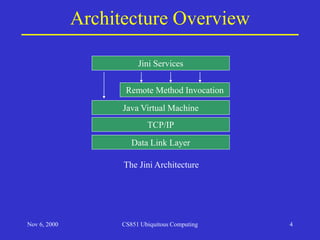
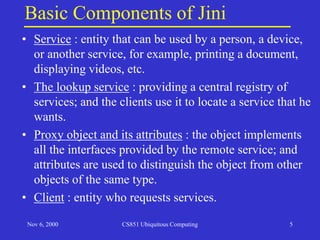
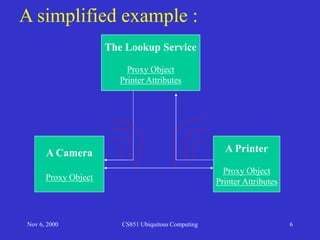
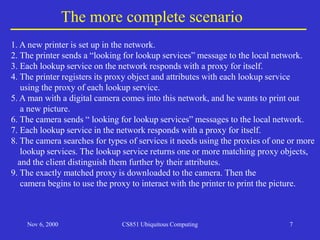
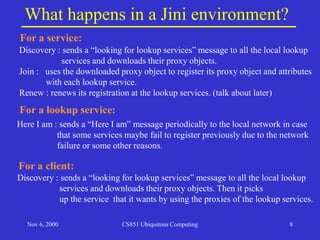
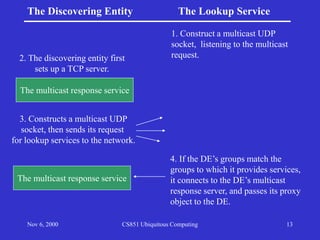
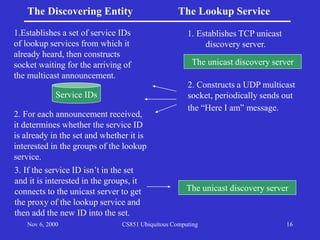
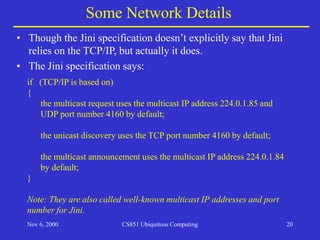
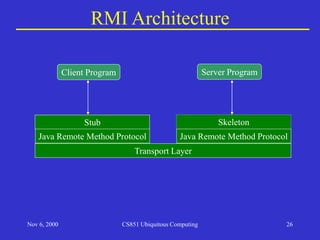
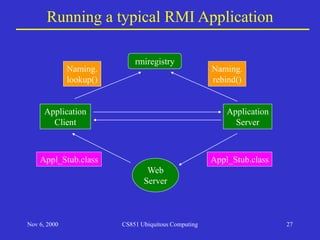
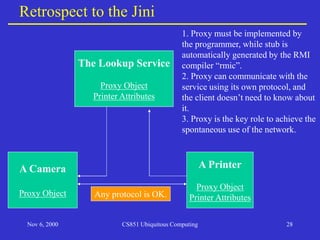
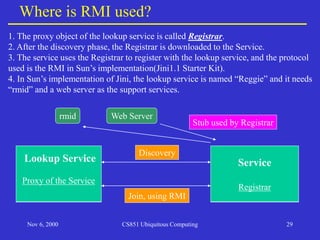
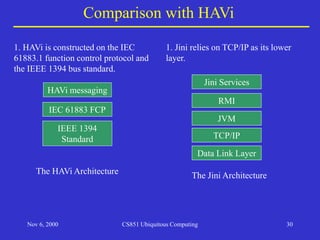
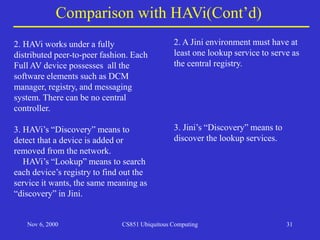
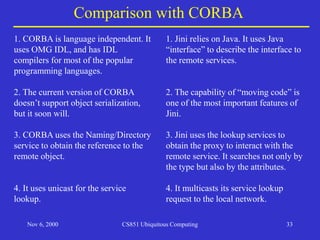
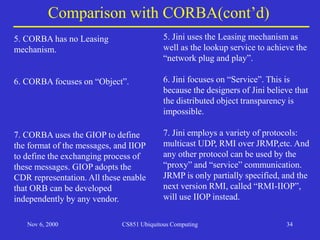
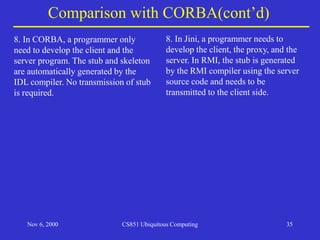
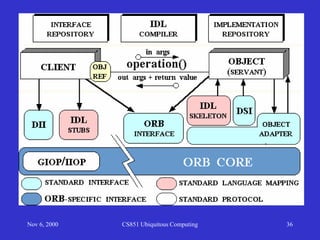
The document provides an overview of the Jini architecture presented by Weisheng Si. It describes Jini as a distributed system architecture developed by Sun Microsystems that aims for "network plug and play". The key components of Jini include services, lookup services, proxy objects, and clients. It explains the service lookup process, including discovery, joining, and leasing. The discovery protocols of multicast request, unicast, and multicast announcement are covered. It also discusses how Jini uses Remote Method Invocation and TCP/IP in the architecture.