JS2 Computer Studies Examination (Third Term)
•Download as DOCX, PDF•
1 like•2,171 views
This document appears to be an exam for a Computer Studies class. It contains questions testing knowledge of computer and internet concepts. The exam has four sections - objectives with multiple choice questions, three theory questions requiring explanations of concepts, and a final section on responsible computer and internet use. Some of the concepts examined include the internet, websites, email, computer networks, data transmission, and abuses/responsible uses of technology.
Report
Share
Report
Share
Recommended
Js1 computer studies examination (Third Term)

This is the third term examination for junior secondary one
JSS2 COMPUTER STUDIES EXAMINATION (FIRST TERM)

This is my first term examination for JSS2. It is well detailed as it covers every part of the scheme.
S.S.2 Computer Studies 3rd Term Examination

Senior Secondary School Two Examination Computer Studies (Third Term)
JSS1 COMPUTER STUDIES EXAMINATION (FIRST TERM)

This is my first term Examination questions for Junior Secondary School One popularly known as JSS1. Each questions are detailed as it covers the whole scheme for the first term.
SS1 Data Processing Examination with Test of Practical (Third Term)

This is the third term examination for data processing including Test of Practical
S.S.1 Computer Studies 3rd Term Examination

Senior Secondary School One Examination Computer Studies (Third Term)
SS2 Data Processing Examination with Test of Practicals (Third Term)

This is the third term for data processing ss2 with Test of Practical
S2 DATA PROCESSING FIRST TERM C.A 2

This is the Continuous Assessment Test for SS2 DP with Test of Practicals included. It is accurately measured so that more than one students can get a copy from a single print out.
Recommended
Js1 computer studies examination (Third Term)

This is the third term examination for junior secondary one
JSS2 COMPUTER STUDIES EXAMINATION (FIRST TERM)

This is my first term examination for JSS2. It is well detailed as it covers every part of the scheme.
S.S.2 Computer Studies 3rd Term Examination

Senior Secondary School Two Examination Computer Studies (Third Term)
JSS1 COMPUTER STUDIES EXAMINATION (FIRST TERM)

This is my first term Examination questions for Junior Secondary School One popularly known as JSS1. Each questions are detailed as it covers the whole scheme for the first term.
SS1 Data Processing Examination with Test of Practical (Third Term)

This is the third term examination for data processing including Test of Practical
S.S.1 Computer Studies 3rd Term Examination

Senior Secondary School One Examination Computer Studies (Third Term)
SS2 Data Processing Examination with Test of Practicals (Third Term)

This is the third term for data processing ss2 with Test of Practical
S2 DATA PROCESSING FIRST TERM C.A 2

This is the Continuous Assessment Test for SS2 DP with Test of Practicals included. It is accurately measured so that more than one students can get a copy from a single print out.
JSS3 COMPUTER STUDIES EXAMINATION (FIRST TERM)

This is my first term examination for JSS3. It comprises of two parts, each part having 60 obj questions. This is intended to prepare them extensively for their upcoming BECE Examination. Which comprises of the things they have learnt from JS1 to JS3
SS1 DATA PROCESSING EXAMINATION (FIRST TERM)

This is my first term examination for SS1 It is well detailed as it covers every part of the scheme. it contains three parts namely; Objective, Theory and Test of Practical a normal waec examination.
SS3 DATA PROCESSING PRACTICAL EXAMINATION (FIRST TERM)

This is the first term SS3 Data Processing Practical Examination strictly on Graphics (Corel Draw). It is NECO and WAEC SSCE standard question to prepare the student.
JS3 COMPUTER STUDIES FIRST TERM C.A 2

This questions are to prepare them for computer Studies BECE for both Neco and Junior Waec. The more you prepare with these questions the more they get ready for the actual Examination.
SS1 DATA PROCESSING PRACTICAL EXAMINATION (FIRST TERM)

This is the first term S1 Data Processing Practical Examination strictly on Microsoft Word. It is NECO and WAEC SSCE standard question to prepare the student.
SS2 DATA PROCESSING EXAMINATION (FIRST TERM)

This is my first term examination for ss2. It is well detailed as it covers every part of the scheme. It contains three parts namely; Objective, Theory, Test of Practical a normal standard WAEC Examination.
SS3 DATA PROCESSING EXAMINATION (FIRST TERM)

This is my first term examination for SS3 D.P. It is well detailed as it covers every part of the scheme. It contains three parts namely; Objective, Theory, Test of Practical a normal standard WAEC Examination.
JS1 COMPUTER STUDIES FIRST TERM C.A 2

This is the second Continuous Assessment Test for J1 first term. It arranged in a format to make it easy for students to use. four student to one print out then you can cut it off. The measurements are accurate if you want to use exactly my questions to set for your students.
SS2 DATA PROCESSING PRACTICAL EXAMINATION (FIRST TERM)

This is the first term S2 Data Processing Practical Examination strictly on Microsoft Access (Database). It is NECO and WAEC SSCE standard question to prepare the student.
S1 DATA PROCESSING FIRST TERM C.A 2

This is the Continuous Assessment Test for SS1 Data Processing and in this C.A 2 I included Test of Practical so that the students can get use to how this test of practical is been written on time. Our School is the first to introduce it in C.A and Examination and I im proud to say I initiated this idea. They accurately measure to economize and make copies available.
S3 Data Processing Pre-Waec Examination (First Half)

This is the First Half Examination of Pre-WAEC Examination on Data Processing for SS3 this is to prepare them extensively for their upcoming WAEC Examination.
S3 DATA PROCESSING FIRST TERM PRE-WAEC (2ND HALF EXAMINATION)

This is the second half of their Examination in preparation for their upcoming Waec data processing. And have been preparing my students extensively with practicals and the syllabus.
JS2 COMPUTER STUDIES FIRST TERM C.A 2

This is the first term Continuous Assessment Test for JS2. It is arranged in a way that economizes for the school. Where you have one print out for four students and all you have to do is cut it off. They are accurately measured.
A Data Processing Presentation on Graphics

This is a presentation teaching the students and audience about importance of graphics
Solved Question Paper of Computer Operator Examination Conducted by EPF 2016

This is the solved question paper of Computer Operator Examination conducted by Employee Provident Fund (Karmachari Sanchaya Kosh) for 2016.
Solved by: Suresh Khanal
More Related Content
What's hot
JSS3 COMPUTER STUDIES EXAMINATION (FIRST TERM)

This is my first term examination for JSS3. It comprises of two parts, each part having 60 obj questions. This is intended to prepare them extensively for their upcoming BECE Examination. Which comprises of the things they have learnt from JS1 to JS3
SS1 DATA PROCESSING EXAMINATION (FIRST TERM)

This is my first term examination for SS1 It is well detailed as it covers every part of the scheme. it contains three parts namely; Objective, Theory and Test of Practical a normal waec examination.
SS3 DATA PROCESSING PRACTICAL EXAMINATION (FIRST TERM)

This is the first term SS3 Data Processing Practical Examination strictly on Graphics (Corel Draw). It is NECO and WAEC SSCE standard question to prepare the student.
JS3 COMPUTER STUDIES FIRST TERM C.A 2

This questions are to prepare them for computer Studies BECE for both Neco and Junior Waec. The more you prepare with these questions the more they get ready for the actual Examination.
SS1 DATA PROCESSING PRACTICAL EXAMINATION (FIRST TERM)

This is the first term S1 Data Processing Practical Examination strictly on Microsoft Word. It is NECO and WAEC SSCE standard question to prepare the student.
SS2 DATA PROCESSING EXAMINATION (FIRST TERM)

This is my first term examination for ss2. It is well detailed as it covers every part of the scheme. It contains three parts namely; Objective, Theory, Test of Practical a normal standard WAEC Examination.
SS3 DATA PROCESSING EXAMINATION (FIRST TERM)

This is my first term examination for SS3 D.P. It is well detailed as it covers every part of the scheme. It contains three parts namely; Objective, Theory, Test of Practical a normal standard WAEC Examination.
JS1 COMPUTER STUDIES FIRST TERM C.A 2

This is the second Continuous Assessment Test for J1 first term. It arranged in a format to make it easy for students to use. four student to one print out then you can cut it off. The measurements are accurate if you want to use exactly my questions to set for your students.
SS2 DATA PROCESSING PRACTICAL EXAMINATION (FIRST TERM)

This is the first term S2 Data Processing Practical Examination strictly on Microsoft Access (Database). It is NECO and WAEC SSCE standard question to prepare the student.
S1 DATA PROCESSING FIRST TERM C.A 2

This is the Continuous Assessment Test for SS1 Data Processing and in this C.A 2 I included Test of Practical so that the students can get use to how this test of practical is been written on time. Our School is the first to introduce it in C.A and Examination and I im proud to say I initiated this idea. They accurately measure to economize and make copies available.
S3 Data Processing Pre-Waec Examination (First Half)

This is the First Half Examination of Pre-WAEC Examination on Data Processing for SS3 this is to prepare them extensively for their upcoming WAEC Examination.
S3 DATA PROCESSING FIRST TERM PRE-WAEC (2ND HALF EXAMINATION)

This is the second half of their Examination in preparation for their upcoming Waec data processing. And have been preparing my students extensively with practicals and the syllabus.
JS2 COMPUTER STUDIES FIRST TERM C.A 2

This is the first term Continuous Assessment Test for JS2. It is arranged in a way that economizes for the school. Where you have one print out for four students and all you have to do is cut it off. They are accurately measured.
A Data Processing Presentation on Graphics

This is a presentation teaching the students and audience about importance of graphics
Solved Question Paper of Computer Operator Examination Conducted by EPF 2016

This is the solved question paper of Computer Operator Examination conducted by Employee Provident Fund (Karmachari Sanchaya Kosh) for 2016.
Solved by: Suresh Khanal
What's hot (20)
SS3 DATA PROCESSING PRACTICAL EXAMINATION (FIRST TERM)

SS3 DATA PROCESSING PRACTICAL EXAMINATION (FIRST TERM)
SS1 DATA PROCESSING PRACTICAL EXAMINATION (FIRST TERM)

SS1 DATA PROCESSING PRACTICAL EXAMINATION (FIRST TERM)
SS2 DATA PROCESSING PRACTICAL EXAMINATION (FIRST TERM)

SS2 DATA PROCESSING PRACTICAL EXAMINATION (FIRST TERM)
S3 Data Processing Pre-Waec Examination (First Half)

S3 Data Processing Pre-Waec Examination (First Half)
S3 DATA PROCESSING FIRST TERM PRE-WAEC (2ND HALF EXAMINATION)

S3 DATA PROCESSING FIRST TERM PRE-WAEC (2ND HALF EXAMINATION)
Solved Question Paper of Computer Operator Examination Conducted by EPF 2016

Solved Question Paper of Computer Operator Examination Conducted by EPF 2016
Similar to JS2 Computer Studies Examination (Third Term)
Computer Networking Multiple Choice Questions

A computer network or data network is a telecommunications network which allows computers to exchange data. In computer networks, networked computing devices exchange data with each other using a data link. The connections between nodes are established using either cable media or wireless media.
Computer Networks Mcqs.pdf

Computer Networks Multiple Choice Questions (MCQs) cover a wide range of topics related to the fundamental principles, protocols, and technologies that govern the communication and connectivity of computer systems. These questions are designed to test the knowledge and understanding of individuals in the field of computer networking. Below is a description outlining the common themes covered by MCQs in this domain:
Network Basics:
MCQs may assess the understanding of basic networking concepts such as nodes, links, topology, and communication models.
Questions might cover the differences between local area networks (LANs) and wide area networks (WANs), as well as their applications.
Protocols and Standards:
Questions often focus on network protocols, such as TCP/IP, HTTP, FTP, and their roles in data transmission.
Familiarity with networking standards and organizations like the IEEE and the Internet Engineering Task Force (IETF) is commonly tested.
Networking Devices:
MCQs may inquire about the functionality of networking devices like routers, switches, hubs, and their roles in network infrastructure.
Understanding the purpose and operation of devices like modems and gateways may also be examined.
IP Addressing and Subnetting:
Questions might cover topics related to IP addressing, subnetting, and the differences between IPv4 and IPv6.
Subnet masks, network classes, and CIDR notation could be focal points in these questions.
Data Link Layer and Switching:
Understanding the data link layer and its protocols (e.g., Ethernet) is often tested.
Questions may address concepts related to MAC addresses, switching techniques, and VLANs (Virtual Local Area Networks).
Routing and Routing Protocols:
Questions may assess knowledge of routing algorithms and protocols such as RIP, OSPF, and BGP.
Understanding the routing table, routing metrics, and the role of routers in forwarding data is essential.
Wireless Networking:
Topics related to wireless communication standards (e.g., Wi-Fi), security protocols, and frequency bands may be covered.
Questions might address challenges and solutions in wireless networking environments.
Network Security:
MCQs may focus on security protocols, firewalls, encryption, and authentication mechanisms.
Understanding common security threats and countermeasures is typically part of these questions.
Network Management and Troubleshooting:
Questions may assess knowledge of network management protocols (e.g., SNMP) and troubleshooting techniques.
Understanding tools for monitoring, diagnosing, and resolving network issues is crucial.
Emerging Technologies:
Some MCQs may explore contemporary topics such as cloud computing, virtualization, and the Internet of Things (IoT) in the context of networking.
Challenge Examination1) In which era were only the U.S. government.docx

Challenge Examination
1) In which era were only the U.S. government, colleges, and universities able to
access the Internet?
a. 1960s
b. 1970s
c. 1980s
d. 1990s
2) Application software includes all of the following EXCEPT ________ software.
a. word-processing
b. Web browser
c. system
d. e-mail
3) Output refers to:
a. displaying the results of the processing operation so that people can undestand
it.
b. information that needs further computer activity in order to have meaning to
people.
c. performing operations on the input data.
d. sending the results of computer processing to a permanent location.
4) Which of the following device types holds the programs and data that the
computer uses?
a. Communication devices
b. Input devices
c. Output devices
d. Storage devices
5) Which of the following is often considered the fi fth operation in the information-
processing cycle?
a. Communications
b. E-commerce
c. Ethics
d. Analysis
Challenge Examination
6) Network computers have limited resources in all the following areas EXCEPT:
a. storage.
b. processing.
c. memory.
d. connectivity.
7) What type of systems are the ones on which human lives depend?
a. Health-dependent
b. Life-and-death-critical
c. Safety-critical
d. Mission-critical
8) Which of the following safety-critical airline computer systems requires the
highest level of quality standards?
a. Reservation
b. Passenger list and seating assignments
c. Passenger entertainment and communication
d. Air traffi c control
9) More than ________ computers, monitors, and TVs become obsolete each
year.
a. 10 million
b. 100 million
c. 10 billion
d. 100 billion
10) What is a school’s code of conduct for computers users called?
a. Computer usage agreement
b. Acceptable use policy
c. Computer conduct agreement
d. Associated usage principals
11) Which of the following would NOT be considered correct netiquette?
a. Reading the Frequently Asked Questions (FAQ) document posted on a mailing
list prior to submitting a question
b. Avoiding slang and jokes in professional e-mail
c. Using all capital letters in an e-mail response
d. Learning and using Internet Relay Chat (IRC) abbreviations in the same way
as other users
Challenge Examination
12) Which of the following statements is TRUE concerning computer games and
violence?
a. The games industry has taken responsibility to minimize the violence in their
games.
b. Computer games are becoming more violent.
c. Playing computer games led to the Columbine tragedy.
d. Computer games cause players to be more violent and aggressive.
13) At the heart of every computer code of ethics is to:
a. eliminate all potential computer bugs.
b. honor property rights and individual privacy.
c. avoid harm and protect human life.
d. fi ght software piracy.
14) Which of the following is NOT considered plagiarism?
a. Purchase a term paper from an Internet company and use it as the basis of
your own work for a college course.
b. Paste a paragraph of text from a Web page into an e.
1) In which era were only the U.S. government, colleges, and unive.docx

1) In which era were only the U.S. government, colleges, and universities able to access the Internet?
a. 1960s b. 1970s c. 1980s d. 1990s
2) Application software includes all of the following EXCEPT ________ software.
a. word-processing b. Web browser c. system d. e-mail
3) Output refers to:
a. displaying the results of the processing operation so that people can under stand it. b. information that needs further computer activity in order to have meaning to people. c. performing operations on the input data. d. sending the results of computer processing to a permanent location.
4) Which of the following device types holds the programs and data that the computer uses?
a. Communication devices b. Input devices c. Output devices d. Storage devices
5) Which of the following is often considered the fi fth operation in the informa- tion-processing cycle?
a. Communications b. E-commerce c. Ethics d. Analysis
6) Network computers have limited resources in all the following areas EXCEPT:
a. storage. b. processing. c. memory. d. connectivity.
7) What type of systems are the ones on which human lives depend?
a. Health-dependent b. Life-and-death-critical c. Safety-critical d. Mission-critical
8) Which of the following safety-critical airline computer systems requires the highest level of quality standards?
a. Reservation b. Passenger list and seating assignments c. Passenger entertainment and communication d. Air traffi c control
9) More than ________ computers, monitors, and TVs become obsolete each year.
a. 10 million b. 100 million c. 10 billion d. 100 billion
10) What is a school’s code of conduct for computers users called?
a. Computer usage agreement b. Acceptable use policy c. Computer conduct agreement d. Associated usage principals
11) Which of the following would NOT be considered correct netiquette?
a. Reading the Frequently Asked Questions (FAQ) document posted on a mailing list prior to submitting a question b. Avoiding slang and jokes in professional e-mail c. Using all capital letters in an e-mail response d. Learning and using Internet Relay Chat (IRC) abbreviations in the same way as other users
12) Which of the following statements is TRUE concerning computer games and violence?
a. The games industry has taken responsibility to minimize the violence in their games. b. Computer games are becoming more violent. c. Playing computer games led to the Columbine tragedy. d. Computer games cause players to be more violent and aggressive.
13) At the heart of every computer code of ethics is to:
a. eliminate all potential computer bugs. b. honor property rights and individual privacy. c. avoid harm and protect human life. d. fi ght software piracy.
14) Which of the following is NOT considered plagiarism?
a. Purchase a term paper from an Internet company and use it as the basis of you.
Page1 of 101. Prior tocellular radio, mobile radio and telep.docx

Page1 of 10
1. Prior tocellular radio, mobile radio and telephoneservices required:
A. a high-power transmitter/receiver
B. multiple transmitters/receivers
C. only one or two dedicated channels
D. that many channels be used, which exceed the frequency capacity
2. When using cellular networks, __________.
A. a single base station can serve multiple cells
B. adjacent cells must use the same frequencies
C. adjacent cells are assigned different frequencies
D. non-adjacent cells are assigned different frequencies
3. Theideal design for cells in a cellular network is a hexagonal shape because _____.
A. this makes enforcement of shapes easier
B. this is the easiest to implement
C. this makes all frequencies available to all cells
D. this makes the distance to all adjacent cells thesame
4. When a mobile unit moves, it may connect with a different base station. This action is called
____________.
A. a handoff
C. a reconfiguration
B. a transfer
D. a dropped signal
5. Which of the following is NOT one of theways that frequency spectrum can be divided among
active users?
A. frequency division multiple access
C. code division multiple access
B. time division multipleaccess
D. cell division multiple access
6. Because of the limited frequencies available, a key design element of any cellular system is to
___________.
A. usesmall cells
B. employ multipleaccess
C. limit the number of users at one time
D. use as many frequencies as possible
7. The Wireless Application Protocol (WAP) is:
A. proprietary protocol developed in theUSA for wireless security
B. dependent on the specific network technologies employed
C. an Internet standard that replaces HTML, HTTP, and XML
D. designed to overcome many of the limitations hindering acceptance of mobile data services
Page2 of 10
Page3 of 10
8. Which of the following is NOT one of thecomponents of the WAP specification?
A. A framework for wireless telephony applications
B. A full-featured communications protocol stack
C. A programming model based on the WWW
D. A markup languageadhering to XML
9. The WAP Programming Model uses a ________that acts as a proxy server for thewireless domain.
A. translator
C. gateway
B. WAP server
D. decoder
10. For a given system, multiple access is based on _______.
A. TDMA
C. CDMA
B. FDMA
D. all of the above
11. Important objectives of computer security include:
A. confidentiality
C. availability
B. integrity
D. all of the above
12. One type of attack on the security of a computer system or network that impacts the availability
of a system (e.g. destruction of a resourcein the system) is referred to as ___________.
A. incapacitation
C. modification
B. interception
D. all of the above
13. Thetype of attack on communications lines and networks known as traffic analysis belongs to the
general category of ____________.
A. active attacks
C.
LS 2 15 Advances in Communication Technology

Learning Strand 2: Scientific Literacy and Critical Thinking Skills
Similar to JS2 Computer Studies Examination (Third Term) (20)
Challenge Examination1) In which era were only the U.S. government.docx

Challenge Examination1) In which era were only the U.S. government.docx
1) In which era were only the U.S. government, colleges, and unive.docx

1) In which era were only the U.S. government, colleges, and unive.docx
Lesson 4 communication and computer network (123 kb)

Lesson 4 communication and computer network (123 kb)
Page1 of 101. Prior tocellular radio, mobile radio and telep.docx

Page1 of 101. Prior tocellular radio, mobile radio and telep.docx
17._CS-12-Networking-1_Evolution_of_Network_1.docx

17._CS-12-Networking-1_Evolution_of_Network_1.docx
More from Ejiro Ndifereke
Sale For E-Note and Exam Questions For Secondary Schools.pdf

- As a school owner do you need E-Note for your teachers in all subject well search no more im here for you at an affordable price you have access to all subject covering every term (first term, second term and third term)
- As a teacher do you E-Note for your subject accross all terms i got you covered
- As a teacher are you looking for examination question for all terms including Continuous Assessment Test (CAT)
A Presentation on Spreadsheet

This is a lecture presentation on spreadsheet using (Microsoft Excel as a case study) to the students and audience
S2 Data Processing C.A 1

This is the Continuous Assessment Test for SS2 Data Processing. Included in this First C.A 1 Test is Test of Practical so as to perfect their skill in writing T.O.P for their WAEC Examination they are going to write.
S1 Data Processing C.A 1

This is the Continuous Assessment Test For Data Processing for Senior Secondary One also known as SS1 First Term Work, in this test I included Test of Practical so as to prepare them early for their Waec Examiniation
J2 Computer Studies C.A 1

This is the Continuous Assessment Test for Junior Secondary School Two for Computer Studies First Term work.
This is uploaded so that other Computer Educator can make use of or at the very least a guide to set a standard question.
J1 Computer Studies C.A 1

This is the Continuous Assessment Test for Junior Secondary One First Term work.
Database Management

This is a slide presentation on Database Management System.
Note: All this slide are design by me and licensed under the school I'm currently teaching "Good Shepherd Schools"
Ways of Misusing The Computer System

This is a slide presentation on ways people can misuse the computer on the internet.
I am currently an ICT Educator at Good Shepherd Schools Lagos State, Nigeria.
Note: I will be uploading more powerpoint presentation in my field so ensure your following me to get updated thanks.
More from Ejiro Ndifereke (8)
Sale For E-Note and Exam Questions For Secondary Schools.pdf

Sale For E-Note and Exam Questions For Secondary Schools.pdf
Recently uploaded
Palestine last event orientationfvgnh .pptx

An EFL lesson about the current events in Palestine. It is intended to be for intermediate students who wish to increase their listening skills through a short lesson in power point.
ESC Beyond Borders _From EU to You_ InfoPack general.pdf

ESC Beyond Borders _From EU to You_ InfoPack general.pdfFundacja Rozwoju Społeczeństwa Przedsiębiorczego
Wolontariat grupowyStudents, digital devices and success - Andreas Schleicher - 27 May 2024..pptx

Andreas Schleicher presents at the OECD webinar ‘Digital devices in schools: detrimental distraction or secret to success?’ on 27 May 2024. The presentation was based on findings from PISA 2022 results and the webinar helped launch the PISA in Focus ‘Managing screen time: How to protect and equip students against distraction’ https://www.oecd-ilibrary.org/education/managing-screen-time_7c225af4-en and the OECD Education Policy Perspective ‘Students, digital devices and success’ can be found here - https://oe.cd/il/5yV
2024.06.01 Introducing a competency framework for languag learning materials ...

http://sandymillin.wordpress.com/iateflwebinar2024
Published classroom materials form the basis of syllabuses, drive teacher professional development, and have a potentially huge influence on learners, teachers and education systems. All teachers also create their own materials, whether a few sentences on a blackboard, a highly-structured fully-realised online course, or anything in between. Despite this, the knowledge and skills needed to create effective language learning materials are rarely part of teacher training, and are mostly learnt by trial and error.
Knowledge and skills frameworks, generally called competency frameworks, for ELT teachers, trainers and managers have existed for a few years now. However, until I created one for my MA dissertation, there wasn’t one drawing together what we need to know and do to be able to effectively produce language learning materials.
This webinar will introduce you to my framework, highlighting the key competencies I identified from my research. It will also show how anybody involved in language teaching (any language, not just English!), teacher training, managing schools or developing language learning materials can benefit from using the framework.
Unit 8 - Information and Communication Technology (Paper I).pdf

This slides describes the basic concepts of ICT, basics of Email, Emerging Technology and Digital Initiatives in Education. This presentations aligns with the UGC Paper I syllabus.
Instructions for Submissions thorugh G- Classroom.pptx

This presentation provides a briefing on how to upload submissions and documents in Google Classroom. It was prepared as part of an orientation for new Sainik School in-service teacher trainees. As a training officer, my goal is to ensure that you are comfortable and proficient with this essential tool for managing assignments and fostering student engagement.
How to Split Bills in the Odoo 17 POS Module

Bills have a main role in point of sale procedure. It will help to track sales, handling payments and giving receipts to customers. Bill splitting also has an important role in POS. For example, If some friends come together for dinner and if they want to divide the bill then it is possible by POS bill splitting. This slide will show how to split bills in odoo 17 POS.
The geography of Taylor Swift - some ideas

Geographical themes connected with Taylor Swift's ERAS tour - coming to the UK in June 2024
Welcome to TechSoup New Member Orientation and Q&A (May 2024).pdf

In this webinar you will learn how your organization can access TechSoup's wide variety of product discount and donation programs. From hardware to software, we'll give you a tour of the tools available to help your nonprofit with productivity, collaboration, financial management, donor tracking, security, and more.
Thesis Statement for students diagnonsed withADHD.ppt

Presentation required for the master in Education.
GIÁO ÁN DẠY THÊM (KẾ HOẠCH BÀI BUỔI 2) - TIẾNG ANH 8 GLOBAL SUCCESS (2 CỘT) N...

GIÁO ÁN DẠY THÊM (KẾ HOẠCH BÀI BUỔI 2) - TIẾNG ANH 8 GLOBAL SUCCESS (2 CỘT) N...Nguyen Thanh Tu Collection
https://app.box.com/s/4hfk1xwgxnova7f4dm37birdzflj806w1.4 modern child centered education - mahatma gandhi-2.pptx

Child centred education is an educational approach that priorities the interest, needs and abilities of the child in the learning process.
Ethnobotany and Ethnopharmacology ......

Ethnobotany and Ethnopharmacology:
Ethnobotany in herbal drug evaluation,
Impact of Ethnobotany in traditional medicine,
New development in herbals,
Bio-prospecting tools for drug discovery,
Role of Ethnopharmacology in drug evaluation,
Reverse Pharmacology.
How libraries can support authors with open access requirements for UKRI fund...

How libraries can support authors with open access requirements for UKRI funded books
Wednesday 22 May 2024, 14:00-15:00.
special B.ed 2nd year old paper_20240531.pdf

Instagram:-
https://instagram.com/special_education_needs_01?igshid=YmMyMTA2M2Y=
WhatsApp:-
https://chat.whatsapp.com/JVakNIYlSV94x7bwunO3Dc
YouTube:-
https://youtube.com/@special_education_needs
Teligram :- https://t.me/special_education_needs
Slide Shere :-
https://www.slideshare.net/shabnambano20?utm_campaign=profiletracking&utm_medium=sssite&utm_source=ssslideview
Recently uploaded (20)
ESC Beyond Borders _From EU to You_ InfoPack general.pdf

ESC Beyond Borders _From EU to You_ InfoPack general.pdf
Students, digital devices and success - Andreas Schleicher - 27 May 2024..pptx

Students, digital devices and success - Andreas Schleicher - 27 May 2024..pptx
2024.06.01 Introducing a competency framework for languag learning materials ...

2024.06.01 Introducing a competency framework for languag learning materials ...
Unit 8 - Information and Communication Technology (Paper I).pdf

Unit 8 - Information and Communication Technology (Paper I).pdf
Instructions for Submissions thorugh G- Classroom.pptx

Instructions for Submissions thorugh G- Classroom.pptx
Basic phrases for greeting and assisting costumers

Basic phrases for greeting and assisting costumers
Welcome to TechSoup New Member Orientation and Q&A (May 2024).pdf

Welcome to TechSoup New Member Orientation and Q&A (May 2024).pdf
Thesis Statement for students diagnonsed withADHD.ppt

Thesis Statement for students diagnonsed withADHD.ppt
GIÁO ÁN DẠY THÊM (KẾ HOẠCH BÀI BUỔI 2) - TIẾNG ANH 8 GLOBAL SUCCESS (2 CỘT) N...

GIÁO ÁN DẠY THÊM (KẾ HOẠCH BÀI BUỔI 2) - TIẾNG ANH 8 GLOBAL SUCCESS (2 CỘT) N...
1.4 modern child centered education - mahatma gandhi-2.pptx

1.4 modern child centered education - mahatma gandhi-2.pptx
How libraries can support authors with open access requirements for UKRI fund...

How libraries can support authors with open access requirements for UKRI fund...
JS2 Computer Studies Examination (Third Term)
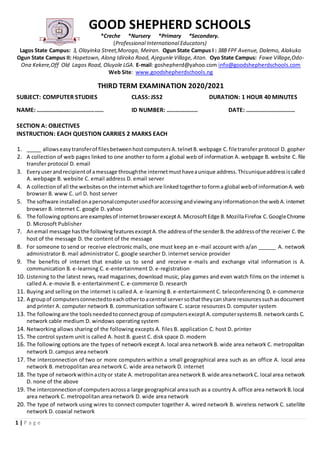
- 1. 1 | P a g e GOOD SHEPHERD SCHOOLS *Creche *Nursery *Primary *Secondary. (Professional International Educators) Lagos State Campus: 3, Olayinka Street,Moroga, Meiran. Ogun State Campus I : 38B FPF Avenue, Dalemo, Alakuko Ogun State Campus II: Hopetown, Along Idiroko Road, Ajegunle Village, Atan. Oyo State Campus: Fawe Village,Odo- Ona Kekere,Off Old Lagos Road, Oluyole LGA. E-mail: goshepherd@yahoo.com info@goodshepherdschools.com Web Site: www.goodshepherdschools.ng THIRD TERM EXAMINATION 2020/2021 SUBJECT: COMPUTER STUDIES CLASS: JSS2 DURATION: 1 HOUR 40 MINUTES NAME: ……………………………………… ID NUMBER: ………………… DATE: …………………………… SECTION A: OBJECTIVES INSTRUCTION: EACH QUESTION CARRIES 2 MARKS EACH 1. _____ allowseasytransferof filesbetweenhostcomputersA.telnetB.webpage C.filetransfer protocol D. gopher 2. A collection of web pages linked to one another to form a global web of information A. webpage B. website C. file transfer protocol D. email 3. Everyuserandrecipientof amessage throughthe internetmusthaveaunique address.Thisuniqueaddressiscalled A. webpage B. website C. email address D. email server 4. A collectionof all the websitesonthe internetwhichare linkedtogethertoforma global webof informationA.web browser B. www C. url D. host server 5. The software installedonapersonalcomputerusedforaccessingandviewinganyinformationonthe webA.internet browser B. internet C. google D. yahoo 6. The followingoptionsare examplesof internetbrowserexceptA.MicrosoftEdge B.MozillaFirefox C.GoogleChrome D. Microsoft Publisher 7. Anemail message hasthe followingfeaturesexceptA.the addressof the senderB.the addressof the receiver C.the host of the message D. the content of the message 8. For someone to send or receive electronic mails, one must keep an e-mail account with a/an ______ A. network administrator B. mail administrator C. google searcher D. internet service provider 9. The benefits of internet that enable us to send and receive e-mails and exchange vital information is A. communication B. e-learning C. e-entertainment D. e-registration 10. Listening to the latest news, read magazines,download music, play games and even watch films on the internet is called A. e-movie B. e-entertainment C. e-commerce D. research 11. Buying and selling on the internet is called A. e-learning B. e-entertainment C. teleconferencing D. e-commerce 12. A groupof computersconnectedtoeachothertoacentral serversothattheycanshare resourcessuchasdocument and printer A. computer network B. communication software C. scarce resources D. computer system 13. The followingare the toolsneededtoconnectgroup of computersexceptA.computersystemsB. networkcards C. network cable medium D. windows operating system 14. Networking allows sharing of the following excepts A. files B. application C. host D. printer 15. The control system unit is called A. host B. guest C. disk space D. modern 16. The following options are the types of network except A. local area networkB. wide area network C. metropolitan network D. campus area network 17. The interconnection of two or more computers within a small geographical area such as an office A. local area network B. metropolitan area network C. wide area network D. internet 18. The type of networkwithinacityor state A. metropolitanareanetwork B.wide areanetworkC. local area network D. none of the above 19. The interconnectionof computersacrossa large geographical areasuch as a country A.office area networkB.local area network C. metropolitan area network D. wide area network 20. The type of network using wires to connect computer together A. wired network B. wireless network C. satellite network D. coaxial network
- 2. 2 | P a g e 21. The type of network which does not employ the use of wire A. local area network B. wireless network C. wired network D. network antenna 22. ________ refers to the communication betweenmachines, computers inorder to increase the speed and ease the movementof informationfromoneplacetoanother A.datacommunication B.datatransmissionC.datainterference D. data movement 23. The mediumthroughwhichdataisconveyedtothe destinationfromthe source A.transmissionchannel B.receiver C. source D. electronic interface 24. The transmission that transmits one character at a time, it is also referred to as start – stop transmission A. asynchronous transmission B. synchronous transmission C. simplex transmission D. half duplex transmission 25. The transmission of data in one direction only A. synchronous transmission B. simplex transmission C. half duplex transmission D. full duplex transmission 26. The transmissionof datainboth directionandsimultaneouslyA.simplex transmissionB.half duplextransmission C. full duplex transmission D. all duplex transmission 27. The device used to extend transmissionsso that the signal can cover longer distances A. modem B. repeater C. demultiplexer D. router 28. The use of internettosteal someone’sideas,wordsandtransformingitintoyours A. piracy B.sendingspammails C. plagiarism D. creating and sending virus 29. Using the internetfor the purpose of trickingvictimsoutof theirmoney A. piracy B. internetfraud C. cyberbullying D. sending mails 30. The means of using the internet to harass or intimidate A. cyber bullying B. internet fraud C. plagiarism D. piracy SECTION B: THEORY ANSWER ALL QUESTIONS PLEASE!!! QUESTION 1 A. Explain the following concept i. Internet ii. WWW iii. E-mail iv. Website B. Usingthis email address ejedafetaejiron@gmail.com label the fourparts. C. Give the full meaning of the following acronym i. .com ii. .gov iii. .edu iv. .net v. .mil D. identifythe followingpartsusingthiswebsite address https://www.mancity.com QUESTION 2 A. Write the stepsonhow to sendane-mail message B. Write the steps in creating an e-mail account specify the server. C. List and explain three benefits of the internet? D. What is a Computer Network and Mentionthe three types of Network QUESTION 3 A. Mention three abuses of internet an explain one B. Mentionandexplainthe methodsof networking C. What isData Communication,mentionfourmodesof data transmissionandexplaintwo D. Mention four data transmission equipment QUESTION 4 A. Mentionfive responsibleuse of computer B. Mentionthree precautionsthatmustbe takenwhen usingthe computersystem C. Mentionthree responsiblewaysof usingthe internet D. Mentionfive areasof Misuse of computersand internet
