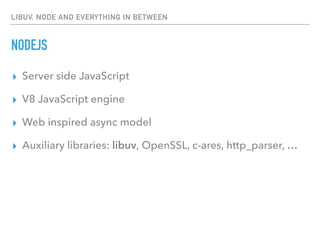
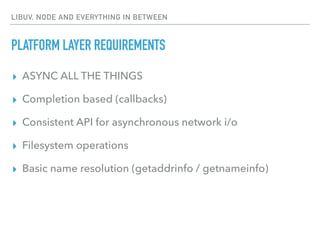
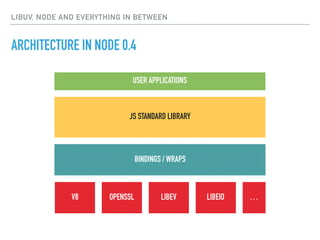
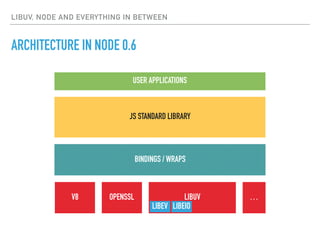
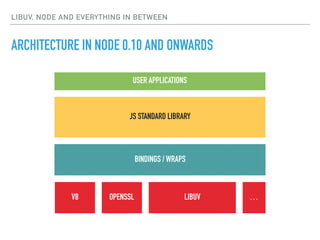
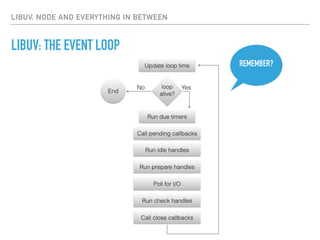
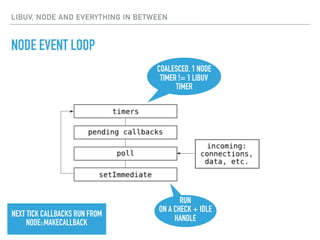
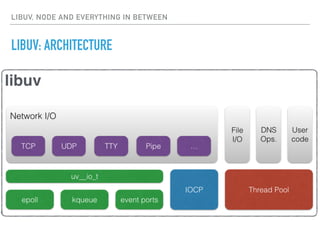
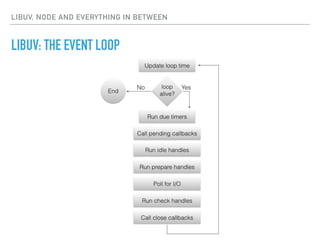
The document provides an overview of libuv, a C library used for asynchronous I/O in Node.js, highlighting its features, architecture, and the event loop mechanism. It explains how libuv facilitates I/O multiplexing, allowing multiple connections without blocking, and describes the implementation of a chat application using libuv. Additionally, it touches upon Node.js's reliance on libuv for asynchronous network I/O and various other operations.



![THE GYP BUILD FILE
# Copyright (c) 2016, Saúl Ibarra Corretgé <saghul@gmail.com>
# Copyright (c) 2012, Ben Noordhuis <info@bnoordhuis.nl>
#
# Permission to use, copy, modify, and/or distribute this software for any
# purpose with or without fee is hereby granted, provided that the above
# copyright notice and this permission notice appear in all copies.
#
# THE SOFTWARE IS PROVIDED "AS IS" AND THE AUTHOR DISCLAIMS ALL WARRANTIES
# WITH REGARD TO THIS SOFTWARE INCLUDING ALL IMPLIED WARRANTIES OF
# MERCHANTABILITY AND FITNESS. IN NO EVENT SHALL THE AUTHOR BE LIABLE FOR
# ANY SPECIAL, DIRECT, INDIRECT, OR CONSEQUENTIAL DAMAGES OR ANY DAMAGES
# WHATSOEVER RESULTING FROM LOSS OF USE, DATA OR PROFITS, WHETHER IN AN
# ACTION OF CONTRACT, NEGLIGENCE OR OTHER TORTIOUS ACTION, ARISING OUT OF
# OR IN CONNECTION WITH THE USE OR PERFORMANCE OF THIS SOFTWARE.
# gyp -Duv_library=static_library --depth=$PWD --generator-output=$PWD/out -Goutput_dir=$PWD/out -f make build.gyp
{
'targets': [
{
'target_name': 'chat-server',
'type': 'executable',
'dependencies': ['deps/libuv/uv.gyp:libuv'],
'sources': ['src/main.c', 'src/queue.h', 'src/pokemon_names.h'],
}
]
}](https://image.slidesharecdn.com/vt9nhmhjqzk3fd4loiiv-signature-804871951955cddd69f25b9fd0863c2fa48f5d0b0a700084358d094fd6286dc6-poli-160804165148/85/libuv-NodeJS-and-everything-in-between-21-320.jpg)
![INITIALISE AND RUN SERVER
struct user
{
QUEUE queue;
uv_tcp_t handle;
char id[32];
};
static QUEUE users;
int main(void)
{
QUEUE_INIT(&users);
srand(1234);
int r;
uv_tcp_t server_handle;
uv_tcp_init(uv_default_loop(), &server_handle);
struct sockaddr_in addr;
uv_ip4_addr(SERVER_ADDR, SERVER_PORT, &addr);
r = uv_tcp_bind(&server_handle, (const struct sockaddr*) &addr, 0);
if (r < 0)
fatal("uv_tcp_bind", r);
const int backlog = 128;
r = uv_listen((uv_stream_t*) &server_handle, backlog, on_connection);
if (r < 0)
fatal("uv_listen", r);
printf("Listening at %s:%dn", SERVER_ADDR, SERVER_PORT);
uv_run(uv_default_loop(), UV_RUN_DEFAULT);
return 0;
}](https://image.slidesharecdn.com/vt9nhmhjqzk3fd4loiiv-signature-804871951955cddd69f25b9fd0863c2fa48f5d0b0a700084358d094fd6286dc6-poli-160804165148/85/libuv-NodeJS-and-everything-in-between-22-320.jpg)
![BROADCAST DATA
static void broadcast(const struct user* sender, const char *fmt, ...)
{
QUEUE *q;
char msg[512];
va_list ap;
va_start(ap, fmt);
vsnprintf(msg, sizeof(msg), fmt, ap);
va_end(ap);
QUEUE_FOREACH(q, &users) {
struct user *user = QUEUE_DATA(q, struct user, queue);
if (user != sender) {
unicast(user, msg);
}
}
}
static void unicast(struct user *user, const char *msg)
{
size_t len = strlen(msg);
uv_write_t *req = xmalloc(sizeof(*req) + len);
void *addr = req + 1;
memcpy(addr, msg, len);
uv_buf_t buf = uv_buf_init(addr, len);
uv_write(req, (uv_stream_t*) &user->handle, &buf, 1, on_write);
}
static void on_write(uv_write_t *req, int status)
{
free(req);
}](https://image.slidesharecdn.com/vt9nhmhjqzk3fd4loiiv-signature-804871951955cddd69f25b9fd0863c2fa48f5d0b0a700084358d094fd6286dc6-poli-160804165148/85/libuv-NodeJS-and-everything-in-between-25-320.jpg)
![MISCELLANEOUS FUNCTIONS
static void on_close(uv_handle_t* handle)
{
struct user *user = QUEUE_DATA(handle, struct user, handle);
free(user);
}
static void make_user_id(struct user *user)
{
snprintf(user->id, sizeof(user->id), "%s", pokemon_names[rand() % ARRAY_SIZE(pokemon_names)]);
}](https://image.slidesharecdn.com/vt9nhmhjqzk3fd4loiiv-signature-804871951955cddd69f25b9fd0863c2fa48f5d0b0a700084358d094fd6286dc6-poli-160804165148/85/libuv-NodeJS-and-everything-in-between-26-320.jpg)