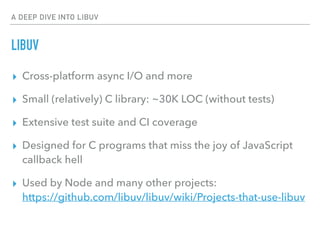
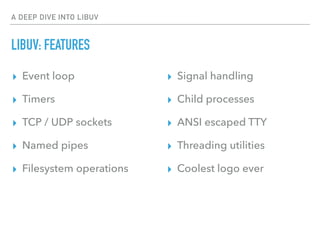
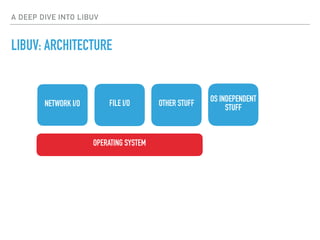
This document provides an overview of the libuv library. Libuv is a cross-platform asynchronous I/O and event loop library written in C. It is used by Node.js and many other projects. The document discusses libuv's architecture, features like the event loop, handles, and requests. It also covers libuv's use in Node.js and the current state and future plans for libuv.