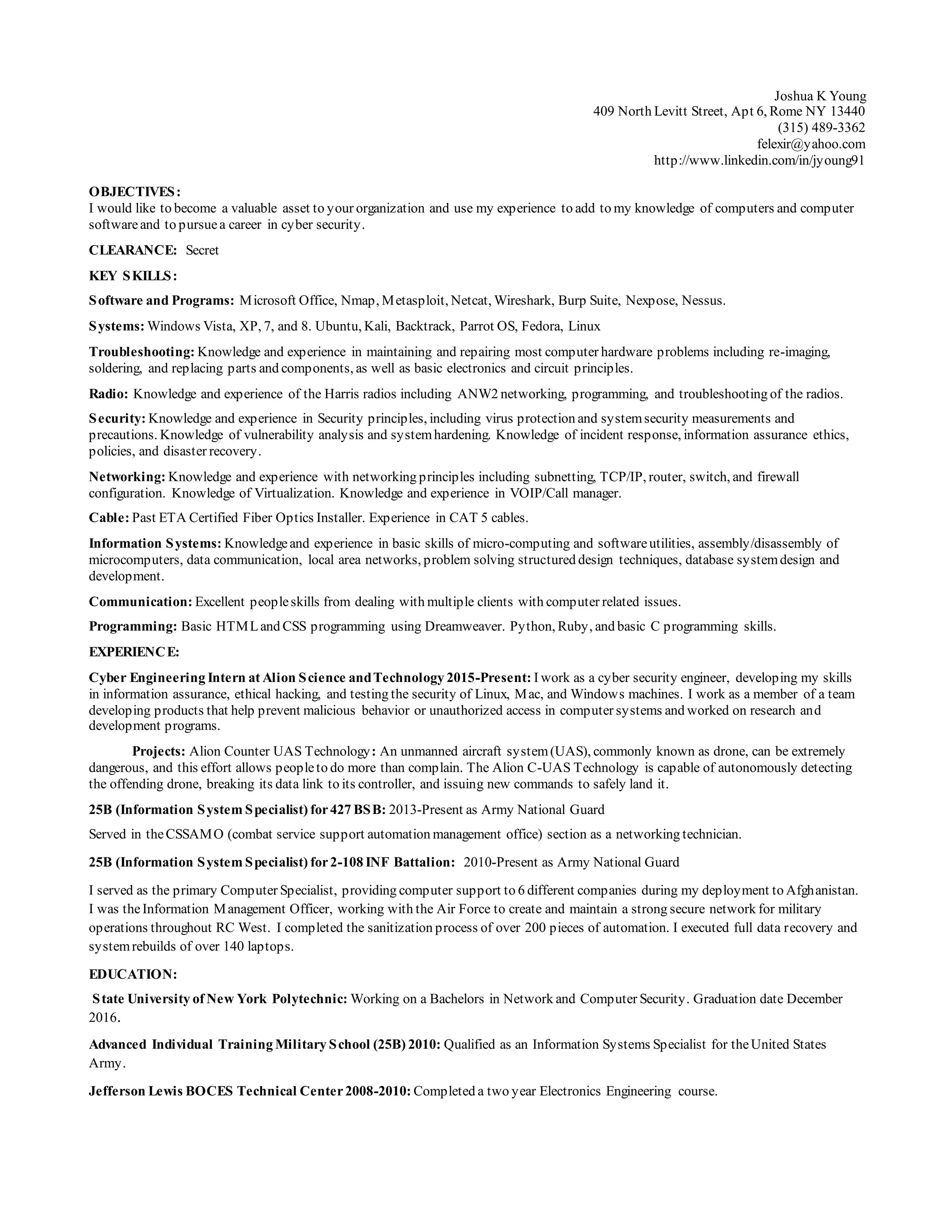
Joshua K Young is seeking a position that allows him to utilize his experience in cyber security. He has skills in various software programs, operating systems, and networking. His experience includes internships in cyber engineering and serving in the Army National Guard as an information systems specialist. He is currently working towards a bachelor's degree in network and computer security.