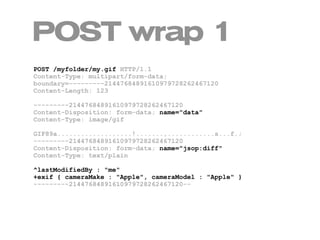
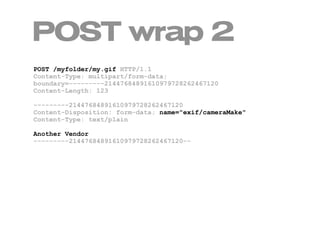
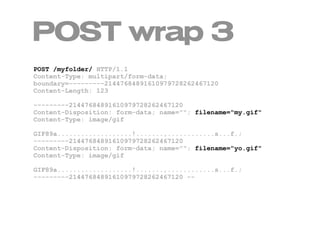
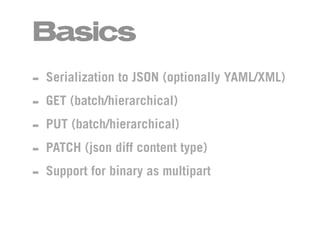
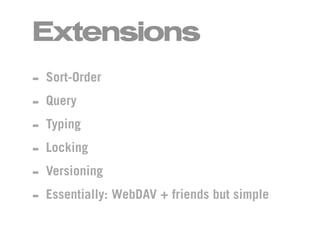
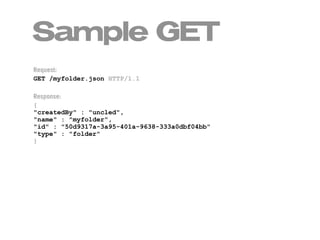
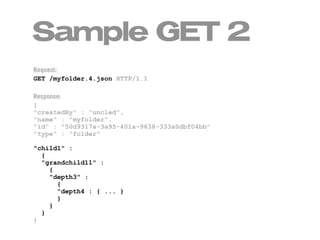
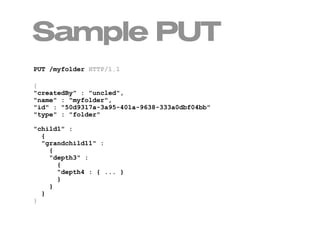
JSOP is a proposed browser-enabled HTTP-based protocol for efficiently exchanging fine-grained information. It involves serializing data to JSON, supports GET, PUT, and PATCH requests, and allows hierarchical resources and binary data. Sample requests and responses are provided to demonstrate retrieving and updating folder structures containing documents. PATCH requests use a JSON diff format to specify changes. Resources can also be manipulated via multipart POST requests wrapping data and diff payloads.



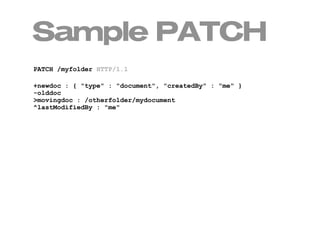

![PATCH diff
diff ::= members
members ::= pair | pairs
pair ::= key [ " : " value ]
pairs ::= pair line-end pair | pair line-end pairs
line-end ::= "rn" | "n" | "r"
key ::= opchar id
opchar ::= "+" | "^" | "-" | ">"
id ::= * identification url (path | id) *
value ::= value+ | value- | value^ | value>
value+ ::= * a JSON object *
value- ::= ""
value^ ::= * any JSON value except JSON object *
value> ::= id](https://image.slidesharecdn.com/jsop-100806071201-phpapp02/85/JSOP-in-60-seconds-11-320.jpg)