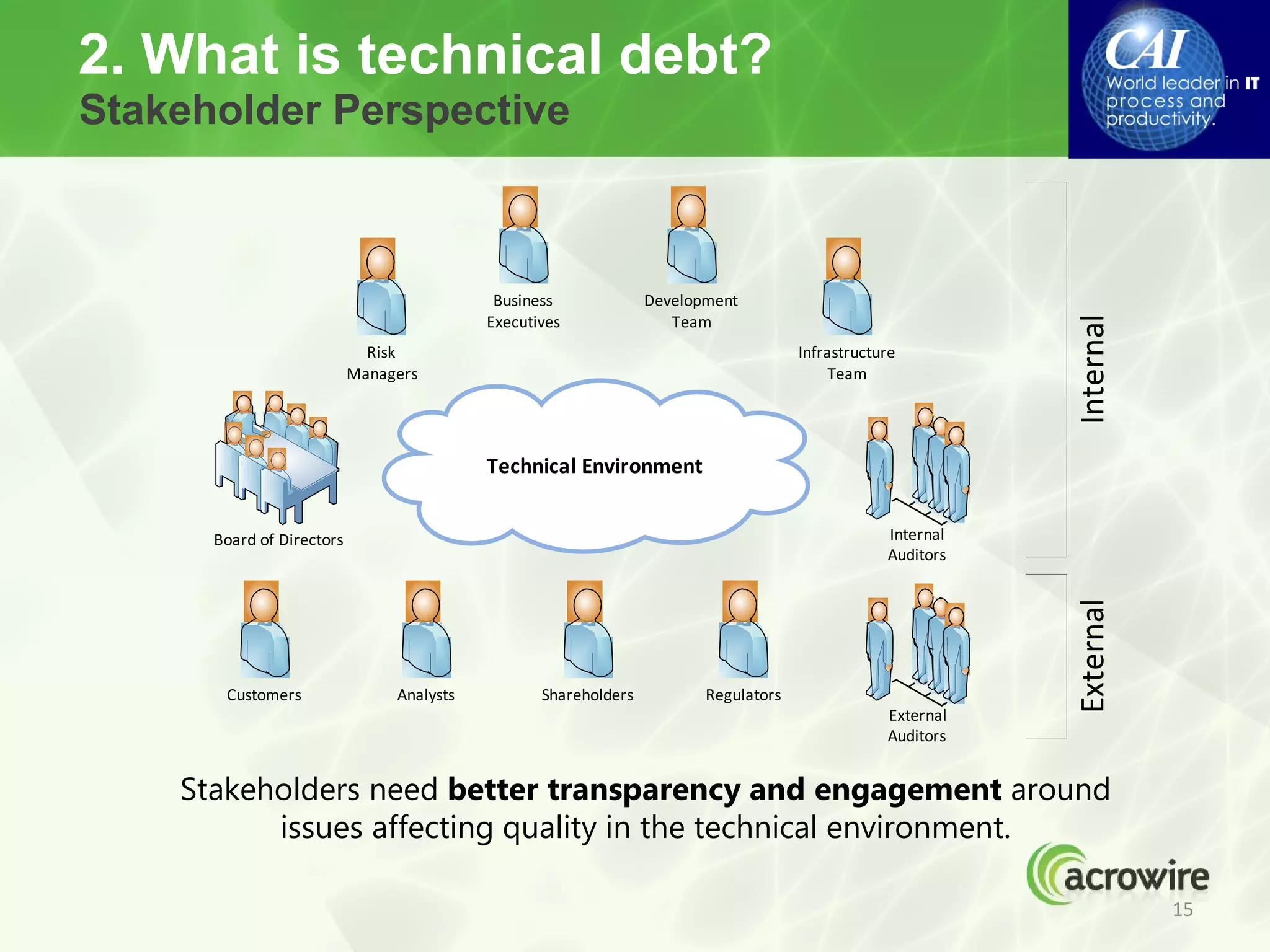
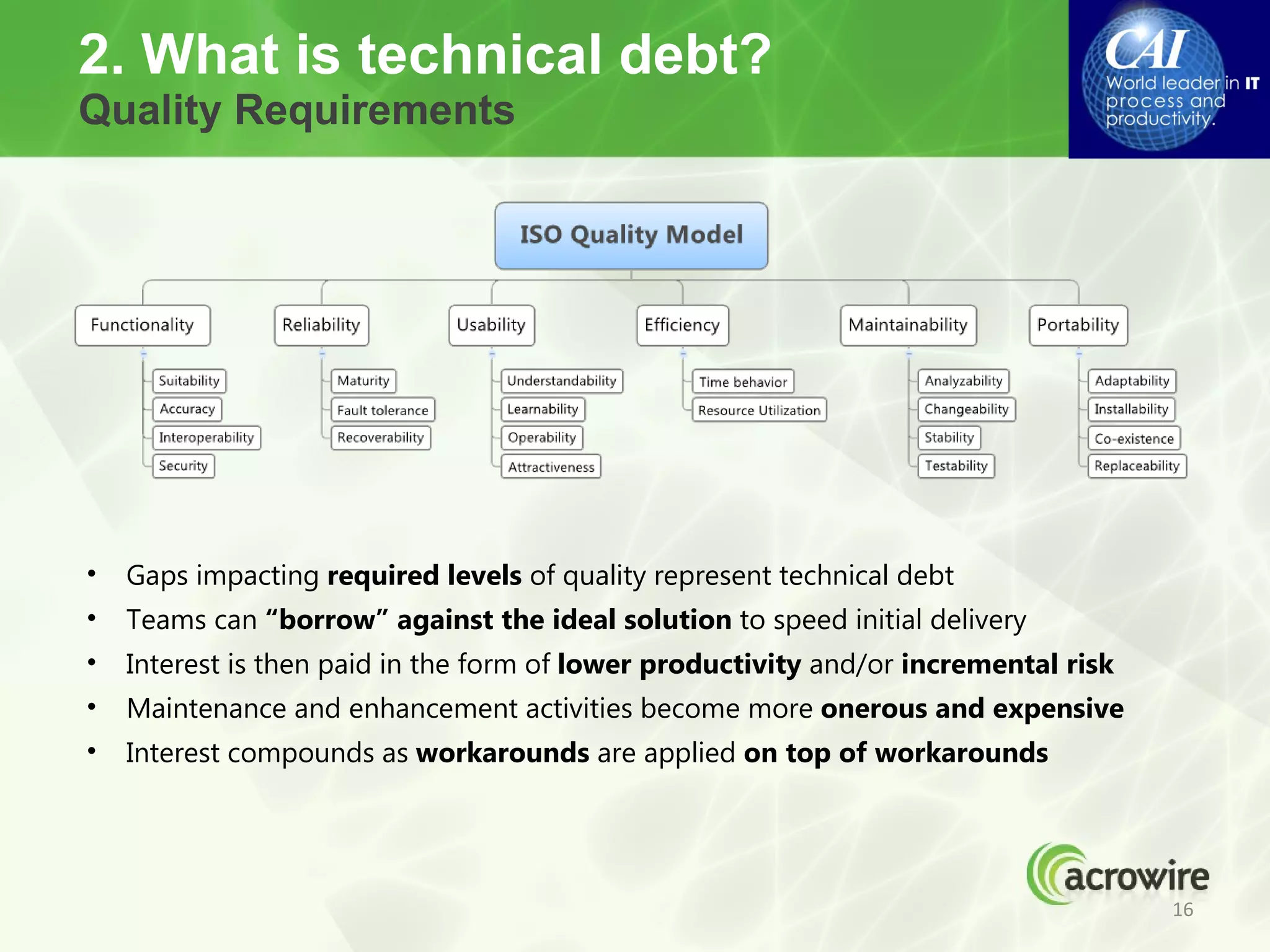
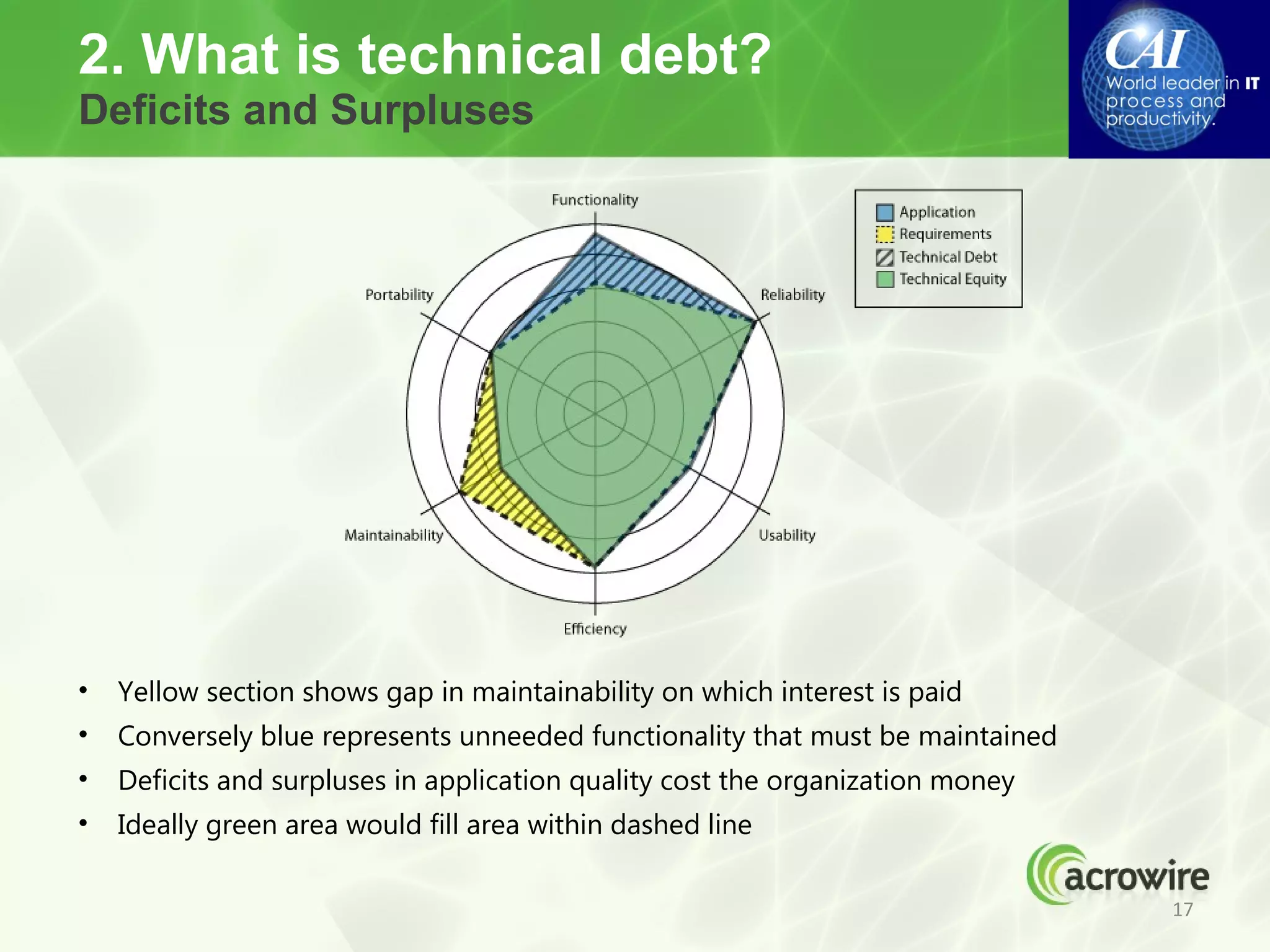
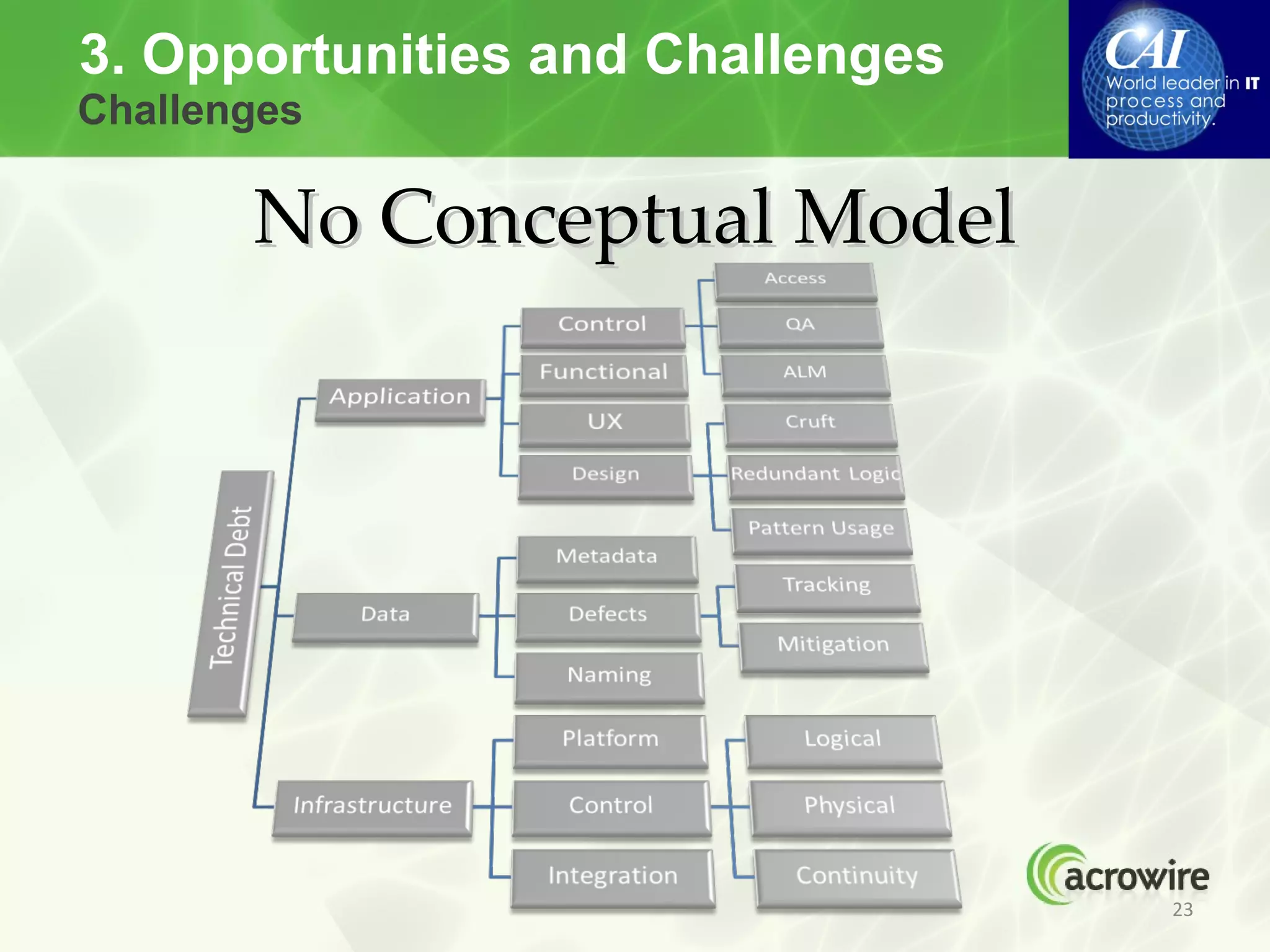
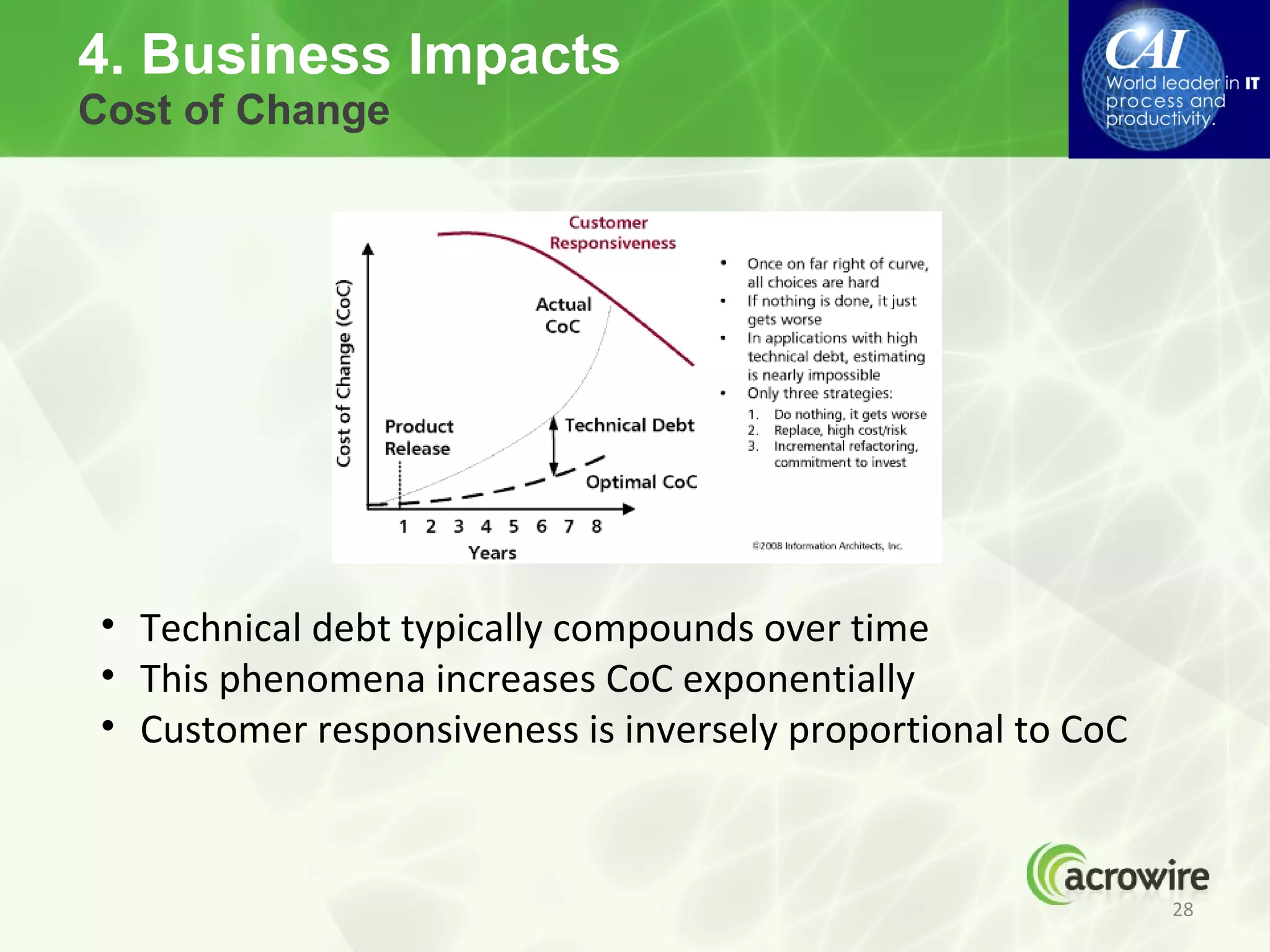
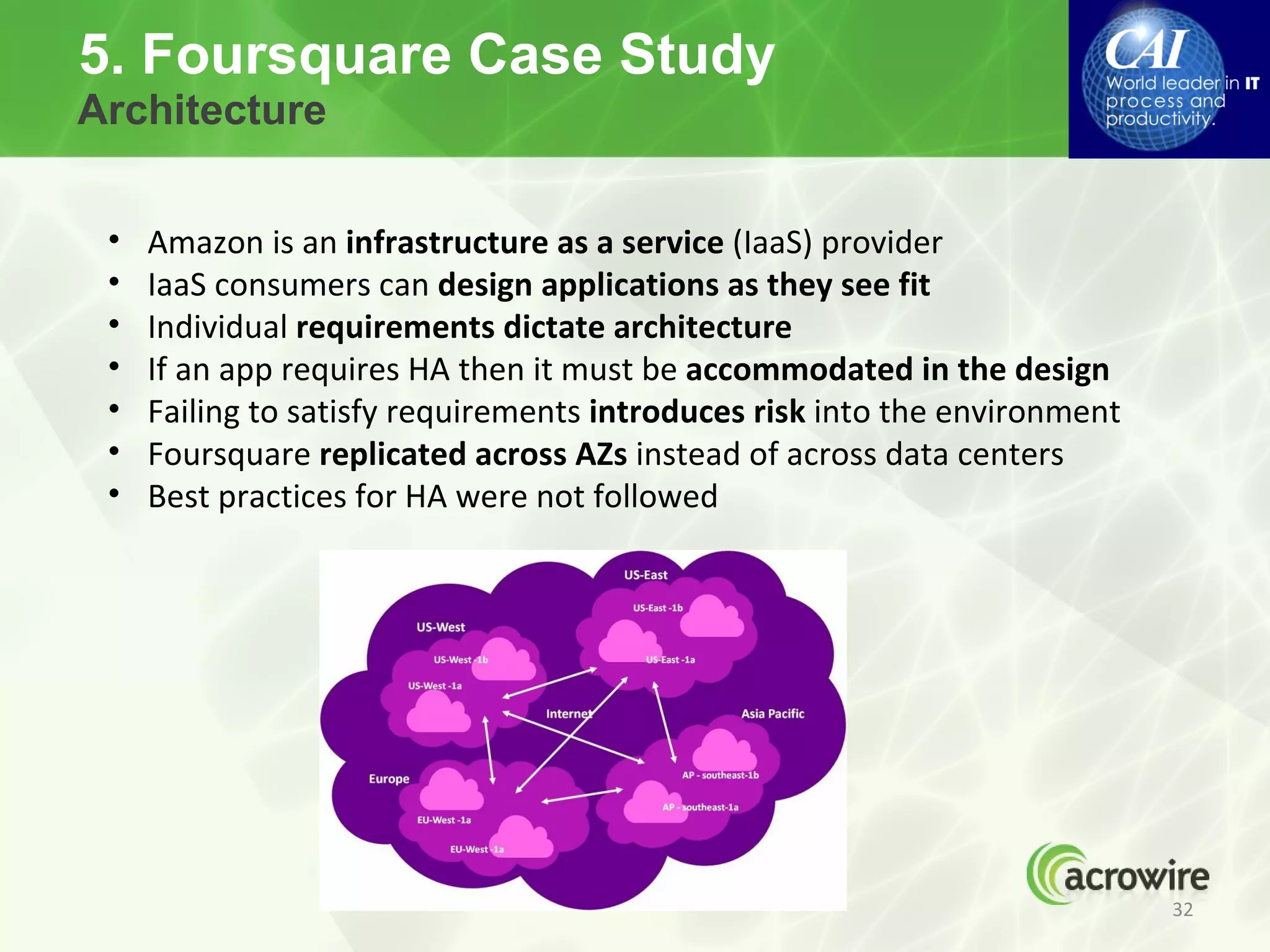
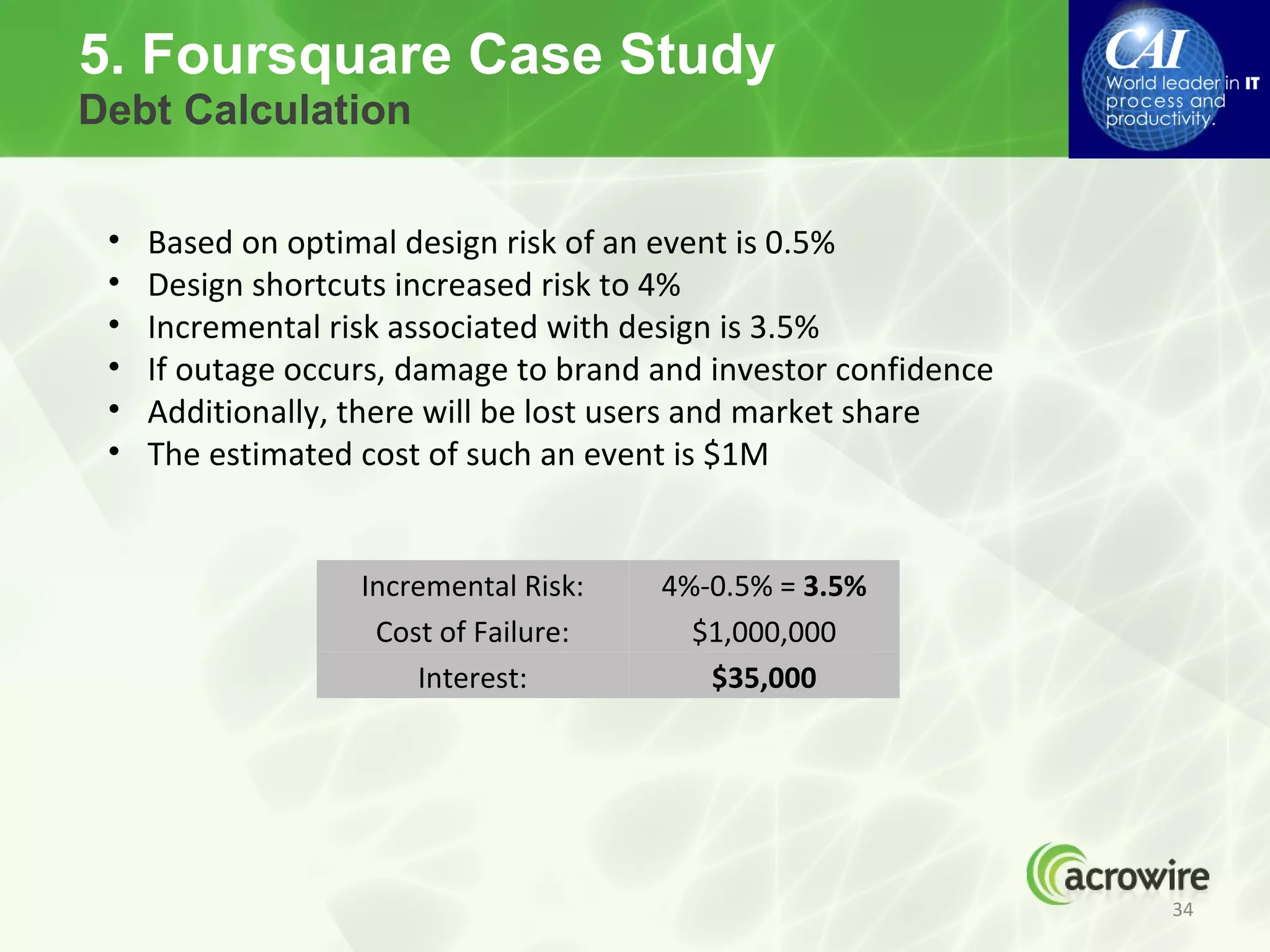
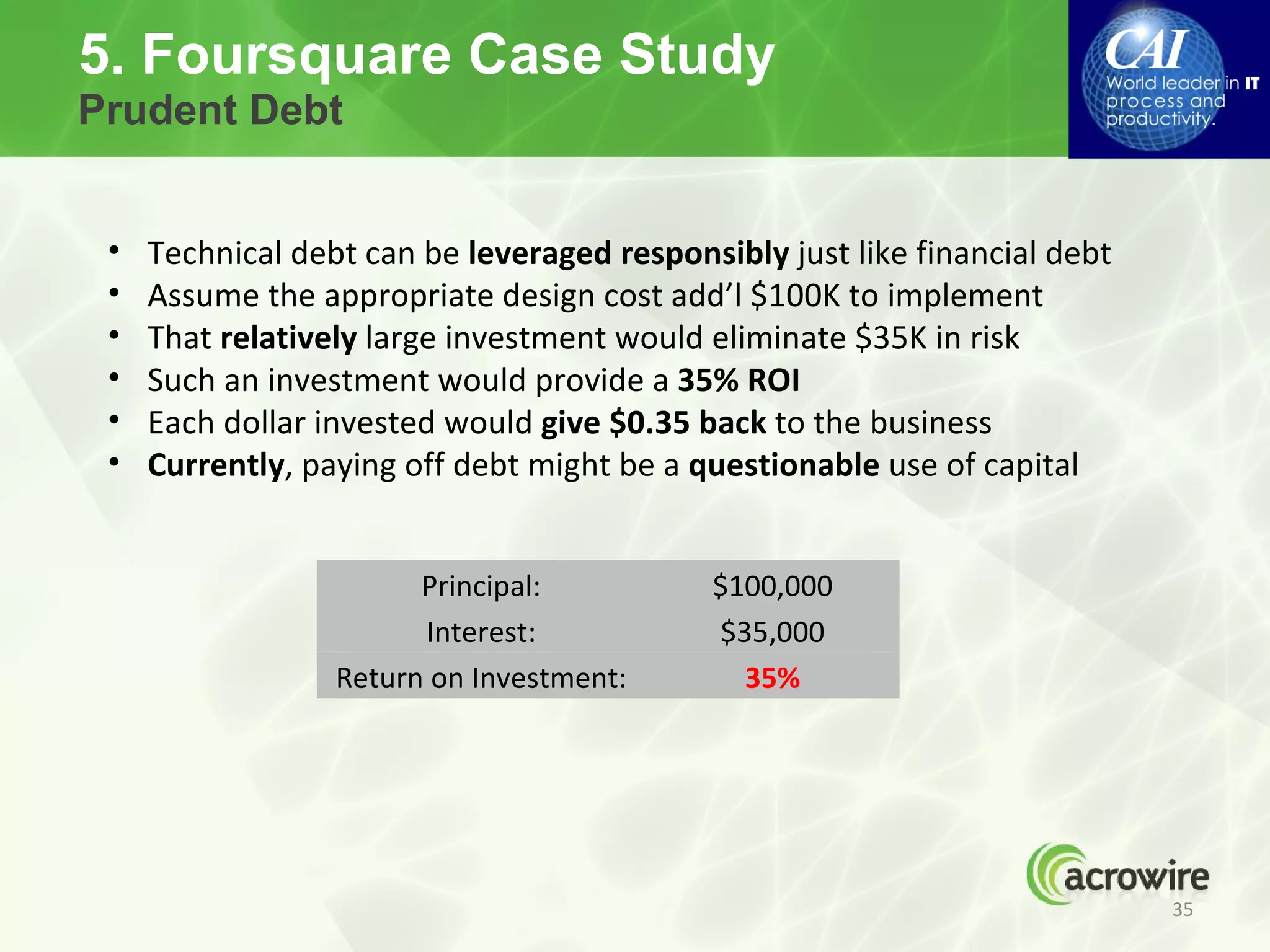
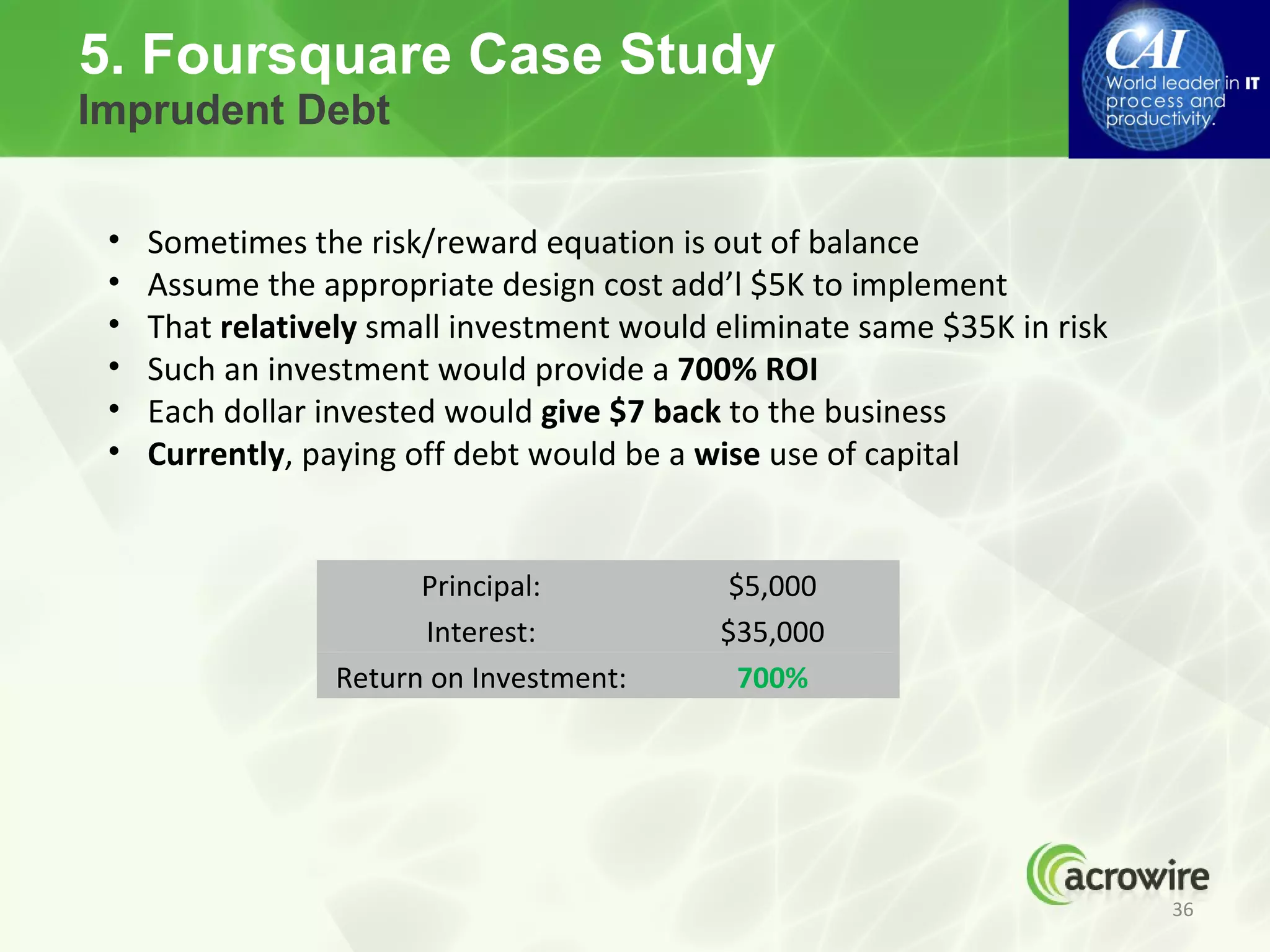
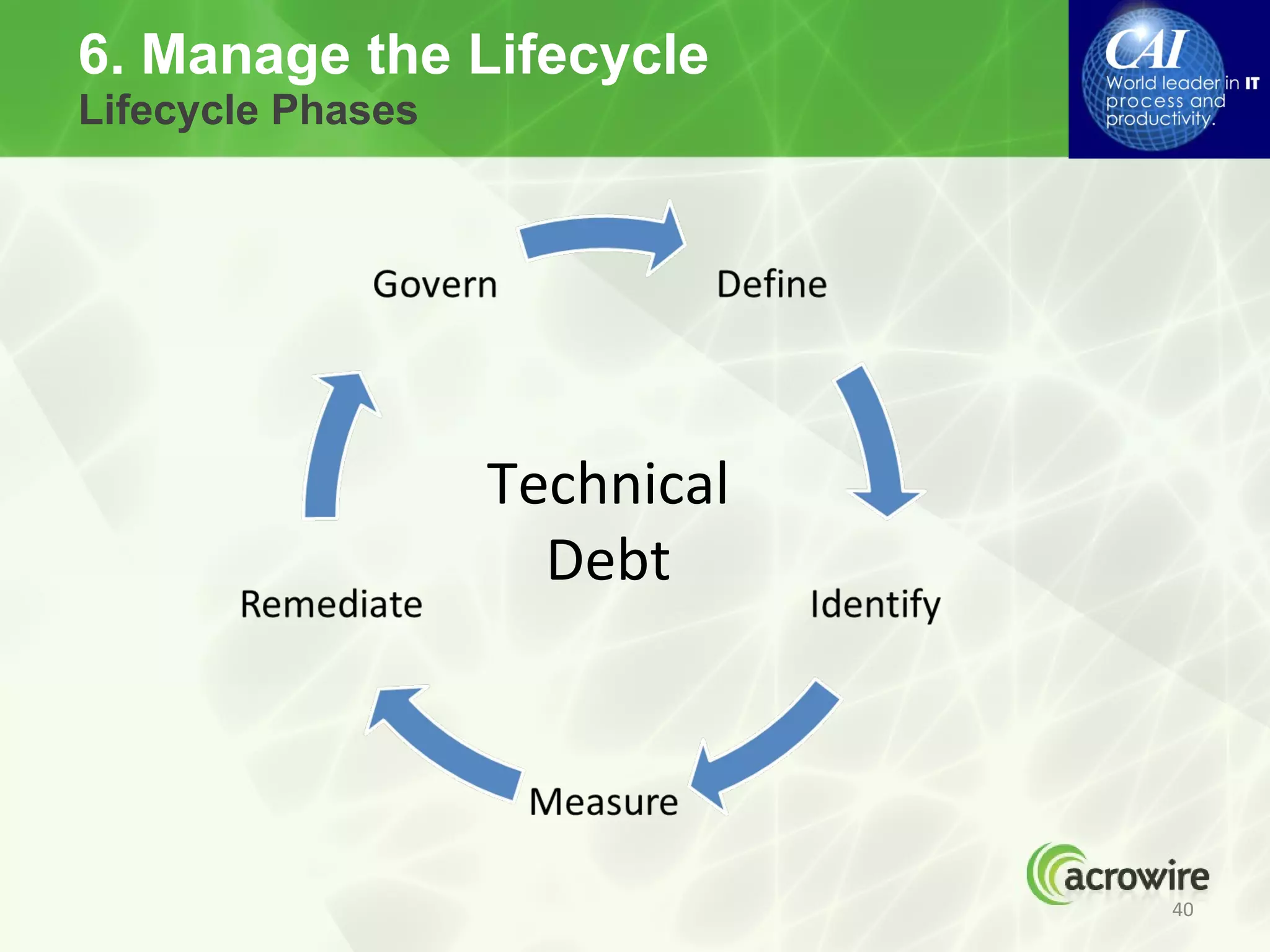
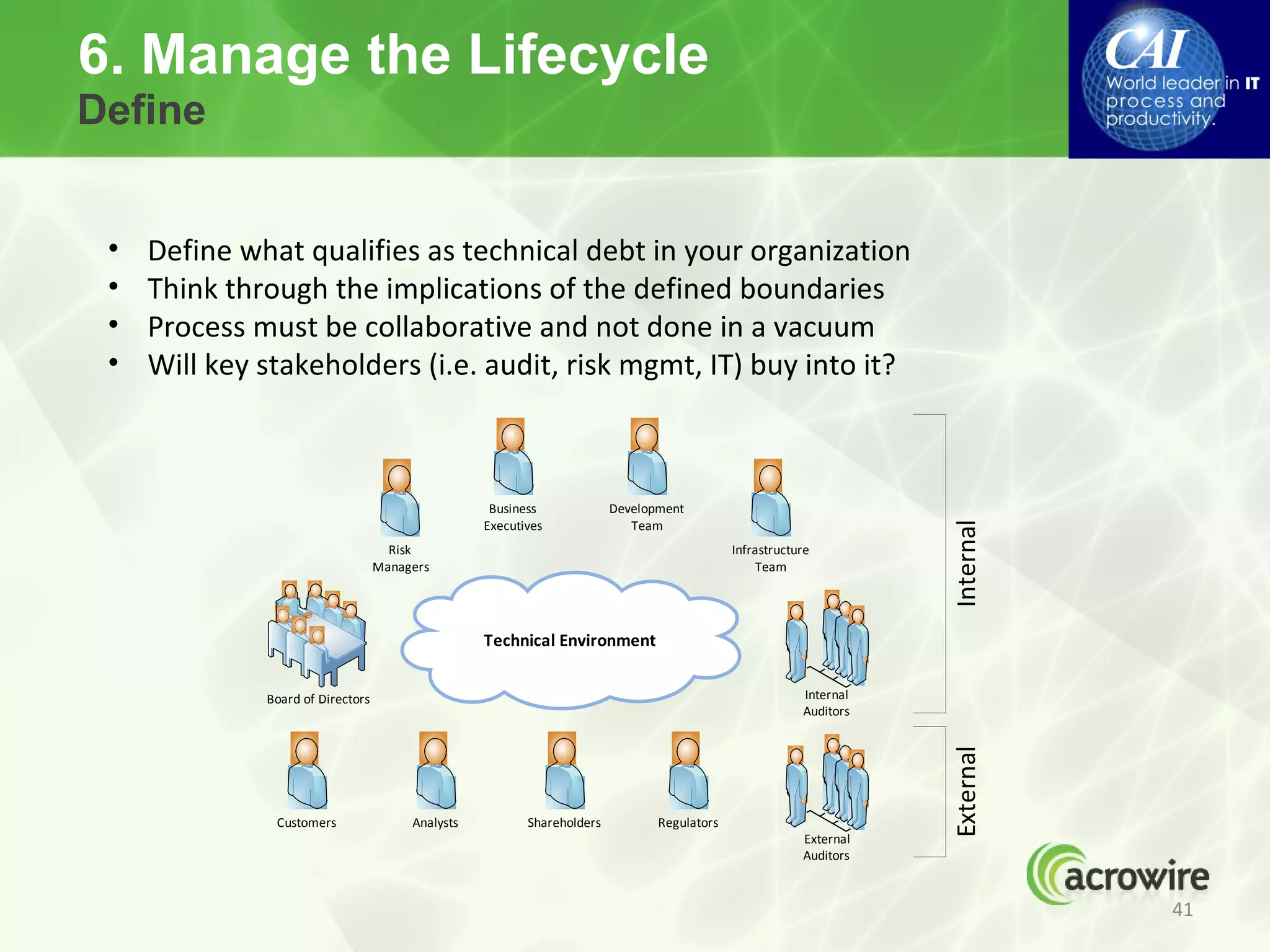
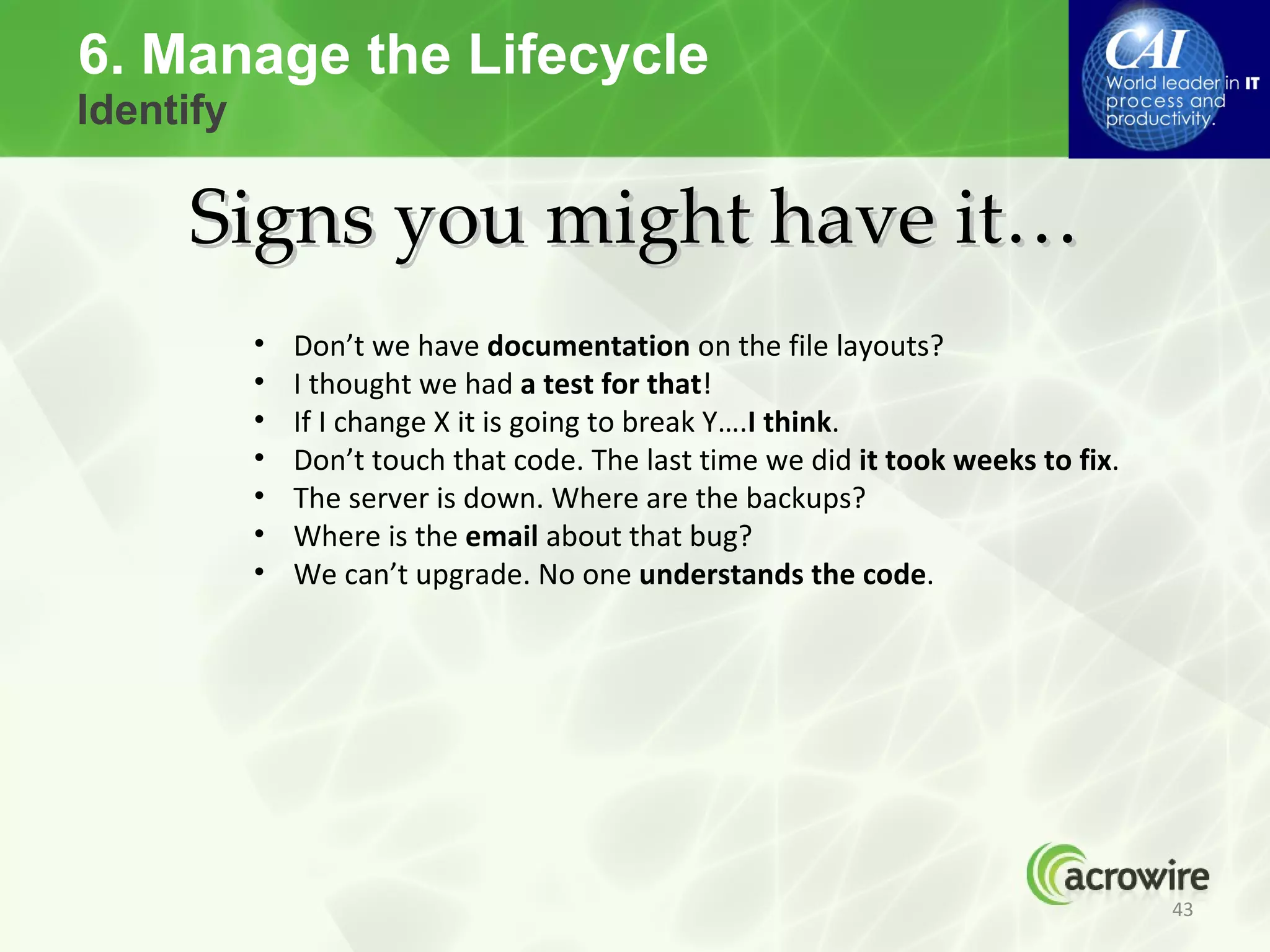
The webinar discusses managing technical debt, defining it as internal issues deferred that can hinder future development, with various perspectives presented from experts. Key concepts include the implications of technical debt, opportunities for managing it, potential business impacts, and a case study of Foursquare's architecture decisions leading to technical debt. The session emphasizes the importance of recognizing and addressing technical debt proactively to maintain system quality and support business growth.