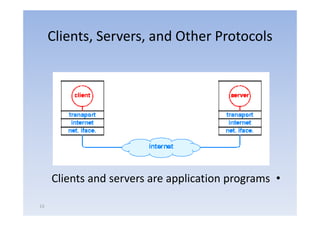
Networking principles involve the transport layer and application layer. The transport layer handles basic communication and reliability, while the application layer provides abstractions like files and services.
The network transfers bits and operates at the application's request, while applications determine what to send, when to send it, where to send it, and the meaning of the bits.
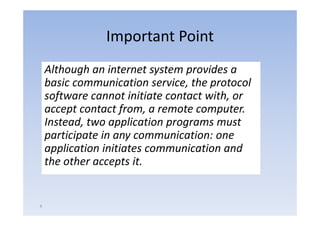
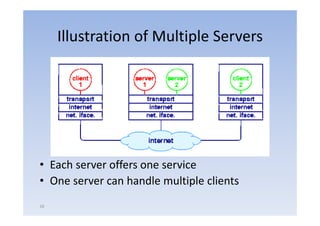
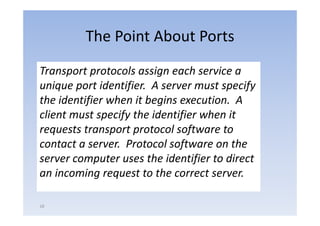
All network applications use a client-server paradigm, where a server waits passively for contact from an active client. A client initiates communication with one server at a time, while a server can handle multiple clients simultaneously. Concurrency allows servers to handle multiple requests without clients waiting.