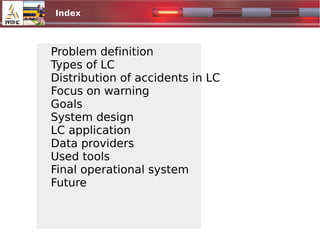
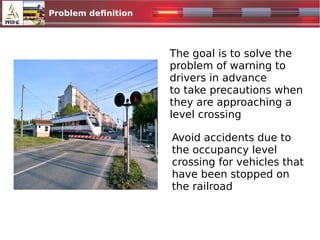
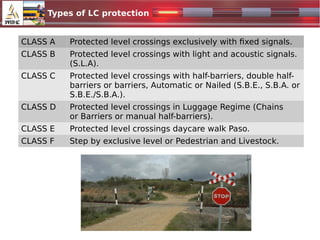
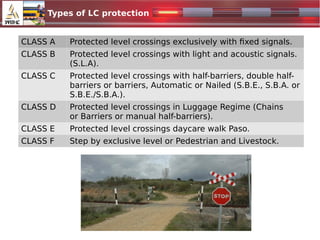
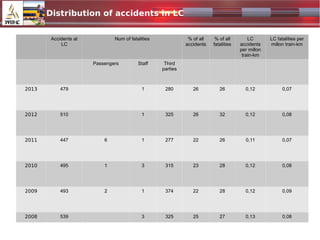
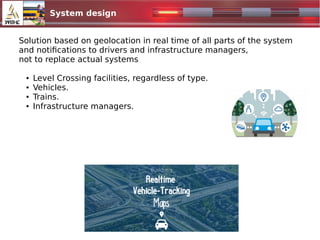
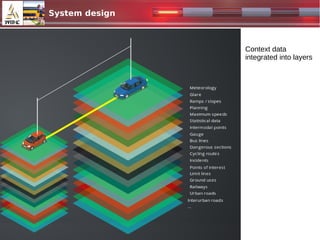
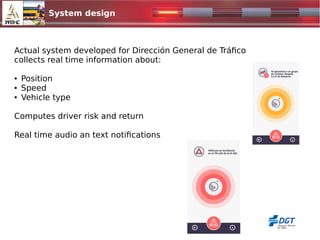
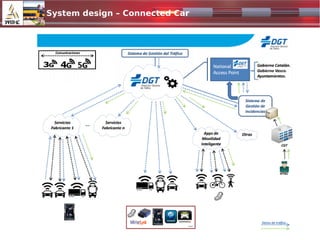
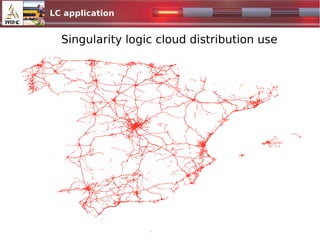
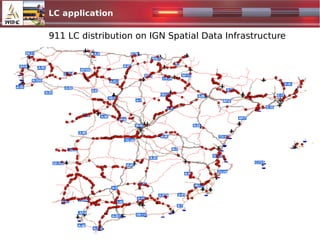
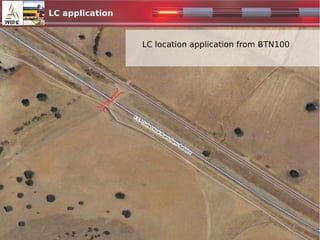
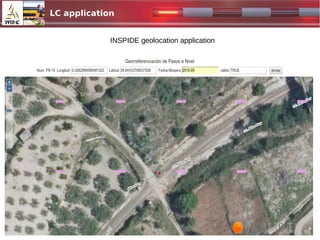
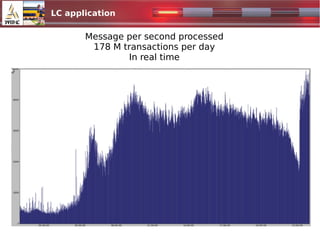
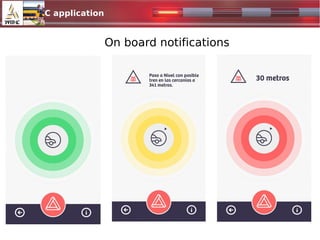
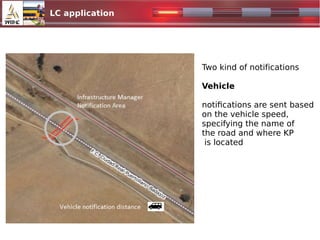
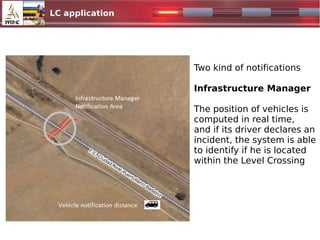
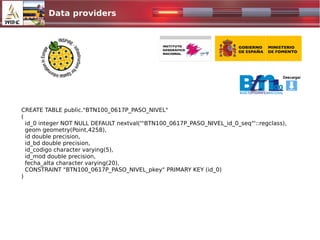
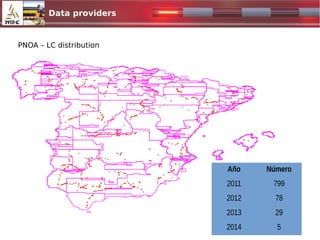
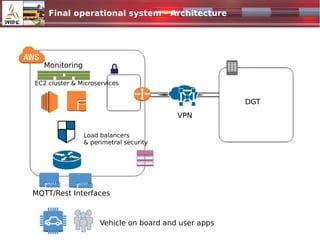
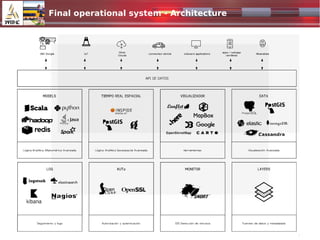
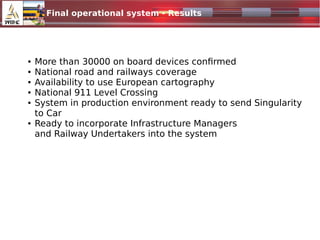
The document discusses the integration of level crossing (LC) protection into connected car technologies to enhance road and railway safety. It outlines the types of level crossings, the current system for notifying drivers and infrastructure managers about these crossings, and the real-time geolocation capabilities of the system. Future steps include improving location accuracy, involving infrastructure managers, and expanding the system's reach internationally.