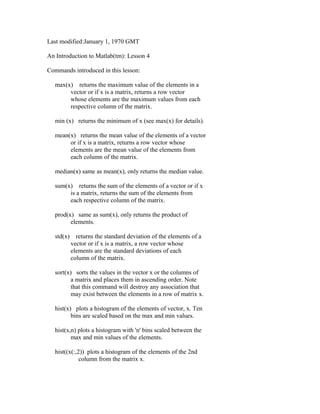
This document introduces Matlab commands for statistical calculations on vectors and matrices. It describes commands like max, min, mean, median, std, and sort that return statistical properties of data in a vector or column-wise in a matrix. It provides an example using a 12x3 matrix of temperature data and demonstrates how the commands return single values for vectors but row vectors describing each column when applied to matrices. The document explains that Matlab treats each column of a matrix separately for these calculations.