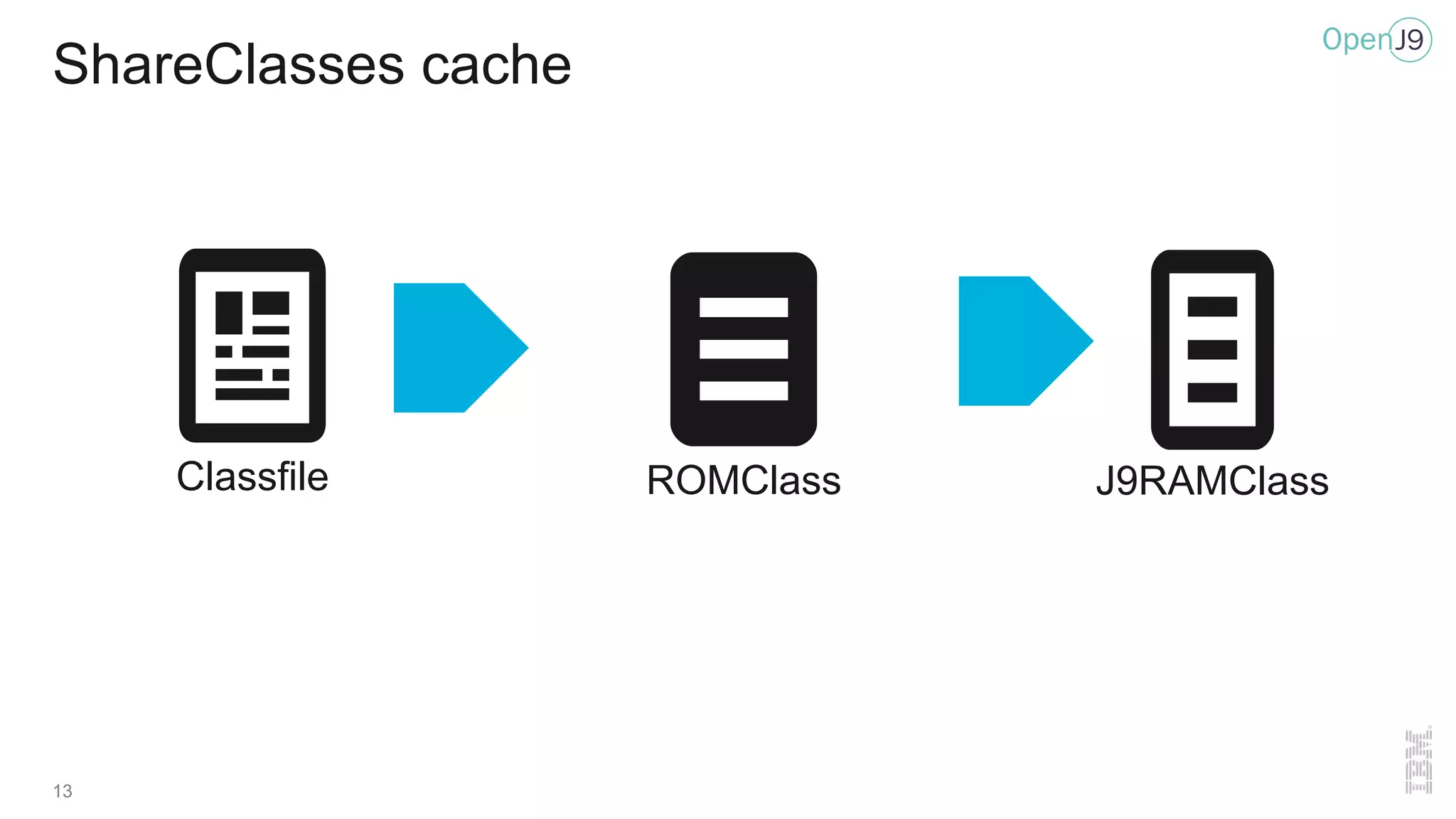
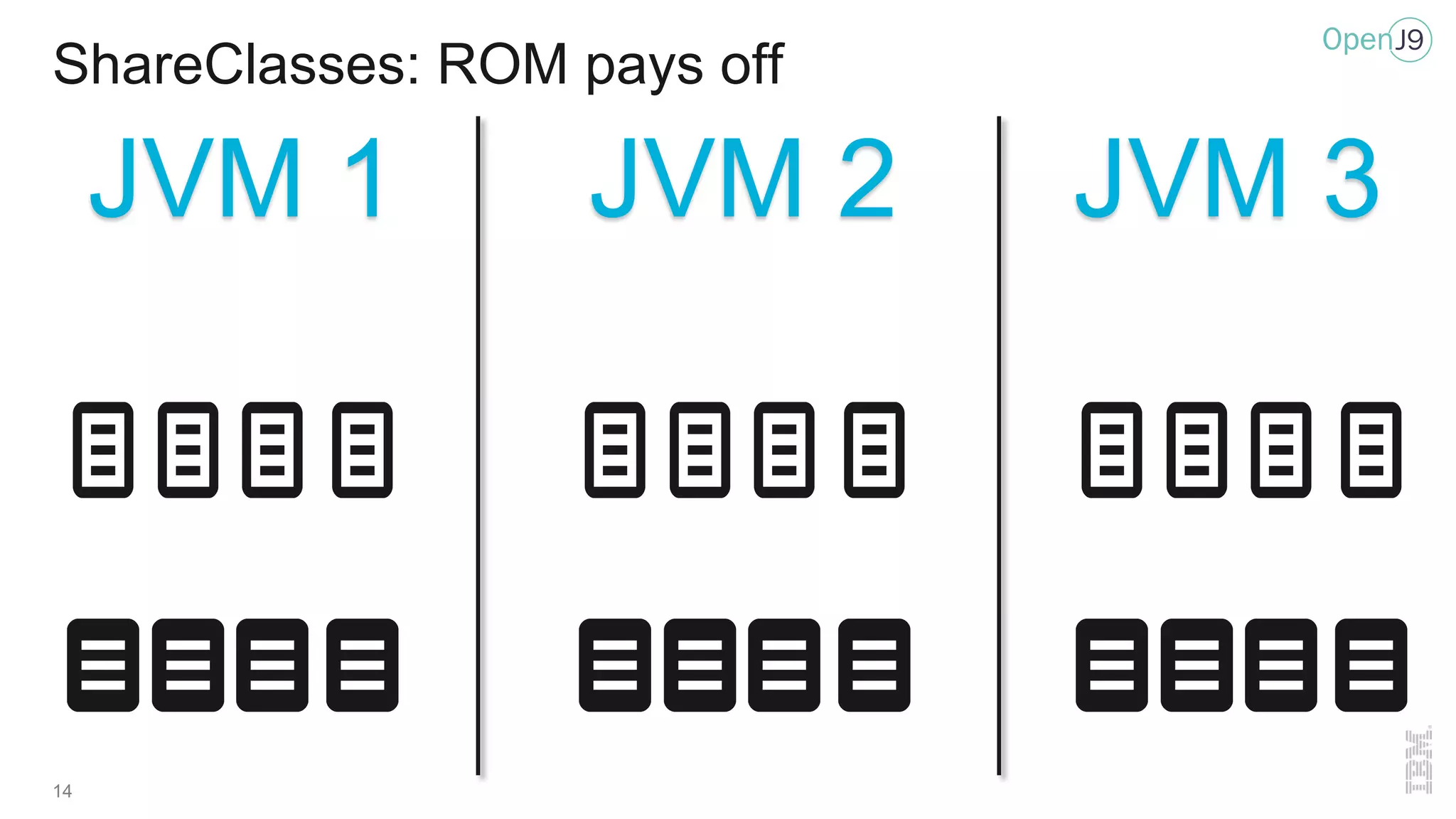
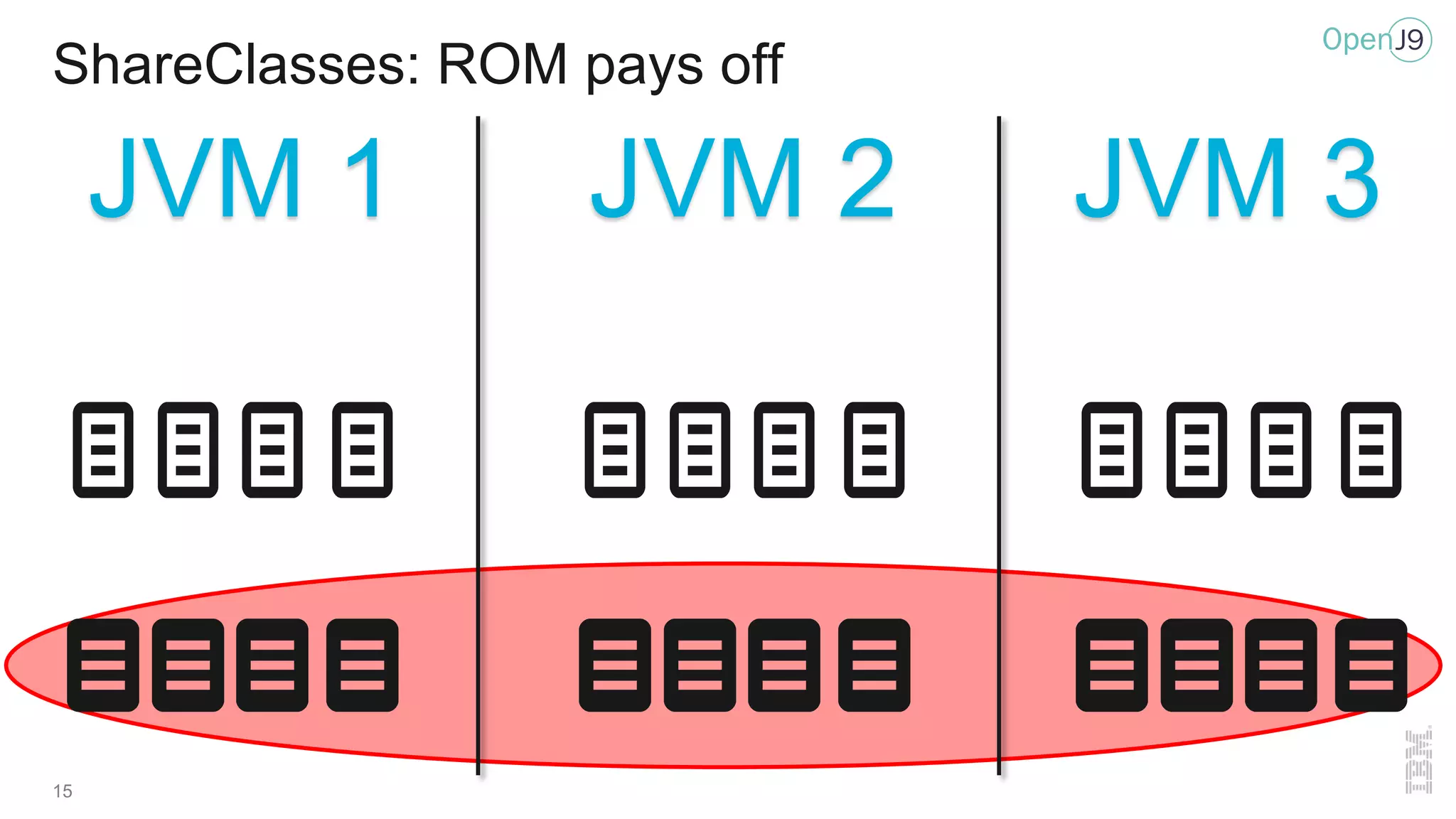
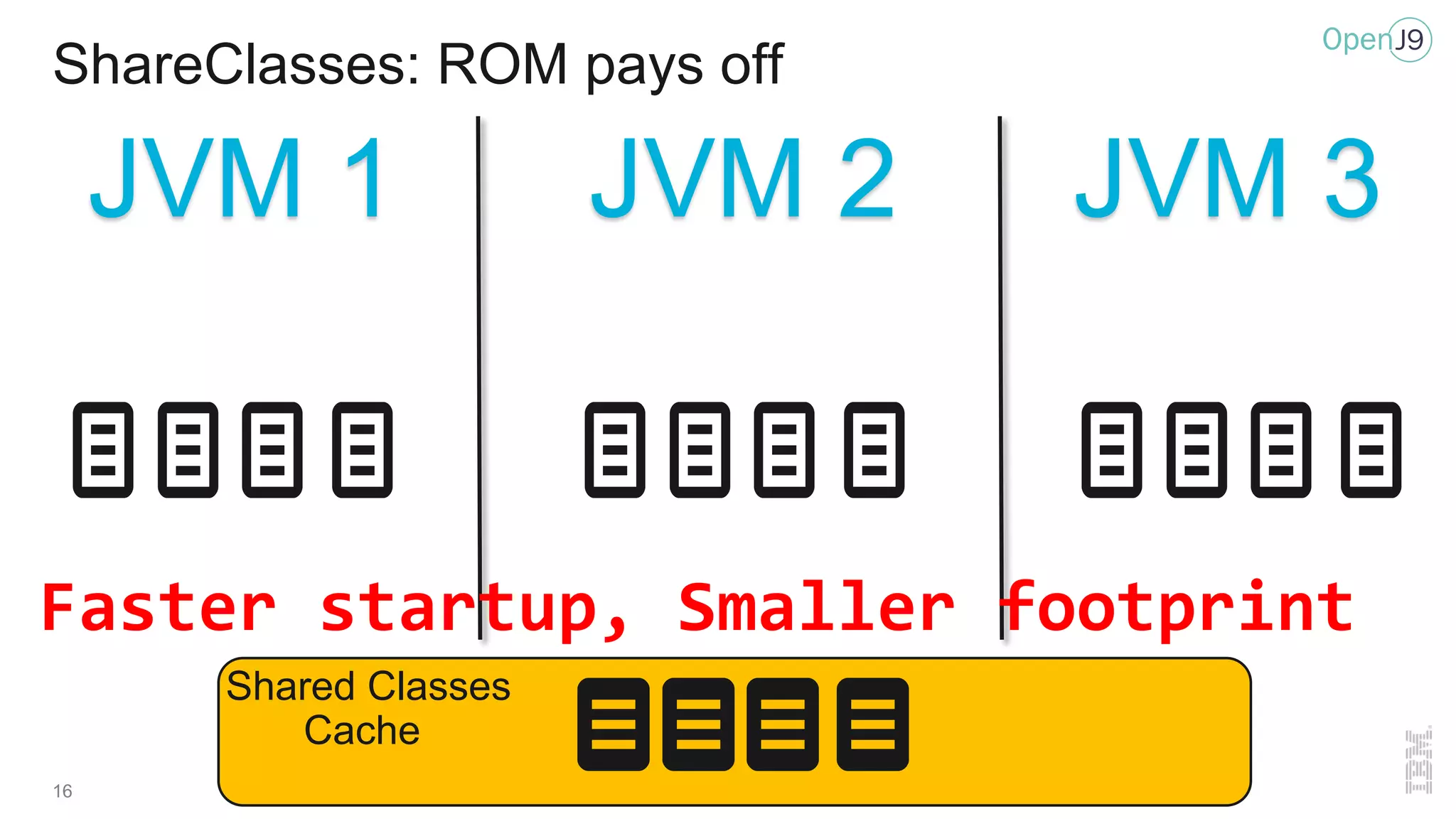
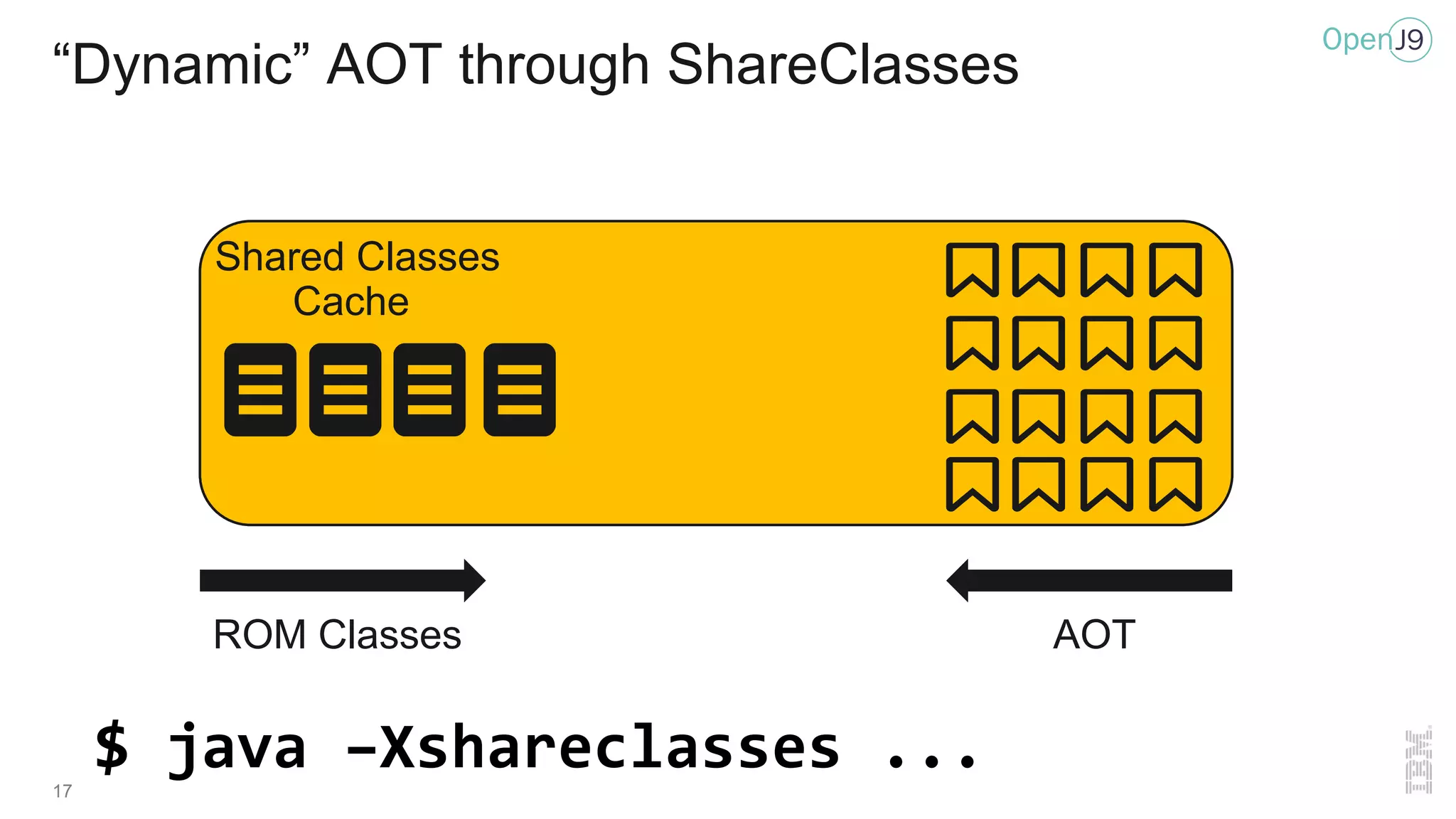
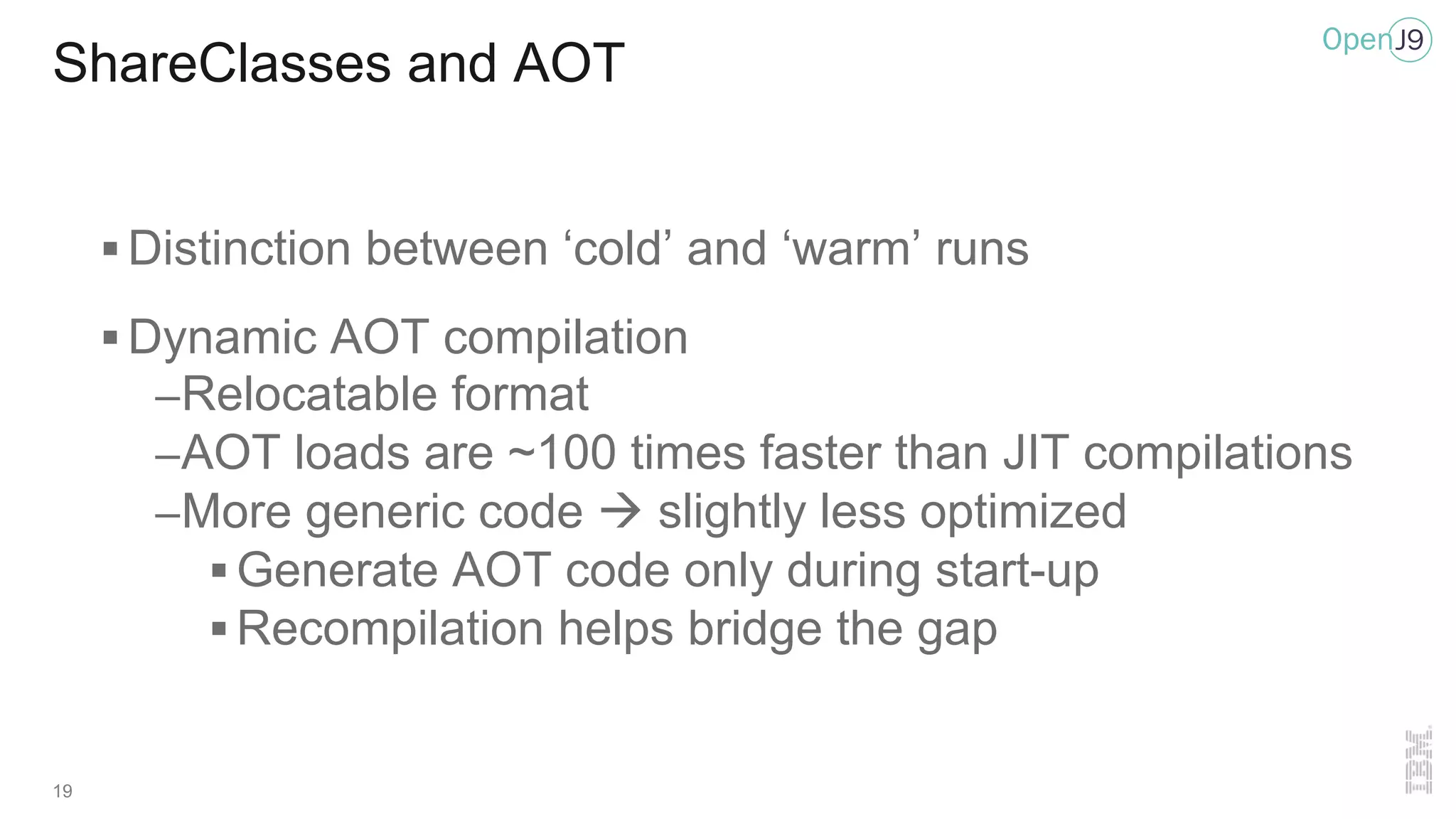
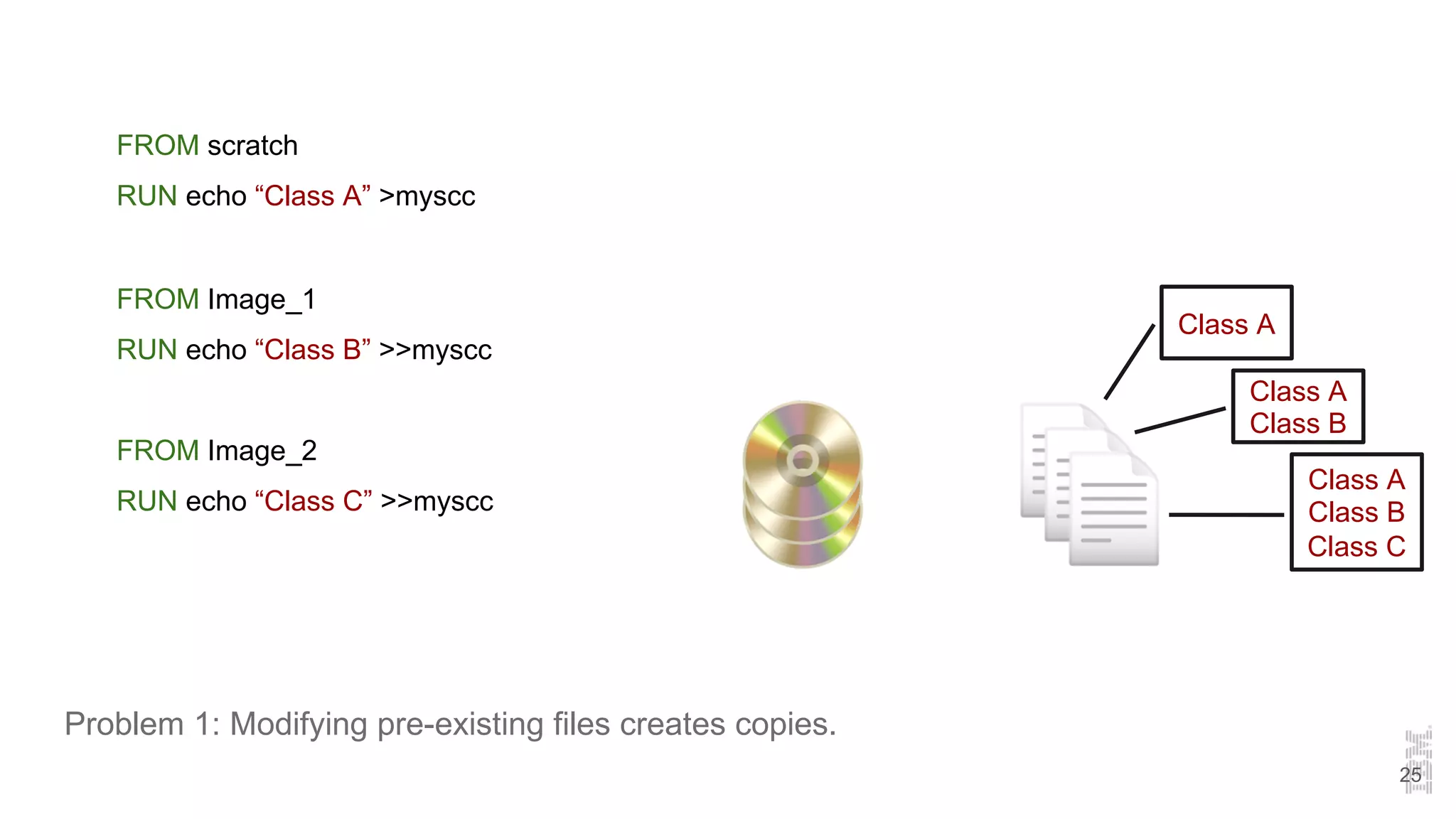
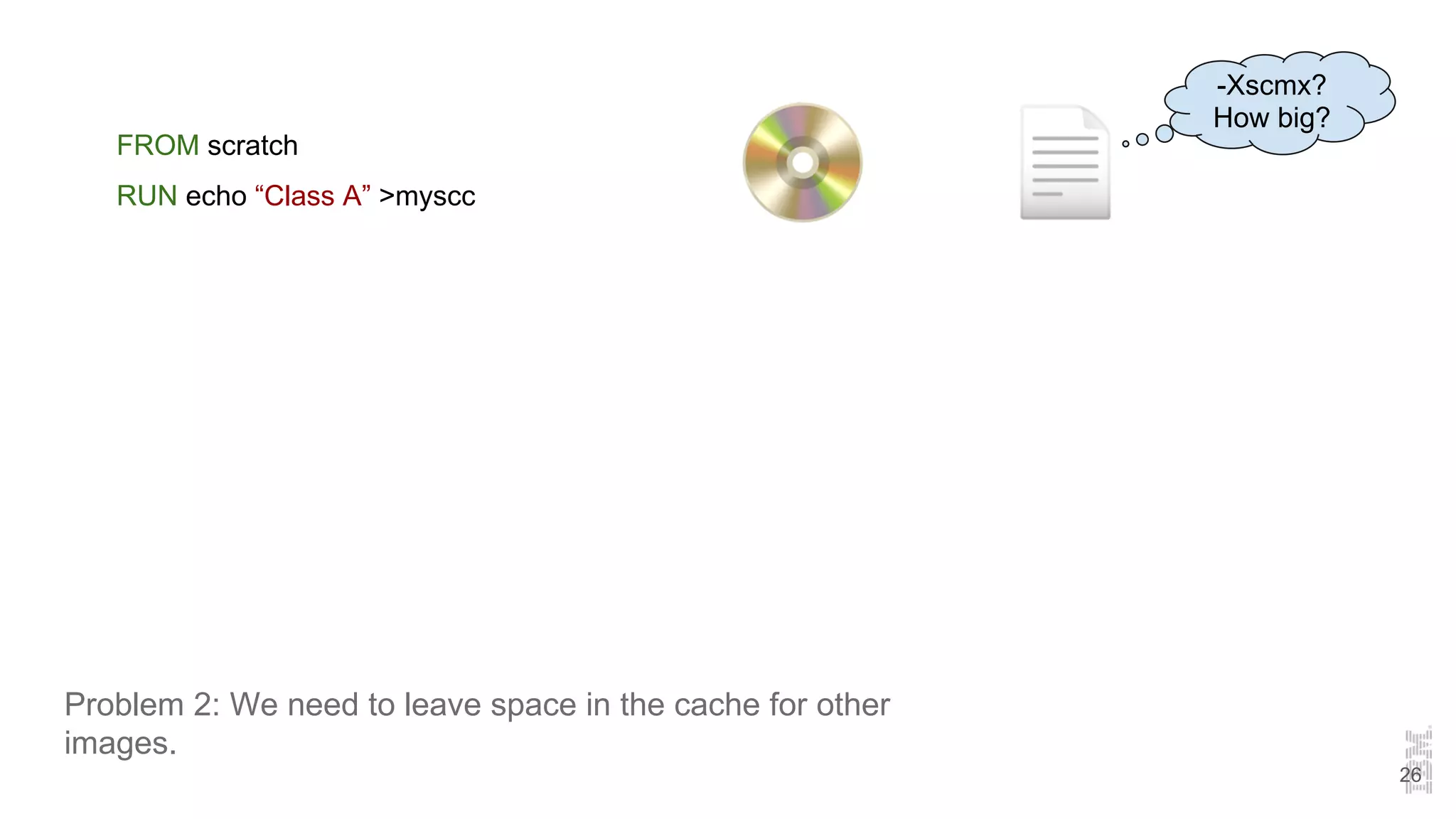
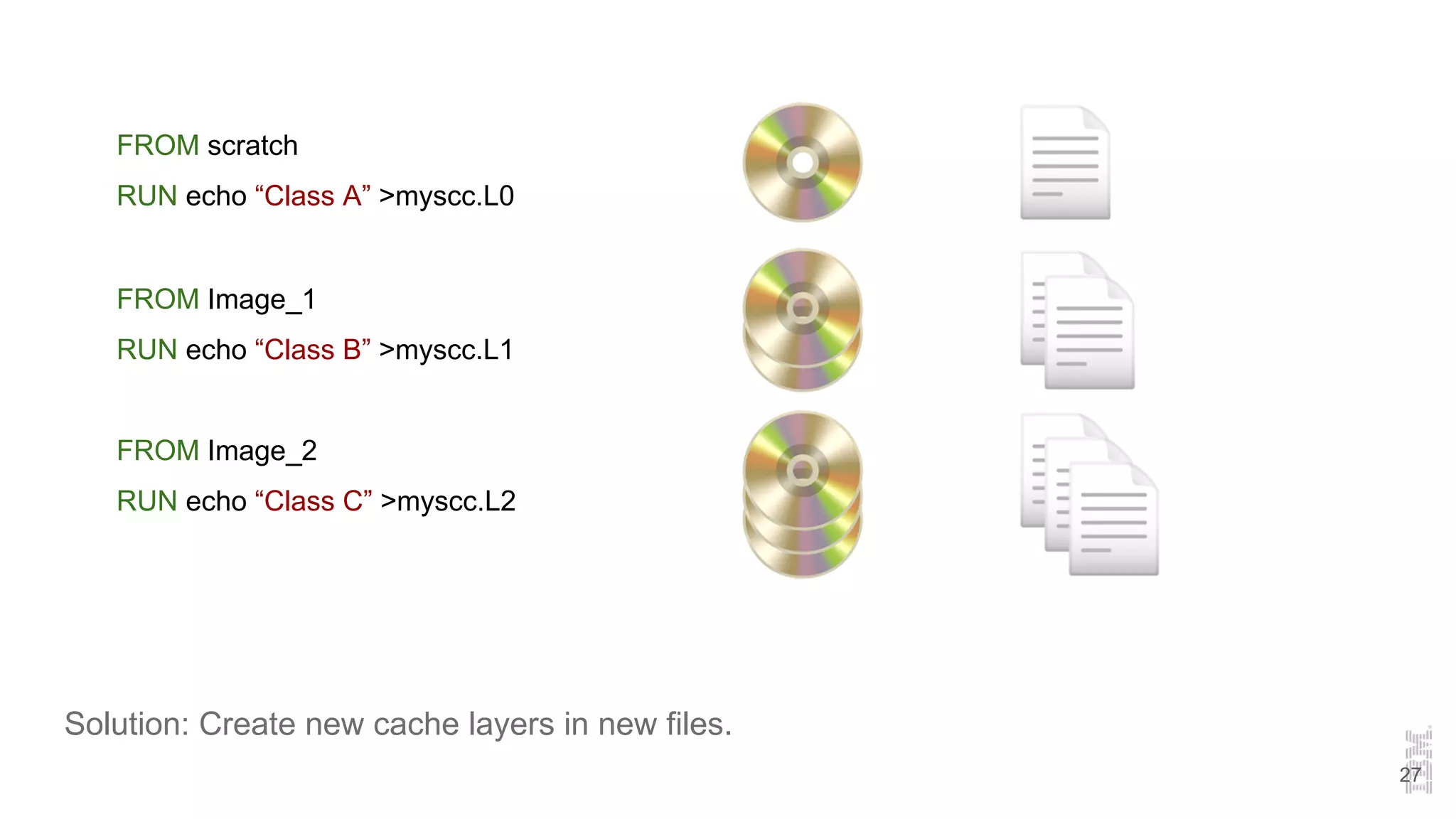
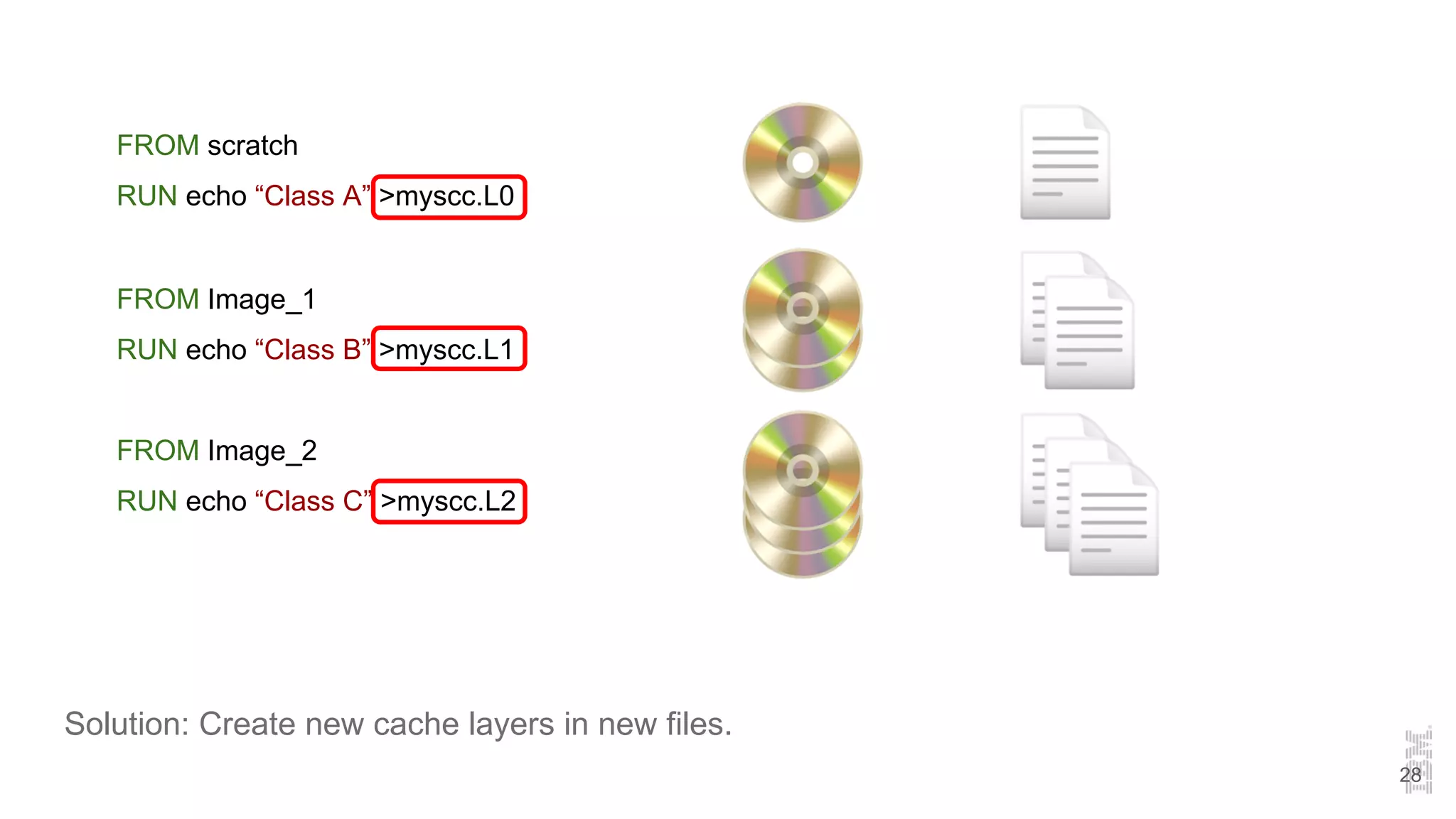
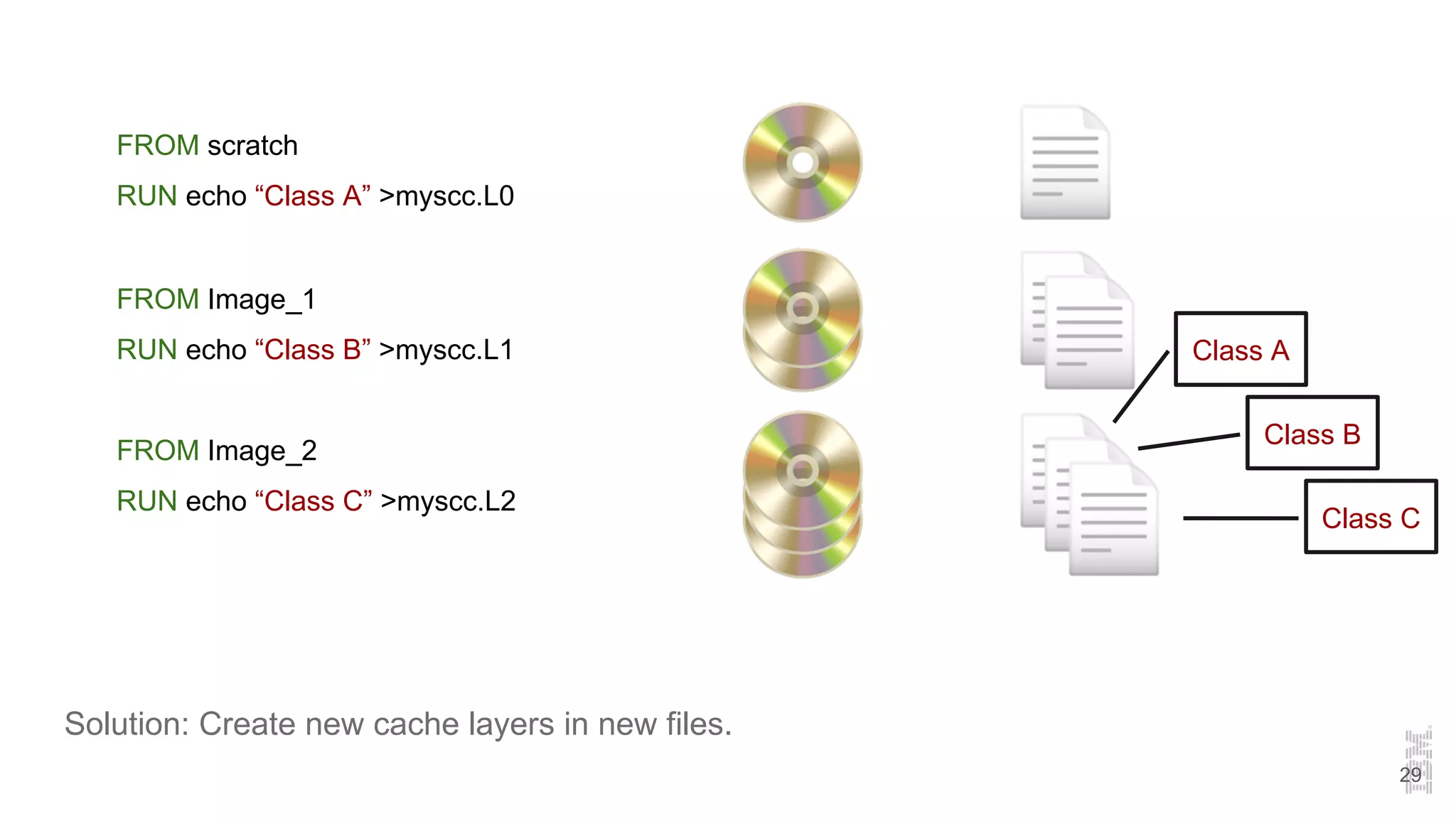
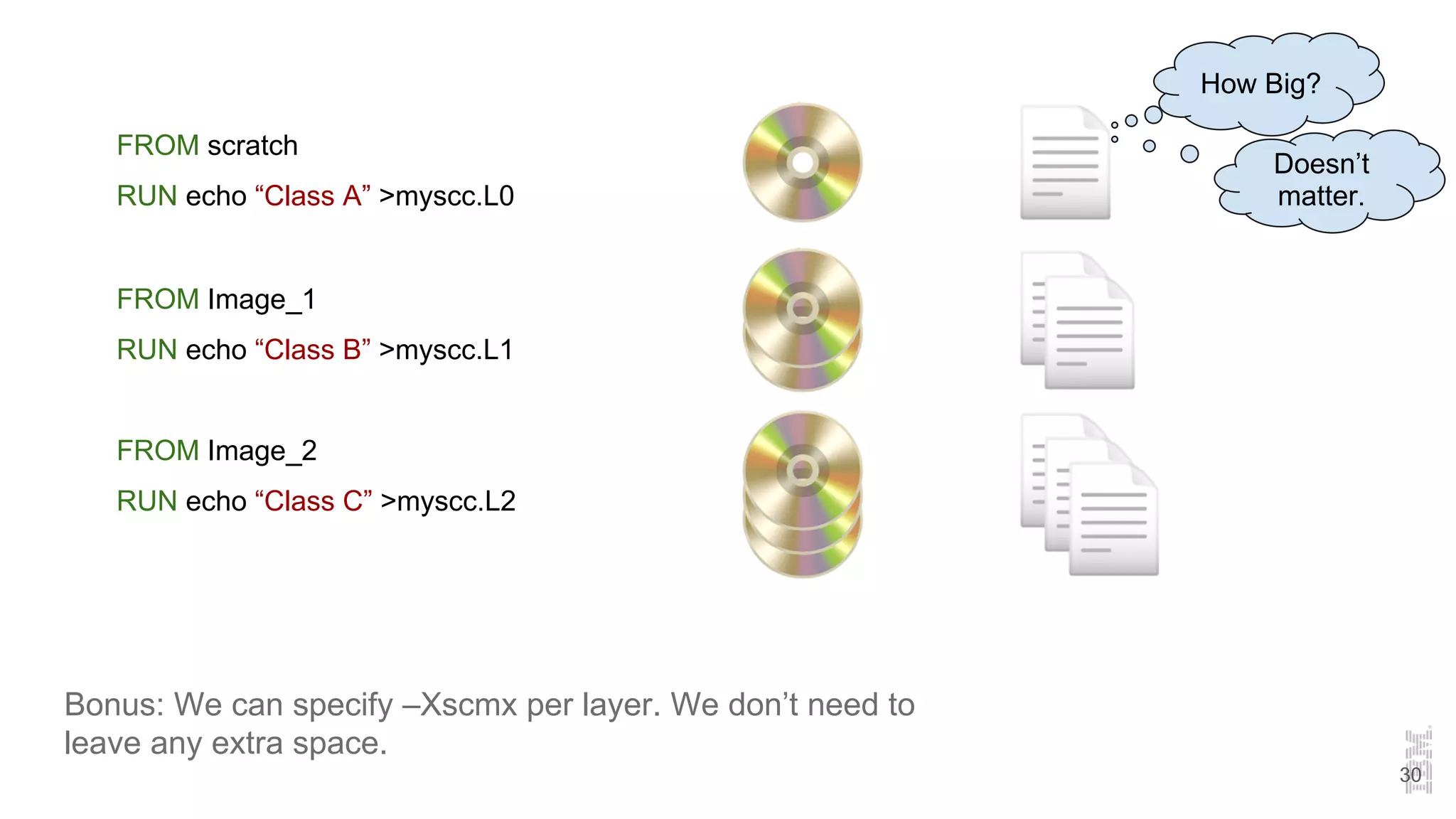
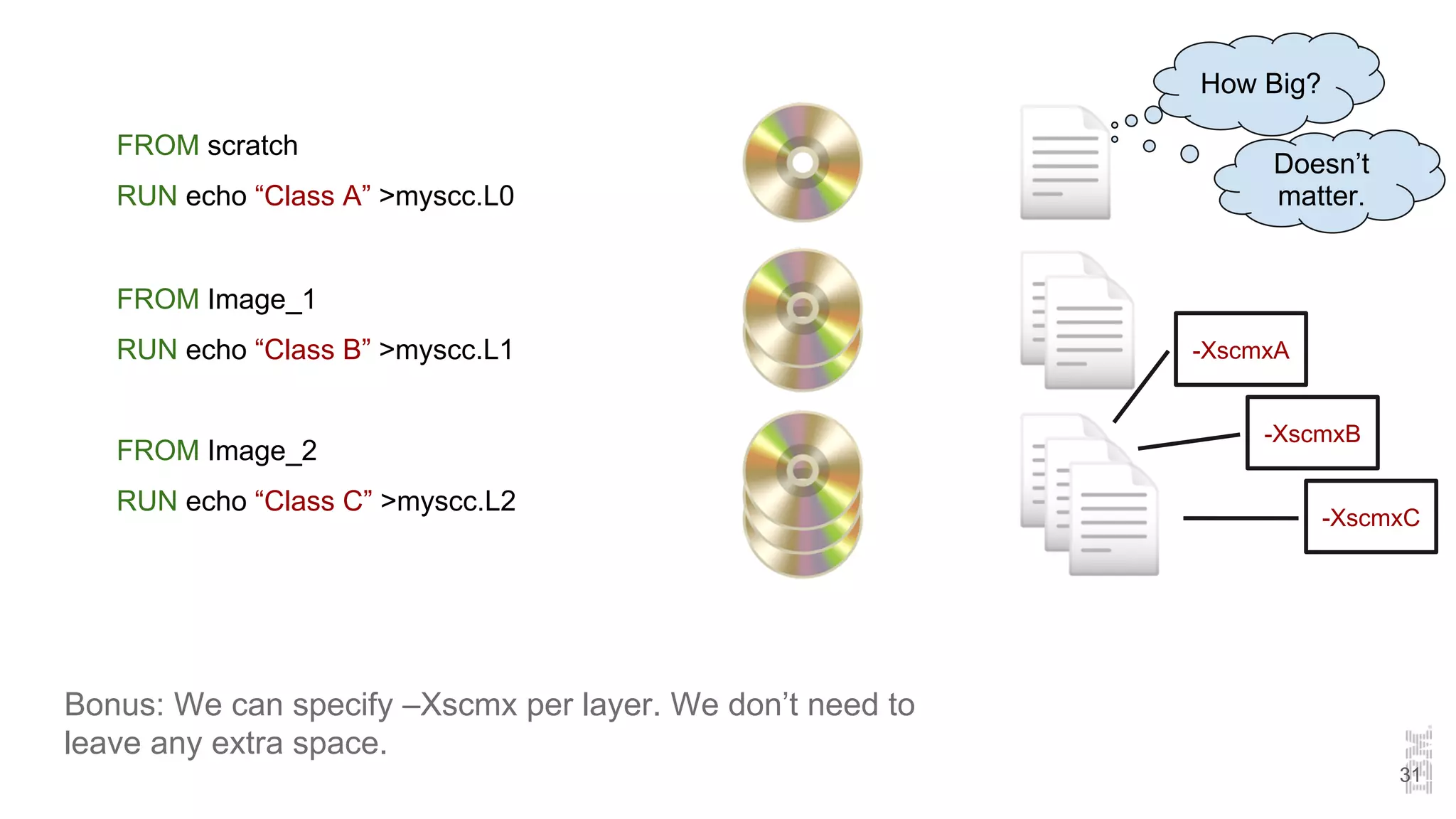
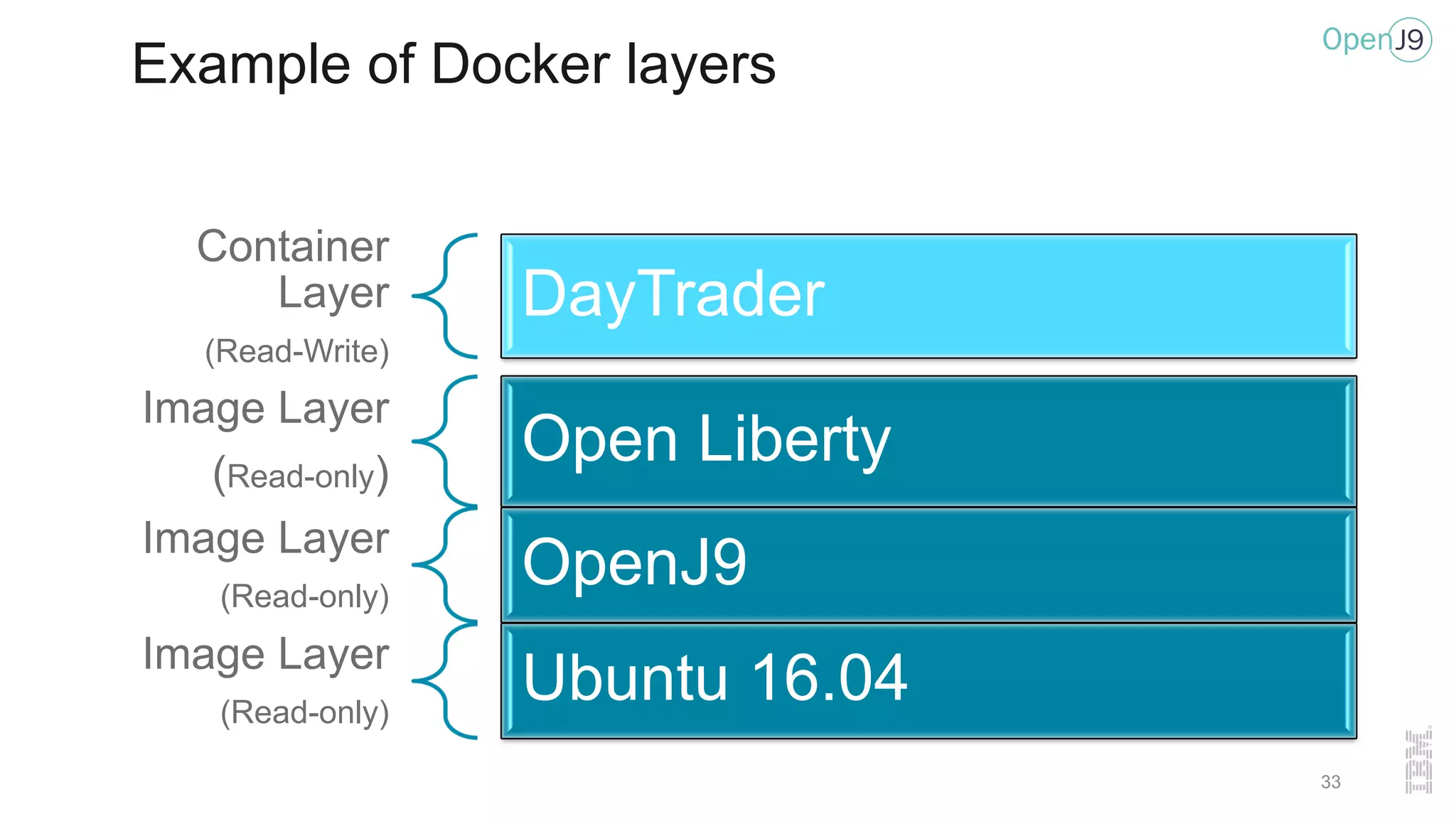
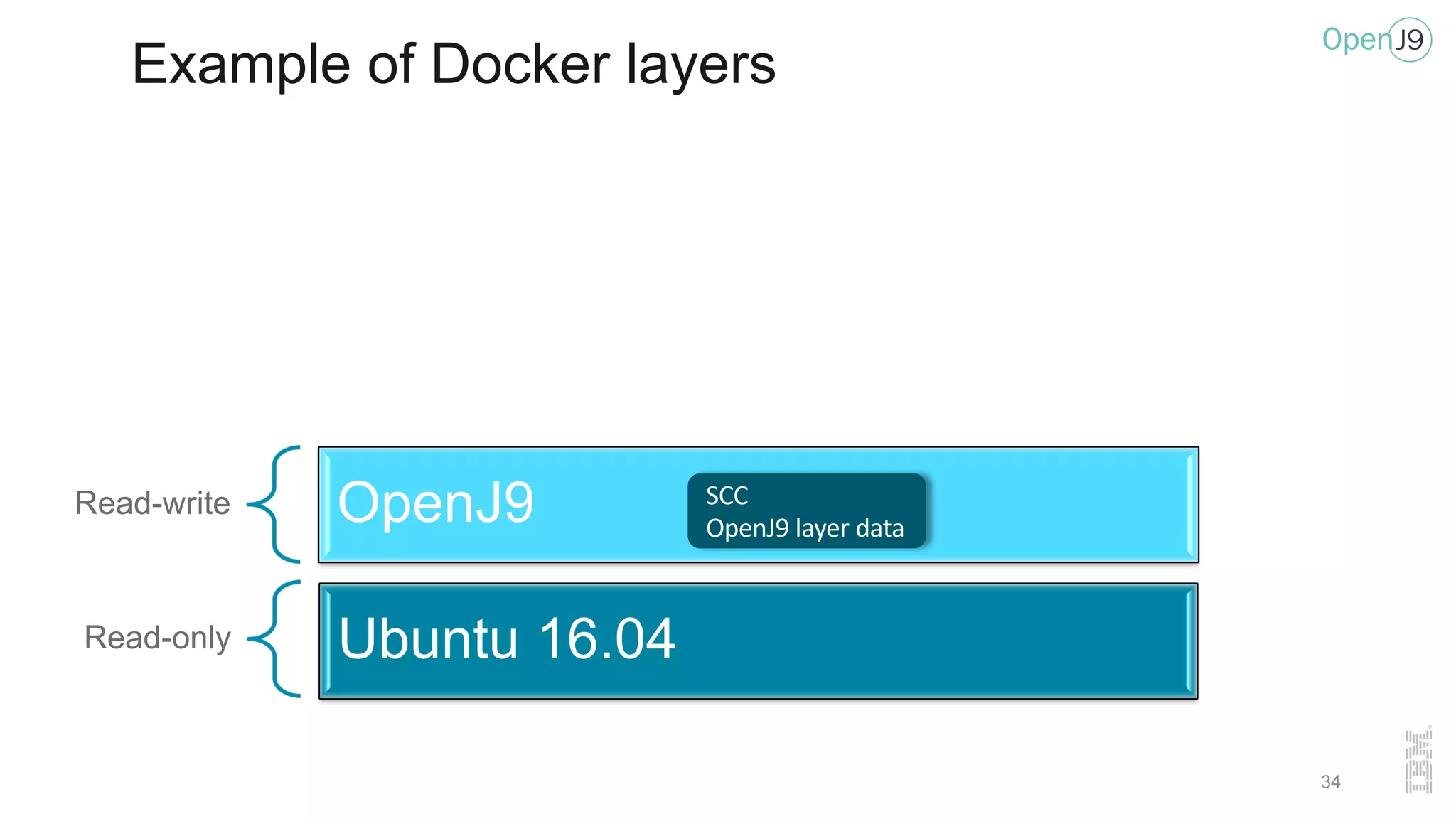
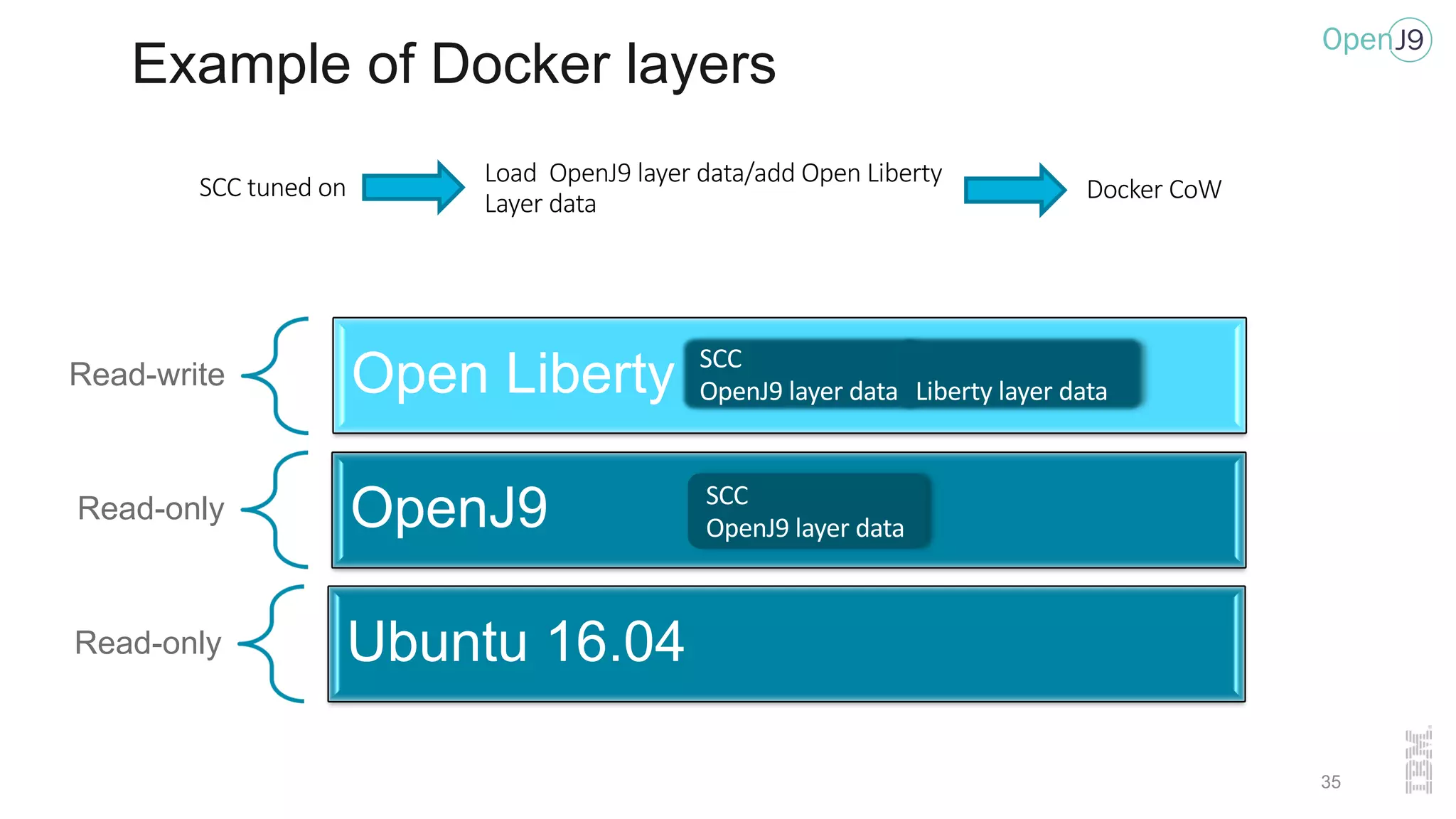
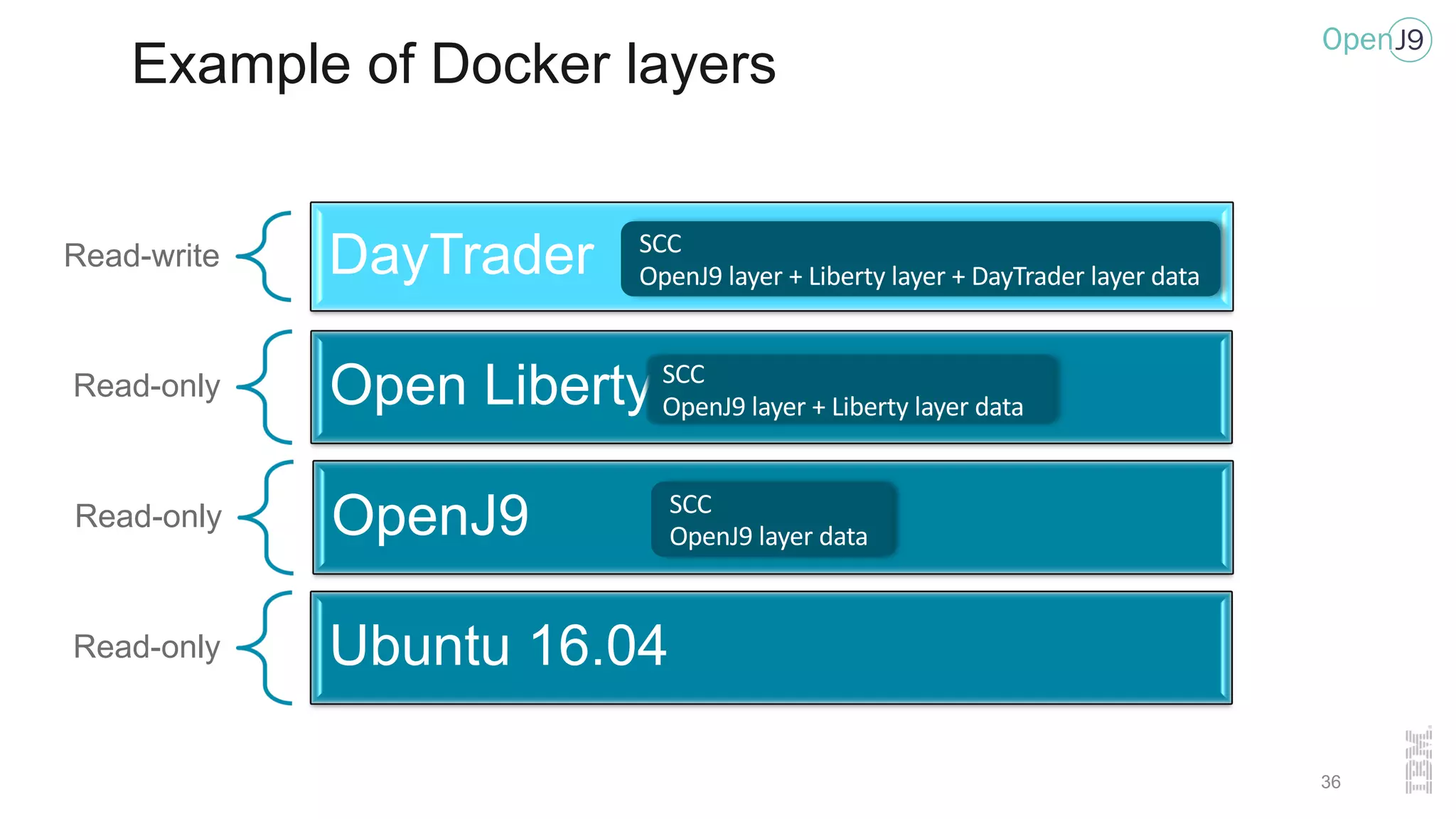
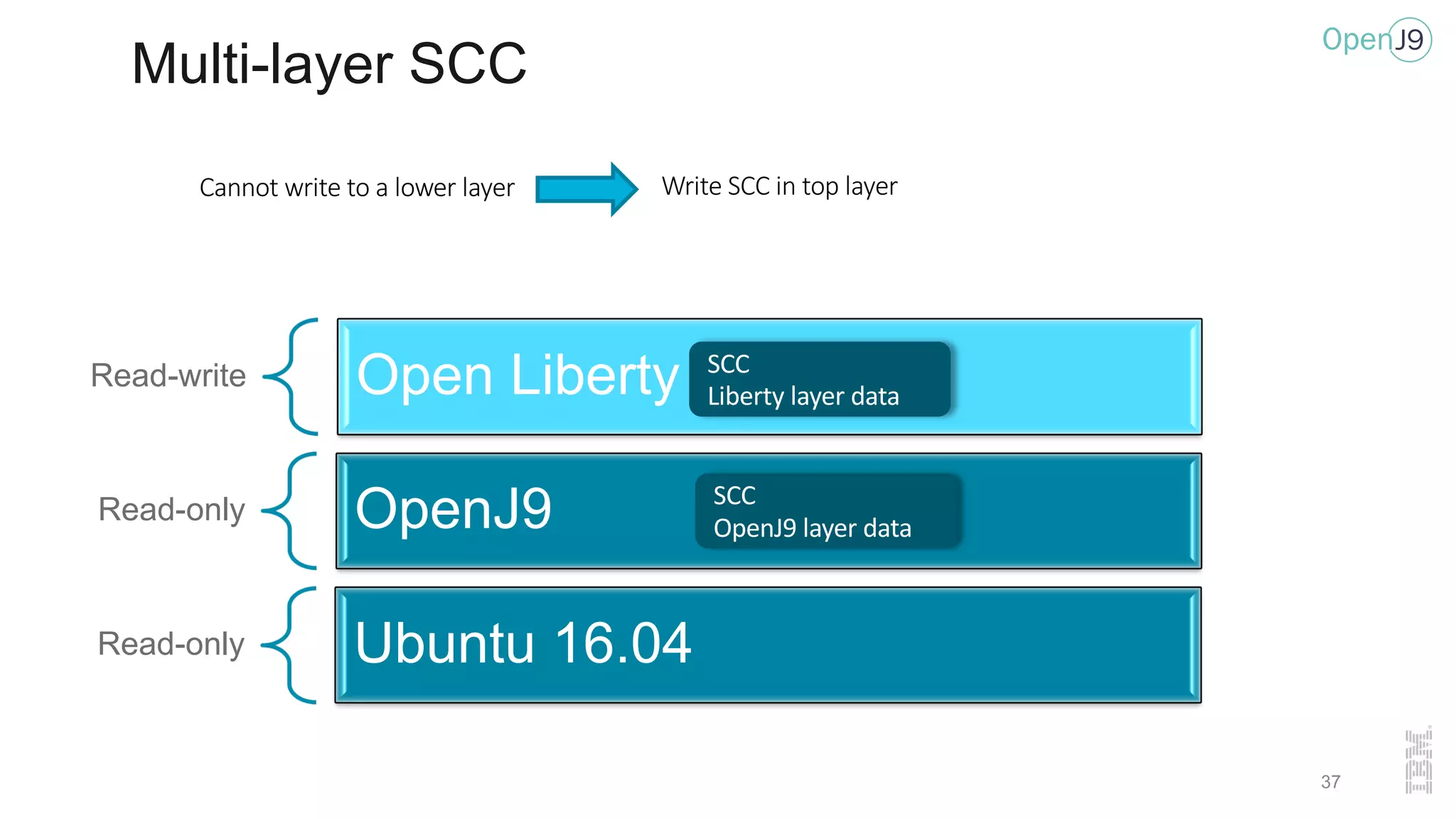
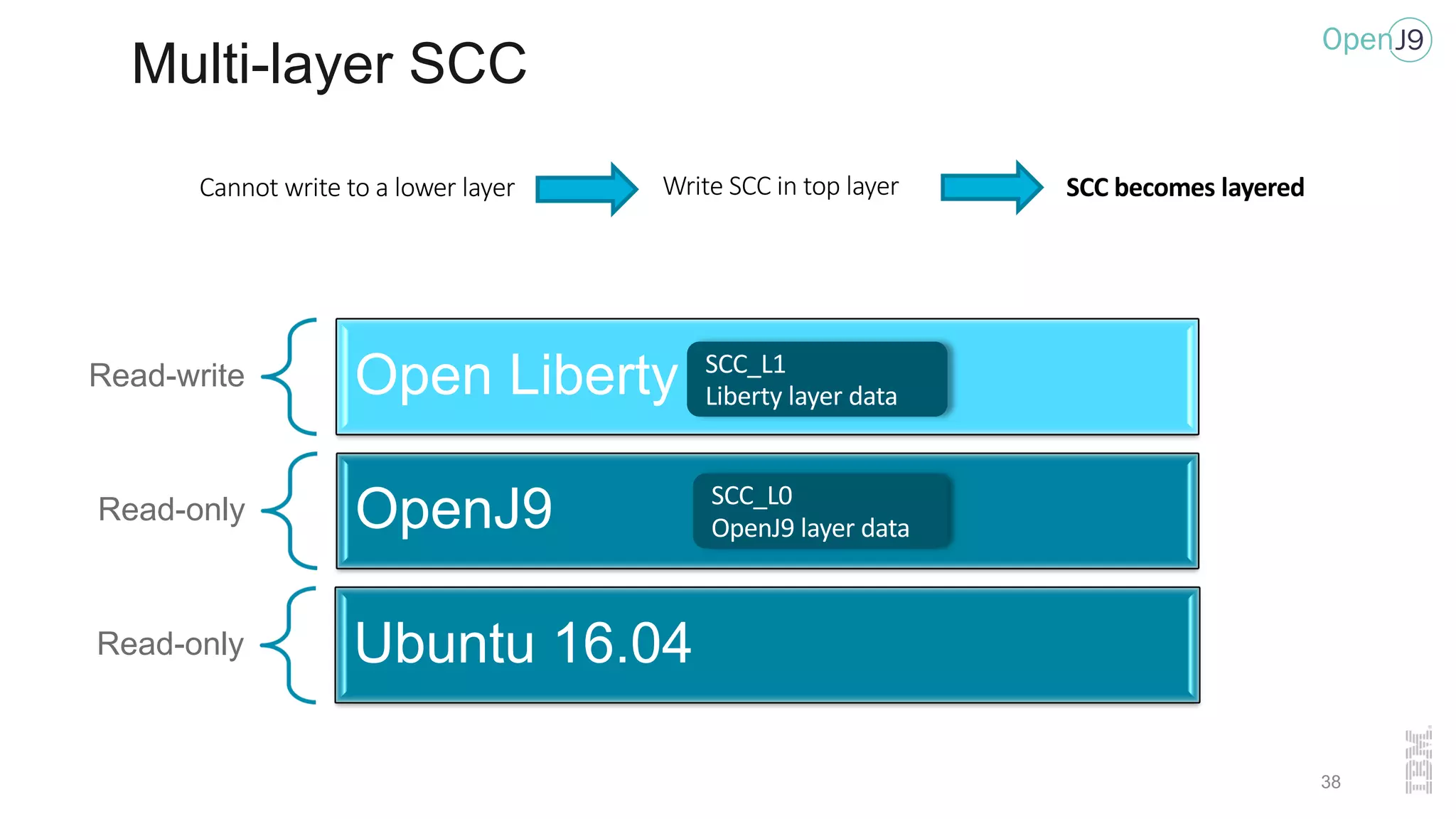
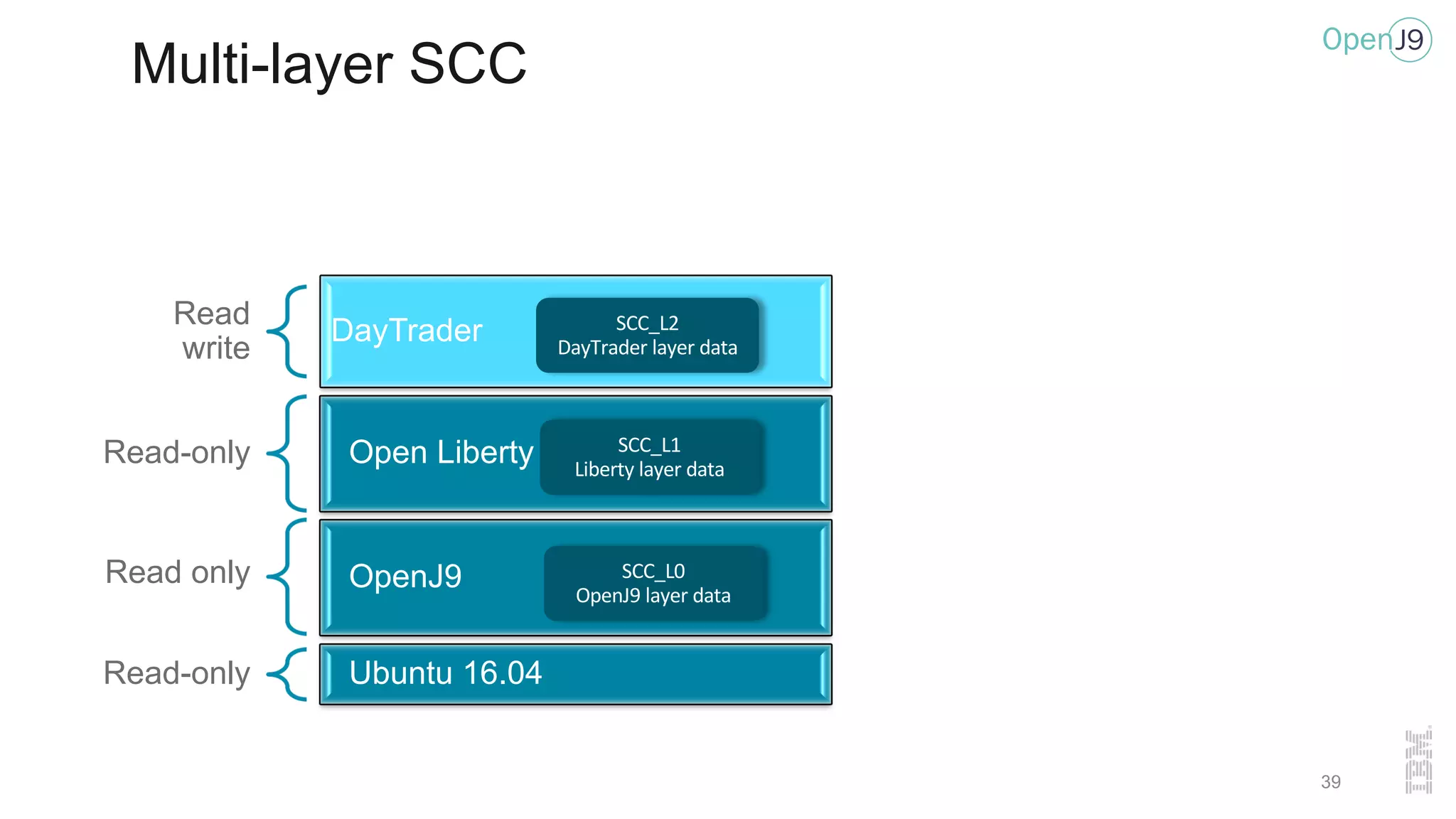
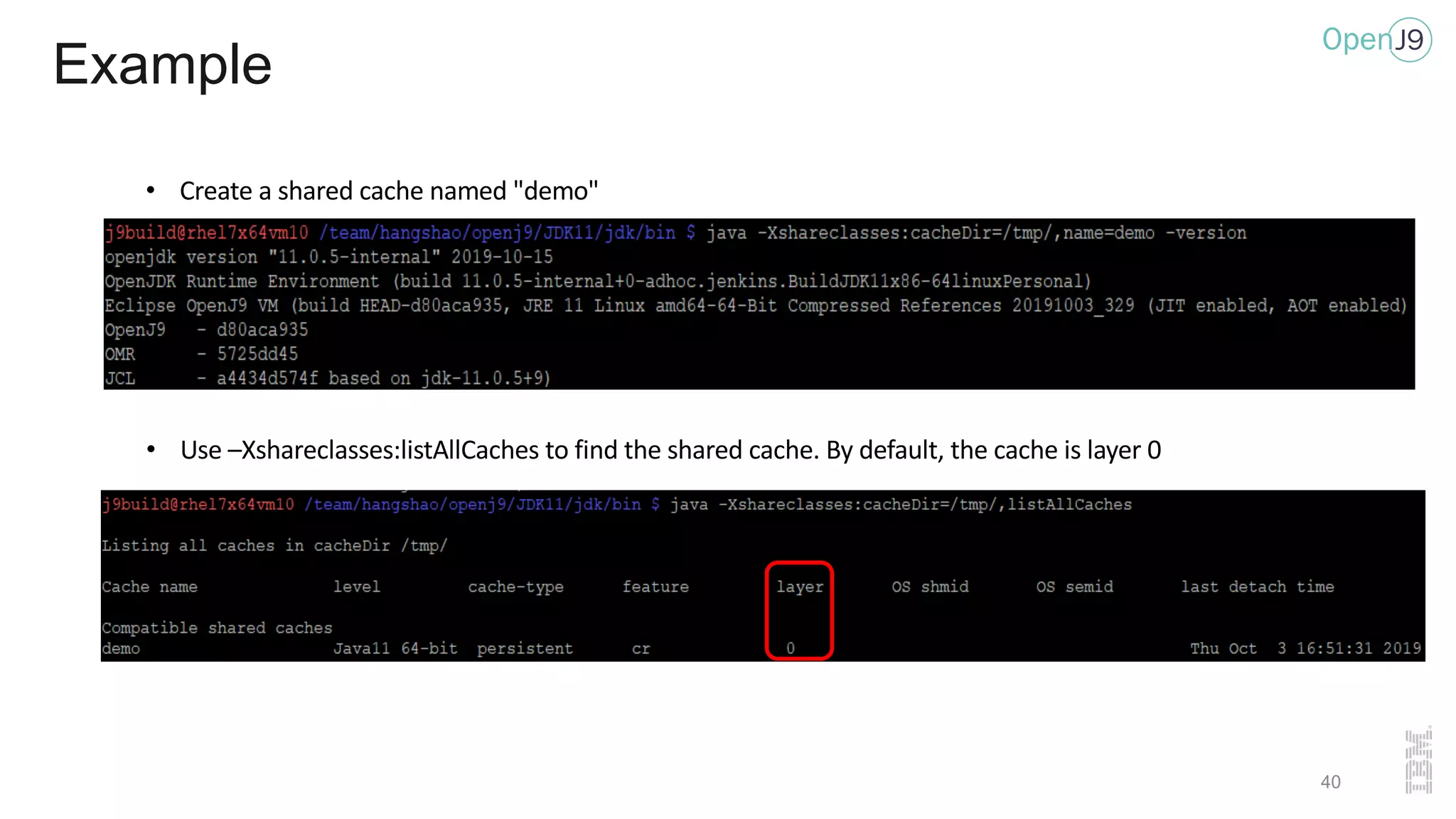
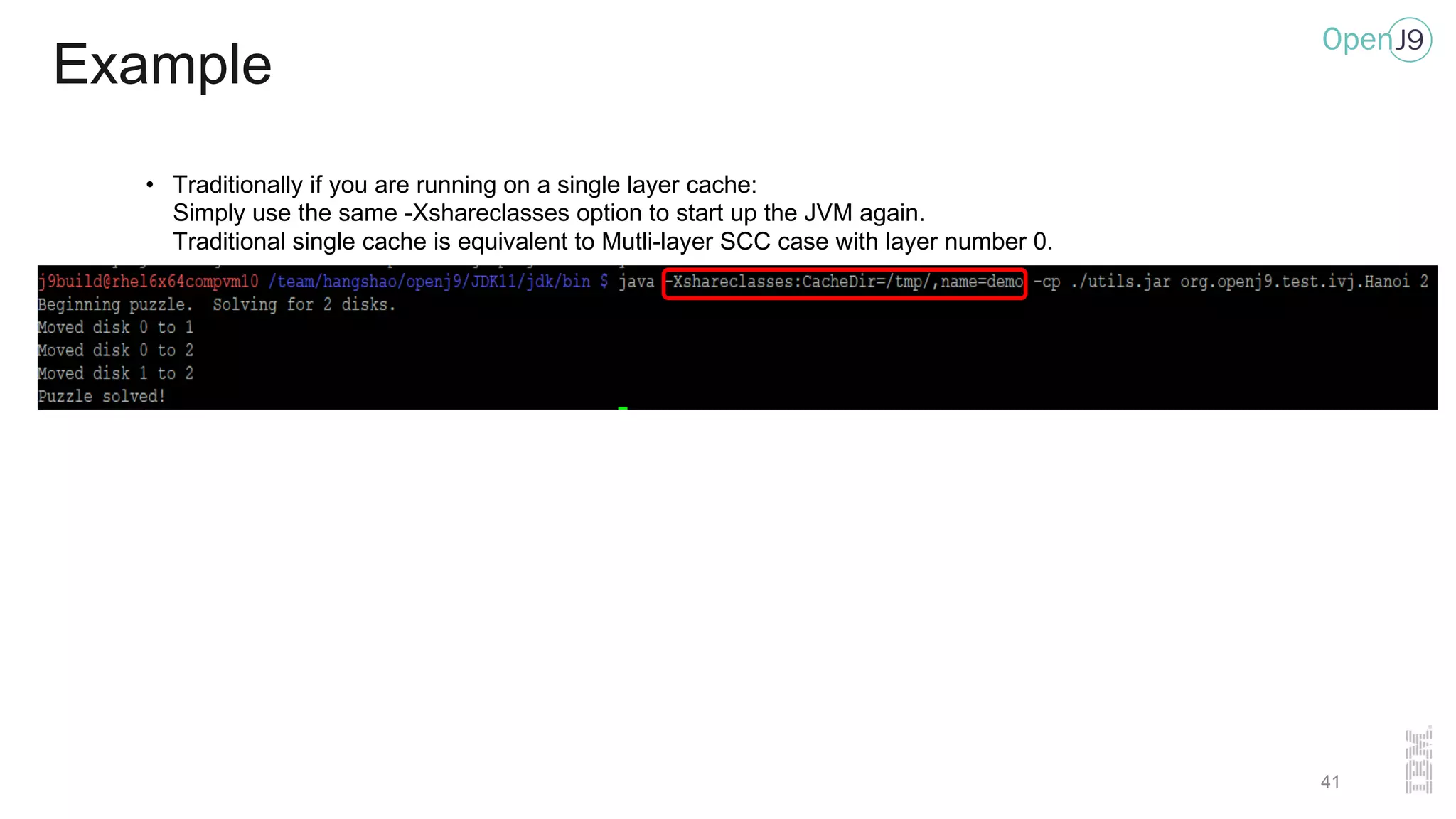
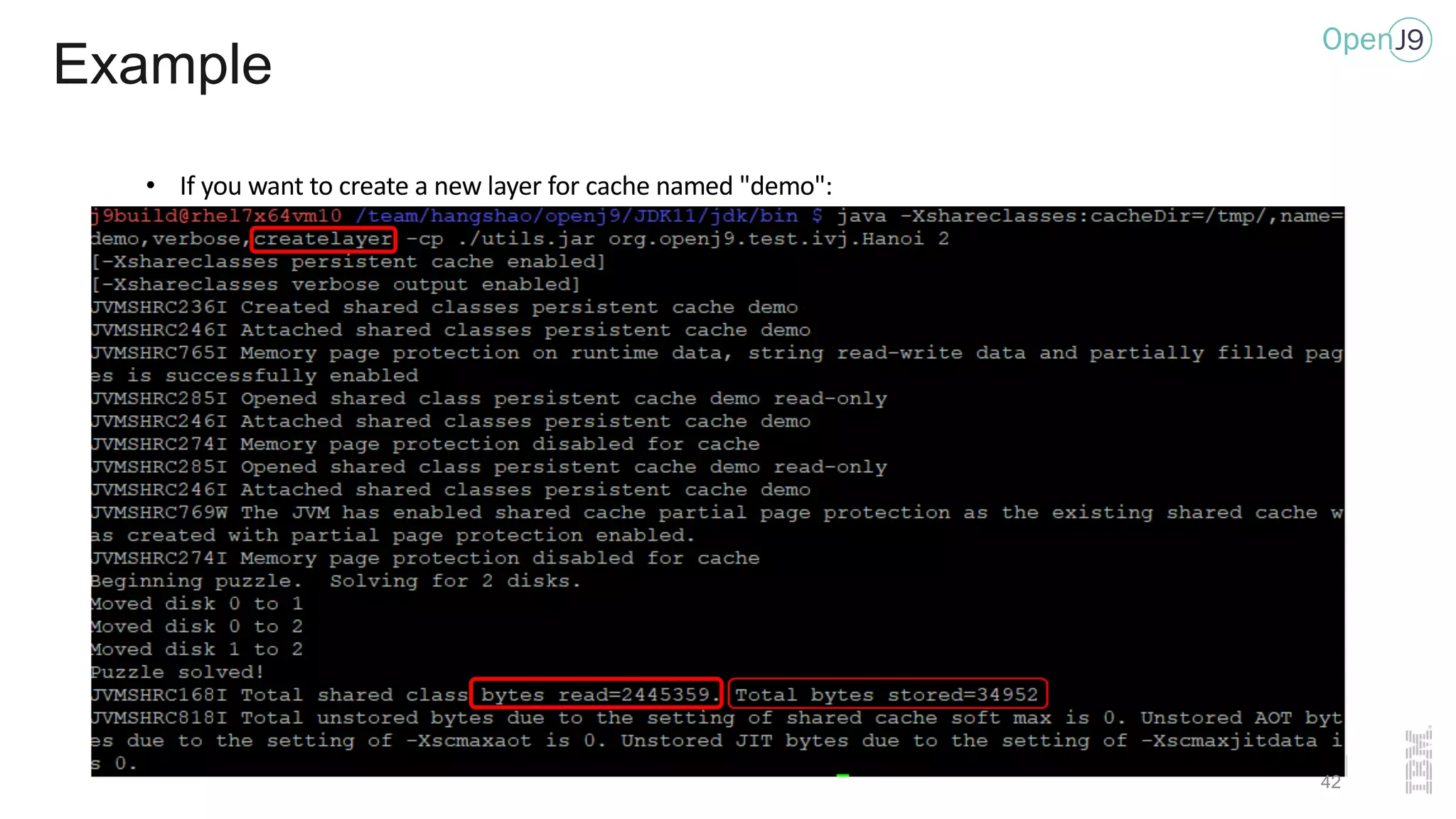
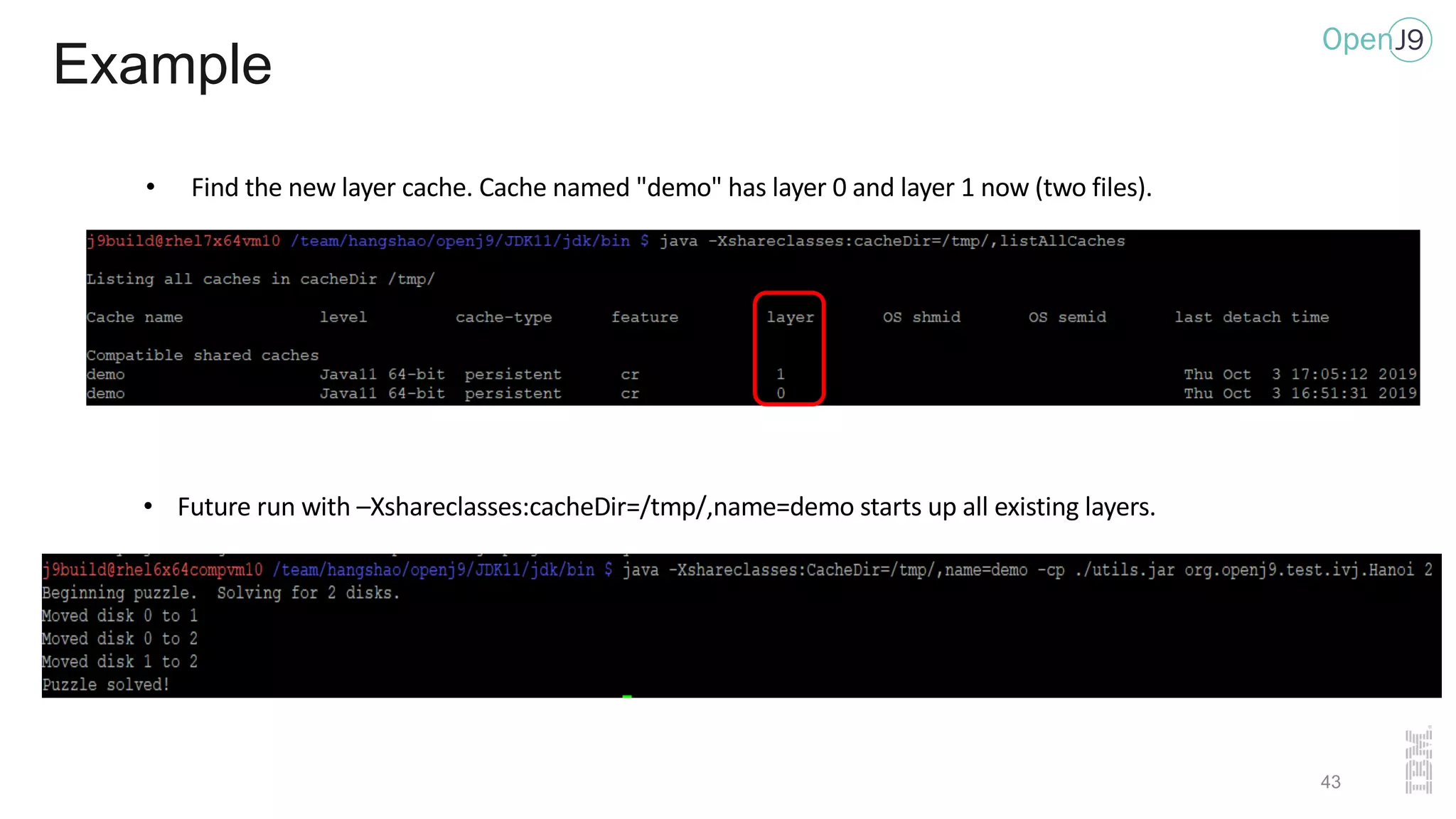
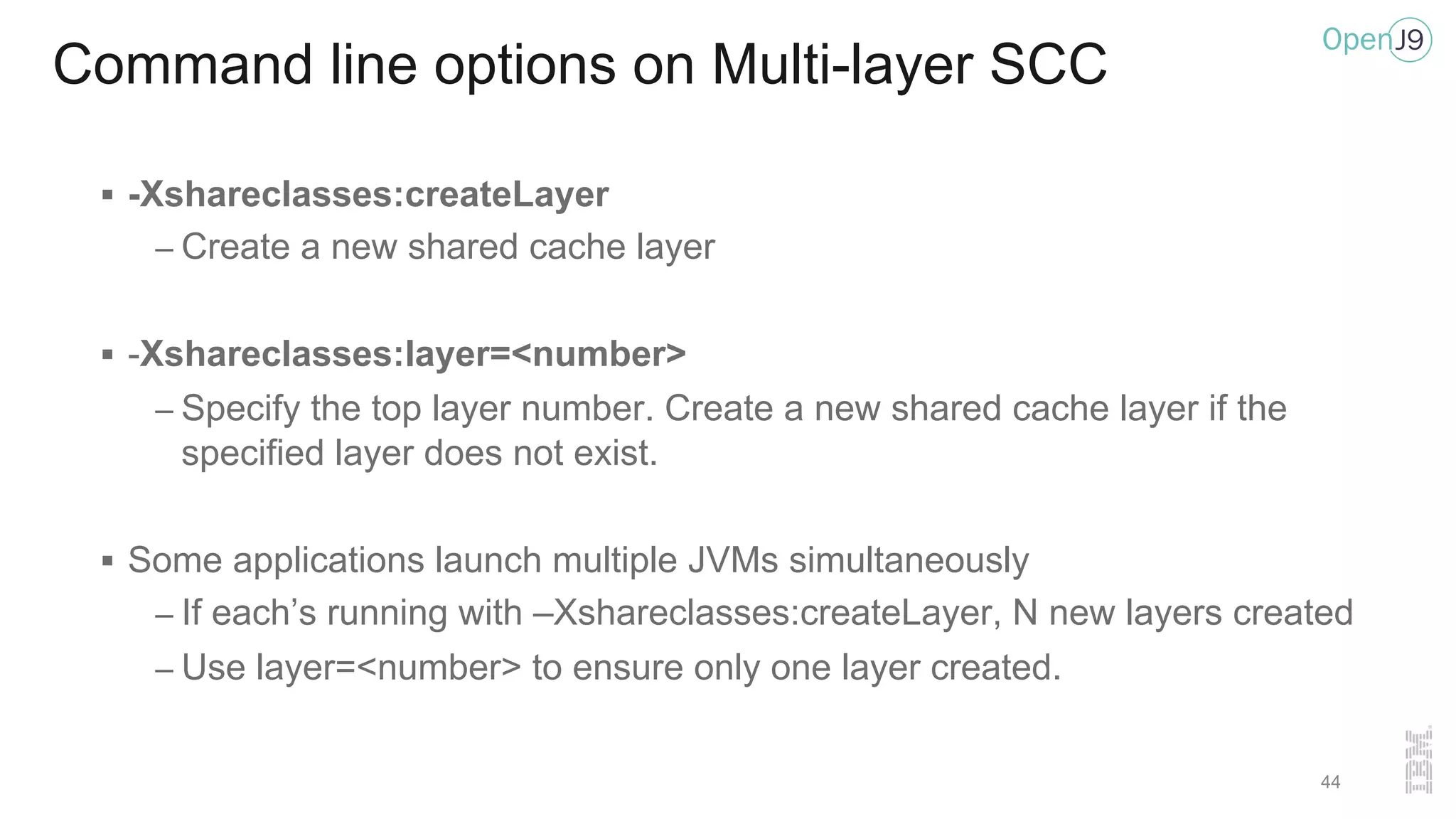
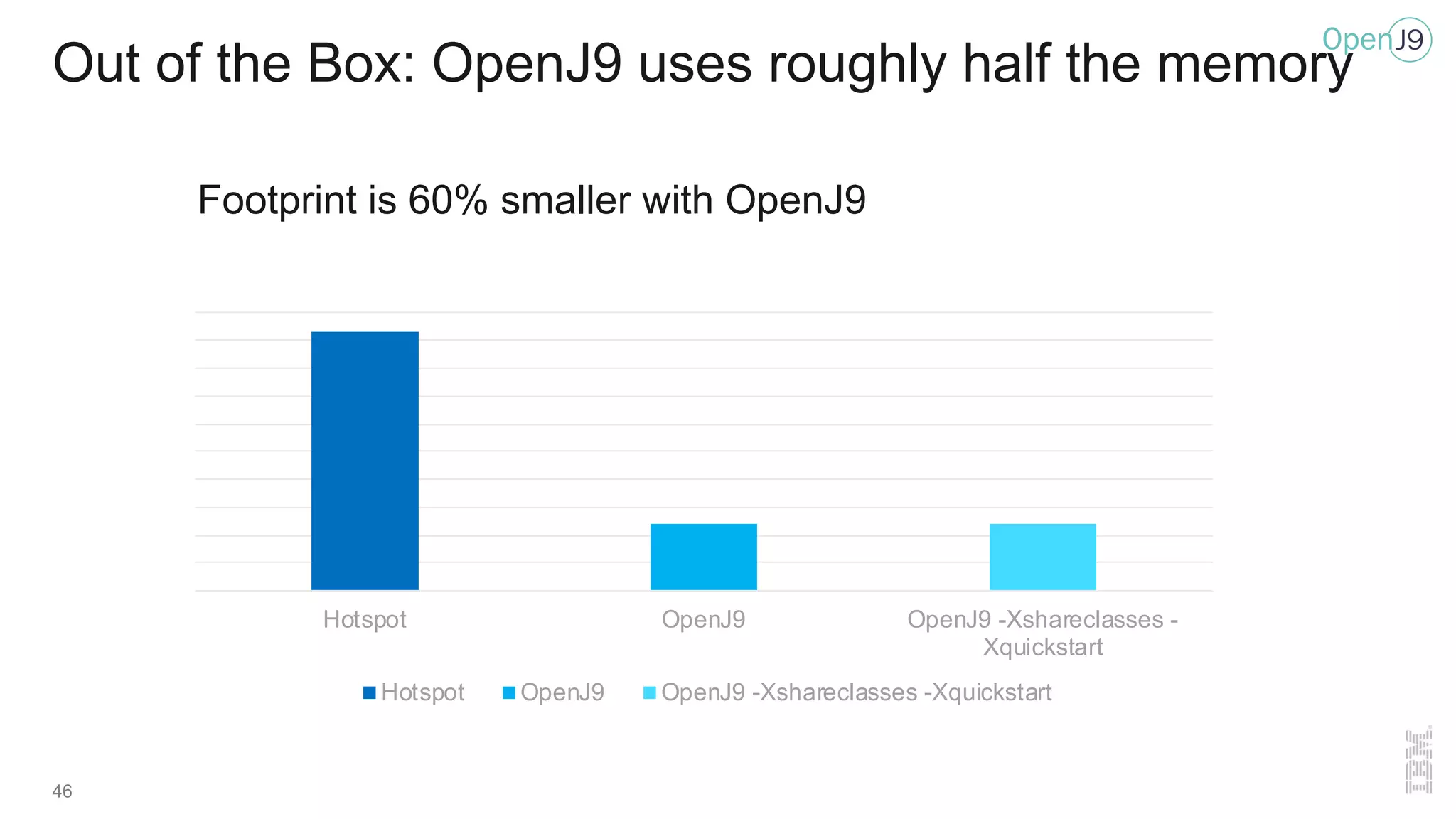
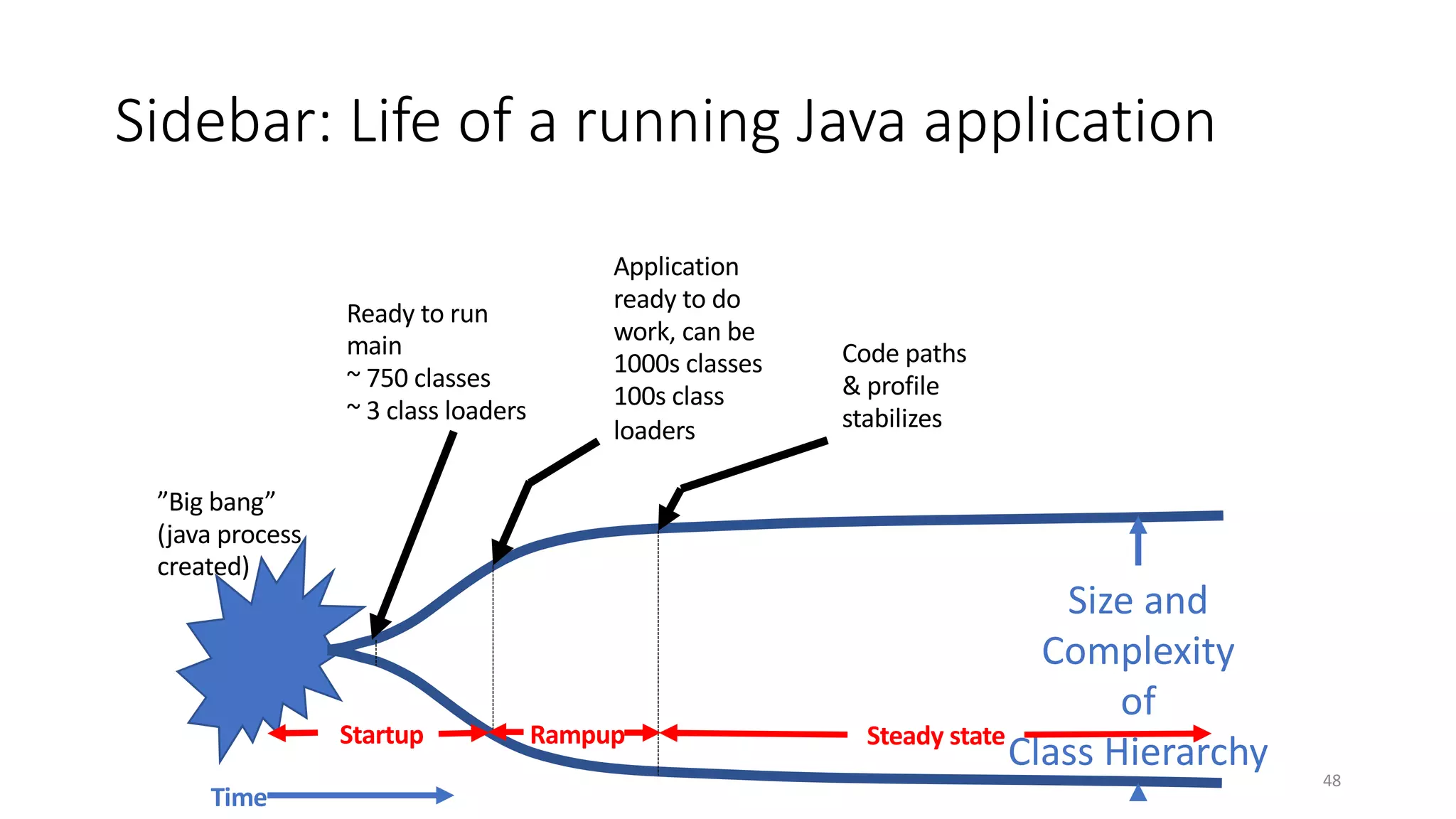
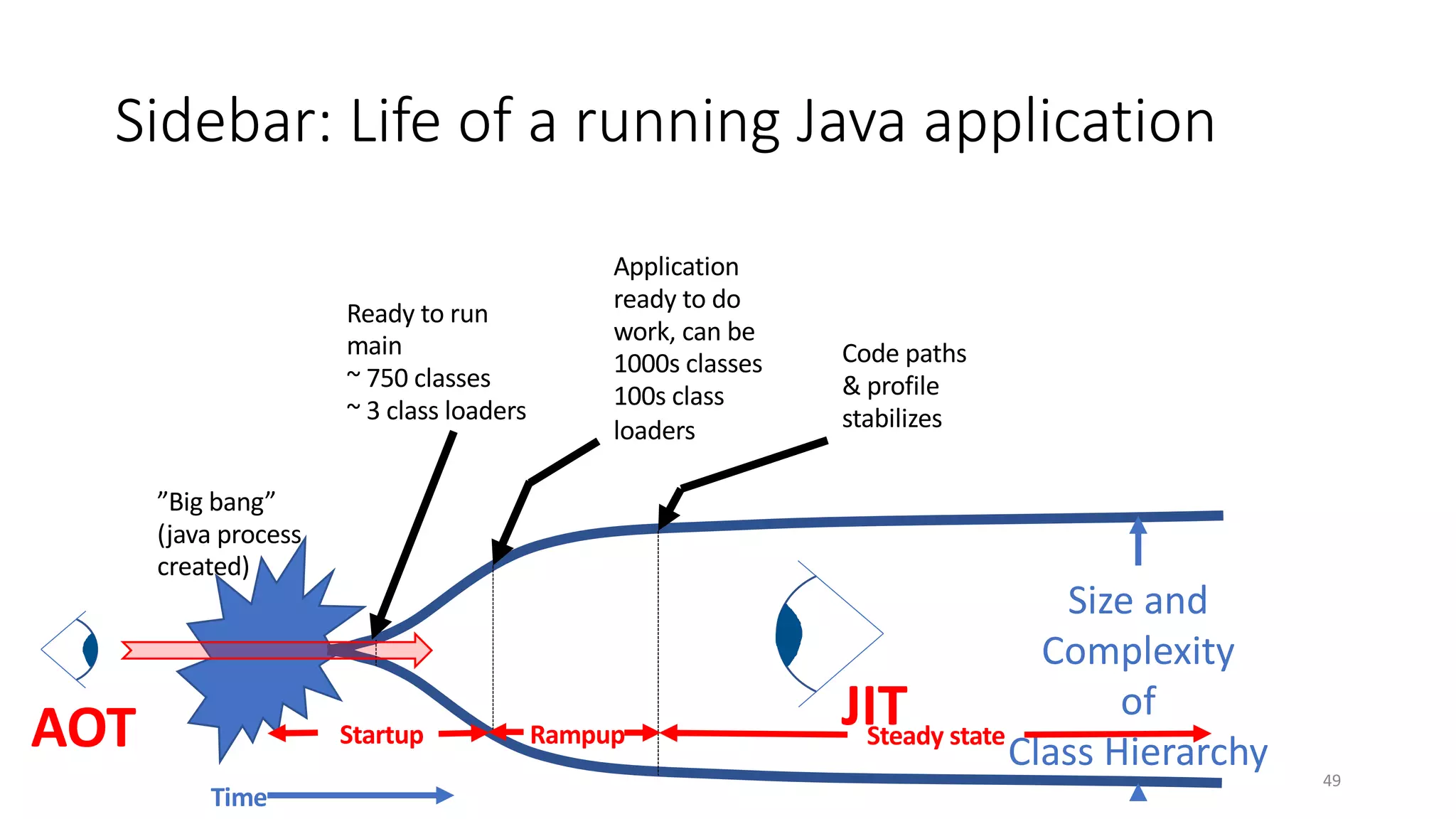
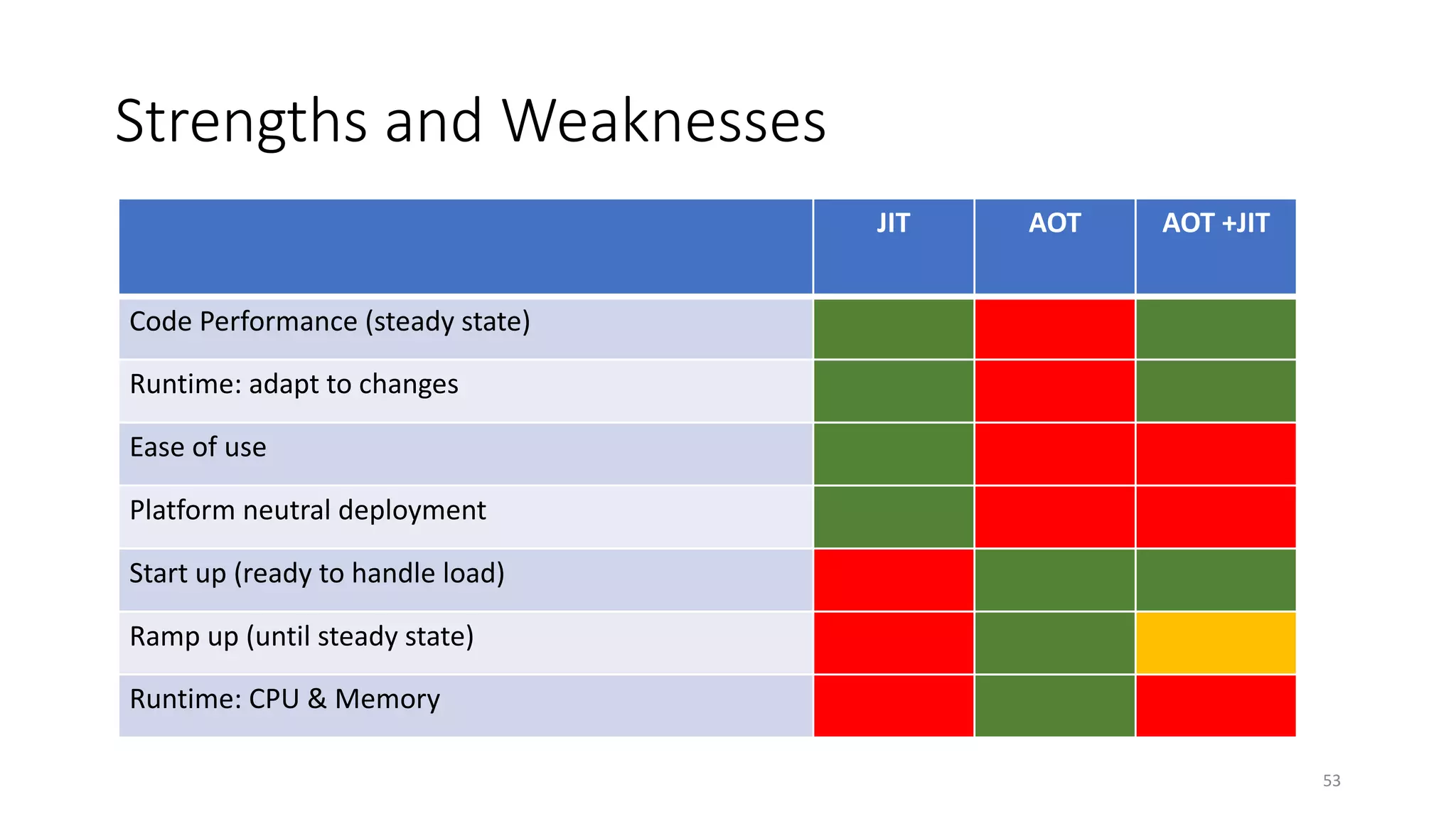
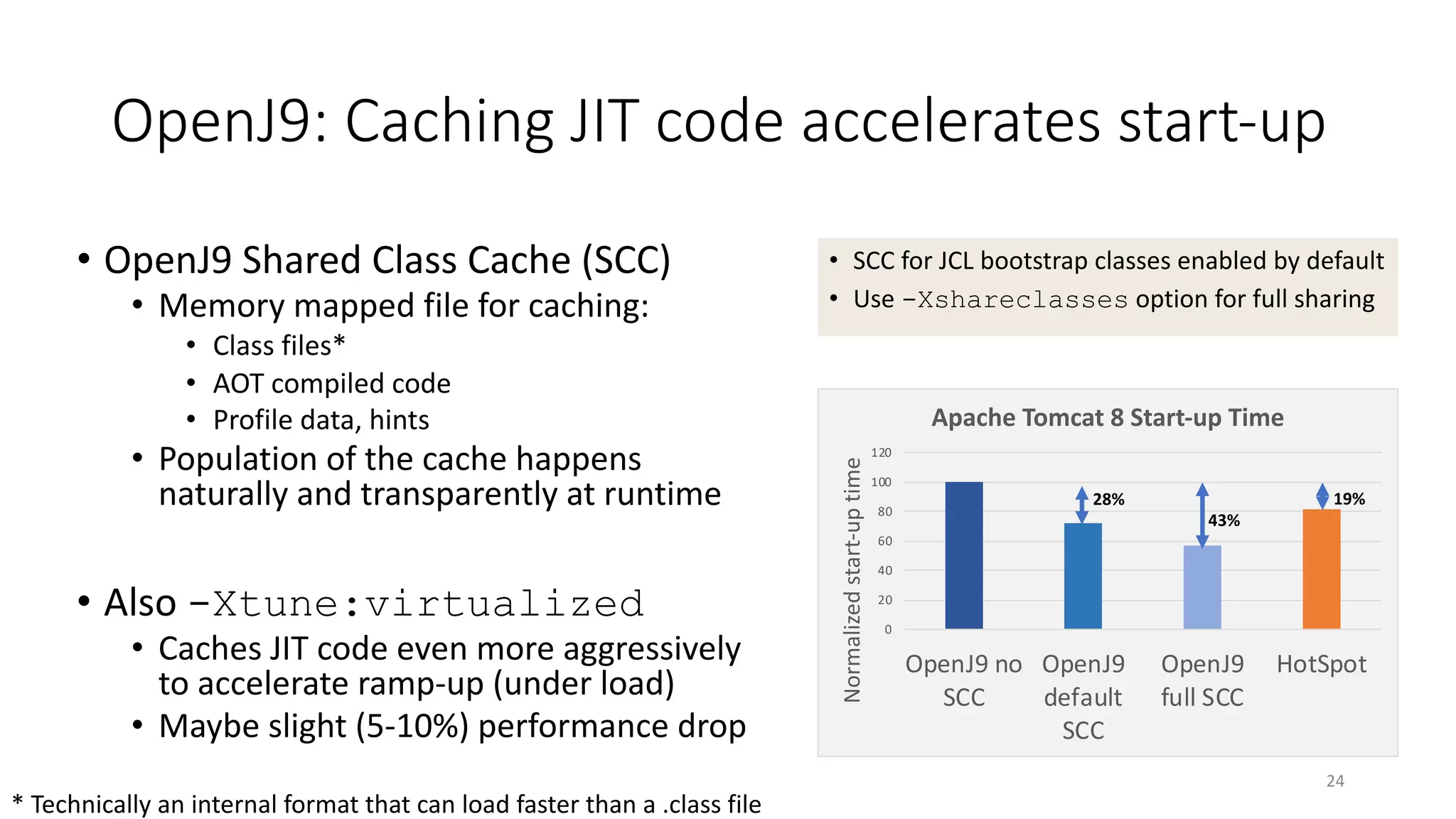
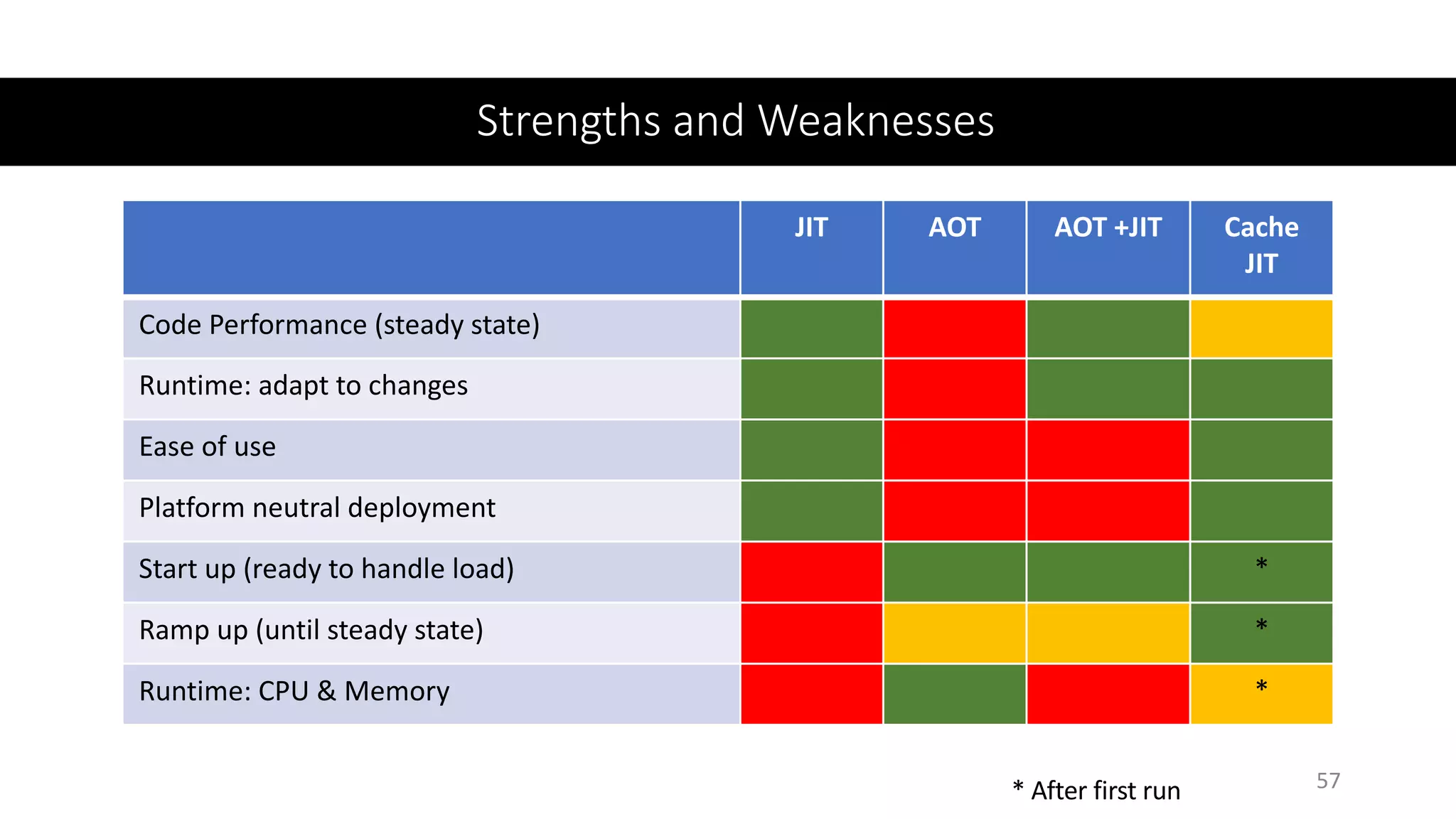
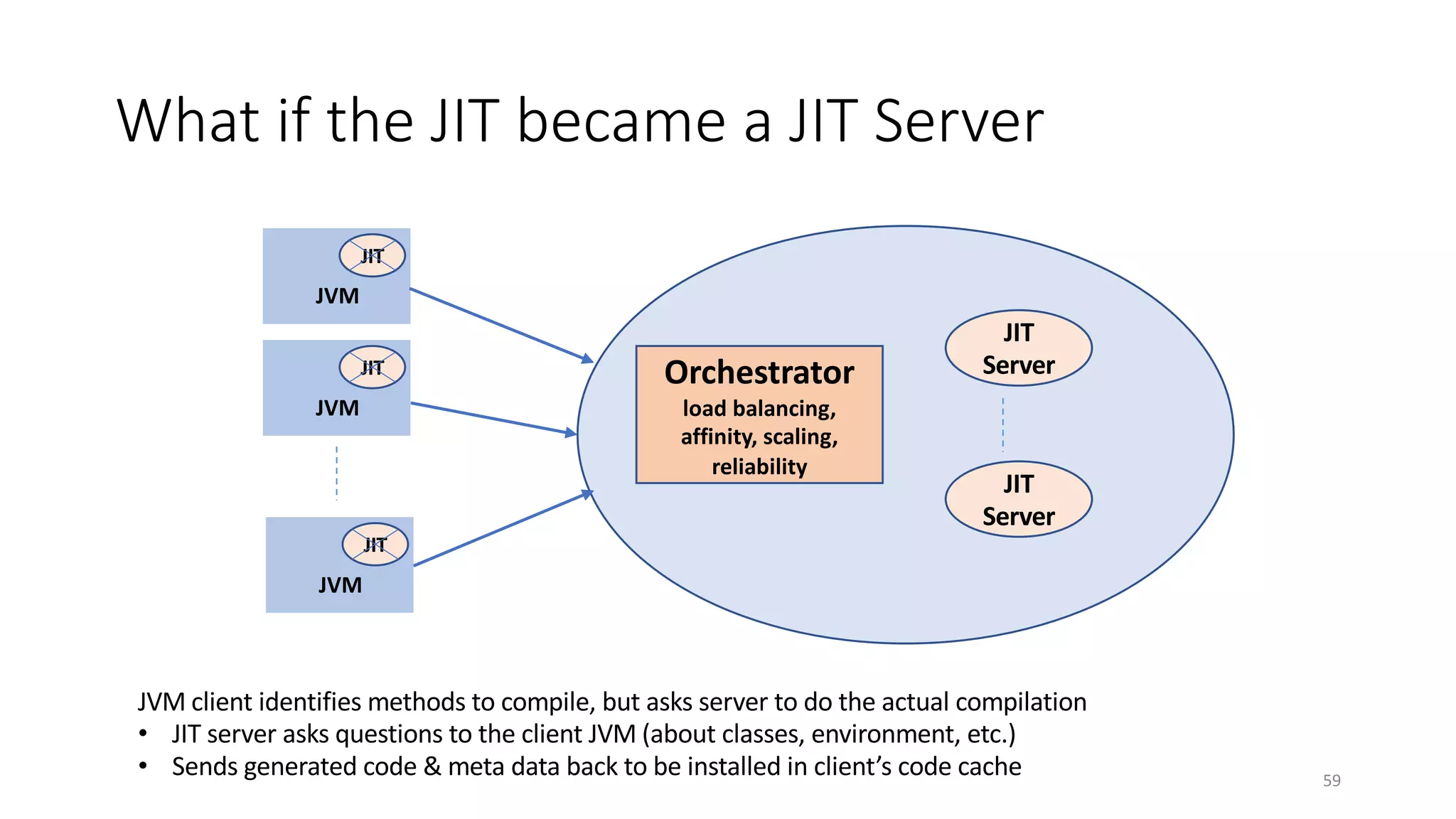
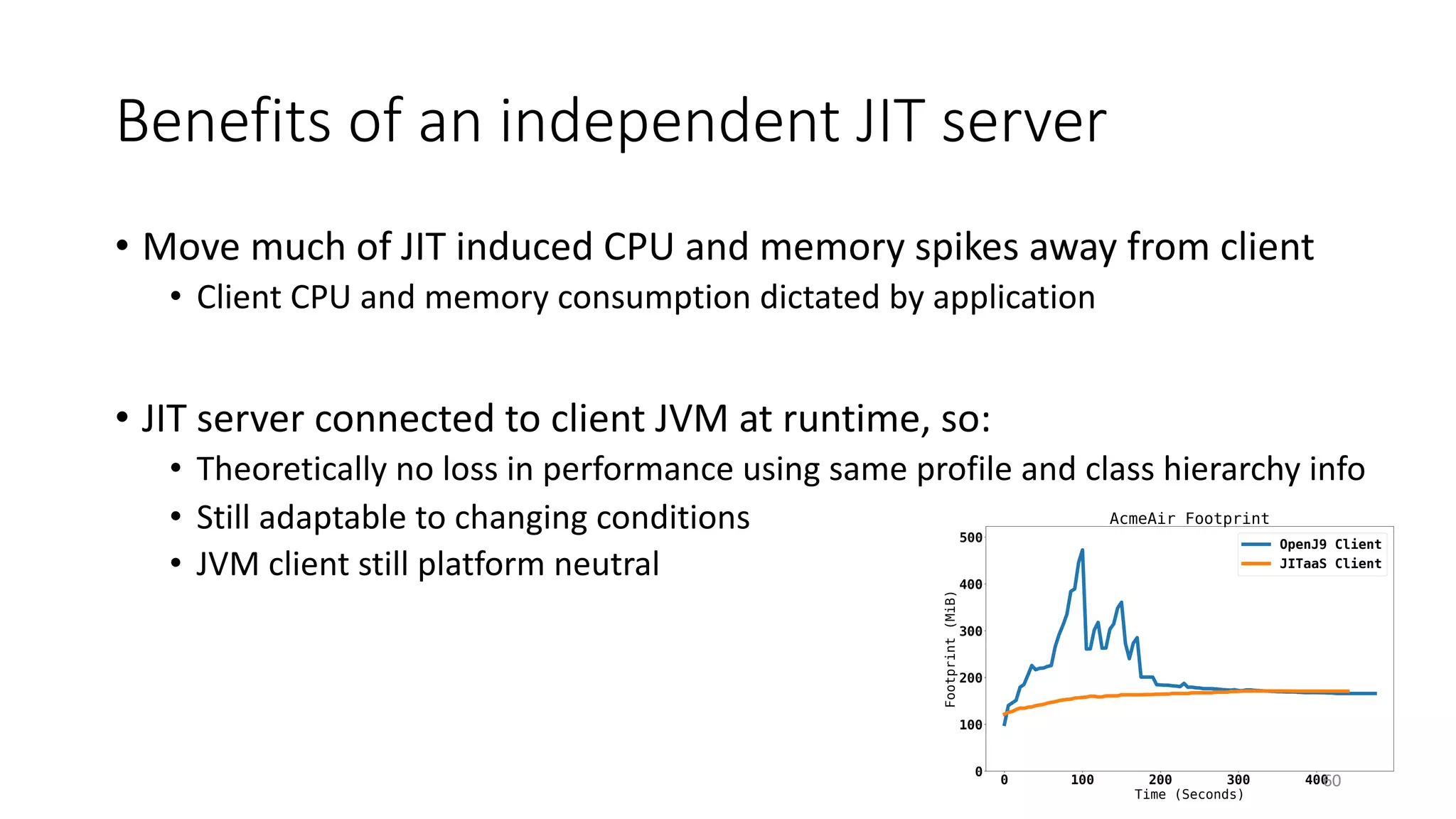
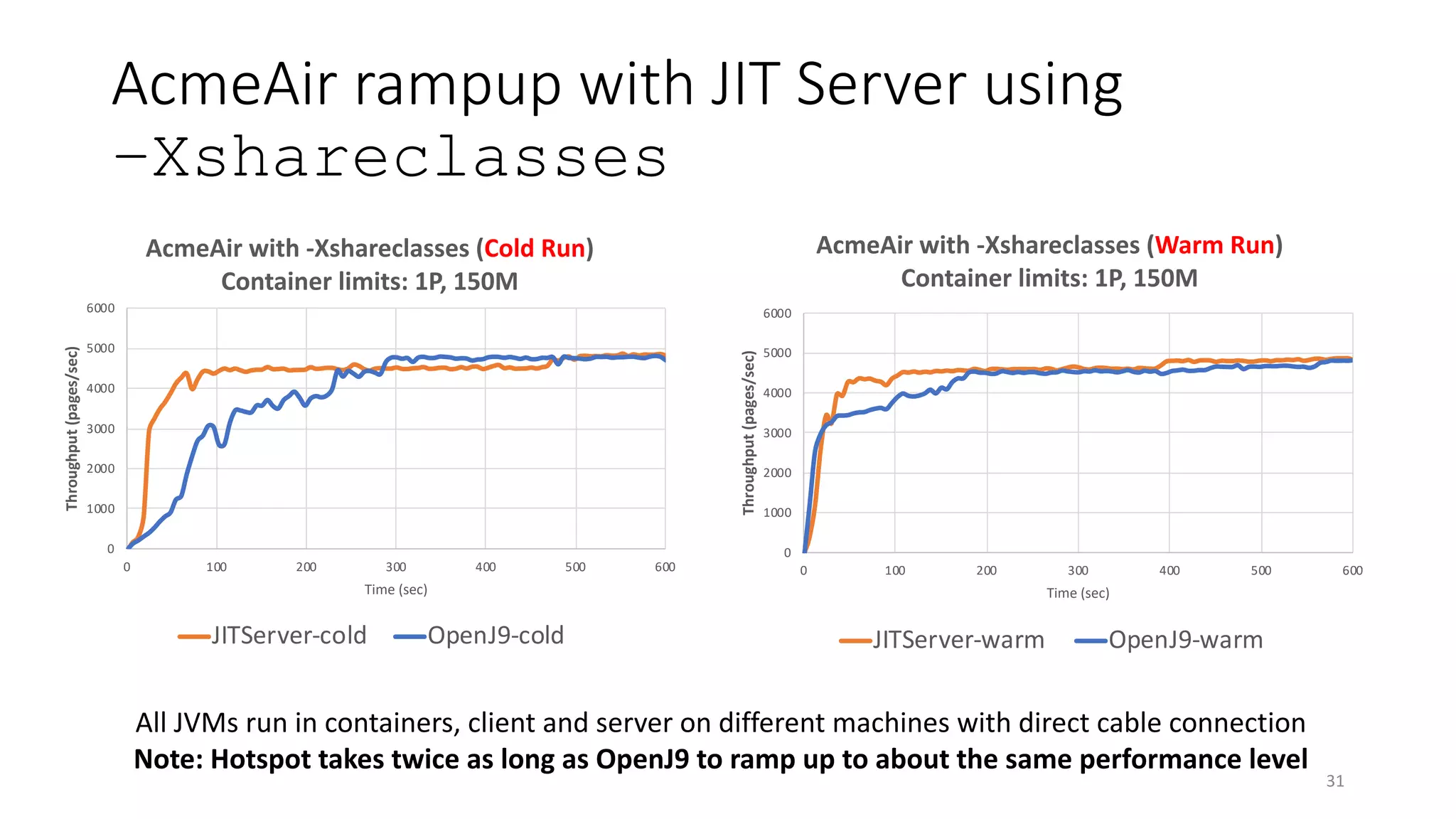
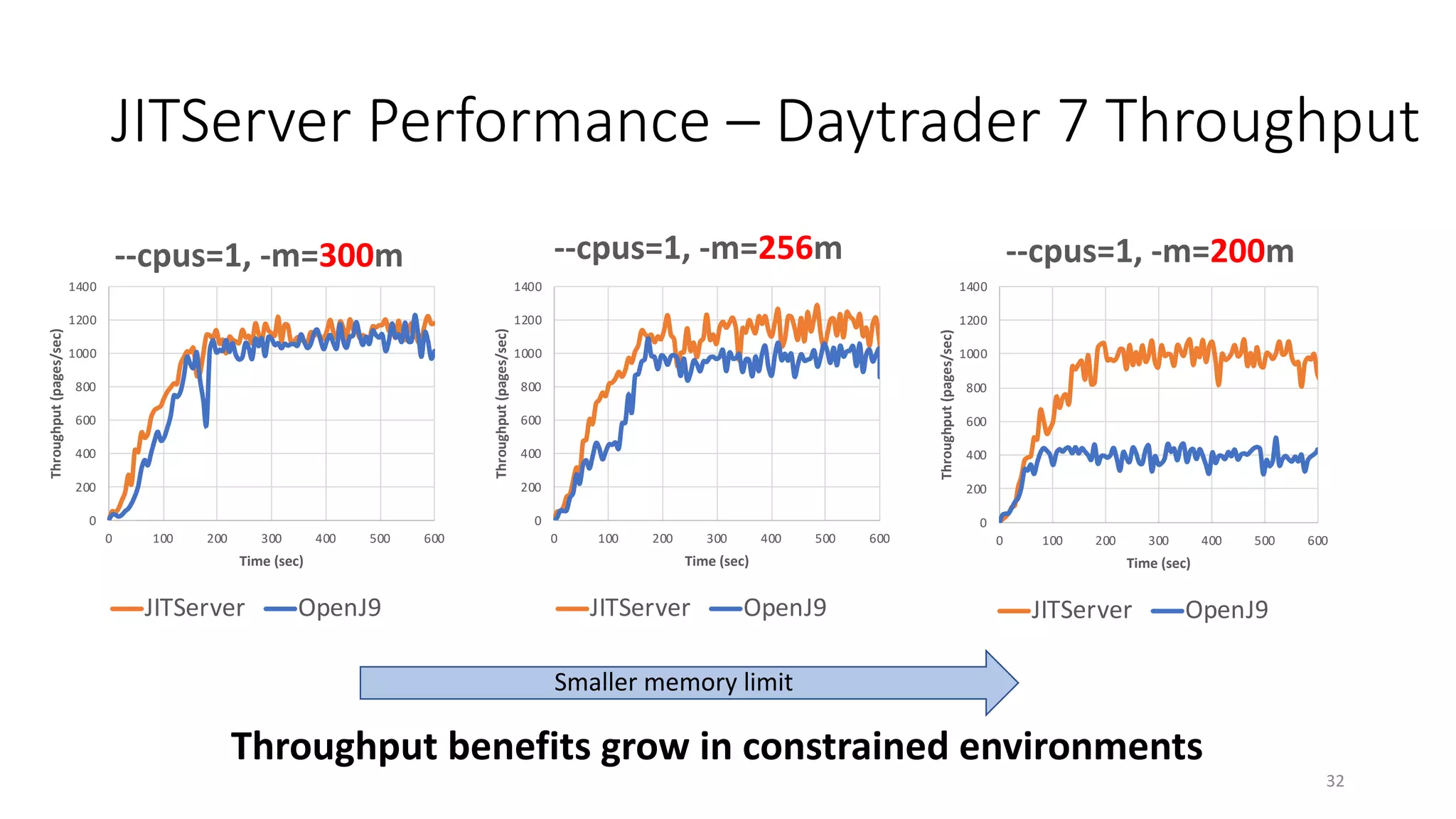
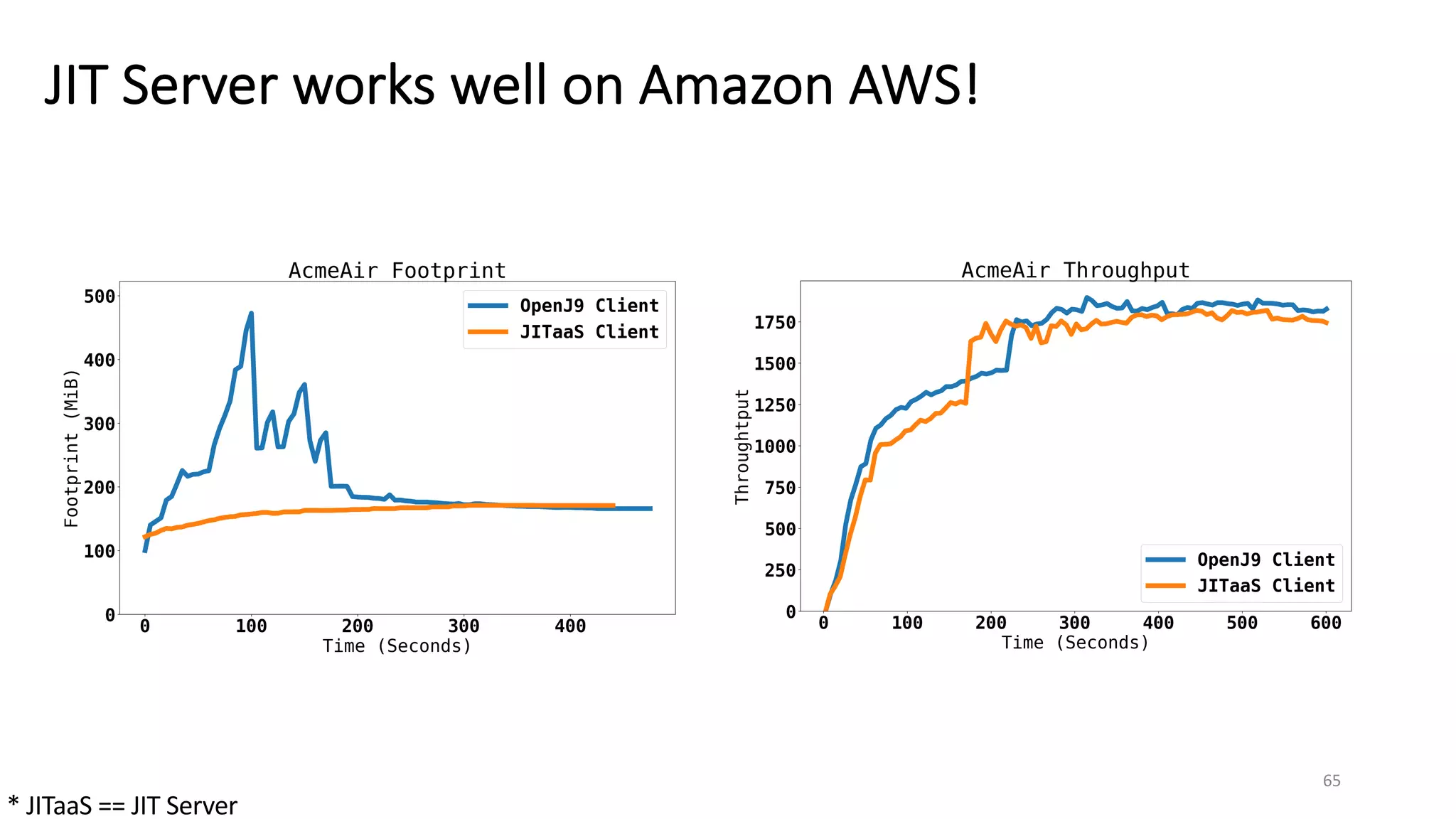
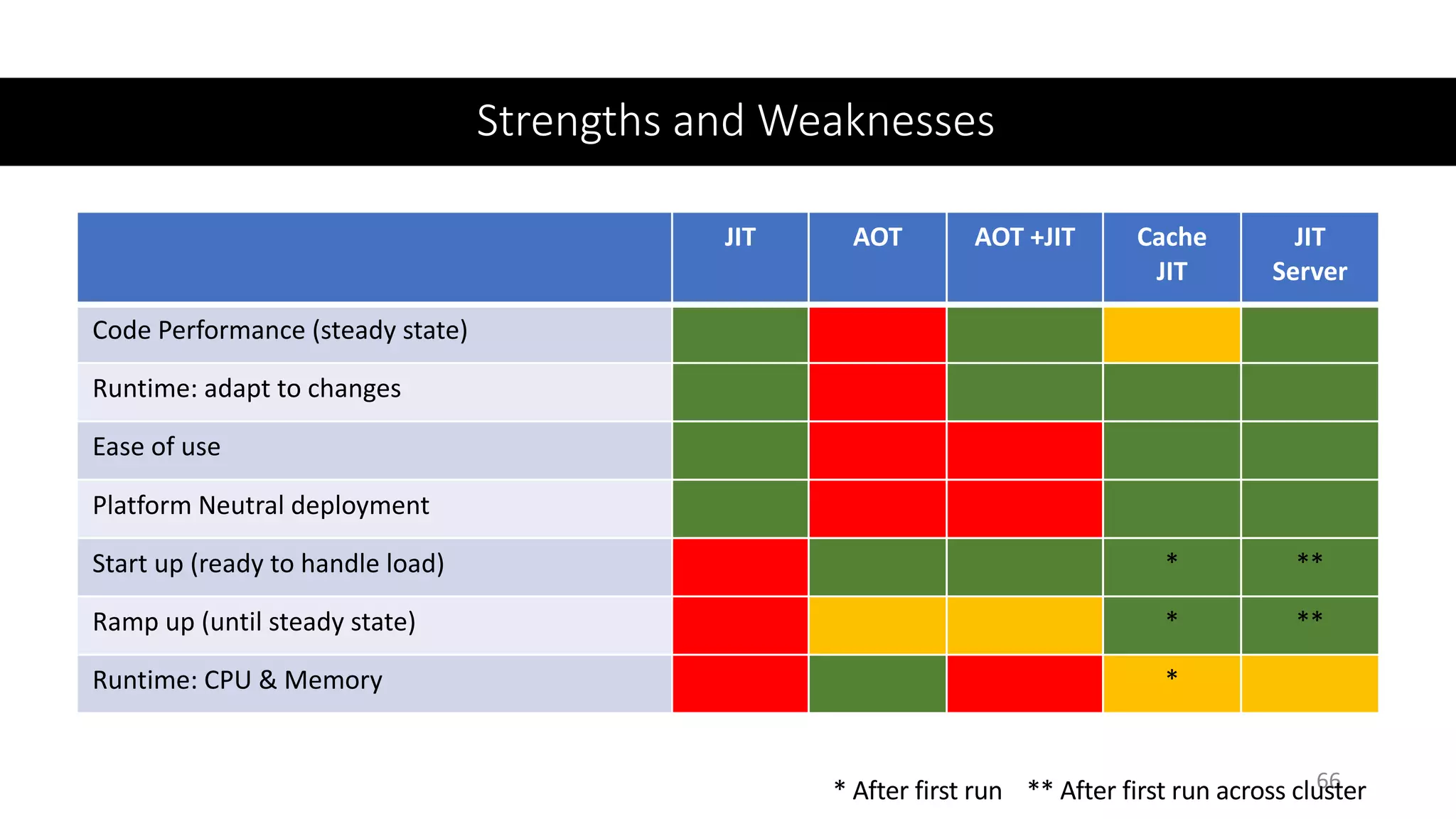
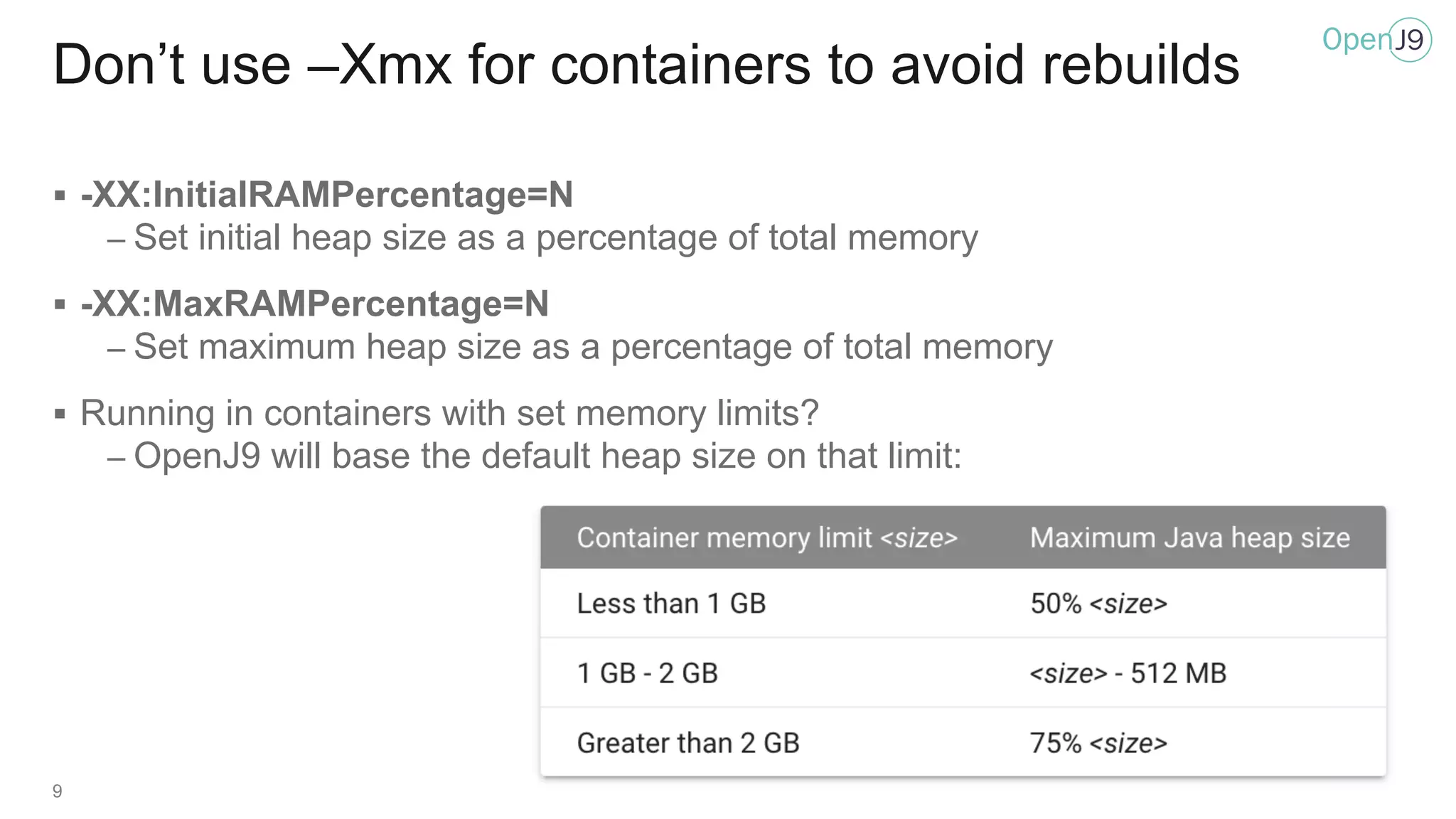
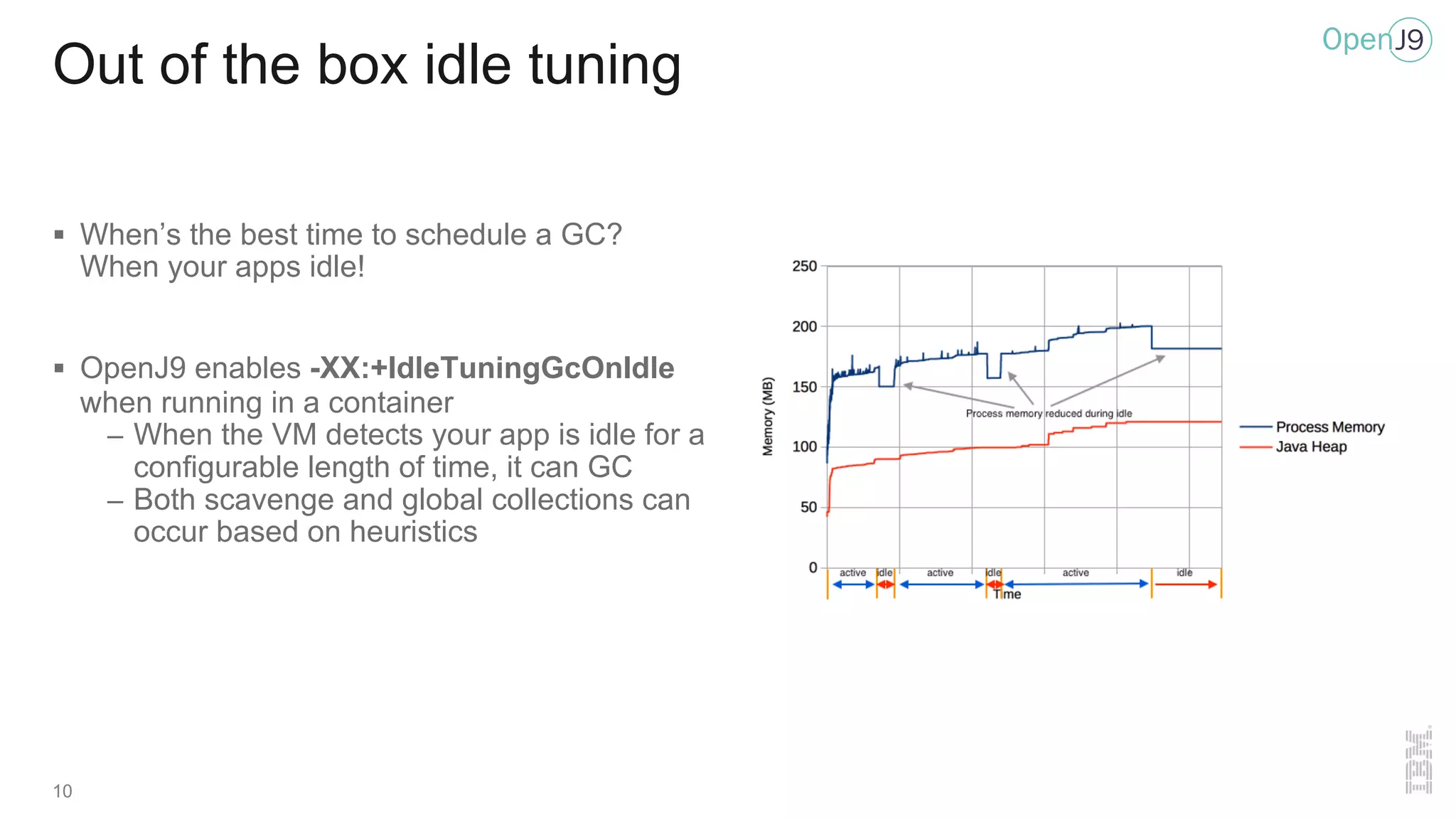
The document discusses OpenJ9, an efficient Java Virtual Machine (JVM) optimized for cloud environments, focusing on its performance benefits such as fast startup and small memory footprint. It highlights features like shared class caching, garbage collection optimizations, and a new JIT server architecture for improved compilation and runtime performance. The presentation reiterates the importance of proper resource management and tuning when running Java applications in containerized environments.




![-Xverify:none never again!
12
§ Use -XX:[+|-]ClassRelationshipVerifier instead for fast and safe startup
public class A {
public static void main(String[] args) {
B b = new B();
acceptC(b);
}
public void acceptC(C c) {}
}](https://image.slidesharecdn.com/danheidingacloudopenj9-200311160803/75/It-s-always-sunny-with-OpenJ9-12-2048.jpg)