Legislation Comparison Grid TemplateUse this document to com.docx
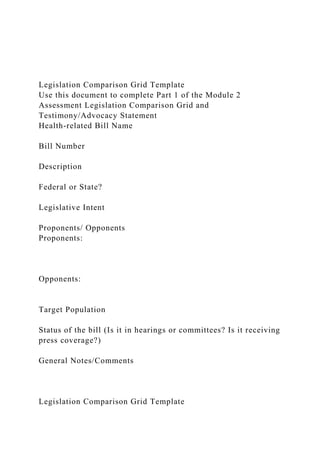
- 1. Legislation Comparison Grid Template Use this document to complete Part 1 of the Module 2 Assessment Legislation Comparison Grid and Testimony/Advocacy Statement Health-related Bill Name Bill Number Description Federal or State? Legislative Intent Proponents/ Opponents Proponents: Opponents: Target Population Status of the bill (Is it in hearings or committees? Is it receiving press coverage?) General Notes/Comments Legislation Comparison Grid Template
- 2. © 2018 Laureate Education Inc. 2 PART 1 Using the Web or other resources, find a case where an illegal search was claimed. Write a brief 250 words essay describing that case and how it relates to this week's topic. PART 2 Discuss, in your own words using 500 words or more, how business process as a service (BPaaS) reduces risk for commercial enterprises. Use at least three sources. Include at least 3 quotes from your sources enclosed in quotation marks and cited in-line by reference to your reference list. Cite your sources. Do not copy. Write an essay format not in bulleted, numbered or other list format. 2 6 9 11 inTeg RaTing geneRaTion y employees To aCCeleRaTe Compe TiTive aDvanTag e Introduction
- 3. This chapter focuses on Gen Y employees who are also known as “ digital natives” and “ millennials.” Gen Y employees possess the attributes to assist companies in transforming their workforce to meet the accelerated change in the competitive landscape. Most executives across industries recognize that digital technologies are the most powerful variable to maintaining and expanding company markets. Gen Y employees provide a natural fit for dealing with emerging digital technologies. However, success with integrating Gen Y employees is contingent upon baby boomer and Gen X man- agement to adapt new leadership philosophies and procedures suited to meet the expectations and needs of these new workers. Ignoring the unique needs of Gen Y employees will likely result in an incon- gruent organization that suffers high turnover of young employees who will seek more entrepreneurial environments. I established in Chapter 10 that digital transformation is at the core of change and competitive survival in the twenty-first cen- tury. Chapter 10 did not address the changes in personnel that are quickly becoming major issues at today’ s global firms. While I offered changes to organizational structures, I did not address the mixture of different generations that are at the fabric of any typical organization. This chapter is designed to discuss how these
- 4. multiple generations need to “ learn” how to work together to form productive and effective organizations that can compete in the digital economy. Furthermore, this chapter will address how access to human capital will change in the future and the different types of relationships that individuals will have with employers. For example, the “ gig” 2 70 InForMAtIon teChnolo GY economy will use non-traditional outside workers who will provide sources of talent for shorter-term employment needs. Indeed, the gig economy will require HR and IT leaders to form new and intri- cate employee relationships. As discussed in Chapter 10, companies need to transform their business from analogue to one that uses digital technologies. Such transformation requires moving from a transactional relation- ship with customers to one that is more “ interactional” (Ernst & Young, 2012). Completing an analogue to digital transformation, while essential for a business to survive in the twenty-first century, is difficult to accomplish. Responsive organizational dynamism (ROD) showed us that successful adaptation of new digital tech- nologies requires strategic integration and cultural assimilation
- 5. of the people that comprise the organization. As stated earlier, these components of ROD can be categorized as the essential roles and responsibilities of the organization that are necessary to utilize new technological inventions that can strategically be integrated within a business entity. The purpose here is to explore why Gen Y employees need to be integrated with baby boomers and Gen X staff to effectively enhance the success of digital transformation initiatives. The Employment Challenge in the Digital Era Capgemini and MIT (2013) research shows that organizations need new operating models to meet the demands of a digital-driven era. Digital tools have provided leaders with ways to connect at an unprec- edented scale. Digital technology has allowed companies to invade other spaces previously protected by a business’ s “ asset specificities” (Tushman & Anderson, 1997), which are defined as advantages enjoyed by companies because of their location, product access, and delivery capabilities. Digital technologies allow those specificities to be neutralized and thus, change the previous competitive balances among market players. Furthermore, digital technology acceler- ates this process, meaning that changes in market share occur very
- 6. quickly. The research offers five key indicators that support successful digital transformation in a firm: 2 71InteGr AtInG Gener AtIon Y 1. A company’ s strategic vision is only as effective as the people behind it. Thus, winning the minds of all levels of the organi- zation is required. 2. To become digital is to be digital. Companies must have a “ one-team culture” and raise their employees’ digital IQ. 3. A company must address the scarcity of talented resources and look more to using Gen Y individuals because they have a more natural adaptation to take on the challenges of digital transformation. 4. Resistant managers are impediments to progress and can actually stop digital transformation. 5. Digital leadership starts at the top. As stated in Chapter 10, Eisenhardt and Bourgeouis (1988) first defined dynamic changing markets as being “ high-velocity.” Their research shows that high-velocity conditions existed in the technol- ogy industry during the early 1980s in Silicon Valley, in the United States. They found that competitive advantage was highly dependent on the quality of people that worked at those firms.
- 7. Specifically, they concluded that workers who were capable of dealing with change and less subjected to a centralized totalitarian management structure out- performed those that had more traditional hierarchical organizational structures. While “ high-velocity” during the 1980s was unusual, dig- ital disruption in the twenty-first century has made it a market norm. The combination of evolving digital business drivers with acceler- ated and changing customer demands has created a business revolution that best defines the imperative of the strategic integration component of ROD. The changing and accelerated way businesses deal with their customers and vendors requires a new strategic integration to become a reality, rather than remain a concept without action. Most experts see digital technology as the mechanism that will require business realignment to create new customer experiences. The driving force behind this realignment emanates from digital technologies, which serve as the principle accelerator of the change in transactions across all business units. The general need to optimize human resources forces organizations to rethink and to realign business processes, in
- 8. order to gain access to new business markets, which are weakening the existing “ asset specificities” of the once dominant market leaders. 2 72 InForMAtIon teChnolo GY Gen Y Population Attributes Gen Y or digital natives are those people who are accustomed to the attributes of living in a digital world and are 18– 35 years old. Gen Y employees are more comfortable with accelerated life changes, par- ticularly change brought on by new technologies. Such individuals, according to a number of commercial and academic research studies (Johnson Controls, 2010; Capgemini, 2013; Cisco, 2012; Saxena & Jain, 2012), have attributes and expectations in the workplace that support environments that are flexible, offer mobility, and provide collaborative and unconventional relationships. Specifically, millen- nial workers • want access to dedicated team spaces where they can have emotional engagements in a socialized atmosphere; • require their own space; that is, are not supportive of a “ hotel-
- 9. ing” existence where they do not have a permanent office or workspace; • need a flexible life/work balance; • prefer a workplace that supports formal and informal collab- orative engagement. Research has further confirmed that 79% of Gen Y workers pre- fer mobile jobs, 40% want to drive to work, and female millennials need more flexibility at work than their male counterparts. As a result of this data, businesses will need to compete to recruit and develop skilled Gen Y workers who now represent 25% of the workforce. In India, while Gen Y represents more than 50% of the working popula- tion, the required talent needed by businesses is extremely scarce. Advantages of Employing Millennials to Support Digital Transformation As stated, Gen Y adults appear to have many identities and capabilities that fit well in a digital-driven business world. Indeed, Gen Y peo- ple are consumers, colleagues, employees, managers, and innovators (Johnson Controls, 2010). They possess attributes that align with the requirements to be an entrepreneur, a person with technology savvy and creativity, someone who works well in a mobile
- 10. environment, and is non-conformant enough to drive change in an organization. Thus, 2 73InteGr AtInG Gener AtIon Y the presence of Gen Y personnel can help organizations to restrat- egize their competitive position and to retain key talent (Saxena & Jain, 2012). Furthermore, Gen Y brings a more impressive array of academic credentials than their predecessors. Most important is Gen Y’ s ability to deal better with market change— which inevitably affects organizational change. That is, the digital world market will constantly require changes in organizational structure to accommodate its consumer needs. A major reason for Gen Y’ s willingness to change is its natural alignment with a company’ s customers. Swadzba (2010) posits that we are approaching the end of what he called the “ work era” and moving into a new age based on consumption. Millennials are more apt to see the value of their jobs from their own consumption needs. Thus, they see employment as an act of consumption (Jonas & Kortenius, 2014). Gen Y employees therefore allow employers to acquire the necessary talent that
- 11. can lead to better consumer reputation, reduced turnover of resources and, ulti- mately, increased customer satisfaction (Bakanauskiené et al., 2011). Yet another advantage of Gen Y employees is their ability to transform organizations that operate on a departmental basis into one that is based more on function; an essential requirement in a digital economy. Integration of Gen Y with Baby Boomers and Gen X The prediction is that 76 million baby boomers (born 1946– 1964) and Gen X workers (born 1965– 1984) will be retiring over the next 15 years. The question for many corporate talent executives is how to manage the transition in a major multigenerational workforce. Baby boomers alone still inhabit the most powerful leadership positions in the world. Currently, the average age of CEOs is 56, and 65% of all corporate leaders are baby boomers. Essentially, corporations need to produce career paths that will be attractive to millennials. Thus, the older generation needs to • Acknowledge some of their preconceived perceptions of cur- rent work ethics that are simply not relevant in today’ s com- plex environments.
- 12. • Allow Gen Y to escalate in ranks to satisfy their ambitions and sense of entitlement. 2 74 InForMAtIon teChnolo GY • Implement more flexible work schedules, offer telecommut- ing, and develop a stronger focus on social responsibility. • Support more advanced uses of technology, especially those used by Gen Yers in their personal lives. • Employ more mentors to help Gen Y employees to better understand the reasons for existing constraints in the organi- zations where they work. • Provide more complex employee orientations, more timely personnel reviews, and in general more frequent feedback needed by Gen Y individuals. • Establish programs that improve the verbal communications skills of Gen Y workers that are typically more comfortable with nonverbal text-based methods of communication. • Implement more continual learning and rotational programs that support a vertical growth path for younger employees. In summary, it is up to the baby boomer and Gen X leaders to modify their styles of management to fit the needs of their younger Gen Y employees. The challenge to accomplish this objective is com- plicated, given the wide variances on how these three generations think, plan, take risks, and most important, learn.
- 13. Designing the Digital Enterprise Zogby completed an interactive poll of 4,811 people on perceptions of different generations. 42% of the respondents stated that baby boomers would be remembered for their focus on consumerism and self-indulgence. Gen Y, on the other hand, are considered more self- interested, entitled narcissists who want to spend all their time post- ing “ selfies” to Facebook. However, other facts offer an expanded perception of these two generations, as shown in Table 11.1 Research completed by Ernst and Young (2013) offers additional comparisons among the three generations as follows: 1. Gen Y individuals are moving into management positions faster due to retirements, lack of corporate succession plan- ning, and their natural ability to use technology at work. Table 11.2 shows percentage comparisons between 2008 and 2013. 2 75InteGr AtInG Gener AtIon Y The acceleration of growth to management positions among Gen Y individuals can be further illuminated in Table 11.3 by comparing the prior five-year period from 2003 to 2007. 2. While responders of the survey felt Gen X were better
- 14. equipped to manage than Gen Y, the number of Gen Y man- agers is expected to double by 2020 due to continued retire- ments. Another interesting result of the research relates to Gen Y expectations from their employers when they become managers. Specifically Gen Y managers expect (1) an oppor- tunity to have a mentor, (2) to receive sponsorship, (3) to have more career-related experiences, and (4) to receive training to build their professional skills. 3. Seventy-five percent of respondents that identified themselves as managers agree that managing the multiple generations is a significant challenge. This was attributed to different work expectations and the lack of comfort with younger employees managing older employees. Table 11.4 provides additional differences among the three generations: Table 11.1 Baby Boomers versus Gen Y BABY BOOMERS GEN Y Married later and less children Not as aligned to political parties Spend lavishly More civically engaged More active and selfless Socially active Fought against social injustice, supported civil rights, and defied the Vietnam War Cheerfully optimistic Had more higher education access More concerned with quality of life than material gain
- 15. Table 11.2 Management Roles 2008– 2013 Baby boomer (ages 49– 67) 19% Gen X (ages 33– 48) 38% Gen Y (18– 32) 87% Table 11.3 Management Roles 2003– 2007 Baby boomer (ages 49– 67) 23% Gen X (ages 33– 48) 30% Gen Y (18– 32) 12% 2 76 InForMAtIon teChnolo GY Assimilating Gen Y Talent from Underserved and Socially Excluded Populations The outsourcing of jobs outside of local communities to countries with lower employment costs has continued to grow during the early part of the twenty-first century. This phenomenon has led to significant social and economic problems, especially in the United States and in Western Europe as jobs continue to migrate to foreign countries where there are lower labor costs and education systems that provide Table 11.4 Baby Boomer, Gen X and Gen Y Compared BABY BOOMERS GEN X GEN Y
- 16. Seek employment in large established companies that provide dependable employment. Established companies no longer a guarantee for lifetime employment. Many jobs begin to go offshore. Seek multiple experiences with heavy emphasis on social good and global experiences. Re-evaluation of offshoring strategies. Process of promotion is well defined, hierarchical and structured, eventually leading to promotion and higher earnings—concept of waiting your turn. Process of promotion still hierarchical, but based more on skills and individual accomplishments. Master’s degree now preferred for many promotions. Less patience with hierarchical promotion policies. More reliance on predictive analytics as the basis for decision making.
- 17. Undergraduate degree preferred but not mandatory. Undergraduate degree required for most professional job opportunities. More focus on specific skills. Multiple strategies developed on how to meet shortages of talent. Higher education is expensive and concerns increase about the value of graduate knowledge and abilities. Plan career preferably with one company and retire. Acceptance of a gradual process of growth that was slow to change. Successful employees assimilated into existing organizational structures by following the rules. Employees begin to change jobs more often, given growth in the technology industry, and opportunities to increase compensation and accelerate promotion by switching jobs. Emergence of a “gig” economy, and the rise of multiple employment relationships
- 18. Entrepreneurism was seen as an external option for those individuals desiring wealth and independence and willing to take risks. Corporate executives’ compensation dramatically increases, no longer requiring starting businesses as the basis for wealth. Entrepreneurism promoted in Higher Education as the basis for economic growth, given the loss of jobs in the U.S. 2 7 7InteGr AtInG Gener AtIon Y more of the skills needed by corporations. Most impacted by the loss of jobs have been the underserved or socially excluded Gen Y youth populations. Indeed, the European average for young adult unem- ployment (aged 15– 25) in 2013 was nearly 25%, almost twice the rate for their adult counterparts (Dolado, 2015). Much of the loss of local jobs can be attributed to expansion of the globalized economy, which has been accelerated by continued technological
- 19. advancements (Wabike, 2014). Thus, the effects of technology gains have negatively impacted efforts toward social inclusion and social equality. Langer, in 2003, established an organization called Workforce Opportunity Services (WOS), as a means of utilizing a form of action research using adult development theory to solve employment problems caused by outsourcing. Langer’ s approach is based on the belief that socially excluded youth can be trained and prepared for jobs in areas such as information technology that would typically be outsourced to lower labor markets. WOS has developed a talent-finding model that has suc- cessfully placed over 1400 young individuals in such jobs. Results of over 12 years of operation and research have shown that talented youth in disadvantaged communities do exist and that such talent can economi- cally and socially contribute to companies (Langer, 2013). The following section describes the Langer Workforce Maturity Arc (LWMA), pres- ents data on its effectiveness as a transformative learning instrument, and discusses how the model can be used as an effective way of recruit- ing Gen Y talent from underserved and socially excluded populations. Langer Workforce Maturity Arc
- 20. The Langer Workforce Maturity Arc (LWMA) was developed to help evaluate socially excluded youth preparation to succeed in the workplace. The LWMA, initially known as the Inner-City Workplace Literacy Arc: charts the progression of underserved or ‘ excluded’ individuals along defined stages of development in workplace culture and skills in relation to multiple dimensions of workplace literacy such as cognitive growth and self-reflection. When one is mapped in relation to the other (work- place culture in relation to stages of literacy assimilation), an Arc is created. LWMA traces the assimilation of workplace norms, a form of individual development. (Langer, 2003: 18) 2 78 InForMAtIon teChnolo GY The LWMA addresses one of the major challenges confronting an organization’ s HR group: to find talent from diverse local populations that can successfully respond to evolving business norms, especially those related to electronic and digital technologies. The LWMA provides a method for measuring the assimilation of workplace cultural norms and
- 21. thus, can be used to meet the mounting demands of an increasingly global, dynamic, and multicultural workplace. Furthermore, if organi- zations are to attain acceptable quality of work from diverse employees, assimilation of socially or economically excluded populations must be evaluated based on (1) if and how individuals adopt workplace cultural norms, and (2) how they become integrated into the business (Langer, 2003). Understanding the relationship between workplace assimila- tion and its development can provide important information on how to secure the work ethic, dignity, solidarity, culture, cognition, and self-esteem of individuals from disadvantaged communities, and their salient contributions to the digital age. Theoretical Constructs of the LWMA The LWMA encompasses sectors of workplace literacy and stages of lit- eracy development , and the arc charts business acculturation require- ments as they pertain to disadvantaged young adult learners. The relationship between workplace assimilation and literacy is a chal- lenging subject. A specific form of literacy can be defined as a social practice that requires specific skills and knowledge (Rassool, 1999).
- 22. In this instance, workplace literacy addresses the effects of workplace practices and culture on the social experiences of people in their work- day, as well as their everyday lives. We need to better understand how individual literacy in the workplace, which subordinates individuality to the demands of an organization, is formulated for diverse groups (Newman, 1999). Most important, are the ways in which one learns how to behave effectively in the workplace— the knowledge, skill, and attitude sets required by business generally, as well as by a specific organization. This is particularly important in disadvantaged commu- nities, which are marginalized from the experiences of more affluent communities in terms of access to high-quality education, informa- tion technologies, job opportunities, and workplace socialization. For example, Friedman et al. (2014) postulate that the active involvement 2 79InteGr AtInG Gener AtIon Y of parents in the lives of their children greatly impacts a student’ s chances of success. It is the absence of this activism that contributes to a system of social exclusion of youth. Prior to determining
- 23. what directions to pursue in educational pedagogies and infrastructures, it is necessary to understand what workplace literacy requirements are present and how they can be developed for disadvantaged youth in the absence of the active support from families and friends. The LWMA assesses individual development in six distinct sectors of workplace literacy: 1. Cognition : Knowledge and skills required to learn and com- plete job duties in the business world, including computational skills; ability to read, comprehend, and retain written infor- mation quickly; remembering and executing oral instructions; and critically examining data. 2. Technology : An aptitude for operating various electronic and digital technologies. 3. Business culture : Knowledge and practice of proper etiquette in the workplace including dress codes, telephone and in-per- son interactions, punctuality, completing work and meeting deadlines, conflict resolution, deference and other protocols associated with supervisors and hierarchies. 4. Socio-economic values : Ability to articulate and act upon main- stream business values, which shape the work ethic. Such val- ues include independent initiative, dedication, integrity, and personal identification with career goals. Values are associated with a person’ s appreciation for intellectual life, cultural sen-
- 24. sitivity to others, and sensitivity for how others view their role in the workplace. Individuals understand that they should make decisions based on principles and evidence rather than personal interests. 5. Community and ethnic solidarity : Commitment to the educa- tion and professional advancement of persons in ethnic minor- ity groups and underserved communities. Individuals can use their ethnicity to explore the liberating capacities offered in the workplace without sacrificing their identity (i.e., they can assimilate workplace norms without abandoning cultural, ethnic, or self-defining principles and beliefs). 2 8 0 InForMAtIon teChnolo GY 6. Self-esteem : The view that personal and professional success work in tandem, and the belief in one’ s capacity to succeed in both arenas. This includes a devotion to learning and self- improvement. Individuals with high self-esteem are reflective about themselves and their potential in business. They accept the realities of the business world in which they work and can comfortably confirm their business disposition, indepen- dently of others’ valuations. Each stage in the course of an individual’ s workplace development reflects an underlying principle that guides the process of adopting workplace norms and behavior. The LWMA is a classificatory scheme that identifies progressive stages in the assimilated uses of workplace literacy. It reflects the perspective that an effective workplace
- 25. partici- pant is able to move through increasingly complex levels of thinking and to develop independence of thought and judgment (Knefelkamp, 1999). The profile of an individual who assimilates workplace norms can be characterized in five developmental stages: 1. Concept recognition : The first stage represents the capacity to learn, conceptualize, and articulate key issues related to the six sectors of workplace literacy. Concept recognition provides the basis for becoming adaptive to all workplace requirements. 2. Multiple workplace perspectives : This refers to the ability to integrate points of view from different colleagues at various levels of the workplace hierarchy. By using multiple perspec- tives, the individual is in a position to augment his or her workplace literacy. 3. Comprehension of business processes : Individuals increase their understanding of workplace cooperation, competition, and advancement as they build on their recognition of busi- ness concepts and workplace perspectives. They increasingly understand the organization as a system of interconnected parts. 4. Workplace competence : As assimilation and competence increase, the individual learns not only on how to perform a particu- lar job adequately but how to conduct oneself professionally within the workplace and larger business environment.
- 26. 2 81InteGr AtInG Gener AtIon Y 5. Professional independence : Individuals demonstrate the ability to employ all sectors of workplace literacy to compete effec- tively in corporate labor markets. They obtain more respon- sible jobs through successful interviewing and workplace performance and demonstrate leadership abilities, leading to greater independence in career pursuits. Professionally inde- pendent individuals are motivated and can use their skills for creative purposes (Langer, 2009). The LWMA is a rubric that charts an individual’ s development across the six sectors of workplace literacy. Each cell within the matrix represents a particular stage of development relative to that sector of workplace literacy, and each cell contains definitions that can be used to identify where a particular individual stands in his or her develop- ment of workplace literacy. The LWMA and Action Research While the LWMA serves as a framework for measuring growth, the model also uses reflection-with-action methods, a component of action research theory, as the primary vehicle for assisting young adults to develop the necessary labor market skills to compete for a job and inevitably achieve some level of professional independence
- 27. (that is, the ability to work for many employers because of achiev- ing required market skills). Reflection-with-action is used as a rubric STAGES OF WORKPLACE LITERACY SECTORS OF WORKPLACE LITERACY CONCEPT RECOGNITION MULTIPLE WORKPLACE PERSPECTIVES COMPREHENSION OF BUSINESS PROCESSES WORKPLACE COMPETENCE PROFESSIONAL INDEPENDENCE Cognition Technology Business Culture
- 28. Socio- Economic Values Community and Ethnic Solidarity Self-Esteem 2 8 2 InForMAtIon teChnolo GY for a variety of methods, involving reflection in relation to learning activities. Reflection has received a number of definitions from differ- ent sources in the literature. Here, “ reflection-with-action” carries the resonance of Schö n’ s (1983) twin constructs: “ reflection-on- action” and “ reflection-in-action,” which emphasize (respectively) reflec- tion in retrospect and reflection to determine what actions to take in the present or immediate future (Langer, 2003). Dewey (1933) and Hullfish and Smith (1978) also suggest that the use of reflection sup- ports an implied purpose. Their formulation suggests the possibility of reflection that is future oriented; what we might call “ reflection-to- action.” These are methodological orientations covered by the rubric.
- 29. Reflection-with-action is critical to the educational and workplace assimilation process of Gen Y. While many people reflect, it is in being reflective that people bring about “ an orientation to their every- day … Chapter 13: Trends in Information Systems Learning Objectives Upon successful completion of this chapter, you will be able to: • describe current trends in information systems. • know how to think about the impacts of changes in technology on society and culture. Introduction Information systems have evolved at a rapid pace ever since their introduction in the 1950s. Today devices you can hold in one hand are more powerful than the computers used to land a man on the
- 30. moon in 1969. The Internet has made the entire world accessible to you, allowing you to communicate and collaborate like never before. This chapter examines current trends and looks ahead to what is coming next. As you read about technology trends in this chapter, think how you might gain competitive advantage in a future career through implementation of some of these devices. Chapter 13: Trends in Information Systems | 291 Global The first trend to note is the continuing expansion of globalization. The use of the Internet is growing all over the world, and with it the use of digital devices. Penetration rates, the percent of the population using the Internet, remains high in the developed world, but other continents are gaining.1
- 31. Internet Users by Continent (Source: Internet World Stats) In addition to worldwide growth in Internet penetration, the number of mobile phones in use continues to increase. At the end of 2017 the world population of people over the age 10 years (those old enough to possibly have their own mobile phone) was about 5.7 billion with an estimated 4.77 billion mobile phone users. This 1. Internet World Stats 292 | Information Systems for Business and Beyond (2019) https://www.internetworldstats.com/stats.htm equates to over 80% of people in the world having a mobile phone. 2 World wide mobile phone users (Source: Statista) Social Social media growth is another trend that continues at a firm growth rate. As of April 2018 there were about 2.18 billion Facebook
- 32. users, a 14% increase from April 2017.3 2. Statistica Forecast of Mobile Phone Users Worldwide 3. Zephoria Top 15 Valuable Facebook Statistics Chapter 13: Trends in Information Systems | 293 https://www.statista.com/statistics/274774/forecast-of-mobile- phone-users-worldwide/ https://zephoria.com/top-15-valuable-facebook-statistics/ Facebook users world wide in June 2017 (Source: Internet World Stats) In 2018, of the 2.2 billion users who regularly use Facebook, only half them spoke English and only 10% were from the US.4 Besides Facebook, other social media sites are also seeing tremendous growth. Over 83% of YouTube’s users are outside the US, with the UK, India, Germany, Canada, France, South Korea, and Russia leading the way.5 Pinterest gets over 57% of its users from outside the US, with over 9% residing in India. 6 Twitter now
- 33. has over 330 million active users. 7 Social media sites not based in the US are also growing. China’s WeChat multipurpose messaging and social media app is the fifth most-visited site in the world.8 4. https://blog.hootsuite.com/facebook-statistics 5. Omnicore Agency Facebook Statistics 6. Omnicore Agency Pinterest Statistics 7. Omnicore Agency Twitter Statistics 8. Statista 294 | Information Systems for Business and Beyond (2019) https://www.omnicoreagency.com/facebook-statistics/ https://www.omnicoreagency.com/pinterest-statistics/ https://www.omnicoreagency.com/twitter-statistics/ https://www.statista.com/statistics/272014/global-social- networks-ranked-by-number-of-users/ Mary Meeker making her Internet Trends presentation Personal Ever since the advent of Web 2.0 and e-commerce, users of
- 34. information systems have expected to be able to modify their experiences to meet their personal tastes. From custom backgrounds on computer desktops to unique ringtones on mobile phones, makers of digital devices provide the ability to personalize how we use them. More recently, companies such as Netflix have begun assisting their users with personalizations by viewing suggestions. In the future, we will begin seeing devices perfectly matched to our personal preferences, based upon information collected about us. Sidebar: Mary Meeker and Internet Trends Chapters such as this are difficult to maintain because the future is a moving target. The same goes for businesses looking to figure out where to develop new products and
- 35. make investments. Enter Mary Meeker, up until 2018 a partner at the notable venture capital firm Kleiner Perkins Caufield & Byers and now forming her own investment group, Bond Capital. For the past several years, Ms. Meeker has presented the “Internet Trends” report at the Code Conference every May. The presentation consists of rapid-fire summaries of data that provides insights into all of the latest trends in digital technologies and their Chapter 13: Trends in Information Systems | 295 https://www.linkedin.com/in/mary-meeker-5823ba48/ https://www.linkedin.com/in/mary-meeker-5823ba48/ impact on economies, culture, and investing. For those wanting to keep up with technology, there is no better way than to unpack her annual presentation by watching a video of the presentation and reviewing the associated slide deck.
- 36. Here are the last few years of videos of her presentation: 2019 2018 2017 You can view her slide decks from previous years by going to the Bond Capital archive. Mobile Perhaps the most impactful trend in digital technologies in the last decade has been the advent of mobile technologies. Beginning with the simple cellphone in the 1990s and evolving into the smartphones of today, the growth of mobile has been overwhelming. Here are some key indicators of this trend: • Mobile vs. Desktop. Minutes spent each day on a mobile device are 2.5 times the number of minutes spent on a desktop computer. • Daytime vs. Evening. Desktop use dominates in the daytime hours, but mobile devices are dominant in the evening, with peak usage around 8:00 pm.
- 37. • Device usage. Smartphones are used more than any other technology. Laptops are in second place, followed by tablets holding a slight edge over desktops. 9 • Smartphone sales decline. According to Gartner Group, world 9. Smart Insights 296 | Information Systems for Business and Beyond (2019) https://www.youtube.com/watch?v=G_dwZB5h56E https://www.youtube.com/watch?v=HdjcdZqODoE https://www.youtube.com/watch?v=UC8GwG6srqs https://www.bondcap.com/#archive https://www.smartinsights.com/mobile-marketing/mobile- marketing-analytics/mobile-marketing-statistics/ wide smartphone sales declined in the fourth quarter of 2017 by 4.7% compared with the fourth quarter of 2016. This is the first decline in global smartphone sales since Gartner began tracking mobile phone sales in 2004. 10 • The rise and fall of tablets. In 2012 the iPad sold more than three times as many units in its first twelve months as the iPhone did in its first twelve months. However, tablet sales dropped 20% from the fourth quarter 2015 to fourth quarter 2016. 11
- 38. The decline in tablet sales continued into 2017 when first quarter sales dropped 8.5% to their lowest total since the third quarter of 2012, the year they were introduced. 12 In comparison, PC sales dropped only 1.7% in 2017 compared with tablet sales being down 10%. 13 As discussed in chapter 5, the advent of 5G connection technologies will accelerate an “always-connected” state for a majority of people around the world. Wearable The average smartphone user looks at his or her smartphone 150 times a day for functions such as messaging (23 times), phone calls (22), listening to music (13), and social media (9).Many of these functions would be much better served if the technology was worn 10. Gartner.com 11. Techcrunch 12. Business Insider
- 39. 13. Telegraph Chapter 13: Trends in Information Systems | 297 https://www.gartner.com/newsroom/id/3859963 https://techcrunch.com/2017/03/21/what-happened-to-tablet- sales/ http://www.businessinsider.com/tablet-sales-decline-ipad-chart- 2017-5 https://www.telegraph.co.uk/technology/2017/01/11/tablet- sales-fall-third-successive-year-pc-market-stabilises/ Wearable Devices Actual and Forecast (Source: Gartner Group, August 2017) on, or even physically integrated into, our bodies. This technology is known as a “wearable.” Wearables have been around for a long time, with technologies such as hearing aids and, later, bluetooth earpieces. Now the product lines have expanded to include the Smartwatch, body cameras, sports watch, and various fitness monitors. The following
- 40. table from the Gartner Group reports both historical and predicted sales. Wearable Devices Worldwide (millions of units) Notice the strong growth predicted by 2021. Total wearable devices are projected to increase by about 45% from 2018 to 2021. 298 | Information Systems for Business and Beyond (2019) https://opentextbook.site/informationsystems2019/wp- content/uploads/sites/3/2018/07/170824_gartner_wearables.png https://opentextbook.site/informationsystems2019/wp- content/uploads/sites/3/2018/07/170824_gartner_wearables.png Waze Screen Shot (Click to enlarge) Collaborative As more people use smartphones and wearables, it will be simpler than ever to share data with each other for mutual benefit. Some of this sharing can be done passively,
- 41. such as reporting your location in order to update traffic statistics. Other data can be reported actively, such as adding your rating of a restaurant to a review site. The smartphone app Waze is a community-based tool that keeps track of the route you are traveling and how fast you are making your way to your destination. In return for providing your data, you can benefit from the data being sent from all of the other users of the app. Waze directs you around traffic and accidents based upon real-time reports from other users. Yelp! allows consumers to post ratings and reviews of local businesses into a database, and then it provides that data back to
- 42. consumers via its website or mobile phone app. By compiling ratings of restaurants, shopping centers, and services, and then allowing consumers to search through its directory, Yelp! has become a huge source of business for many companies. Unlike data collected passively however, Yelp! relies on its users to take the time to provide honest ratings and reviews. Chapter 13: Trends in Information Systems | 299 http://www.waze.com/ http://www.yelp.com/ Printable One of the most amazing innovations to be developed recently is the 3-D printer. A 3-D printer allows you to print virtually any 3-D object based on a model of that object designed on a computer. 3-D printers work by creating layer upon layer of the model using malleable materials, such as different types of glass, metals, or even
- 43. wax. 3-D printing is quite useful for prototyping the designs of products to determine their feasibility and marketability. 3-D printing has also been used to create working prosthetic legs and an ear that can hear beyond the range of normal hearing. The US military now uses 3-D printed parts on aircraft such as the F- 18.14 Here are more amazing productions from 3D printers. • Buildings. Researchers at MIT in 2017 unveiled a 3D printing robot that can construct a building. It has a large arm and small arm. The large arm moves around the perimeter of the building while the small arm sprays a variety of materials including concrete and insulation. Total time to construct a dome- shaped building is just 14 hours. • Musical Instruments. Flutes, fiddles, and acoustic guitars are being produced with 3D printing using both metal and plastic. You can click here for an example of making a violin. • Medical Models. Medical models are being used to help doctors train in the areas of orthopedics, transplant surgery,
- 44. and oncology. Using a 3D printed brain model similar to the one shown here, surgeons were able to save a patient from a cerebral aneurysm. • Clothing. How would you like clothes that fit perfectly? Special 14. The Economist. (2013, September 13). 3-D Printing Scales Up. 300 | Information Systems for Business and Beyond (2019) http://inhabitat.com/these-beautiful-customized-3d-printed- prosthetic-legs-are-made-to-be-seen http://news.yahoo.com/7-weirdest-things-made-3d-printing- 122023635.html https://violinodigitale.com/ http://www.3ders.org/articles/20170713-3d-printed-brain- model-helps-surgeons-save-60-year-old-woman-with-cerebral- aneurysm.html http://www.economist.com/news/technology- quarterly/21584447-digital-manufacturing-there-lot-hype- around-3d-printing-it-fast http://www.economist.com/news/technology- quarterly/21584447-digital-manufacturing-there-lot-hype- around-3d-printing-it-fast software is used to measure a person, then 3D printing produces the clothing to the exact measurements. The result is
- 45. well-fitting clothes that consume less raw materials. Initially the challenge was to find materials that would not break. You can read more about 3D printing of clothes and shoes. 15 3-D printing is one of many technologies embraced by the “maker” movement. Chris Anderson, editor of Wired magazine, puts it this way16: In a nutshell, the term “Maker” refers to a new category of builders who are using open-source methods and the latest technology to bring manufacturing out of its traditional factory context, and into the realm of the personal desktop computer. Until recently, the ability to manufacture was reserved for those who owned factories. What’s happened over the last five years is that we’ve brought the Web’s democratizing power to manufacturing. Today, you can manufacture with the push of a button. 15. Bosavage, J. (2017, September 5). Unbelievable Creations from 3-D Printers. 16. Anderson, C. (2012). Makers: The New Industrial
- 46. Revolution.. Crown Business. Chapter 13: Trends in Information Systems | 301 https://www.wired.com/2017/05/the-shattering-truth-of-3d- printed-clothing/ http://theinstitute.ieee.org/technology-topics/consumer- electronics/unbelievable-creations-from-3d-printers http://theinstitute.ieee.org/technology-topics/consumer- electronics/unbelievable-creations-from-3d-printers Findable The “Internet of Things” (IoT) refers to devices that have been embedded into a variety of objects including appliances, lamps, vehicles, lightbulbs, toys, thermostats, jet engines, etc. and then connecting them via Wi-Fi, BlueTooth, or LTE to the Internet. Principally three factors have come together to give us IoT: inexpensive processors, wireless connectivity, and a new standard for addresses on the Internet known as IPv6. The result is these small, embedded objects (things) are capable of sending and receiving data. Lights can be turned on or off remotely. Thermostats can be reset with anyone being present. And, perhaps on the
- 47. downside, how you drive your car can be monitored and evaluated by your insurance company. Processors have become both smaller and cheaper in recent years, leading to their being embedded in more devices. Consider technological advancements in your vehicles. Your car can now collect data about how fast you drive, where you go, radio stations you listen to, and your driving performance such as acceleration and braking. Insurance companies are offering discounts for the right to monitor your driving behavior. On the positive side, imagine 302 | Information Systems for Business and Beyond (2019) the benefit of being informed instantly of anticipated traffic delays each time you adjust your route to work in the morning. Think of IoT as devices that you wouldn’t normally consider being connected to the Internet. And, the connection is independent of
- 48. human intervention. So a PC is not an IoT, but a fitness band could be. One keyword for IoT would be “independent”, not relying directly or constantly on human action. Another keyword would be “interconnected”, in the sense that IoTs are connected to other IoTs and data collection points or data servers. This interconnectedness or uploading of data is virtually automatic. “Ubiqutous” is also a good descriptor of IoTs. And so is “embeddedness.” It is reasonable to expect that devices through IoTs are reporting data about conditions and events that are not foremost in our thinking, at least not on a continuous basis. Today there are IoTs for monitoring traffic, air quality, soil moisture, bridge conditions, consumer electronics, autonomous vehicles, and the list seemingly never stops. The question that might come to mind is “How many IoTs are there today?”
- 49. The Gartner Group released a study in January 2017 which attempted to identify where IoTs exist. They reported that over half of all IoTs are installed in devices used by consumers. They also noted that growth in IoTs increased by over 30% from 2016 to the projected levels for 2017.17 Benefits from IoTs are virtually everywhere. Here is a quick list. • Optimization of Processes. IoTs in manufacturing monitor a variety of conditions that impact production including temperature, humidity, barometric pressure – all factors which 17. Ranger, S. (2018, January 19). What is the IoT? Everything You Wanted to Know about The Internet of Things Right Now. ZDNet. Chapter 13: Trends in Information Systems | 303 https://www.zdnet.com/article/what-is-the-internet-of-things- everything-you-need-to-know-about-the-iot-right-now/ https://www.zdnet.com/article/what-is-the-internet-of-things- everything-you-need-to-know-about-the-iot-right-now/ https://www.zdnet.com/article/what-is-the-internet-of-things- everything-you-need-to-know-about-the-iot-right-now/
- 50. require adjustment in application of manufacturing formulas. • Component Monitoring. IoTs are added to components in the manufacturing process, then monitored to see how each component is performing. • Home Security Systems. IoTs make the challenge of monitoring activity inside and outside your home are now easier. • Smart Thermostats. Remote control of home thermostats through the use of IoTs allows the homeowner to be more efficient in consumption of utilities. • Residential Lighting. IoTs provide remote control of lighting, both interior and exterior, and at any time of day.18 Security issues need to be acknowledged and resolved, preferably before IoTs in the form of remote lighting, thermostats, and security systems are installed in a residence. Here are some security concerns that need monitoring. • Eavesdropping. Smart speaker systems in residences have been hacked, allowing others to eavesdrop on conversations within the home.
- 51. • Internet-connected Smart Watches. These devices are sometimes used to monitor the location of children in the family. Unfortunately, hackers have been able to breakin and again, eavesdrop as well as learn where children are located. • Lax Use by Owners. Devices such as smart thermometers, security systems, etc. come with a default password. Many owners fail to change the password, thereby allowing easy access by a hacker. 18. Ranger, S. (2018, January 19). What is the IoT? Everything You Wanted to Know about The Internet of Things Right Now. ZDNet. 304 | Information Systems for Business and Beyond (2019) https://www.zdnet.com/article/what-is-the-internet-of-things- everything-you-need-to-know-about-the-iot-right-now/ https://www.zdnet.com/article/what-is-the-internet-of-things- everything-you-need-to-know-about-the-iot-right-now/ https://www.zdnet.com/article/what-is-the-internet-of-things- everything-you-need-to-know-about-the-iot-right-now/ Autonomous Another trend that is emerging is an extension of the Internet of Things: autonomous robots and vehicles. By combining
- 52. software, sensors, and location technologies, devices that can operate themselves to perform specific functions are being developed. These take the form of creations such as medical nanotechnology robots (nanobots), self-driving cars, or unmanned aerial vehicles (UAVs). A nanobot is a robot whose components are on the scale of about a nanometer, which is one-billionth of a meter. While still an emerging field, it is showing promise for applications in the medical field. For example, a set of nanobots could be introduced into the human body to combat cancer or a specific disease. In March of 2012, Google introduced the world to their driverless car by releasing a video on YouTube showing a blind man driving the car around the San Francisco area. The car combines several technologies, including a laser radar system, worth about
- 53. $150,000. While the car is not available commercially yet, three US states (Nevada, Florida, and California) have already passed legislation making driverless cars legal. A UAV, often referred to as a “drone,” is a small airplane or helicopter that can fly without a pilot. Instead of a pilot, they are either run autonomously by computers in the vehicle or operated by a person using a remote control. While most drones today are used for military or civil applications, there is a growing market for personal drones. For around $300, a consumer can purchase a drone for personal use. Secure As digital technologies drive relentlessly forward, so does the Chapter 13: Trends in Information Systems | 305 http://www.youtube.com/watch?v=cdgQpa1pUUE http://www.amazon.com/Parrot-AR-Drone-Quadricopter- Controlled-Android/dp/B007HZLLOK http://www.amazon.com/Parrot-AR-Drone-Quadricopter- Controlled-Android/dp/B007HZLLOK
- 54. demand for increased security. One of the most important innovations in security is the use of encryption, which we covered in chapter 6. Summary As the world of information technology moves forward, we will be constantly challenged by new capabilities and innovations that will both amaze and disgust us. As we learned in chapter 12, many times the new capabilities and powers that come with these new technologies will test us and require a new way of thinking about the world. Businesses and individuals alike need to be aware of these coming changes and prepare for them. Study Questions 1. Which countries are the biggest users of the Internet? Social media? Mobile? 2. Which country had the largest Internet growth (in %) in the
- 55. last five years? 3. How will most people connect to the Internet in the future? 4. What are two different applications of wearable technologies? 5. What are two different applications of collaborative technologies? 6. What capabilities do printable technologies have? 7. How will advances in wireless technologies and sensors make objects “findable”? 8. What is enhanced situational awareness? 9. What is a nanobot? 10. What is a UAV? 306 | Information Systems for Business and Beyond (2019) Exercises 1. If you were going to start a new technology business, which of the emerging trends do you think would be the biggest opportunity? Do some original research to estimate the market
- 56. size. 2. What privacy concerns could be raised by collaborative technologies such as Waze? 3. Do some research about the first handgun printed using a 3-D printer and report on some of the concerns raised. 4. Write up an example of how IoT might provide a business with a competitive advantage. 5. How do you think wearable technologies could improve overall healthcare? 6. What potential problems do you see with a rise in the number of autonomous cars? Do some independent research and write a two-page paper that describes where autonomous cars are legal and what problems may occur. 7. Seek out the latest presentation by Mary Meeker on “Internet Trends” (if you cannot find it, the video from 2018 is available at Mary Meeker). Write a one-page paper describing what the top three trends are, in your opinion.
- 57. 8. Select a business enterprise of interest to you, one that you may pursue following graduation. Select one or more of the technologies listed in this chapter, then write a one or two page paper about how you might use that technology to gain a competitive advantage. Chapter 13: Trends in Information Systems | 307 https://www.youtube.com/results?search_query=mary+meeker+i nternet+trends+2018 Index Below are listed terms that can be found in this text. The terms are indexed by chapter and page. For example, “12-254” indicates that the term can be found in chapter 12 on page 254. Please also note that page numbers may vary based upon how you are reading this text! Acceptable User Policy, 12-254
- 58. Access control, 6-127 Agile methodologies, 10-205 Altair 8800, 1-20 Apple II, 1-20 Application software, 1-16, 3-57 ARPA Net, 1-225-104 Assembly language, 10-210 Authentication, 6-125 Autonomous devices, 13-289 Availability, 6-125 Backups, 6-131 Berners-Lee, Tim, 1-22 Big Data, 4-91, 4-93 Binary, 2-33, -34 Binary prefixes, 2-36 Biometrics, 6-126 Bit, 2-33 Bitcoin, 11-245
- 59. Blockchain, 11-244 Bluetooth, 2-43, 5-114 Brynjolfson, Eric, 7-146 Build v. buy, 10-218 Bus, 2-39 Business Analytics, 4-98 Business Intelligence, 4-98 Index | 309 Business process, 8-163 Business Process Management (BPM), 7-153, 8-168 Business process re-engineering, 8-170 Byte, 2-33</p> Cambridge Analytica, 12-251 Career paths, 9-189 Carr, Nicholas, 1-12, 2-26, 7-147 CASE tools, 10-215 Castells, Manuel, 11-233
- 60. Cellphone abroad, 5-114 Central Processing Unit (CPU), 2-36, video 2-37, multi-core 2- 45 Certifications, 9-190 Change management, 10-223 Chief Information Officer (CIO), 9-186 Client-server, 1-21, 5-116 Cloud computing, 1-25, 3-68, 5-118 Collaborative systems, 7-155, 13-283 Code of ethics, 12-252 Commoditization, 2-50 Competitive advantage, 1-13, 2-26, 7-147, 7-153, 7-158 Compiled v. interpreted, 10-213 Components, 1-14 Computer engineer, 9-183 Computer operator, 9-185 Confidentiality, 6-124 Copyright, 12-256
- 61. Creative Commons, 12-261 Cross platform development, 10-221 Customer Relationship Management (CRM), 3-65 Data dictionary, 4-93 Data-Information-Knowledge-Wisdom, 4-77 Data integrity, 4-86 Data mining, 4-96, sidebar, 4-97 Data privacy, 12-251 Data types, 4-83 310 | Information Systems for Business and Beyond (2019) Data warehouse, 4-93, benefits, 4-95 Database, 4-78 Database administrator, 9-185 Database, enterprise, 4-91 Database spreadsheet sidebar, 4-85 Database Management System (DBMS), 4-90 Database, Relational, 4-78
- 62. Decimal numbering system, 2-34 Decision Support Systems (DSS), 7-156 Developer, 9-183 Digital devices, 2-33 Digital divide, 11-240 Digital Millennium Copyright Act, 12-260 Disintermediation, 1-23 Domain name, 5-107 DNS, 5-107 Do Not Track, 12-273 Dot-comm bubble, 1-235, 5-109 Double Data Rate (DDR), 2-40 Eclipse IDE, 3-61 Electronic Data Interchange (EDI), 7-154 Email, 5-110 Encryption, 6-128 End-user computing, 10-220 Enterprise Resource Planning (ERP), 1-21, 3-64, 8-166
- 63. Eras, business computing, 1-25 Ethics, 12-250 Extranet, 5-117 Facebook, 11-251, 13-280 Fair use, 12-258 Family Educational Rights and Privacy Act, 12-271 Fernandes, Benjamin, 11-245 Findable, 13-286 Firewalls, 6-132 First sale doctrine, 12-257 Index | 311 Ford, Henry, 12-250 Friedman, Thomas, 11-234 Gantt chart, 9-188 General Data Protection Regulation, 12-272 Global firm, 11-236 Globalization, 11-232
- 64. Ghemawat, Pankaj, 11-236 Hammer, Michael, 8-170 Hard disk, 2-41 Hardware, 1-15, 2-32 Health Insurance Portability and Accountability Act, 12-271 Huang’s Law, 2-38 Implementation Methodologies, 10-222 Information security triad, 6-124 Information systems, 1-14 Information systems employment, 9-180 Integrity, 6-124 Intellectual property, 12-255 Internet speed, 11-239 Internet usage statistics, 11-233 Intrusion Detection System (IDS), 6-133 IBM-PC, 1-20 Integrated circuits, 2-45 Internet, 1-22, internet and www, 5-111, high speed, 5-111
- 65. Internet of Things (IoT), 2-49, 13-286, install, 13-287 IP address, 5-106 Integrated Development Environment (IDE), 10-214 Internet user worldwide, 5-108 Intranet, 5-116 Isabel, 7-157 ISO certification, 8-174 IT doesn’t matter, 7-147 Key-Value database, 4-89 Kim, Paul, 11-243 Knowledge Management (KM), 4-98 312 | Information Systems for Business and Beyond (2019) Laptop, 1-12 Lean methodologies, 10-207 Linux, 3-56 Local Area Network (LAN), 1-21 Machine code, 10-209
- 66. Mainframe, 1-18 Manufacturing Resource Planning (MRP), 1-19 Metadata, 4-92 Metcaffe’s Law, 5-119 Microsoft Excel, 3-57 Mobile applications, 3-67, building, 10-221, cross platform, 10- 221 Mobile phone users worldwide, 13-280 Mobile networking, 5-113 Mobile security, 6-136 Mobile technology trends, 13-282 Motherboard, 2-39 Moore’s Law, 2-37