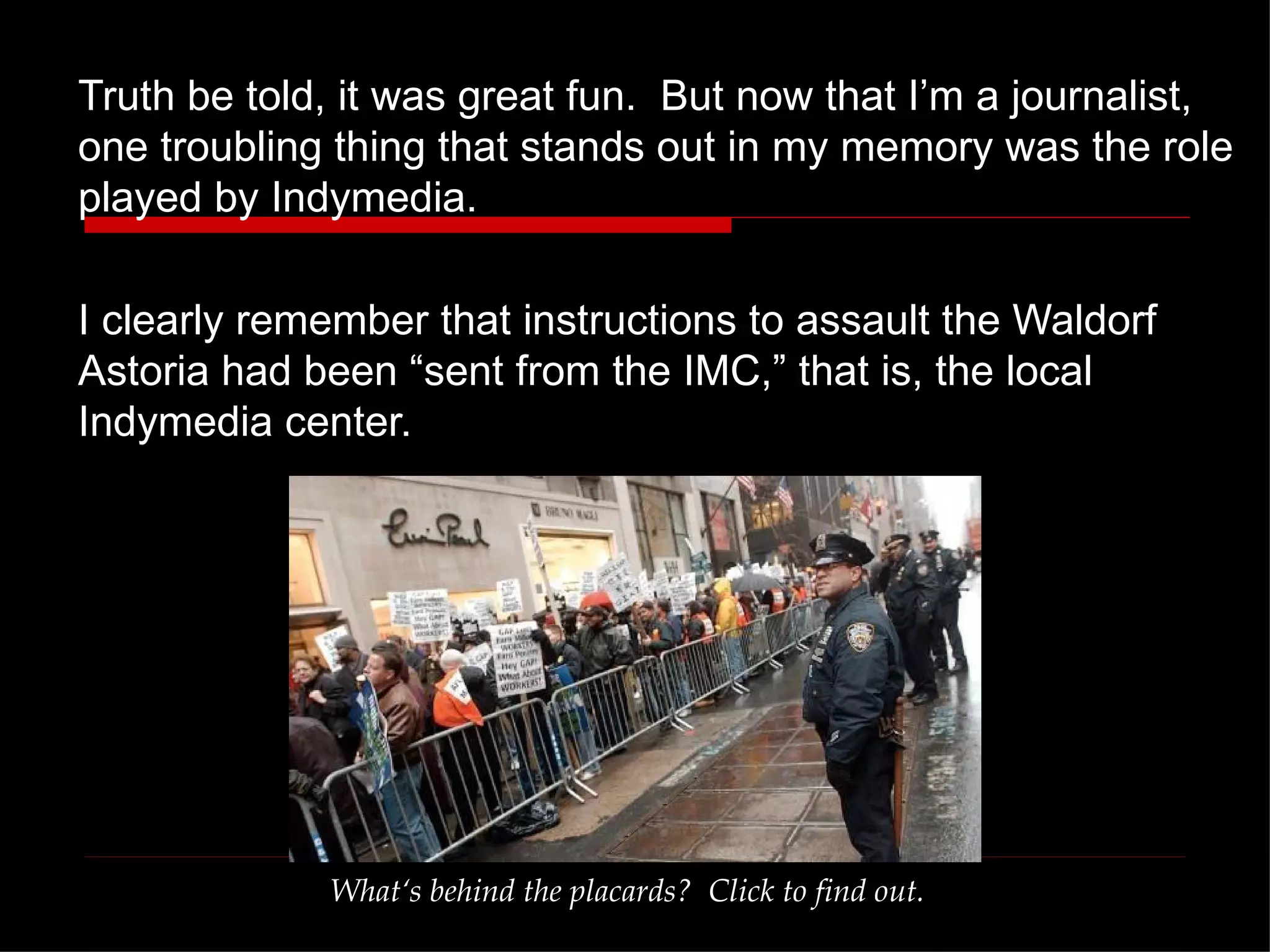
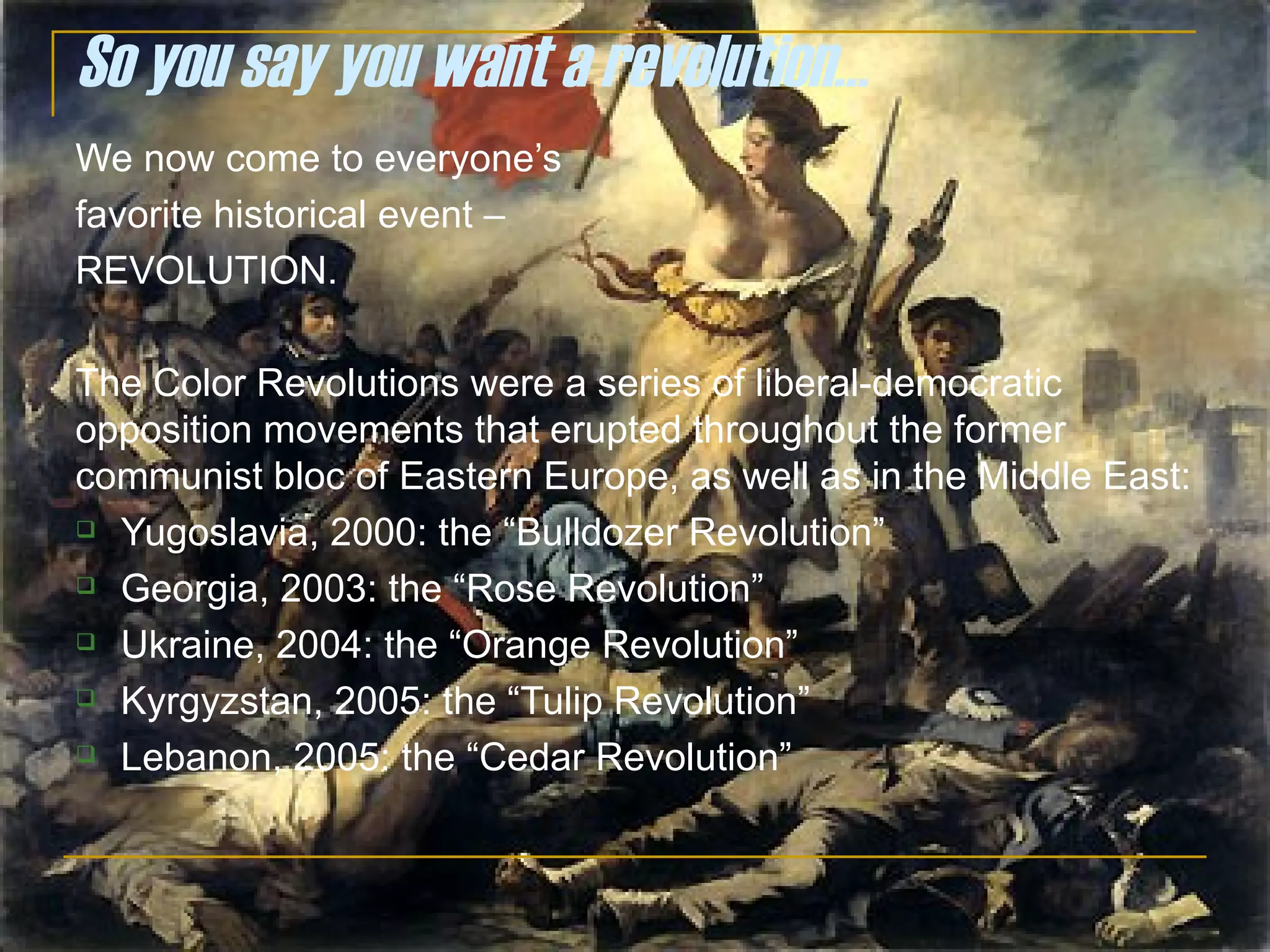
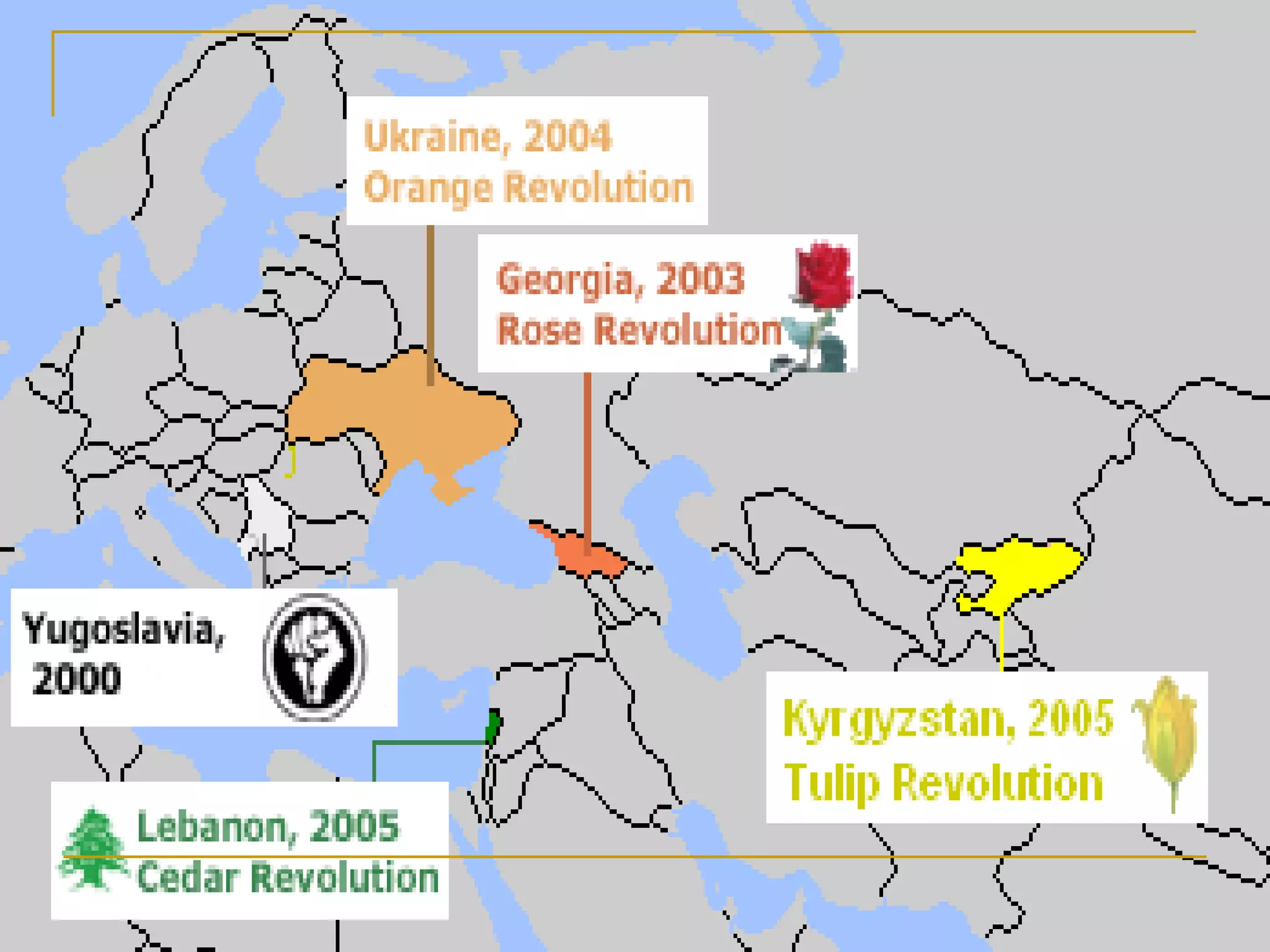
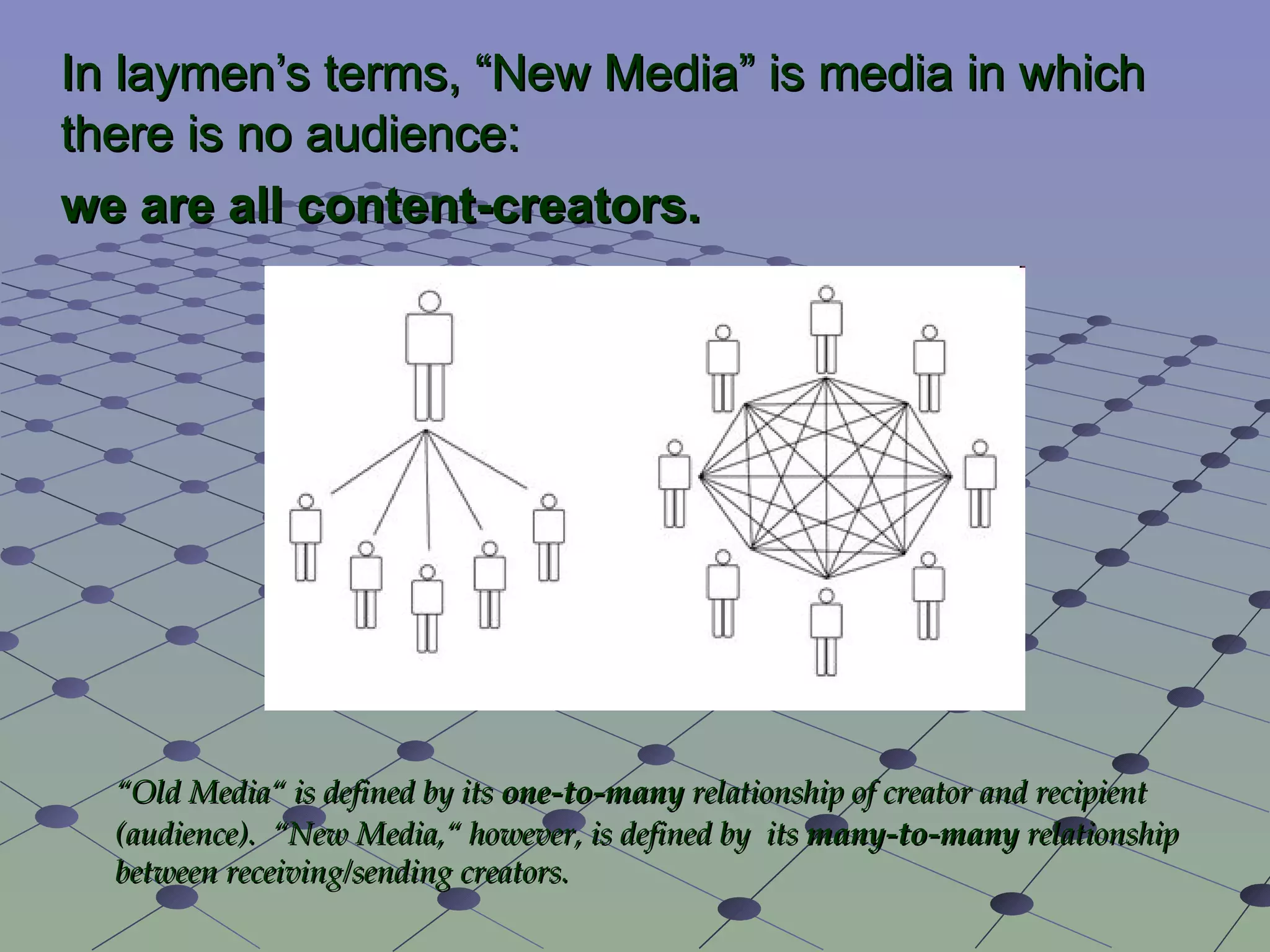
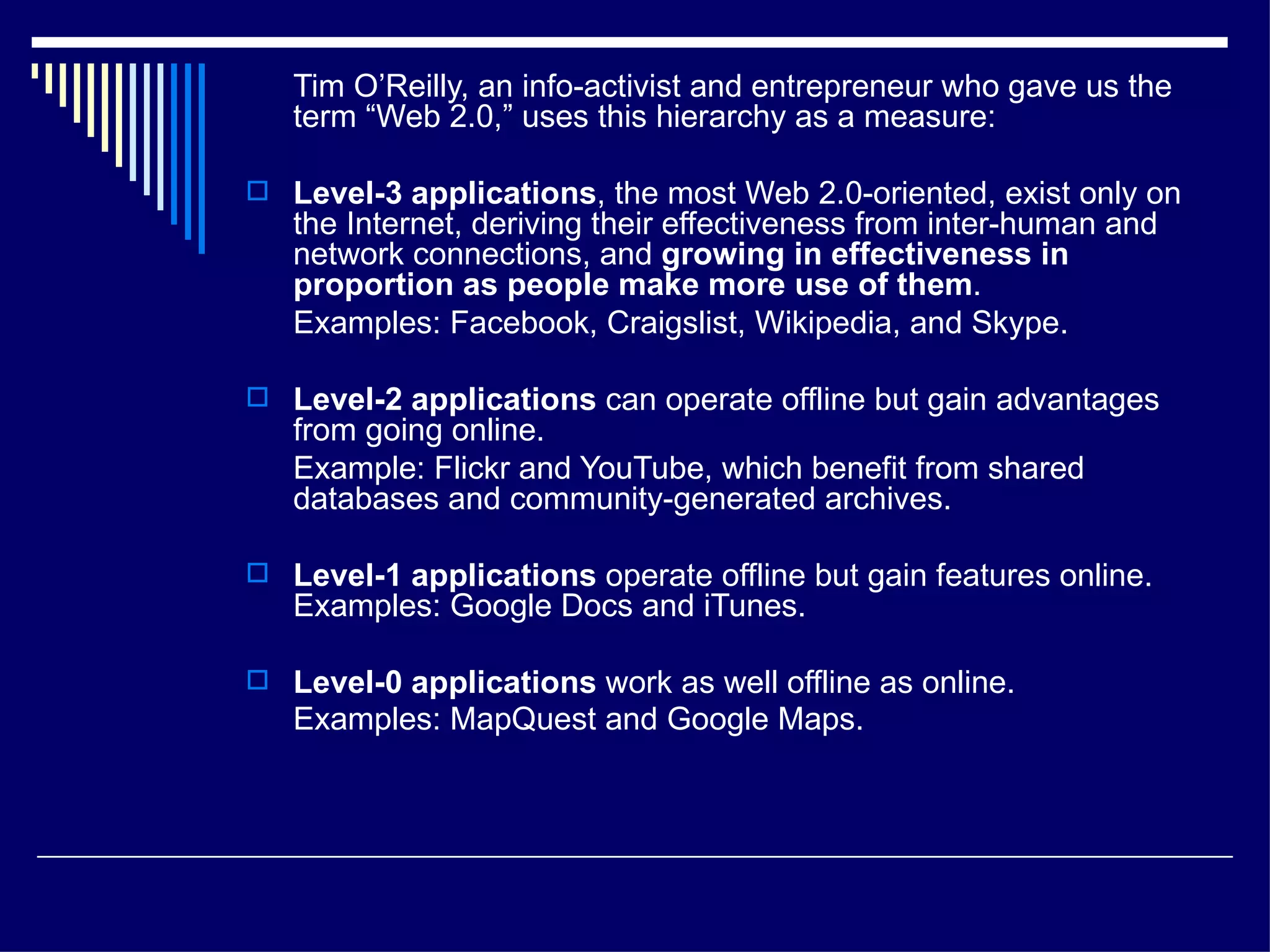
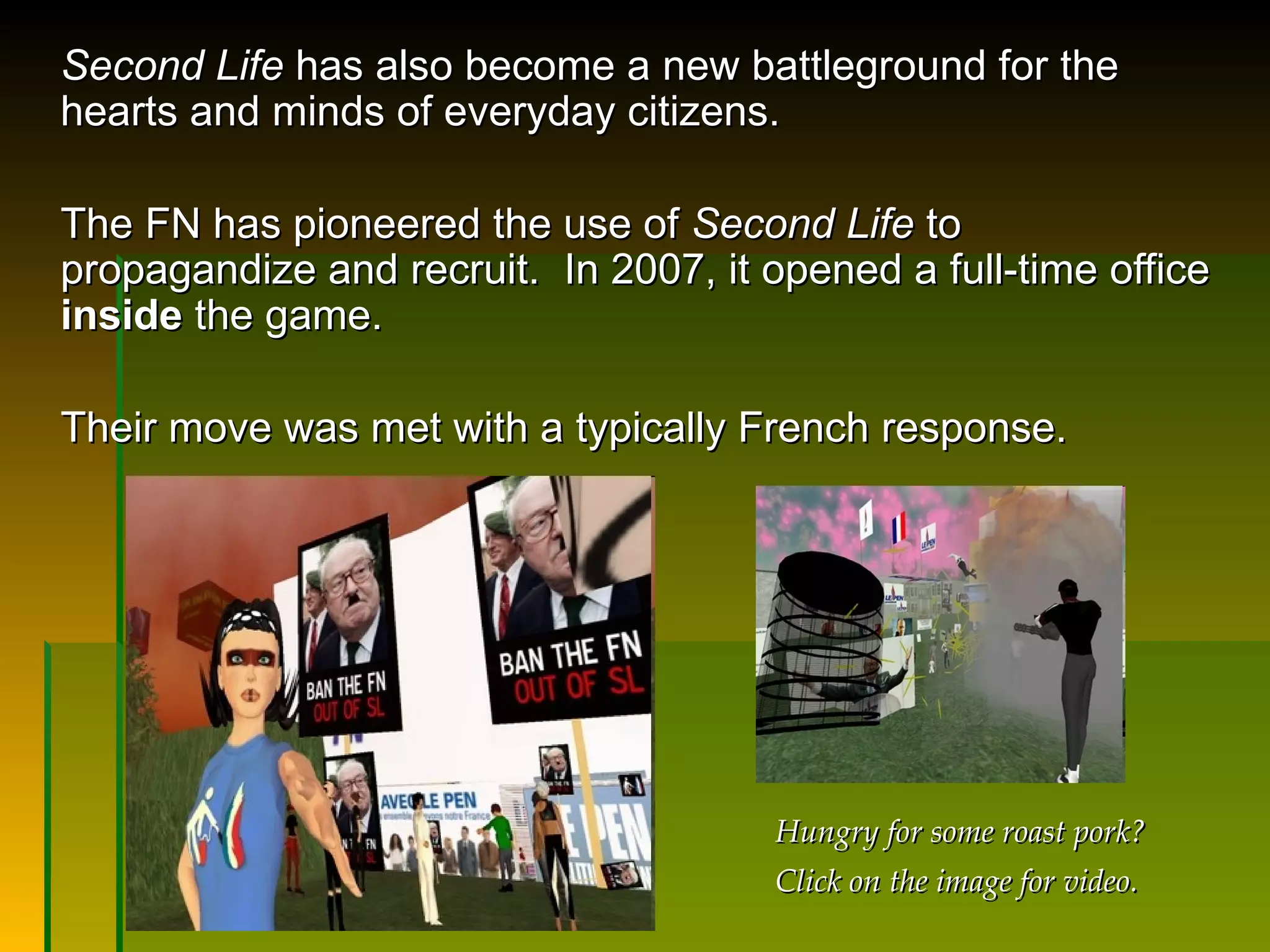
The document explores the role of new media, such as blogs and social networks, in facilitating citizen journalism and enabling subversive activities. It emphasizes the innovative use of these tools by movements, including Barack Obama's campaign, to mobilize grassroots support and challenge established power structures. The text also critiques the dual nature of new media as a platform for both democratic advancements and extremist ideologies.




![But this isn’t fine: in a 1998 interview for the alternative weekly newspaper Miami New Times , Stormfront’s owner, Don Black (a former Klu Klux Klan Grand Wizard) is quoted as saying, “ We want to take America back. […] Whites won't have any choice but to take military action. It's our children whose interests we have to defend.” 2 Then in 2006, the Southern Poverty Law Center reported a discussion on Stormfront in which white nationalists were encouraged to join the US military. Why? So that they could learn the skills necessary for winning a race war. 3](https://image.slidesharecdn.com/schwartznewmedialecture-1229546670270071-1/75/Log-on-tune-in-blog-out-citizen-journalists-New-Media-and-subversive-activity-40-2048.jpg)